2022
Annual Report
Wells Fargo & Company

CEO Letter
Dear Shareholders,
I’m proud to report that Wells Fargo continued to make
progress on our priorities in 2022. Our underlying financial
performance is improving, we are moving forward on our risk,
control and regulatory agenda, we are focusing on businesses
where we can generate appropriate risk-adjusted returns, we
continue to strengthen the leadership team, and we are
executing on our strategic objectives. While we have made
progress, our work is not complete and we remain focused on
successful and timely execution of our multi-year journey to
complete our risk and control work and to move forward with
our businesses.
Stronger financial performance
Our financial performance benefitted as we continued to drive
improved efficiency, and it was positively impacted by both
rising rates and a benign credit environment.
In 2022, Wells Fargo generated $13.2 billion in net income, or
$3.17 per common share. Our results were significantly
impacted by $7 billion of operating losses, primarily related to
putting historical issues behind us, including litigation,
regulatory matters, and customer remediations. However, our
performance excluding those items was solid and demonstrates
the continued progress we are making to improve returns.
Our revenue decreased 6% from the previous year. The higher
rate environment and good loan growth drove strong growth in
net interest income, which was up 26% from a year ago.
However, this growth was more than offset by lower net gains
from equity securities, mortgage banking, and investment
advisory and other asset-based fees reflecting market
conditions, as well as the lost revenue related to businesses we
sold in 2021.
Expenses increased 6% from a year ago, reflecting higher
operating losses primarily related to putting historical matters
behind us, as noted above. Excluding operating losses,
noninterest expense declined from a year ago, reflecting
continued progress on our efficiency initiatives and the impact
from business sales. We achieved these efficiency gains while we
made continued investments in our risk and control
infrastructure and in strategic initiatives across our businesses,
and in the face of continued inflationary pressures.
Credit quality remained strong, but, as expected, losses started
to slowly increase in the second half of the year off their
historical lows. Our net charge-off rate declined from 18 basis
points in 2021 to 17 basis points in 2022, and our allowance for
credit losses declined by $75 million in 2022, as our reserve
release in the first quarter was slightly larger than the reserve
builds we had in the last three quarters of the year.
Loans outstanding increased by 7% from one year ago, with
growth in both our consumer and commercial portfolios.
Consumer Banking and Lending grew 4%, driven by growth in
residential mortgage and credit card, which offset a decline in
auto loans. Both Commercial Banking and Corporate and
Investment Banking had strong loan growth, with commercial
loans up 9% from a year ago, driven by growth across all asset
classes. Average deposits in 2022 decreased 1% to $1.42 trillion,
as higher market rates spurred customers to look for higher
yielding alternatives, and consumers continued to spend savings
that built up during the pandemic.
Our capital levels remained well above our required regulatory
minimums plus buffers. We increased our quarterly common
stock dividend in the first quarter of 2022 from $0.20 per share
to $0.25 per share and then to $0.30 in the third quarter of
2022. While we did not repurchase any common stock in the last
three quarters of 2022, we have repurchased shares in the first
quarter of 2023.
Our return on equity was 7.5% and our return on tangible
common equity (ROTCE) was 9.0%
1
. Both of these ratios were
impacted by the operating losses I highlighted earlier.
In my shareholder letter over the past two years, I have
discussed our path to higher returns. Since 2020, we have
executed on a number of important items to improve our
returns, including returning $16 billion to shareholders through
net common stock repurchases, increasing our common stock
dividend from $0.10 per share to $0.30 per share, and delivering
approximately $7.5 billion of gross expense saves. Based on
these actions and others that are in flight, we believe we have a
clear line of sight to a sustainable ROTCE of approximately 15%
in the medium term. In order to achieve that, we need to
continue to optimize our capital, including returning capital to
shareholders and redeploying capital to higher returning
businesses; execute on efficiency initiatives; and benefit from
the investments we are making in our businesses.
1
Return on tangible common equity (ROTCE) is a non-GAAP
financial measure. For additional information, including a
corresponding reconciliation to GAAP financial measures, see
the “Financial Review – Capital Management – Tangible
Common Equity” section in this Report.
2022 Annual Report i
We are actively watching the
economy
Consumers
After a period of strong economic growth and low
unemployment, the Federal Reserve has been increasing
interest rates aggressively with a goal of combatting high
inflation. Increasing interest rates and a slowing economy have
caused headwinds for some of our customers, but our
customers have largely remained resilient over the past year,
with deposit balances, consumer spending and credit quality still
stronger than pre-pandemic levels.
Consumer credit card spend continued to be strong in 2022,
with spending up 25% compared with 2021, which reflects the
benefit of new Wells Fargo product launches. Almost all
spending categories had double-digit spend growth year over
year. Consumer debit card spend slowed to 3% growth in 2022
compared to 2021. Growth was driven by ticket size since
transaction volume was flat year-over-year, and discretionary
spend outpaced non-discretionary spend.
At the same time, we are carefully watching the impact of higher
rates and we expect to see deposit balances continue to
decrease and credit quality to continue to weaken. For certain
cohorts of customers, average deposit balances are below
pre-pandemic levels, and we are closely monitoring activity for
signs of potential stress. For our borrowers, we are working to
limit the risk – both to them and to us – of overextension. We
have taken selective actions across our consumer lending
businesses to mitigate risks associated with inflation and
increased debt leverage. In our auto business, we have adjusted
policies to address risk associated with collateral value declines
and inflationary pressures on consumers’ ability to pay. In home
lending, we have tightened loan-to-value policies nationally and
even more so in local markets that have elevated home value
risk. Additionally, in our card business, we have tightened our
lending policy to focus on applicants who may be exhibiting
debt-seeking behavior.
Businesses
Commercial loans grew 9% in 2022, with most of the growth in
the first half of the year. Higher inventory levels contributed to
increased working capital needs, which drove higher utilization
rates. However, utilization rates stabilized in the second half of
the year, and current data is not pointing to additional inventory
builds, which indicates most businesses are carefully managing
inventory levels amid slowing demand.
We continue to closely monitor the most pandemic-impacted
sectors and inflation-sensitive industries in our commercial
portfolio. This includes:
• Updating underwriting guidelines to include interest-rate
sensitivity to leveraged loans
• Analyzing supply chain issues, inflationary pressures, and the
impact of a potential recession
• Making timely updates to our watchlist
The Commercial Real Estate office market is showing signs of
weakness due to lower demand, driving higher vacancy rates and
deteriorating operating performance. Challenging economic and
capital market conditions are also buffeting the office market,
and while we haven’t seen this translate to significant loss
content yet, we do expect to see stress over time and are
proactively working with borrowers to manage our exposure.
Specifically, we have issued underwriting guidance for navigating
current conditions, including limited tolerance for new credit
policy exceptions, increasing minimum debt yield thresholds,
and stress testing and expansion of the watchlist process,
including additional emphasis on the office market.
Looking ahead to the remainder of 2023, we are prepared for a
range of scenarios. As a large lender to both consumers and
businesses in the United States, we have significant credit
exposure across our businesses, and as the Federal Reserve
continues to take action to reduce inflation, we will continue to
monitor both the markets and our own customer data and will
react accordingly. If our view of economic stress deteriorates
from our view at the end of 2022, we will likely add to credit loss
reserves during 2023.
Moving forward on our risk, control,
and regulatory agenda
We continue to move forward with the foundational work of
building out a risk and control framework appropriate for our
company. This multi-year journey continues to be about setting
clear priorities, cultural change, and operational execution. I have
been clear and consistently reinforce that this foundational work
is our top priority. This should always be the case for a bank such
as ours, but this has not always been the case, so reinforcement
is necessary. We remain confident in our ability to complete this
work and build appropriate risk, control, and operational
excellence into our culture.
The Acting Comptroller of the Currency gave an important
speech in January addressing the potential difficulties of
managing a large bank. Given that the OCC is a key supervisor of
ours, we take the speech seriously and are focused on its key
messages.
The speech focused on the view that there are limits to an
organization’s manageability based on size and, if so, that the most
efficient and effective way to fix this is to compel its simplification.
I am not in a position to agree or disagree with this premise, but I
am in a position to have the strong point of view that Wells Fargo
is not too big or complex to manage. Our shortcomings are not
structural, but they are the result of historically ineffective
management and the lack of proper prioritization of building out
an appropriate risk and control environment that will ultimately
take multiple years to correct.
ii
We are large but are far less complex than many with whom we
compete. In fact, we have more similarities with regional banks
than other global systemically important banks (GSIBs), and
strong and effective risk management processes should scale to
a company of our size. In addition, we have acted and will
continue to act on our own to simplify our company and reduce
operational complexity and risk, as I detail in the section later in
this letter entitled “Executing on Strategic Objectives.”
Operating at a broad scale but with less complexity than peers
1. We are primarily a US domestic bank and we do not have
the many complexities that running large-scale
international businesses bring. Our legal entity structure,
extent of international regulatory oversight and physical
footprint are far simpler than many of our competitors.
Approximately 90% of our revenues come from U.S. clients
or activities of non-U.S. clients in the U.S. Our businesses
outside the U.S. primarily support our U.S. customer base.
We are very happy with our existing footprint and are not
looking beyond for growth opportunities.
2. Our products are not complex compared with those offered
by other banks and are similar to those offered by smaller
institutions. We predominantly provide the same products
and services as regional and smaller, more local banks. We
take deposits, provide financing, move money, and provide
financial advice for our customers. Our trading activities
and the size of our market risk are relatively small compared
to other large GSIBs.
3. Scale in each of our businesses should not make us more
complex. Our distribution methods are similar to smaller
institutions. We manage a branch network, have
relationship managers across our markets, market through
the internet, traditional advertising, direct mail, and word of
mouth, and we rely on our local reputation. The controls
necessary to manage a network of 4,000+ branches are
similar to those necessary to manage a smaller branch
network. The same is true for managing relationship
managers, marketing, and protecting our reputation. Senior
management should be involved at a detailed level, but all
institutions should have and rely on defined control
frameworks in place that are effective at risk management,
regardless of individuals in a seat. These frameworks can
effectively scale to a bank of our size.
4. Our customers benefit from our size and reach. Wells Fargo
has nearly 4,600 retail bank branches, with a presence in 25
of the largest 30 markets in the U.S. A Wells Fargo branch
or ATM is within 2 miles of over half of U.S. Census
households and small businesses in our footprint. The range
of banking services we provide helps us build full
relationships with individuals and companies, allowing us to
see a full picture of their personal, family, and/or business
financial needs, and to meet these needs. We have the
ability to invest in technology to make it faster, safer, and
more transparent for our customers to handle their banking
needs. In addition, our resources allow us to innovate
quickly, developing new products, services, and digitized
experiences to meet constantly changing consumer and
business expectations. These capabilities, along with our
size and reach, are of tangible benefit to consumers across
the country, whether they live in large cities or more rural
areas, and also to the U.S. economy as a whole.
Managing the company with significantly heightened discipline
We agree that there are also traits that management should
avoid as they grow. These signs are familiar to us, as we
identified them as historical behaviors at Wells Fargo when I
arrived. We viewed them then – as we do now – as unacceptable.
Our approach today is dramatically different than it was at Wells
Fargo in the past and we will continue to work so it becomes
part of our culture at all levels in the organization.
1.
Don’t hide behind materiality – As a large institution we
know we cannot let our size hide potential issues. We must
think about raw numbers, not just percentages which are
indexed to a large customer base, asset base, or capital
base. We have built functions and processes to review
customer complaints, employee allegations, and issues
raised from outside the company, and aim to use them to
identify issues and themes so we can address them and
make changes as required.
2. Don’t assume incidents are isolated – One of the
advantages large institutions have is the amount of data
and information we see and have, but we must use it
expeditiously. Individual incidents provide data points which
can help us learn and react, and we should treat each as
such. We strive to make data-driven decisions and to
explore whether incidents that can appear isolated can in
fact have broader application elsewhere in the company.
3. Identify weaknesses ourselves and address them quickly –
The Acting Comptroller stated that “the business of
banking is operationally intensive. Even at banks with
strong teams and robust risk management systems and
controls, mistakes and problems can arise. Well-managed
banks identify such problems early and often, address them
quickly, and take steps to prevent their recurrence.” We
agree completely. Many of the historical issues we continue
to work through were identified by regulators, not by us.
We are changing this, emphasizing our responsibility to
self-identify more issues and address them with a
heightened sense of urgency. As we implement our risk and
control framework, we will likely identify more issues and
move with haste to implement compensating and
ultimately permanent controls. Our risk and control
framework is not a project, but an ongoing set of actions,
and it will be part of our culture.
4.
Hubris, contempt, and indifference are unacceptable and
dangerous traits – We cannot believe that we know better
2022 Annual Report iii

than others and need to react with seriousness and urgency
when issues are raised – whether from employees,
customers, regulators, or others outside the company.
Every issue raised has the opportunity to be a learning
moment and we should also proactively look at our
competitors to learn as well.
5. Integration of mergers is more than a short-term
technology conversion – While we have not had a merger-
related systems integration in my time at Wells Fargo, we
agree that “simply stitch[ing]…systems together” can
cause a proliferation of issues. It is critical to merge and
simplify platforms, whether merger-related or as part of a
customer service strategy, as the reduced complexity in the
number of platforms should make it easier to properly serve
customers. For example, asking customer-service
representatives to learn multiple systems to provide the
same information creates more operational risk and the
possibility of a poor customer experience.
But these platform mergers should be the beginning of
integration, not the end. This is true looking both from our
perspective and the customer perspective. Customers think
of us as one company, not as separate relationships with
individual lines of business. They want to see their
information seamlessly and be able to transact with us
easily across all of their products. Unless we integrate our
platforms, we will either not appear as one company to the
customer, or we will create workarounds to try and
accomplish this, which creates unneeded operational risk. A
major competitive advantage of Wells Fargo is serving our
customers across a broad range of products, but we can
only do so effectively with common platforms.
The same is true of data platforms. Pulling customer data
from multiple platforms is operationally complex and
expensive. Common data platforms across our company are
critical. We rely on this for financial reporting, regulatory
reporting, risk reporting, and the ability to assess a
customer relationship holistically.
And finally, it is a mistake to lose sight of aged platforms, to
not invest in improving them and to not move to new ones.
New software and hardware solutions make it easier to
reduce complexity and properly serve customers, and when
these solutions are part of a program with a clear target
state, they should significantly reduce operational
complexity.
Recognizing this, Wells Fargo is implementing a modern
technology stack that is cloud-native and therefore more
elastic and resilient. We are applying this stack for the
various product domains that we are modernizing across
our businesses. Examples include a more modern digital
desktop for our financial advisors in Wealth and Investment
Management, our value-at-risk models in Corporate and
Investment Banking, and our payment platforms across
businesses. These modernization initiatives are guided
top-down by a product and platform architecture that sets
clear boundaries and expectations for teams. In addition to
this, the hosting of our platforms is more and more
migrating to a combination of private and public cloud,
powered by our partnerships with Google and Microsoft.
This also is leading to faster innovation by plugging in
innovative services provided by these cloud providers into
our platforms.
In parallel to these modernization efforts, we are also
enhancing the way we deliver software and the developer
experience. We are implementing new cloud-native tool-
chains that allow our developers to have the experience that
they deserve: on-demand, instant, elastic and with
embedded automated controls.
Further taking stock of where we stand – why haven’t we
completed our risk and regulatory work
I am frequently asked why our risk and regulatory work is not
complete though we have been publicly reprimanded, have a
growth constraint, and I have been leading the company for over
3 years. I wish my job was merely to complete work that was well
underway, but unfortunately this was not the case. Simply said,
the work to build the appropriate risk and control infrastructure
and close consent orders takes years when managed effectively,
and we were not as far along as I had expected when I arrived.
Much work was needed to build what is necessary to properly
accomplish the work.
When I arrived, we did not have the culture, effective processes,
or appropriate management oversight in place to remediate
weaknesses on a timely basis. Today, we approach these issues
differently. This management team (the broad team – not just
me) has the skills and experience and is now responsible for
closing our consent orders. We have changed and implemented
much to put ourselves in a position to have the confidence that
we can accomplish this. The specifics of our regulatory
remediation plans are confidential, and while we are not where
we need to be, I believe that our position is significantly
improved and that we will reach our goals. We are committed to
making all necessary resources available to meet our obligations.
I have said we are a different company today, and in this
sub-section, I provide some examples.
1. When I arrived at the company in 2019, we had 12 open,
public enforcement actions. Given this and the other
control issues we needed to assess, it took many months to
understand the depth and breadth of the weaknesses and
what was required to complete the work.
2. We then went about recruiting a mostly new management
team with the experience and skills that we did not
sufficiently have at the company. A large portion of the
Operating Committee was recruited during 2020 and they
then needed to do their own assessments and develop
plans. They then needed several years to build out their
teams.
iv
3. For each consent order Matters Requiring Attention
(MRAs), and other control gaps identified, we needed to
build detailed plans that satisfied both us and our
regulators. Our plans are now detailed and have hundreds of
deliverables with designated delivery dates. Many of our
consent orders have work that relies on work from another
order, so any slippage on one plan can impact another. Our
ability to assess all of this accurately for work to be done
over multiple years has not been perfect, and we have
missed some deliverables, but we have learned, adjusted,
and continue to move forward.
4. We needed to build processes to manage these across the
company. Building reporting and setting up management
review structures for these activities has been critical to
moving the work forward. Most of these did not exist or
were ineffective, and we now believe we have much more
effective reporting and processes in place to provide
appropriate oversight and allow us to identify issues early
so we can course-correct.
5. We did not have the resources necessary to accomplish this
work when I arrived. We have added close to 10,000 people
across numerous risk- and control-related groups and have
spent approximately $2 billion more in 2022 than in 2018 in
these areas. We are committed to make the investments
needed to complete the work.
6. And we had to build the management disciplines and
culture to govern and execute such a large body of work.
Our Operating Committee reviews risk and regulatory
progress and escalations on a weekly basis. We provide
detailed reporting to the full board and appropriate
committees so they can provide oversight. These reviews
are systematic and detailed, and they are helping us provide
the appropriate oversight and involvement to accomplish
the work.
I should add that we had to do all of this during the very worst of
the COVID-19 pandemic. While we were not alone in dealing
with the complexities of work from home, social distancing and
meeting the needs of customers during a pandemic, we were
alone in what we had to build, and doing so in a remote working
environment increased the difficulty level significantly.
Some have suggested that banks view enforcement actions and
fines as a cost of doing business, but I can tell you that today,
nothing is further from the truth at Wells Fargo. We view any
such action by our regulators as something that requires
immediate management attention. We aim both to avoid the
necessity of such action by doing the work ourselves and, when
regulators do take enforcement action against us, we follow a
disciplined process to work towards closure, again with all
necessary resources available for the effort.
The negative impact on our reputation of having not fulfilled our
obligations is clear. Simply put, failure to satisfy our regulatory
requirements carries significant consequences for our company.
On the other hand, fulfilling our obligations and building an
appropriate risk and control framework will allow us to build a
strong reputation amongst a broad set of stakeholders. So why
do we have so many consent orders that have been open for
extended periods? Again, our historical practices were
inadequate, and it has taken time to build what is necessary to
change our historical inadequacies.
So as I look at our situation today, the failure of Wells Fargo to
complete its work appropriately has resulted in multiple consent
orders, fines, and an asset cap. But I can say confidently that we
have taken significant actions including focusing and simplifying
the company, refreshing the board, replacing most of the senior
management team, and are now moving forward to correct past
deficiencies. We have the willingness and the ability to complete
the work.
And to be clear, we are committed to prioritizing this work
above all else by devoting all necessary resources to the effort.
Our planning is designed to ensure other activities do not
interfere with this top priority. If we have a conflict, our risk and
control work comes first.
I have said our progress will likely not be a straight line. We
continue to resolve issues that were found years ago or are the
result of the inadequate control environment that existed when
we arrived at the company. This means that resolution of
outstanding issues such as litigation, customer remediations or
regulatory investigations have and could continue to have
financial impacts. Additionally, until our work is complete, we will
likely find new issues that need to be remediated, and these may
result in additional regulatory actions.
Finally, as we continue to execute on our detailed plans, given
the scope and complexity of our work, we may miss some
interim milestones. We recognize the importance of meeting
milestones that we ourselves set, but perfection is unlikely.
When we discover an issue, we act quickly to course-correct and
do what we can to get back on schedule. This is frustrating for us
and others outside the company but is not indicative of our
willingness or ability to complete our work. Rather, it is an
obstacle that presents itself in nearly any large-scale, multi-year
transformation.
When Wells Fargo faces criticism about where we stand, I
understand the sentiment. I hope this section has provided
detailed context and is helpful in providing an understanding of
what we are doing to close our gaps. This team is taking decisive
action to move our company past these issues.
Leadership Team
Key to transforming the company, changing our culture, and
realizing the full strength of our franchise is having the best
management team in place. Since I joined the company in 2019,
12 of our 17 Operating Committee members are new to Wells
Fargo and 15 are new to their roles. In 2022, we put in place a
new Chief Auditor, a new Chief Risk Officer, a new head of
Consumer Lending, and a new head of Diverse Segments,
Representation and Inclusion.
2022 Annual Report v

We continue to refresh our management ranks more broadly.
Over 80% of our senior executive leaders – a group of
approximately 150 people, most of whom report to Operating
Committee members – are new to their roles since 2019, and
nearly 60% are new to the company over the same time period.
Over 30% of the individuals in this senior executive cohort began
in new roles in 2022 or 2023. New leaders who have joined over
the past several years bring important experience that is
necessary for our journey.
Executing on Strategic Objectives
Simplifying our business
We continue to review the strategic positioning of the company
and are focusing our efforts on building products and services
that are core to serving our clients. This focus has led us to
decisions to sell, downsize, or curtail multiple businesses. These
decisions simplify the company, reduce operational complexity
and risk, and allow us to focus on both our core risk and control
buildout and ways to serve our customers in our core franchises.
There are several examples since I joined the company in 2019.
In January 2023, we announced plans to simplify our Home
Lending business and will primarily serve bank and wealth
management customers as well as borrowers in minority
communities. As part of this shift, we announced our plans to
exit the Correspondent business, reduce the size of our Servicing
portfolio, and optimize our Retail team so it aligns with our
narrower customer focus. These actions will allow us to reduce
risk in the Home Lending business while continuing making
homeownership possible to thousands of Americans.
Over the past year, we have taken several additional steps to
simplify the way we operate. For instance, we have:
• Implemented a cloud-native operating model which will
enable us to reduce reliance on older, less stable platforms
and allows us to innovate faster
• Centrally organized our Control Management teams, to
enable better coordination across our businesses
• Streamlined our divisional leadership in Wells Fargo Advisors,
moving from eight regional divisions to four
• Combined Treasury Services platforms across Commercial
Banking and Corporate and Investment Banking
Looking further back to 2021, 2020, and 2019, we have:
• Sold Wells Fargo Asset Management
• Sold our Corporate Trust Services business
• Sold our student lending portfolio and stopped the
origination of new student loans
• Exited our international wealth management segment
• Sold our Canadian direct equipment finance business
• Stopped offering new home equity lines and loans
• Exited the direct Auto business
• Stopped originating personal lines of credit
• Sold our Institutional Retirement and Trust business
• In addition, over the past several years, we have closed over a
dozen representative offices globally to better focus our
international business, including offices in Asia, Europe, South
America, the Middle East, and elsewhere.
Going forward, we will continue to evaluate our businesses with
an eye toward reducing complexity, increasing risk-adjusted
returns, and focusing our resources on the most important
products and services our customers require. Market dynamics
change, the competitive environment changes, regulatory
expectations evolve and we must adjust our business
accordingly.
Focusing on customer needs and expectations
Each of our businesses is working to transform how we serve our
customers by offering focused, innovative products and
solutions. Many of the initiatives underway reduce risk in the
company and we evaluate new initiatives to consider the
potential impact on our control environment. Some examples
are below.
Our Consumer Businesses: Consumer and Small Business
Banking, Consumer Lending, and Wealth and Investment
Management
• We rolled out our new consumer mobile app with a simpler,
more intuitive user experience which has improved customer
satisfaction. We also completed the development of Fargo,
our new AI-powered virtual assistant, which provides a more
personalized, convenient, and simple consumer banking
experience. Fargo is currently live for eligible employees and is
set to begin rolling out to customers during the first half of
this year. Providing such digitized services directly to our
customers reduces operational complexity in our service
centers and increases customer satisfaction.
• We continued to improve our credit card offerings including
launching two new cards – Wells Fargo Autograph and BILT.
While we describe these as new products, these are actually
updated products in a business we have been in for many
years.
• We launched Wells Fargo Premier, our new offering dedicated
to the financial needs of affluent clients by bringing together
our branch-based and wealth-based businesses to provide a
more comprehensive, relevant, and integrated offering for
our clients.
• We also relaunched Intuitive Investor in our Wealth and
Investment Management segment, making it easier for
customers to invest with a streamlined account opening
process and a lower minimum investment.
vi

Our Wholesale Businesses: Commercial Banking and Corporate
and Investment Banking
• We have made several hires in Corporate and Investment
Banking that have received some press. These hires are in
industries we currently serve and products we currently offer,
but the individuals bring new expertise to Wells Fargo.
• We continued to enhance the partnership within our
commercial businesses to bring Corporate and Investment
Banking products such as foreign exchange and M&A advisory
services to our middle-market corporate clients.
• In December we announced Vantage, an enhanced digital
experience for our commercial and corporate clients. Vantage
uses artificial intelligence and machine learning to provide a
tailored and intuitive platform based on our clients’ specific
needs.
• Over the past year our industry-leading API platform team
continued the development of payment APIs for commercial
and corporate clients, invested in solutions to support our
financial institution clients, ramped-up and grew product
offerings in consumer lending, and began developing
commercial lending solutions.
Evolving our approach to technology
Technology is helping us better serve our consumer and
corporate clients. Our technology talent is modernizing
platforms for our customers, clients and colleagues. Specific
areas of focus are:
• A cross-product pricing platform
• Digitization of our lending origination platforms across Small
Business, Commercial and Corporate Banking
• Continued modernization of our Treasury Services and
Payments platforms
• Strengthening our technological capabilities in fraud
prevention
• Modernizing key corporate risk platforms
• Refreshing our Auto loans platform
These enhanced digital capabilities are just the start of the
initiatives we have planned as part of our multi-year digital
transformation.
Seeing early returns from this work
Our work to build better, more customer-focused products and
a more technology-enabled company is generating measurable
returns. For instance:
• In Consumer and Small Business Banking, mobile active
customers grew 4% from a year ago.
• The new credit cards I mentioned above helped drive a 31%
increase in new credit card accounts in 2022, and we’ve
continued to maintain strong credit profiles. The average
FICO score of our new accounts in 2022 was 773, compared
to 761 for the 2019 vintage.
• In Wealth and Investment Management, total active Intuitive
Investor accounts increased 56% from a year ago.
• Our U.S. investment banking market share was 3.2% in 2022,
up 61 basis points versus 2021. We had the #7 ranking in this
year’s U.S. investment banking league tables, up two spots
from 2021.
• As a company, we deliver many solutions nowadays in sprints,
reducing our through-put time by as much as 60% compared
to 2020.
ESG, communities and customer
centricity
As I look back at 2022, I’m enthusiastic about the progress we’ve
made in serving our communities and our customers, and I feel
even better about the opportunities ahead.
Let me start with the changes we made during the year to help
millions of customers avoid overdraft fees and meet short-term
cash needs. These efforts included:
• The elimination of non-sufficient funds fees and transfer fees
for customers enrolled in Overdraft Protection.
• Early Pay Day, making eligible direct deposits available up to
two days early.
• Extra Day Grace, giving eligible customers an extra business
day to make deposits to avoid overdraft fees.
• And in the fourth quarter we launched Flex Loan, a new
digital-only, small-dollar loan that provides eligible customers
convenient and affordable access to funds. Teams from
across the company came together to roll out this new
product in just a few months. Though it’s still early, customer
response is exceeding our expectations.
The above actions build on services we’ve introduced over the
past several years, including Clear Access Banking, a consumer
banking account with no overdraft fees. We now have
over 1.7 million of those accounts, up 48% from a year ago.
Beyond our customers, we have an important responsibility to
strengthen the communities we serve. We continued that work
in 2022. This was true on several fronts.
Supporting homeownership
• We launched a Special Purpose Credit Program in 2022,
committing $150 million to advance racial equity in
homeownership, with an additional $100 million investment
towards this racial equity effort announced in 2023.
• We established Wealth Opportunities Restored through
Homeownership, or WORTH, a $60 million national effort to
address systematic barriers to homeownership for people of
color. Nationally, WORTH aims to help create 40,000 new
homeowners of color in eight markets by the end of 2025
2022 Annual Report vii

• We announced an expansion of our Dream.Plan.Home closing
cost credit, which provides borrowers with an income at or
below 80% of the area median income where the property is
located up to $5,000 to use toward closing costs. The credit is
available in 16 states and in Washington, DC.
• We announced Growing Diverse Housing Developers, a
$40 million grant initiative focused on expanding the growth
and success of real estate developers of color, including Black-
and Latino-owned firms.
Banking inclusion
• As part of our Banking Inclusion Initiative, we launched our
first Community Connections Branch outside Atlanta, with
more to come. These branches offer spaces for financial
health seminars and individual consultations.
• Also as part of our Banking Inclusion Initiative, we announced
plans with Operation HOPE to introduce HOPE Inside centers
in 20 markets. HOPE Inside Centers feature financial coaches
who will help empower community members to achieve their
financial goals through financial education and free
one-on-one coaching. To date, we’ve launched these centers
in the Atlanta, Houston, Los Angeles, Oakland and Phoenix
metro regions.
• Since its launch in 2022, our Small Business Resource
Navigator has connected nearly 1,300 small businesses to
potential credit opportunities and technical assistance
services provided by CDFIs.
Climate initiatives
• We announced interim greenhouse gas reduction targets for
the Oil & Gas and Power sectors.
• We issued our second Inclusive Communities and Climate
Bond, a $2 billion bond that will finance projects and
programs supporting housing affordability, economic
opportunity, renewable energy and clean transportation.
In addition, we have made significant progress on our Diversity,
Equity and Inclusion initiatives. These are detailed in our first
Diversity, Equity, and Inclusion annual report, which we
published last summer. We continue to push forward on our
commitment to integrating DE&I across the company, and, as
part of this commitment, we have commissioned an external,
third-party Racial Equity Assessment. We plan to publish the
results of the assessment by the end of this year.
I’m proud of all this work. We are balanced in our approach to
environmental, social and governance issues, and, as I wrote a
year ago, we believe that for us to be successful as a company,
we must consider a broad set of stakeholders in our decisions
and actions, beyond shareholders. This is not in lieu of
shareholders – in fact we believe it will enhance our returns to
shareholders over time. Our history has shown this to be true.
Consumers and businesses want to do business with a company
that has a strong reputation. A strong reputation is achieved not
just from strong financial performance, but from actively
supporting employees, customers, and communities – especially
those most in need.
As we look forward
I remain confident in our company. The franchise we have is
enviable and will become increasingly more so as we transform
the company. We have done much and we must finish the risk
and control work I’ve described in a timeframe and with the
quality to satisfy our regulators to take advantage of the
opportunities in front of us, so this will remain our top priority.
We will do this while we navigate what will likely be a tricky
economic environment. 2022 was a turning point in the cycle
and the impact of the Federal Reserve’s interest rate increases
have not been fully seen in the economy yet. Though we are
starting to see the impact on consumer spend, credit, housing,
and demands for goods and services, it is still early. Thus far, the
impact to consumers and businesses has been manageable.
Though there will certainly be some industries and segments of
consumers that are more impacted than others, the rate of
impact we see in our customer base is not materially
accelerating. This plus the strength with which consumers and
businesses went into this slowing economy is a helpful set of
facts as we look forward.
While we are not predicting a severe downturn, we must be
prepared for one and we are a stronger company today than 1
and 2 years ago. We have actively managed our capital position
and focused on efficiency. Our margins are wider, our returns are
higher, we are better managed, and our capital position is
strong. While we will be impacted by a downturn in the
economic cycle, we feel prepared for a downside scenario if
we see broader deterioration than we currently see or predict.
We still have clear opportunities to improve our performance as
we make progress on our efficiency initiatives. We will invest as
necessary in our risk and control infrastructure, we will
modernize our existing platforms, and we will continue to make
the investments necessary serve our customers through service,
technology and product enhancements.
I want to conclude by thanking our employees across the
company who are working hard each day to continue to make
progress on our transformation. The pressure they feel to
accomplish our work is immense and the dedication that I see is
unmatched. I’m thankful for all that they do and remain
committed to leading us towards the goal of being the most
respected financial institution in the country.
I’m excited about all that we will accomplish in the year ahead.
Charles W. Scharf
Chief Executive Officer
Wells Fargo & Company
March 3, 2023
viii
Our Performance
$ and shares outstanding in millions, except per share amounts 2022 2021 2020
SELECTED INCOME STATEMENT DATA
Total revenue $ 73,785 78,492 74,264
Noninterest expense 57,282 53,831 57,630
Pre-tax pre-provision profit (PTPP)
1
16,503 24,661 16,634
Provision for credit losses 1,534 (4,155) 14,129
Wells Fargo net income 13,182 21,548 3,377
Wells Fargo net income applicable to common stock 12,067 20,256 1,786
COMMON SHARE DATA
Diluted earnings per common share 3.14 4.95 0.43
Dividends declared per common share 1.10 0.60 1.22
Common shares outstanding 3,833.8 3,885.8 4,144.0
Average common shares outstanding 3,805.2 4,061.9 4,118.0
Diluted average common shares outstanding 3,837.0 4,096.2 4,134.2
Book value per common share
2
$ 41.89 43.32 39.71
Tangible book value
per common share
2, 3
34.89 36.35 32.99
SELECTED EQUITY DATA (PERIOD-END)
Total equity 181
,875 190,110 185,712
Common stockholders’ equity 160,614 168,331 164,570
Tangible common equity
3
133,752 141,254 136,727
PERFORMANCE RATIOS
Return on average assets
(ROA)
4
0.70% 1.11 0.17
Return on average equity (ROE)
5
7.5 12.0 1.1
Return on average tangible common equity (ROTCE)
3
9.0 14.3 1.3
Efficiency ratio
6
78 69 78
SELECTED BALANCE SHEET DATA (AVERAGE)
Loans $ 929,820 864,288 941,788
Assets 1,894,309 1,941,905 1,941,709
Deposits 1,424,269 1,437,812 1,376,011
SELECTED BALANCE SHEET DATA (PERIOD-END)
Debt securities 496,808 537,531 501,207
Loans 955,871 895,394 887,637
Allowance for loan losses 12,985 12,490 18,516
Assets 1,881,016 1,948,068 1,952,911
Deposits 1,383,985 1,482,479 1,404,381
OTHER METRICS
Common Equity Tier 1 (CET1) ratio
7
10.60% 11.35 11.59
Market capitalization $ 158
,298 186,441 125,066
Headcount (#) (period-end) 238,698
249,435 268,531
1. Pre-tax pre-provision profit (PTPP) is total revenue
less noninterest expense. Management believes that PTPP is a useful financial measure because it enables investors and others to assess the Company’s ability to
generate capital to cover credit losses through a credit cycle.
2. Book value per common share is common stockholders’ equity divided by common shares outstanding. Tangible book value per common share is tangible common equity divided by common shares outstanding.
3. Tangible common equity, tangible book value per common share, and return on average tangible common equity are non-GAAP financial measures. For additional information, including a corresponding reconciliation to
GAAP financial measures, see the “Financial Review – Capital Management – Tangible Common Equity” section in this Report.
4. Represents Wells Fargo net income divided by average assets.
5. Represents Wells Fargo net income applicable to common stock divided by average common stockholders’ equity.
6. The efficiency ratio is noninterest expense divided by total revenue (net interest income and noninterest income).
7. Represents our Common Equity Tier 1 (CET1) ratio calculated under the Standardized Approach, which is our binding CET1 ratio. For additional information, see the “Financial Review – Capital Management” section and
Note 25 (Regulatory Capital Requirements and Other Restrictions) to Financial Statements in this Report.
Wells Fargo & Company 2022 Financial Report
Financial Review
2
Overview
7
Earnings Performance
25
Balance Sheet Analysis
27
Off-Balance Sheet Arrangements
28
Risk Management
52
Capital Management
58
Regulatory Matters
61
Critical Accounting Policies
65
Current Accounting Developments
67
Forward-Looking Statements
69
Risk Factors
Controls and Procedures
83
Disclosure Controls and Procedures
83
Internal Control Over Financial Reporting
83
Management’s Report on Internal Control over
Financial Reporting
84
Report of Independent Registered Public
Accounting Firm (KPMG LLP, Charlotte, NC,
Auditor Firm ID: 185)
Financial Statements
85
Consolidated Statement of Income
86
Consolidated Statement of Comprehensive
Income
87
Consolidated Balance Sheet
88
Consolidated Statement of Changes in Equity
90
Consolidated Statement of Cash Flows
Notes to Financial Statements
91 1
Summary of Significant Accounting Policies
103 2
Trading Activities
104
3
Available-for-Sale and Held-to-Maturity Debt Securities
110
4
Equity Securities
112
5
Loans and Related Allowance for Credit Losses
125
6
Mortgage Banking Activities
127
7
Intangible Assets and Other Assets
128
8
Leasing Activity
130
9
Deposits
131
10
Long-Term Debt
133
11
Preferred Stock
135
12
Common Stock and Stock Plans
137
13
Legal Actions
140
14
Derivatives
148
15
Fair Values of Assets and Liabilities
158
16
Securitizations and Variable Interest Entities
163
17
Guarantees and Other Commitments
166
18
Pledged Assets and Collateral
169
19
Operating Segments
171
20
Revenue and Expenses
174
21
Employee Benefits
179
22
Income Taxes
181
23
Earnings and Dividends Per Common Share
182
24
Other Comprehensive Income
184
25
Regulatory Capital Requirements and Other Restrictions
186
26
Parent-Only Financial Statements
188 Report of Independent Registered Public
Accounting Firm
191 Quarterly Financial Data
192 Glossary of Acronyms
Wells Fargo & Company 1

This Annual Report, including the Financial Review and the Financial Statements and related Notes, contains forward-looking statements,
which may include forecasts of our financial results and condition, expectations for our operations and business, and our assumptions for those
forecasts and expectations. Do not unduly rely on forward-looking statements. Actual results may differ materially from our forward-looking
statements due to several factors. Factors that could cause our actual results to differ materially from our forward-looking statements are
described in this Report, including in the “Forward-Looking Statements” section, and in the “Risk Factors” and “Regulation and Supervision”
sections of our Annual Report on Form 10-K for the year ended December 31, 2022 (2022 Form 10-K).
When we refer to “Wells Fargo,” “the Company,” “we,” “our,” or “us” in this Report, we mean Wells Fargo & Company and Subsidiaries
(consolidated). When we refer to the “Parent,” we mean Wells Fargo & Company. See the “Glossary of Acronyms” for definitions of terms used
throughout this Report.
Financial Review
Overview
Wells Fargo & Company is a leading financial services company
that has approximately $1.9 trillion in assets, proudly serves one
in three U.S. households and more than 10% of small businesses
in the U.S., and is a leading middle market banking provider i n the
U.S. We provide a diversified set of banking, investment and
mortgage products and services, as well as consumer and
commercial finance, through our four reportable operating
segments: Consumer Banking and Lending, Commercial Banking,
Corporate and Investment Banking, and Wealth and Investment
Management. Wells Fargo ranked No. 41 on Fortune’s 2022
rankings of America’s largest corporations. We ranked fourth i n
assets and third in the market value of our common stock among
all U.S. banks at December 31, 2022 .
Wells Fargo’s top priority remains building a risk and control
infrastructure appropriate for its size and complexity. The
Company is subject to a number of consent orders and other
regulatory actions, which may require the Company, among
other things, to undertake certain changes to its business,
operations, products and services, and risk management
practices. Addressing these regulatory actions is expected to
take multiple years, and we are likely to experience issues or
delays along the way in satisfying their requirements. Issues o r
delays with one regulatory action could affect our progress on
others, and failure to satisfy the requirements of a regulator y
action on a timely basis could result in additional penalties,
business restrictions, enforcement actions, and other negative
consequences, which could be significant. While we still have
significant work to do and have not yet satisfied certain aspec ts
of these regulatory actions, the Company is committed to
devoting the resources necessary to operate with strong
business practices and controls, maintain the highest level of
integrity, and have an appropriate culture in place.
Federal Reserve Board Consent Order Regarding
Governance Oversight and Compliance and Operational
Risk Management
On February 2, 2018, the Company entered into a consent order
with the Board of Governors of the Federal Reserve System
(FRB). As required by the consent order, the Company’s Board of
Directors (Board) submitted to the FRB a plan to further enhance
the Board’s governance and oversight of the Company, and the
Company submitted to the FRB a plan to further improve the
Company’s compliance and operational risk management
program. The Company continues to engage with the FRB as the
Company works to address the consent order provisions. The
consent order also requires the Company, following the FRB’s
acceptance and approval of the plans and the Company’s
adoption and implementation of the plans, to complete an initial
third-party review of the enhancements and improvements
provided for in the plans. Until this third-party review is complete
and the plans are approved and implemented to the satisfaction
of the FRB, the Company’s total consolidated assets as defined
under the consent order will be limited to the level as of
December 31, 2017. Compliance with this asset cap is measured
on a two-quarter daily average basis to allow for management of
temporary fluctuations. After removal of the asset cap, a second
third-party review must also be conducted to assess the efficacy
and sustainability of the enhancements and improvements.
Consent Orders with the Consumer Financial Protection
Bureau and Office of the Comptroller of the Currency
Regarding Compliance Risk Management Program,
Automobile Collateral Protection Insurance Policies, and
Mortgage Interest Rate Lock Extensions
On April 20, 2018, the Company entered into consent orders
with the Consumer Financial Protection Bureau (CFPB) and the
Office of the Comptroller of the Currency (OCC) to pay an
aggregate of $1 billion in civil money penalties to resolve matters
regarding the Company’s compliance risk management program
and past practices involving certain automobile collateral
protection insurance (CPI) policies and certain mortgage interest
rate lock extensions. As required by the consent orders, the
Company submitted to the CFPB and OCC an enterprise-wide
compliance risk management plan and a plan to enhance the
Company’s internal audit program with respect to federal
consumer financial law and the terms of the consent orders. In
addition, as required by the consent orders, the Company
submitted for non-objection plans to remediate customers
affected by the automobile collateral protection insurance and
mortgage interest rate lock matters, as well as a plan for the
management of remediation activities conducted by the
Company. The Company continues to work to address the
provisions of the consent orders. On September 9, 2021, the
OCC assessed a $250 million civil money penalty against the
Company related to insufficient progress in addressing
requirements under the OCC’s April 2018 consent order and loss
mitigation activities in the Company’s Home Lending business.
On December 20, 2022, the CFPB modified its consent order to
clarify how it would terminate.
Consent Order with the OCC Regarding Loss Mitigation
Activities
On September 9, 2021, the Company entered into a consent
order with the OCC requiring the Company to improve the
execution, risk management, and oversight of loss mitigation
activities in its Home Lending business. In addition, the consent
order restricts the Company from acquiring certain third-party
Wells Fargo & Company 2

residential mortgage servicing and limits transfers of certain
mortgage loans requiring customer remediation out of the
Company’s mortgage servicing portfolio until remediation is
provided.
Consent Order with the CFPB Regarding Automobile
Lending, Consumer Deposit Accounts, and Mortgage
Lending
On December 20, 2022, the Company entered into a consent
order with the CFPB requiring the Company to provide customer
remediation for multiple matters related to automobile lending,
consumer deposit accounts, and mortgage lending; maintain
practices designed to ensure auto lending customers receive
refunds for the unused portion of certain guaranteed automobile
protection agreements; comply with certain business practice
requirements related to consumer deposit accounts; and pay a
$1.7 billion civil penalty to the CFPB. The required actions related
to many of these matters were already substantially complete at
the time we entered into the consent order, and the consent
order lays out a path to termination after the Company
completes the remainder of the required actions.
Retail Sales Practices Matters
In September 2016, we announced settlements with the CFPB,
the OCC, and the Office of the Los Angeles City Attorney, and
entered into related consent orders with the CFPB and the OCC,
in connection with allegations that some of our retail customers
received products and services they did not request. As a result, it
remains a priority to rebuild trust through a comprehensive
action plan that includes making things right for our customers,
employees, and other stakeholders, and building a better
Company for the future. On September 8, 2021, the CFPB
consent order regarding retail sales practices expired.
For additional information regarding retail sales practices
matters, including related legal and regulatory risk, see the “Risk
Factors” section and Note 13 (Legal Actions) to Financial
Statements in this Report.
Customer Remediation Activities
Our priority of rebuilding trust has included an effort to identify
areas or instances where customers may have experienced
financial harm, provide remediation as appropriate, and
implement additional operational and control procedures. We are
working with our regulatory agencies in this effort.
We have accrued for the probable and estimable costs
related to our customer remediation activities, which amounts
may change based on additional facts and information, as well as
ongoing reviews and communications with our regulators. As our
ongoing reviews continue and as we continue to strengthen our
risk and control infrastructure, we have identified and may in the
future identify additional items or areas of potential concern. To
the extent issues are identified, we will continue to assess any
customer harm and provide remediation as appropriate. We have
previously disclosed key areas of focus as part of these activities.
For additional information regarding accruals for customer
remediation, see the “Expenses” section in Note 20 (Revenue and
Expenses) to Financial Statements in this Report, and for
additional information regarding these activities, including
related legal and regulatory risk, see the “Risk Factors” section
and Note 13 (Legal Actions) to Financial Statements in this
Report.
Recent Developments
LIBOR Transition
The London Interbank Offered Rate (LIBOR) is a widely
referenced benchmark rate that seeks to estimate the cost at
which banks can borrow on an unsecured basis from other banks.
On March 5, 2021, the United Kingdom’s Financial Conduct
Authority and ICE Benchmark Administration, the administrator
of LIBOR, announced that certain settings of LIBOR would no
longer be published on a representative basis after December 31,
2021, and the most commonly used U.S. dollar (USD) LIBOR
settings would no longer be published on a representative basis
after June 30, 2023. Central banks in various jurisdictions
convened committees to identify replacement rates to facilitate
the transition away from LIBOR. The committee convened by the
Federal Reserve in the United States, the Alternative Reference
Rates Committee (ARRC), recommended the Secured Overnight
Financing Rate (SOFR) as the replacement rate for USD LIBOR.
In first quarter 2022, the Adjustable Interest Rate (LIBOR)
Act (the LIBOR Act) was enacted into U.S. federal law to provide
a statutory framework to replace LIBOR with a benchmark rate
based on SOFR in U.S. law contracts that do not have fallback
provisions or that have fallback provisions resulting in a
replacement rate based on LIBOR. The FRB adopted a final rule
implementing the LIBOR Act on December 16, 2022, which will
become effective on February 27, 2023. We expect that the
LIBOR Act will transition certain of our legacy USD LIBOR
contracts that do not have appropriate fallback provisions to the
applicable SOFR-based replacement rates specified in the FRB’s
final rule.
We no longer offer new contracts referencing LIBOR, subject
to limited exceptions based on regulatory guidance. During 2022,
we executed certain LIBOR transition activities to enhance our
operational readiness such as the development of new
alternative reference rate products, model and system updates,
and employee training.
For certain contracts, including commercial credit facilities
and related derivatives, we continue to proactively engage with
our clients and contract parties to replace LIBOR with SOFR-
based rates or other alternative reference rates in advance of the
June 30, 2023 cessation date.
Following June 30, 2023, we expect substantially all of our
consumer loans, commercial credit facilities, debt securities,
derivatives, and long-term debt indexed to USD LIBOR to
transition to SOFR-based or other alternative reference rates in
accordance with existing fallback provisions or the LIBOR Act.
For additional information regarding the risks and potential
impact of LIBOR or any other referenced financial metric being
significantly changed, replaced or discontinued, see the “Risk
Factors” section in this Report.
Wells Fargo & Company 3
Overview (continued)
Financial Performance
In 2022, we generated $13.2 billion of net income and diluted
earnings per common share (EPS) of $3.14, compared with
$21.5 billion of net income and diluted EPS of $4.95 in 2021.
Financial performance for 2022, compared with 2021, included
the following:
Credit quality reflected the following:
• total revenue decreased due to lower net gains from equity
securities, mortgage banking, and investment advisory and
other asset-based fee income, partially offset by higher net
interest income;
• provision for credit losses increased reflecting loan growth
and a less favorable economic environment;
• noninterest expense increased due to higher operating
losses, partially offset by lower personnel expense, and
professional and outside services expense;
• average loans increased driven by loan growth across both
our commercial and consumer loan portfolios; and
• average deposits decreased driven by reductions in
Corporate and Investment Banking, Commercial Banking,
Wealth and Investment Management, and Corporate,
partially offset by growth in Consumer Banking and Lending.
Capital and Liquidity
We maintained a strong capital position in 2022. Total equity of
$181.9 billion at December 31, 2022, decreased compared with
$190.1 billion at December 31, 2021, driven by a decrease in
accumulated other comprehensive income due to net unrealized
losses on available-for-sale (AFS) debt securities. Our liquidity
and regulatory capital ratios remained strong at December 31,
2022, including:
• our Common Equity Tier 1 (CET1) ratio was 10.60% under
the Standardized Approach (our binding ratio), which
continued to exceed the regulatory minimum and buffers of
9.20%;
• our total loss absorbing capacity (TLAC) as a percentage of
total risk-weighted assets was 23.27%, compared with the
regulatory minimum of 21.50%; and
• our liquidity coverage ratio (LCR) was 122%, which
continued to exceed the regulatory minimum of 100%.
See the “Capital Management” and the “Risk Management –
Asset/Liability Management – Liquidity Risk and Funding”
sections in this Report for additional information regarding our
capital and liquidity, including the calculation of our regulatory
capital and liquidity amounts.
Credit Quality
• The allowance for credit losses (ACL) for loans of
$13.6 billion at December 31, 2022, decreased $179 million
from December 31, 2021, reflecting reduced uncertainty
around the economic impact of the COVID-19 pandemic on
our loan portfolio. This decrease was partially offset by loan
growth and a less favorable economic environment.
• Our provision for credit losses for loans was $1.5 billion in
2022, compared with $(4.2) billion in 2021, reflecting loan
growth and a less favorable economic environment.
• The allowance coverage for total loans was 1.42% at
December 31, 2022, compared with 1.54% at December 31,
2021.
• Commercial portfolio net loan charge-offs were $79 million,
or 1 basis point of average commercial loans, in 2022,
compared with net loan charge-offs of $295 million, or
6 basis points, in 2021, driven by lower losses in our
commercial and industrial and commercial real estate
mortgage portfolios.
• Consumer portfolio net loan charge-offs were $1.5 billion, or
39 basis points of average consumer loans, in 2022,
compared with net loan charge-offs of $1.3 billion, or
33 basis points, in 2021, predominantly due to higher losses
in our auto portfolio.
• Nonperforming assets (NPAs) of
$5.8 billion
at
December 31, 2022
, decreased
$1.6 billion
, or
21%, from
December 31, 2021
, driven by improved credit quality across
our commercial loan portfolios, and a decrease in residential
mortgage nonaccrual loans
primarily
due to sustained
payment performance of borrowers after exiting COVID-19
-
related accommodation programs. NPAs represented
0.60%
of total loans at
December 31, 2022
.
Wells Fargo & Company 4
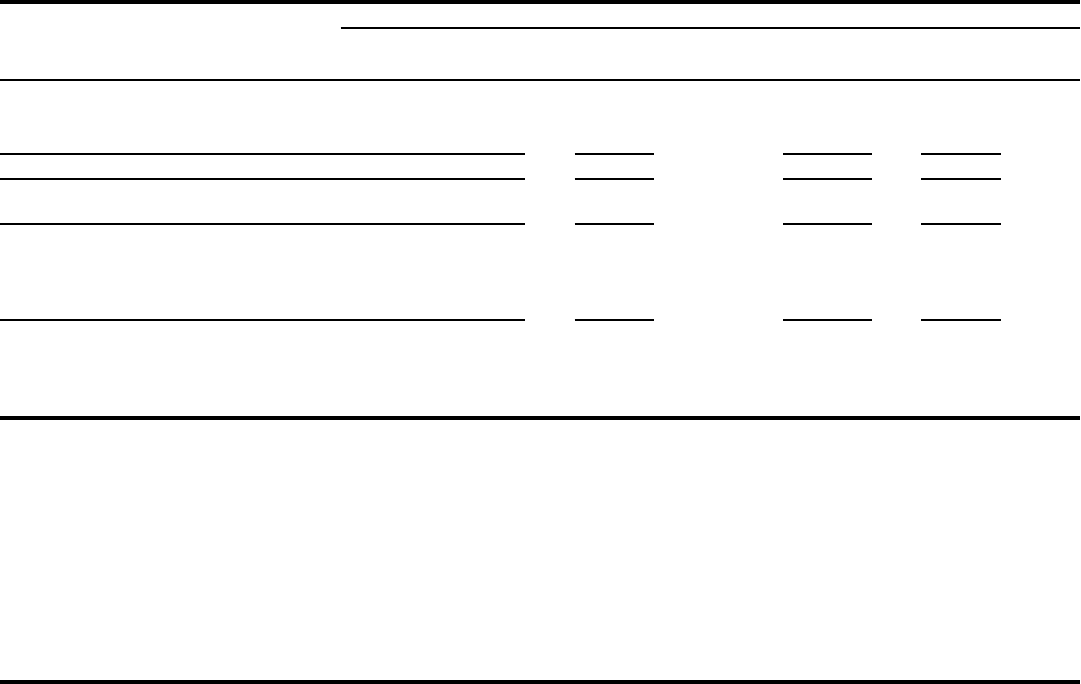
Table 1 presents a three-year summary of selected financial
data and Table 2 presents selected ratios and per common share
data.
Table 1: Summary of Selected Financial Data
Year ended December 31,
(in millions, except per share amounts) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Income statement
Net interest income $ 44,950 35,779 9,171 26 % $ 39,956 (4,177) (10)%
Noninterest income 28,835 42,713 (13,878) (32) 34,308 8,405 24
Total revenue 73,785 78,492 (4,707) (6) 74,264 4,228 6
Net charge-offs 1,609 1,582 27 2 3,370 (1,788) (53)
Change in the allowance for credit losses (75) (5,737) 5,662 99 10,759 (16,496) NM
Provision for credit losses 1,534 (4,155) 5,689 137 14,129 (18,284) NM
Noninterest expense 57,282 53,831 3,451 6 57,630 (3,799) (7)
Net income before noncontrolling interests 12,882 23,238 (10,356) (45) 3,662 19,576 535
Less: Net income from noncontrolling interests (300) 1,690 (1,990) NM 285 1,405 493
Wells Fargo net income 13,182 21,548 (8,366) (39) 3,377 18,171 538
Earnings per common share 3.17 4.99 (1.82) (36) 0.43 4.56 NM
Diluted earnings per common share 3.14 4.95 (1.81) (37) 0.43 4.52 NM
Dividends declared per common share 1.10 0.60 0.50 83 1.22 (0.62) (51)
Balance sheet (at year end)
Debt securities 496,808 537,531 (40,723) (8) 501,207 36,324 7
Loans 955,871 895,394 60,477 7 887,637 7,757 1
Allowance for loan losses
12,985 12,490 495 4 18,516 (6,026) (33)
Equity securities 64,414 72,886 (8,472) (12) 60,008 12,878 21
Assets 1,881,016 1,948,068 (67,052) (3) 1,952,911 (4,843) —
Deposits 1,383,985 1,482,479 (98,494) (7) 1,404,381 78,098 6
Long-term debt 174,870 160,689 14,181 9 212,950 (52,261) (25)
Common stockholders’ equity 160,614 168,331 (7,717) (5) 164,570 3,761 2
Wells Fargo stockholders’ equity 179,889 187,606 (7,717) (4) 184,680 2,926 2
Total equity 181,875 190,110 (8,235) (4) 185,712 4,398 2
NM – Not meaningful
Wells Fargo & Company 5

Table 2: Ratios and Per Common Share Data
Year ended December 31,
2022 2021 2020
Performance ratios
Return on average assets (ROA) (1)
0.70%
1.11
0.17
Return on average equity (ROE) (2)
7.5
12.0
1.1
(3) Return on average tangible common equity (ROTCE)
9.0
14.3
1.3
(4) Efficiency ratio
78
69
78
(5) Capital and other metrics
At year end:
Wells Fargo common stockholders’ equity to assets
8.54
8.64
8.43
Total equity to assets
9.67
9.76
9.51
Risk-based capital ratios and components:
Standardized Approach:
Common Equity Tier 1 (CET1)
10.60
11.35
11.59
Tier 1 capital
12.11
12.89
13.25
Total capital
14.82
15.84
16.47
Risk-weighted assets (RWAs) (in billions)
$
1,259.9
1,239.0
1,193.7
Advanced Approach:
Common Equity Tier 1 (CET1)
12.00%
12.60
11.94
Tier 1 capital
13.72
14.31
13.66
Total capital
15.94
16.72
16.14
Risk-weighted assets (RWAs) (in billions)
$
1,112.3
1,116.1
1,158.4
Tier 1 leverage ratio
8.26%
8.34
8.32
Supplementary Leverage Ratio (SLR)
6.86
6.89
8.05
Total Loss Absorbing Capacity (TLAC) Ratio (6)
23.27
23.03
25.74
Liquidity Coverage Ratio (LCR) (7)
122
118
133
Average balances:
Average Wells Fargo common stockholders’ equity to average assets
8.51
8.73
8.43
Average total equity to average assets
9.67
9.85
9.51
Per common share data
Dividend payout ratio (8)
35.0
12.1
283.7
Book value (9)
$
41.89
43.32
39.71
Overview (continued)
(1) Represents Wells Fargo net income divided by average assets.
(2) Represents Wells Fargo net income applicable to common stock divided by average common stockholders’ equity.
(3) Tangible common equity is a non-GAAP financial measure and represents total equity less preferred equity, noncontrolling interests, goodwill, certain identifiable intangible assets (other than
mortgage servicing rights) and goodwill and other intangibles on investments in consolidated portfolio companies, net of applicable deferred taxes. The methodology of determining tangible
common equity may differ among companies. Management believes that return on average tangible common equity, which utilizes tangible common equity, is a useful financial measure because it
enables management, investors, and others to assess the Company’s use of equity. For additional information, including a corresponding reconciliation to generally accepted accounting principles
(GAAP) financial measures, see the “Capital Management – Tangible Common Equity” section in this Report.
(4) The efficiency ratio is noninterest expense divided by total revenue (net interest income and noninterest income).
(5) See the “Capital Management” section and Note 25 (Regulatory Capital Requirements and Other Restrictions) to Financial Statements in this Report for additional information.
(6) Represents TLAC divided by risk-weighted assets (RWAs), which is our binding TLAC ratio, determined by using the greater of RWAs under the Standardized and Advanced Approaches.
(7) Represents average high-quality liquid assets divided by average projected net cash outflows, as each is defined under the LCR rule.
(8) Dividend payout ratio is dividends declared per common share as a percentage of diluted earnings per common share.
(9) Book value per common share is common stockholders’ equity divided by common shares outstanding.
Wells Fargo & Company 6

Earnings Performance
Wells Fargo net income for 2022 was $13.2 billion ($3.14 diluted
EPS), compared with $21.5 billion ($4.95 diluted EPS) in 2021.
Net income decreased in 2022, compared with 2021, due to a
$13.9 billion decrease in noninterest income, a $5.7 billion
increase in provision for credit losses, and a $3.5 billion increase
in noninterest expense, partially offset by a $9.2 billion increase
in net interest income, a $3.5 billion decrease in income tax
expense, and a $2.0 billion decrease in net income from
noncontrolling interests.
For a discussion of our 2021 financial results, compared with
2020, see the “Earnings Performance” section of our Annual
Report on Form 10-K for the year ended December 31, 2021.
Net Interest Income
Net interest income is the interest earned on debt securities,
loans (including yield-related loan fees) and other interest-
earning assets minus the interest paid on deposits, short-term
borrowings and long-term debt. The net interest margin is the
average yield on earning assets minus the average interest rate
paid for deposits and our other sources of funding.
Net interest income and the net interest margin in any one
period can be significantly affected by a variety of factors
including the mix and overall size of our earning assets portfolio
and the cost of funding those assets. In addition, variable sources
of interest income, such as loan fees, periodic dividends, and
collection of interest on nonaccrual loans, can fluctuate from
period to period.
Net interest income and net interest margin increased in
2022, compared with 2021, due to the impact of higher interest
rates on earning assets, higher loan balances, and lower
mortgage-backed securities (MBS) premium amortization,
partially offset by lower interest income from Paycheck
Protection Program (PPP) loans and loans purchased from
Government National Mortgage Association (GNMA) loan
securitization pools, and higher expenses for interest-bearing
deposits and long-term debt.
Table 3 presents the individual components of net interest
income and net interest margin. Net interest income and net
interest margin are presented on a taxable-equivalent basis in
Table 3 to consistently reflect income from taxable and tax-
exempt loans and debt and equity securities based on a 21%
federal statutory tax rate for the periods ended December 31,
2022, 2021 and 2020.
Wells Fargo & Company 7
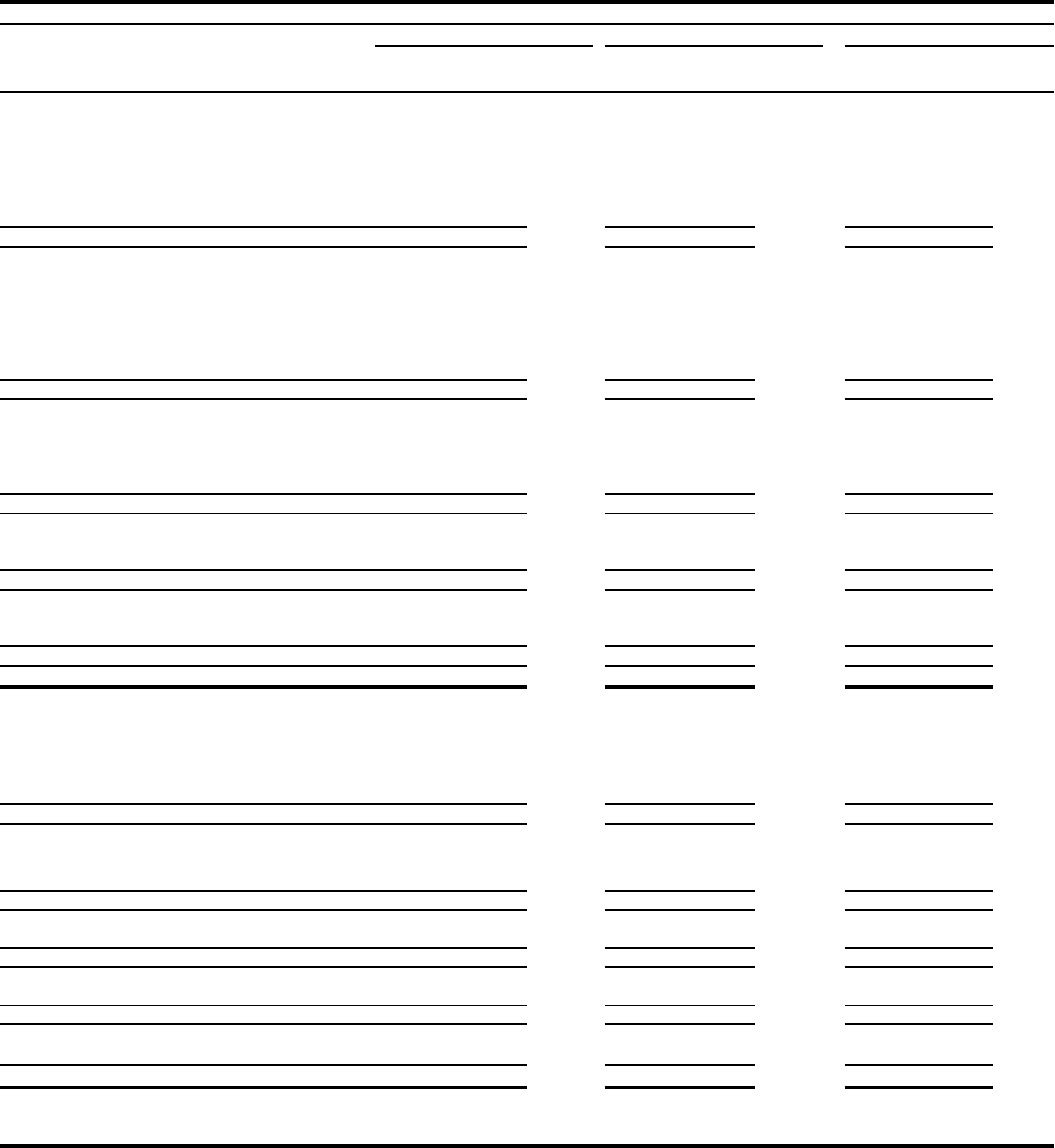
Table 3: Average Balances, Yields and Rates Paid (Taxable-Equivalent Basis) (1)
Year ended December 31,
2022 2021 2020
(in millions)
Average
balance
Interest
income/
expense
Interest
rates
Average
balance
Interest
income/
expense
Interest
rates
Average
balance
Interest
income/
expense
Interest
rates
Assets
Interest-earning deposits with banks $ 145,802 2,245 1.54 % $ 236,281 314 0.13 % $ 186,386 547 0.29 %
Federal funds sold and securities purchased under resale agreements 62,137 859 1.38 69,720 14 0.02 82,798 393 0.47
Debt securities:
Trading debt securities 91,515 2,490 2.72 88,282 2,107 2.39 94,731 2,544 2.69
Available-for-sale debt securities 141,404 3,167 2.24 189,237 2,924 1.55 229,077 5,248 2.29
Held-to-maturity debt securities 296,540 6,480 2.19 245,304 4,589 1.87 173,505 3,841 2.21
Total debt securities
529,459 12,137
2.29
522,823 9,620
1.84
497,313 11,633
2.34
Loans held for sale (2)
13,900 513
3.69
27,554 865
3.14
27,493 947
3.45
Loans:
Commercial and industrial – U.S. 291,996 11,293 3.87 252,025 6,526 2.59 281,080 7,912 2.82
Commercial and industrial – Non-U.S. 80,033 2,681 3.35 71,114 1,448 2.04 66,915 1,673 2.50
Commercial real estate mortgage 131,304 4,974 3.79 121,638 3,276 2.69 122,482 3,842 3.14
Commercial real estate construction 21,510 991 4.61 21,589 667 3.09 21,608 760 3.52
Lease financing 14,555 607 4.17 15,519 692 4.46 17,801 877 4.93
Total commercial loans 539,398 20,546 3.81 481,885 12,609 2.62 509,886 15,064 2.95
Residential mortgage – first lien 249,985 7,912 3.17 249,862 7,903 3.16 288,105 9,661 3.35
Residential mortgage – junior lien 14,703 729 4.95 19,710 818 4.15 26,700 1,185 4.44
Credit card 41,275 4,752 11.51 35,471 4,086 11.52 37,093 4,315 11.63
Auto 55,429 2,366 4.27 51,576 2,317 4.49 48,362 2,379 4.92
Other consumer 29,030 1,489 5.13 25,784 962 3.73 31,642 1,719 5.43
Total consumer loans 390,422 17,248 4.42 382,403 16,086 4.21 431,902 19,259 4.46
Total loans (2) 929,820 37,794 4.06 864,288 28,695 3.32 941,788 34,323 3.64
Equity securities 30,575 708 2.31 31,946 608 1.91 28,950 557 1.92
Other 13,275 204 1.54 10,052 6 0.06 7,505 14 0.18
Total interest-earning assets $ 1,724,968 54,460 3.16 % $ 1,762,664 40,122 2.28 % $ 1,772,233 48,414 2.73 %
Cash and due from banks 25,817 — 24,562 — 21,676 —
Goodwill 25,177 — 26,087 — 26,387 —
Other 118,347 — 128,592 — 121,413 —
Total noninterest-earning assets $ 169,341 — 179,241 — 169,476 —
Total assets $ 1,894,309 54,460 1,941,905 40,122 1,941,709 48,414
Liabilities
Deposits:
Demand deposits $ 432,745 1,356 0.31 % $ 450,131 127 0.03 % $ 98,182 184 0.19 %
Savings deposits 433,415 406 0.09 423,221 124 0.03 744,226 1,492 0.20
Time deposits 33,148 449 1.36 36,519 122 0.33 81,674 892 1.09
Deposits in non-U.S. offices 19,191 138 0.72 28,297 15 0.05 39,260 236 0.60
Total interest-bearing deposits 918,499 2,349 0.26 938,168 388 0.04 963,342 2,804 0.29
Short-term borrowings:
Federal fu nds p urchased and securities sold under agreements t o
repurchase 24,553 407 1.66 35,245 8 0.02 58,971 276 0.47
Other short-term borrowings 15,257 175 1.15 12,020 (48) (0.41) 11,235 (25) (0.22)
Total short-term borrowings 39,810 582 1.46 47,265 (40) (0.09) 70,206 251 0.36
Long-term debt 157,742 5,505 3.49 178,742 3,173 1.78 224,587 4,471 1.99
Other liabilities 34,126 638 1.87 28,809 395 1.37 28,435 438 1.54
Total interest-bearing liabilities $ 1,150,177 9,074 0.79 % $ 1,192,984 3,916 0.33 % $ 1,286,570 7,964 0.62 %
Noninterest-bearing demand deposits 505,770 — 499,644 — 412,669 —
Other noninterest-bearing liabilities 55,138 — 58,058 — 57,781 —
Total noninterest-bearing liabilities $ 560,908 — 557,702 — 470,450 —
Total liabilities $ 1,711,085 9,074 1,750,686 3,916 1,757,020 7,964
Total equity 183,224 — 191,219 — 184,689 —
Total liabilities and equity $ 1,894,309 9,074 1,941,905 3,916 1,941,709 7,964
(3) Interest rate spread on a taxable-equivalent basis 2.37 % 1.95 % 2.11 %
Net interest margin and net interest income on a taxable-equivalent
basis (3) $ 45,386 2.63 % $ 36,206 2.05 % $ 40,450 2.28 %
Earnings Performance (continued)
(1) The a verage b alance a mounts r epresent amortized costs, except for certain h eld-to-maturity debt securities, which exclude u namortized basis a djustments r elated to t he t ransfer of t hose secu rities
from available-for-sale d ebt securities. The int erest rates a re b ased on int erest income or expense a mounts for the p eriod and are a nnualized. Interest rates a nd amounts inclu de t he effect s of h edge
and risk management activities a ssociated with the r espective a sset and liability categories.
(2) Nonaccrual loans and any related income are included in their respective loan categories.
(3) Includes taxable-equivalent adjustments of $436 million, $427 million and $494 million for the years ended December 31, 2022, 2021 and 2020, respectively, predominantly related to tax-exempt
income on certain loans and securities.
Wells Fargo & Company 8
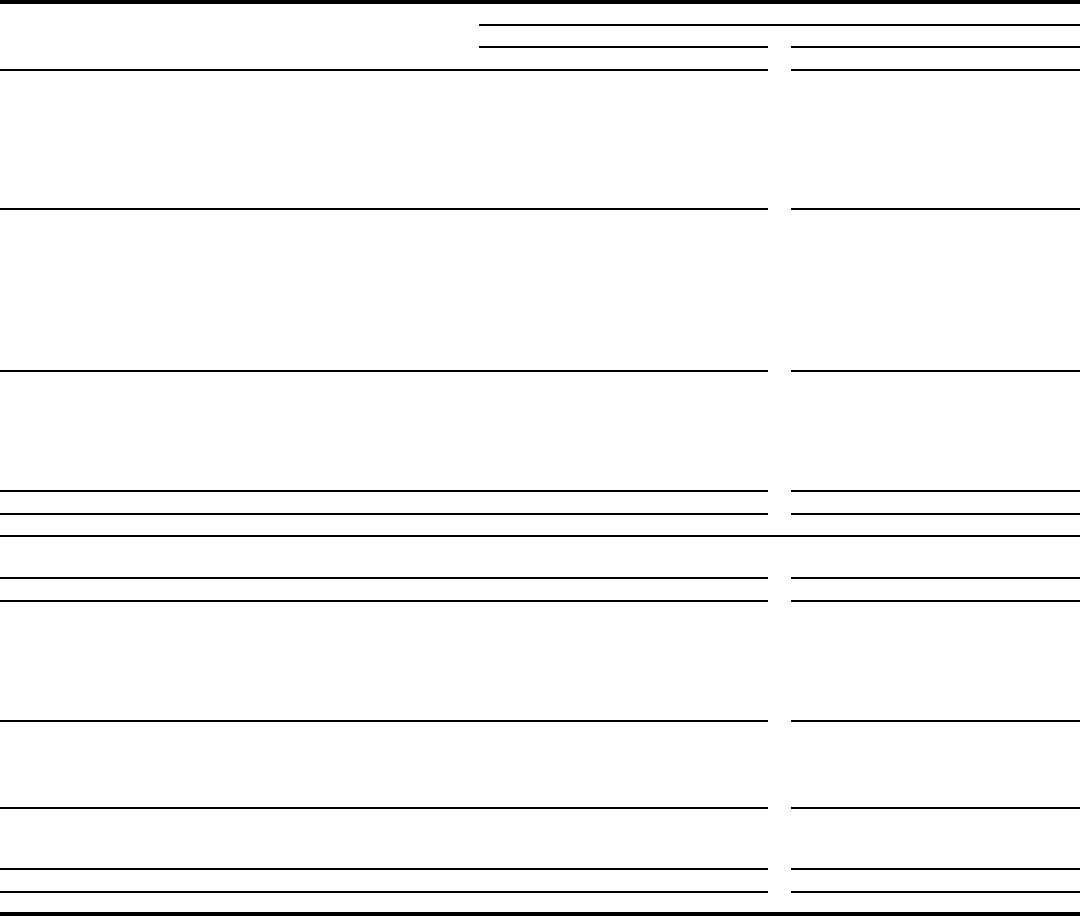
Table 4 allocates the changes in net interest income on a
taxable-equivalent basis to changes in either average balances or
average rates for both interest-earning assets and interest-
bearing liabilities. Because of the numerous simultaneous volume
and rate changes during any period, it is not possible to precisely
Table 4: Analysis of Changes in Net Interest Income
allocate such changes between volume and rate. For this table,
changes that are not solely due to either volume or rate are
allocated to these categories on a pro-rata basis based on the
absolute value of the change due to average volume and average
rate.
Year ended December 31,
2022 vs. 2021 2021 vs. 2020
(in millions) Volume Rate Total Volume Rate Total
Increase (decrease) in interest income:
Interest-earning deposits with banks $ (162) 2,093 1,931 119 (352) (233)
Federal funds sold and securities purchased under resale agreements (2) 847 845 (53) (326) (379)
Debt securities:
Trading debt securities 80 303 383 (165) (272) (437)
Available-for-sale debt securities (858) 1,101 243 (813) (1,511) (2,324)
Held-to-maturity debt securities 1,039 852 1,891 1,405 (657) 748
Total debt securities 261 2,256 2,517 427 (2,440) (2,013)
Loans held for sale (484) 132 (352) 2 (84) (82)
Loans:
Commercial and industrial – U.S. 1,158 3,609 4,767 (775) (611) (1,386)
Commercial and industrial – Non-U.S. 201 1,032 1,233 99 (324) (225)
Commercial real estate mortgage 276 1,422 1,698 (26) (540) (566)
Commercial real estate construction (2) 326 324 (1) (92) (93)
Lease financing (42) (43) (85) (106) (79) (185)
Total commercial loans 1,591 6,346 7,937 (809) (1,646) (2,455)
Residential mortgage – first lien 1 8 9 (1,232) (526) (1,758)
Residential mortgage – junior lien (230) 141 (89) (294) (73) (367)
Credit card 670 (4) 666 (188) (41) (229)
Auto 166 (117) 49 153 (215) (62)
Other consumer 132 395 527 (281) (476) (757)
Total consumer loans 739 423 1,162 (1,842) (1,331) (3,173)
Total loans 2,330 6,769 9,099 (2,651) (2,977) (5,628)
Equity securities (26) 126 100 54 (3) 51
Other 3 195 198 4 (12) (8)
Total increase (decrease) in interest income 1,920 12,418 14,338 (2,098) (6,194) (8,292)
Increase (decrease) in interest expense:
Deposits:
Demand deposits $ (5) 1,234 1,229 208 (265) (57)
Savings deposits 3 279 282 (461) (907) (1,368)
Time deposits (12) 339 327 (340) (430) (770)
Deposits in non-U.S. offices (7) 130 123 (52) (169) (221)
Total interest-bearing deposits (21) 1,982 1,961 (645) (1,771) (2,416)
Short-term borrowings:
Federal funds purchased and securities sold under agreements to repurchase (3) 402 399 (80) (188) (268)
Other short-term borrowings (10) 233 223 (2) (21) (23)
Total short-term borrowings (13) 635 622 (82) (209) (291)
Long-term debt (412) 2,744 2,332 (855) (443) (1,298)
Other liabilities 82 161 243 6 (49) (43)
Total increase (decrease) in interest expense (364) 5,522 5,158 (1,576) (2,472) (4,048)
Increase (decrease) in net interest income on a taxable-equivalent basis $ 2,284 6,896 9,180 (522) (3,722) (4,244)
Wells Fargo & Company 9

Noninterest Income
Table 5: Noninterest Income
Year ended December 31,
(in millions) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Deposit-related fees
$
5,316
5,475
(159)
(3)%
$
5,221
254
5 %
Lending-related fees
1,397
1,445
(48)
(3)
1,381
64
5
Investment advisory and other asset-based fees
9,004
11,011
(2,007)
(18)
9,863
1,148
12
Commissions and brokerage services fees
2,242
2,299
(57)
(2)
2,384
(85)
(4)
Investment banking fees
1,439
2,354
(915)
(39)
1,865
489
26
Card fees
4,355
4,175
180
4
3,544
631
18
Net servicing income
533
194
339
175
(139)
333
240
Net gains on mortgage loan originations/sales
850
4,762
(3,912)
(82)
3,632
1,130
31
Mortgage banking
1,383
4,956
(3,573)
(72)
3,493
1,463
42
Net gains from trading activities
2,116
284
1,832
645
1,172
(888)
(76)
Net gains from debt securities
151
553
(402)
(73)
873
(320)
(37)
Net gains (losses) from equity securities
(806)
6,427
(7,233)
NM
665
5,762
866
Lease income
1,269
996
273
27
1,245
(249)
(20)
Other
969
2,738
(1,769)
(65)
2,602
136
5
Total
$
28,835 42,713
(13,878)
(32) $
34,308
8,405
24
Earnings Performance (continued)
NM – Not meaningful
Full year 2022 vs. full year 2021
Deposit-related fees decreased reflecting:
• lower treasury management fees on commercial accounts
driven by a higher earnings credit rate due to an increase in
interest rates; and
• the elimination of non-sufficient funds and other fees as well
as efforts to help customers avoid overdraft fees ;
partially offset by:
• lower fee waivers as 2021 included additional
accommodations to support customers.
Lending-related fees decreased reflecting lower commercial
loan commitment fees.
Investment advisory and other asset-based fees decreased
reflecting:
• lower asset-based and trust fees due to divestitures in 2021;
and
• lower average market valuations.
For additional information on certain client investment
assets, see the “Earnings Performance – Operating Segment
Results – Wealth and Investment Management – WIM Advisory
Assets” section in this Report.
Commissions and brokerage services fees decreased driven by
lower transactional revenue.
Investment banking fees decreased due to lower market
activity.
Card fees increased reflecting higher network revenue as well as
higher interchange fees, net of rewards, driven by increased
purchase and transaction volumes.
Net servicing income increased driven by a lower decline in
residential mortgage servicing rights (MSRs) as a result of
reduced prepayment rates, partially offset by net unfavorable
hedge results due to interest rate volatility.
Net gains on mortgage loan originations/sales decreased
driven by:
• lower residential mortgage origination volumes and lower
gain on sale margins; and
• lower gains related to the resecuritization of loans we
purchased from GNMA loan securitization pools.
For additional information on servicing income and net gains
on mortgage loan originations/sales, see Note 6 (Mortgage
Banking Activities) to Financial Statements in this Report.
Net gains from trading activities increased driven by higher
commodities, foreign exchange, rates, and equities trading
revenue.
Net gains from debt securities decreased due to lower gains on
sales of corporate debt securities and agency MBS.
Net gains (losses) from equity securities decreased reflecting:
• lower unrealized gains on nonmarketable equity securities
driven by our affiliated venture capital and private equity
businesses;
• a $2.5 billion impairment of equity securities (before the
impact of noncontrolling interests) in 2022 predominantly in
our affiliated venture capital business driven by market
conditions; and
• lower realized gains on the sales of equity securities.
Lease income increased driven by a $268 million impairment in
2021 of certain rail cars in our rail car leasing business that are
used for the transportation of coal products.
Wells Fargo & Company 10
Other income decreased driven by:
• gains in 2021 on the sales of
our Corporate Trust Services
business, our student loan portfolio, and Wells Fargo Asset
Management (WFAM); and
• higher amortization due to growth in wind energy
investments (offset by benefits and credits in income tax
expense);
partially offset by:
• lower valuation losses related to the retained litigation risk
associated with shares of Visa Class B common stock that
we sold.
Noninterest Expense
Table 6: Noninterest Expense
Year ended December 31,
(in millions) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Personnel
$
34,340
35,541
(1,201)
(3)%
$
34,811
730
2 %
Technology, telecommunications and equipment
3,375
3,227
148
5
3,099
128
4
Occupancy
2,881
2,968
(87)
(3)
3,263
(295)
(9)
Operating losses
6,984
1,568
5,416
345
3,523
(1,955)
(55)
Professional and outside services
5,188
5,723
(535)
(9)
6,706
(983)
(15)
(1) Leases
750
867
(117)
(13)
1,022
(155)
(15)
Advertising and promotion
505
600
(95)
(16)
600
—
—
Restructuring charges
5
76
(71)
(93)
1,499
(1,423)
(95)
Other
3,254
3,261
(7)
—
3,107
154
5
Total
$
57,282
53,831
3,451
6
$
57,630
(3,799)
(7)
(1) Represents expenses for assets we lease to customers.
Full year 2022 vs. full year 2021
Personnel expense decreased driven by:
• lower revenue-related compensation expense; and
• the impact of divestitures and efficiency initiatives;
partially offset by:
• higher severance expense primarily in Home Lending.
Technology, telecommunications and equipment expense
increased due to higher expense for technology contracts.
Occupancy expense decreased driven by lower cleaning fees,
supplies, and equipment expense.
Operating losses increased reflecting a $5.1 billion increase in
expenses for litigation, regulatory, and customer remediation
matters primarily related to a variety of historical matters.
As previously disclosed, we have outstanding litigatio n,
regulatory, and customer remediation matters that could impact
operating losses in the coming quarters.
Professional and outside services expense decreased driven by
efficiency initiatives to reduce our spending on consultants and
contractors.
Leases expense decreased driven by lower depreciation expense
from a reduction in the size of our operating lease asset portfolio.
Advertising and promotion expense decreased due to lower
marketing and brand campaign volumes.
Income Tax Expense
Table 7: Income Tax Expense
Year ended December 31,
(in millions) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Income before income tax expense (benefit) $ 14,969 28,816 (13,847) (48)% $ 2,505 26,311 NM
Income tax expense (benefit) 2,087 5,578 (3,491) (63) (1,157) 6,735 582 %
Effective Income tax rate 13.7% 20.6 (52.1)%
NM – Not meaningful
Income tax expense for 2022, compared with 2021,
decreased primarily due to lower pre-tax income. The effective
income tax rate for 2022, compared with 2021, decreased
reflecting the impact of income tax benefits, including tax
credits, on lower pre-tax income and discrete tax benefits related
to interest on overpayments in prior years.
For additional information on income taxes, see Note 22
(Income Taxes) to Financial Statements in this Report.
Wells Fargo & Company 11

Earnings Performance (continued)
Operating Segment Results
Our management reporting is organized into four reportable
operating segments: Consumer Banking and Lending;
Commercial Banking; Corporate and Investment Banking; and
Wealth and Investment Management. All other business
activities that are not included in the reportable operating
segments have been included in Corporate. For additional
information, see Table 8 . We define our reportable operating
segments by type of product and customer segment, and their
results are based on our management reporting process. The
management reporting process measures the performance of
the reportable operating segments based on the Company’s
management structure, and the results are regularly reviewed
with our Chief Executive Officer and relevant senior
management. The management reporting process is based on
U.S. GAAP and includes specific adjustments, such as funds
transfer pricing for asset/liability management, shared revenu e
and expenses, and taxable-equivalent adjustments to
consistently reflect income from taxable and tax-exempt
sources, which allows management to assess performance
consistently across the operating segments.
Funds Transfer Pricing Corporate treasury manages a funds
transfer pricing methodology that considers interest rate risk,
liquidity risk, and other product characteristics. Operating
segments pay a funding charge for their assets and receive a
funding credit for their deposits, both of which are included in
net interest income. The net impact of the funding charges or
credits is recognized in corporate treasury.
Revenue and Expense Sharing When lines of business jointly
serve customers, the line of business that is responsible for
providing the product or service recognizes revenue or expense
with a referral fee paid or an allocation of cost to the other line of
business based on established internal revenue-sharing
agreements.
When a line of business uses a service provided by another
line of business or enterprise function (included in Corporate),
expense is generally allocated based on the cost and use of the
service provided.
Taxable-Equivalent Adjustments Taxable-equivalent
adjustments related to tax-exempt income on certain loans and
debt securities are included in net interest income, while taxable-
equivalent adjustments related to income tax credits for low-
income housing and renewable energy investments are included
in noninterest income, in each case with corresponding impacts
to income tax expense (benefit). Adjustments are included in
Corporate, Commercial Banking, and Corporate and Investment
Banking and are eliminated to reconcile to the Company’s
consolidated financial results.
Allocated Capital Reportable operating segments are allocated
capital under a risk-sensitive framework that is primarily based
on aspects of our regulatory capital requirements, and the
assumptions and methodologies used to allocate capital are
periodically assessed and revised.
Management believes that
return on allocated capital is a useful financial measure because it
enables management, investors, and others to assess a
reportable operating segment’s use of capital.
Selected Metrics We present certain financial and nonfinancial
metrics that management uses when evaluating reportable
operating segment results. Management believes that these
metrics are useful to investors and others to assess the
performance, customer growth, and trends of reportable
operating segments or lines of business.
Table 8: Management Reporting Structure
Wells Fargo & Company
Consumer
Banking a nd
Lending
• Consumer and
Small Business
Banking
• Home Lending
• Credit Card
• Auto
• Personal Lending
Commercial
Banking
• Middle Market
Banking
• Asset-Based
Lending and Leasing
Corporate a nd
Investment
Banking
• Banking
• Commercial Real
Estate
• Markets
Wealth a nd
Investment
Management
• Wells Fargo
Advisors
• The Private
Bank
Corporate
• Corporate
Treasury
• Enterprise
Functions
• Investment
Portfolio
• Affiliated venture
capital and private
equity businesses
• Non-strategic
businesses
Wells Fargo & Company 12
Table 9 and the following discussion present our results by
reportable operating segment. For additional information, see
Note 19 (Operating Segments) to Financial Statements in this
Report.
Table 9: Operating Segment Results – Highlights
(in millions)
Consumer
Banking and
Lending
Commercial
Banking
Corporate and
Investment
Banking
Wealth and
Investment
Management Corporate (1)
Reconciling
Items (2)
Consolidated
Company
Year ended December 31, 2022
Net interest income $ 27,044 7,289 8,733 3,927 (1,607) (436) 44,950
Noninterest income 8,766 3,631 6,509 10,895 609 (1,575) 28,835
Total revenue 35,810 10,920 15,242 14,822 (998) (2,011) 73,785
Provision for credit losses 2,276 (534) (185) (25) 2 — 1,534
Noninterest expense 26,277 6,058 7,560 11,613 5,774 — 57,282
Income (loss) before income tax expense (benefit) 7,257 5,396 7,867 3,234 (6,774) (2,011) 14,969
Income tax expense (benefit)
Net income (loss) before noncontrolling interests
5,441 4,030 5,878 2,422 (4,889) — 12,882
1,816 1,366 1,989 812 (1,885) (2,011) 2,087
Less: Net income (loss) from noncontrolling
interests
Net income (loss) $ 5,441 4,018 5,878 2,422 (4,577) — 13,182
— 12 — — (312) — (300)
Year ended December 31, 2021
Net interest income $ 22,807 4,960 7,410 2,570 (1,541) (427) 35,779
Noninterest income 12,070 3,589 6,429 11,776 10,036 (1,187) 42,713
Total revenue 34,877 8,549 13,839 14,346 8,495 (1,614) 78,492
Provision for credit losses (1,178) (1,500) (1,439) (95) 57 — (4,155)
Noninterest expense 24,648 5,862 7,200 11,734 4,387 — 53,831
Income (loss) before income tax expense (benefit) 11,407 4,187 8,078 2,707 4,051 (1,614) 28,816
Income tax expense (benefit)
Net income before noncontrolling interests 8,555 3,142 6,059 2,027 3,455
— 23,238
2,852 1,045 2,019 680 596 (1,614) 5,578
Less: Net income (loss) from noncontrolling
interests — 8 (3) — 1,685 — 1,690
Net income $ 8,555
3,134 6,062 2,027 1,770 — 21,548
Year ended December 31, 2020
Net interest income $ 23,378 6,134 7,509 2,988 441 (494) 39,956
Noninterest income 10,638 3,041 6,419 10,225 4,916 (931) 34,308
Total revenue 34,016 9,175 13,928 13,213 5,357 (1,425) 74,264
Provision for credit losses 5,662 3,744 4,946
249 (472) — 14,129
Noninterest expense 26,976 6,323 7,703 10,912 5,716 — 57,630
Income (loss) before income tax expense (benefit) 1,378 (892) 1,279 2,052 113 (1,425) 2,505
Income tax expense (benefit)
Net income (loss) before noncontrolling interests 1,076 (684) 949 1,538 783
— 3,662
302 (208) 330 514 (670) (1,425) (1,157)
Less: Net income (loss) from noncontrolling
interests — 5 (1) — 281 — 285
Net income (loss) $ 1,076 (689) 950 1,538 502 — 3,377
(1) All other business activities that are not included in the reportable operating segments have been included in Corporate. For additional information, see the “Corporate” section below.
(2) Taxable-equivalent adjustments related to tax-exempt income on certain loans and debt securities are included in net interest income, while taxable-equivalent adjustments related to income tax
credits for low-income housing and renewable energy investments are included in noninterest income, in each case with corresponding impacts to income tax expense (benefit). Adjustments are
included in Corporate, Commercial Banking, and Corporate and Investment Banking and are eliminated to reconcile to the Company’s consolidated financial results.
Wells Fargo & Company 13
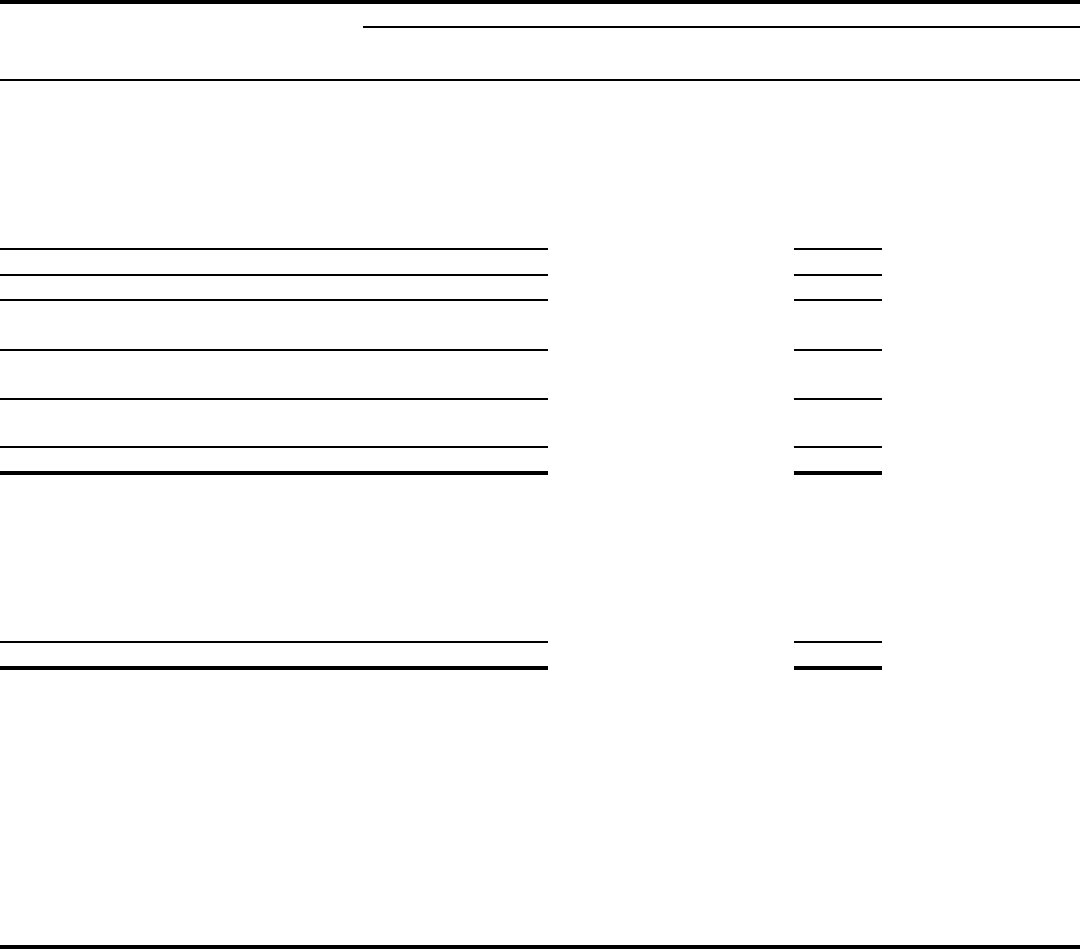
Consumer Banking and Lending offers diversified financial
products and services for consumers and small businesses with
annual sales generally up to $10 million. These financial products
and services include checking and savings accounts, credit and
debit cards as well as home, auto, personal, and small business
lending. Table 9a and Table 9b provide additional information for
Consumer Banking and Lending.
Table 9a: Consumer Banking and Lending – Income Statement and Selected Metrics
Year ended December 31,
($ in millions, unless otherwise noted) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Income Statement
Net interest income $ 27,044 22,807 4,237 19 % $ 23,378 (571) (2) %
Noninterest income:
Deposit-related fees 3,093 3,045 48 2 2,904 141 5
Card fees 4,067 3,930 137 3 3,318 612 18
Mortgage banking 1,100 4,490 (3,390) (76) 3,224 1,266 39
Other 506 605 (99) (16) 1,192 (587) (49)
Total noninterest income 8,766 12,070 (3,304) (27) 10,638 1,432 13
Total revenue 35,810 34,877 933 3 34,016 861 3
Net charge-offs 1,693 1,439 254 18 1,875 (436) (23)
Change in the allowance for credit losses 583 (2
,617)
3,200 122 3,787 (6,404) NM
Provision for credit losses 2,276 (1
,178) 3,454 293 5,662 (6,840) NM
Noninterest expense 26,277 24,648 1,629 7 26,976 (2,328) (9)
Income before income tax expense 7,257 11,407 (4,150) (36) 1,378 10,029 728
Income tax expense 1,816 2,852 (1,036) (36) 302 2,550 844
Net income $ 5,441 8,555 (3,114) (36) $ 1,076 7,479 695
Revenue by Line of Business
Consumer and Small Business Banking $ 23,421 18,958 4,463 24 $ 18,684 274 1
Consumer Lending:
Home Lending 4,221
8,154 (3,933) (48) 7,875 279 4
Credit Card 5,271 4,928 343 7 4,685 243
5
Auto 1,716 1,733 (17) (1) 1,575 158 10
Personal Lending 1,181 1,104 77 7 1,197 (93) (8)
Total revenue
$ 35,810
34,877
933 3 $ 34,016 861 3
Selected Metrics
Consumer Banking and Lending:
Return on allocated capital (1) 10.8% 17.2 1.6 %
Efficiency ratio (2) 73 71 79
Retail bank branches (#) 4,598 4,777 (4) 5,032 (5)
Digital active customers (# in millions) (3) 33.5 33.0 2 32.0 3
Mobile active customers (# in millions) (3) 28.3 27.3 4 26.0 5
Consumer and Small Business Banking:
Deposit spread (4) 2.0% 1.5 1.8 %
Debit card purchase volume ($ in billions) (5) $ 486.6 471.5 15.1 3 $ 391.9 79.6 20
Debit card purchase transactions (# in millions) (5) 9,852 9,808 — 8,792 12
(continued on following page)
Earnings Performance (continued)
14 Wells Fargo & Company
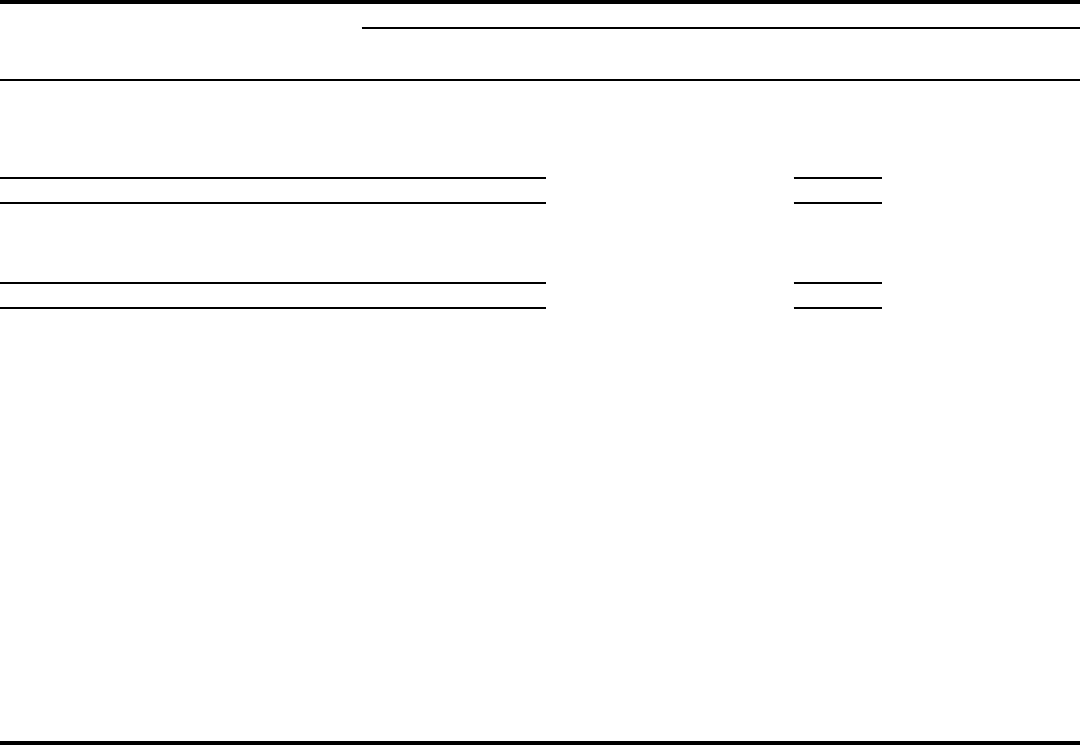
(continued from previous page)
Year ended December 31,
($ in millions, unless otherwise noted) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Home Lending:
Mortgage banking:
Net servicing income $ 368 35 333 951 % $ (160) 195 122 %
Net gains on mortgage loan originations/sales 732 4,455 (3,723) (84) 3,384 1,071 32
Total mortgage banking $ 1,100 4,490 (3,390) (76) $ 3,224 1,266 39
Originations ($ in billions):
Retail $ 64.3 138.5 (74.2) (54) $ 118.7 19.8 17
Correspondent 43.8 66.5 (22.7) (34) 104.0 (37.5) (36)
Total originations $ 108.1 205.0 (96.9) (47) $ 222.7 (17.7) (8)
% of originations held for sale (HFS) 52.5 % 64.6 73.9 %
Third-party mortgage loans serviced (period-end)
($ in billions) (6)
$ 679.2 716.8 (37.6) (5) $ 856.7 (139.9) (16)
Mortgage servicing rights (MSR) carrying value
(period-end) 9,310 6,920 2,390 35 6,125 795 13
Ratio of MSR carrying value (period-end) to third-
party mortgage loans serviced (period-end) (6)
1.37 % 0.97 0.71 %
Home lending loans 30+ days delinquency rate
(7)(8)(9)
0.31 0.39 0.64
Credit Card:
Point of sale (POS) volume ($ in billions) $ 119.1 95.3 23.8 25 $ 75.3 20.0 27
New accounts (# in thousands) 2,153 1,640 31 1,022 60
Credit card loans 30+ days delinquency rate 2.08 % 1.52 2.26 %
Credit card loans 90+ days delinquency rate 1.01 0.72 1.04
Auto:
Auto originations ($ in billions) $ 23.1
33.9 (10.8) (32) $ 22.8 11.1 49
Auto loans
30+ days delinquency rate (8) 2.64 % 1.84 1.77 %
Personal Lending:
New volume ($ in billions) $ 12.6 9.8 2.8 29 $ 7.9 1.9 24
NM – Not meaningful
(1) Return on allocated capital is segment net income (loss) applicable to common stock divided by segment average allocated capital. Segment net income (loss) applicable to common stock is segment
net income (loss) less allocated preferred stock dividends.
(2) Efficiency ratio is segment noninterest expense divided by segment total revenue (net interest income and noninterest income).
(3) Digital and mobile active customers is the number of consumer and small business customers who have logged on via a digital or mobile device, respectively, in the prior 90 days. Digital active
customers includes both online and mobile customers.
(4) Deposit spread is (i) the internal funds transfer pricing credit on segment deposits minus interest paid to customers for segment deposits, divided by (ii) average segment deposits.
(5) Debit card purchase volume and transactions reflect combined activity for both consumer and business debit card purchases.
(6) Excludes residential mortgage loans subserviced for others.
(7) Excludes residential mortgage loans insured by the Federal Housing Administration (FHA) or guaranteed by the Department of Veterans Affairs (VA) and loans held for sale.
(8) Excludes nonaccrual loans.
(9) Beginning in second quarter 2020, customer payment deferral activities instituted in response to the COVID-19 pandemic may have delayed the recognition of delinquencies for those customers
who would have otherwise moved into past due or nonaccrual status.
Full year 2022 vs. full year 2021
Revenue increased driven by:
• higher net interest income reflecting higher interest rates
and higher average deposit balances and deposit spreads;
• higher card fees reflecting higher network revenue as well as
higher interchange fees, net of rewards, driven by increased
purchase and transaction volumes; and
• higher deposit-related fees reflecting lower fee waivers as
2021 included additional accommodations to support
customers, and a higher volume of monthly account service
fees in 2022, partially offset by the elimination of non-
sufficient funds and other fees in 2022 as well as initiatives
to help customers avoid overdraft fees;
partially offset by:
• lower mortgage banking noninterest income due to lower
origination volumes and gain on sale margins, and lower
revenue related to the resecuritization of loans we
purchased from GNMA loan securitization pools.
Provision for credit losses increased reflecting loan growth, a
less favorable economic environment, and higher net charge-
offs.
Noninterest expense increased driven by:
• higher operating losses reflecting higher expenses primarily
related to a variety of historical matters, including litigation,
regulatory, and customer remediation matters; and
• higher operating costs;
partially offset by:
• lower personnel expense driven by lower revenue-related
incentive compensation in Home Lending due to lower
production and the impact of efficiency initiatives, partially
offset by higher severance expense;
Wells Fargo & Company 15

• lower occupancy expense as well as lower professional and
outside services expense related to efficiency initiatives; and
• lower donation expense due to higher donations of PPP
processing fees in 2021.
Table 9b: Consumer Banking and Lending – Balance Sheet
Year ended December 31,
(in millions) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Selected Balance Sheet Data (average)
Loans by Line of Business:
Consumer and Small Business Banking $ 10,132 16,625 (6,493) (39) % $ 15,173 1,452 10 %
Consumer Lending:
Home Lending 219,157 224,446 (5,289) (2) 268,586 (44,140) (16)
Credit Card 34,151 29,052 5,099 18 30,861 (1,809) (6)
Auto 55,994 52,293 3,701 7 49,460 2,833 6
Personal Lending 12,999 11,469 1,530 13 12,383 (914) (7)
Total loans $ 332,433 333,885 (1,452) — $ 376,463 (42,578) (11)
Total deposits 883,130 834,739 48,391 6 722,085 112,654 16
Allocated capital 48,000 48,000 — — 48,000 — —
Selected Balance Sheet Data (period-end)
Loans by Line of Business:
Consumer and Small Business Banking $ 9,704 11,270 (1,566) (14) $ 17,743 (6,473) (36)
Consumer Lending:
Home Lending 223,525 214,407 9,118 4 253,942 (39,535) (16)
Credit Card 38,475 31,671 6,804 21 30,178 1,493 5
Auto 54,281 57,260 (2,979) (5) 49,072 8,188 17
Personal Lending 14,544 11,966 2,578 22 11,861 105 1
Total loans $ 340,529 326,574 13,955 4
$ 362,796 (36,222) (10)
Total deposits 859,695 883,674
(
23,979) (3) 784,565 99,109 13
Full year 2022 vs. full year 2021
Total loans (average) decreased driven by:
• a decline in PPP loans in Consumer and Small Business
Banking; and
• a decline in Home Lending loan balances due to the
resecuritization of loans we purchased from GNMA loan
securitization pools and the continued pause in originating
home equity loans;
partially offset by:
• higher customer purchase volume and the impact of new
products in our Credit Card business; and
• higher loan balances in our Auto business.
Total loans (period-end) increased driven by:
• originations exceeding paydowns in Home Lending;
• higher customer purchase volume and the impact of new
products in our Credit Card business; and
• growth in our Personal Lending business;
partially offset by:
• a decline in our Auto business due to lower origination
volumes reflecting credit tightening actions and rising
interest rates; and
• a decline in PPP loans in Consumer and Small Business
Banking.
Total deposits (average) increased driven by higher levels of
customer liquidity and savings in the first half of 2022, partially
offset by increased consumer spending in the second half of
2022, customers continuing to allocate more cash into higher
yielding liquid alternatives, and lower servicing escrow deposits.
Total deposits (period-end) decreased driven by increased
consumer spending, customers continuing to allocate more cash
into higher yielding liquid alternatives, and lower servicing escrow
deposits.
Earnings Performance (continued)
16 Wells Fargo & Company
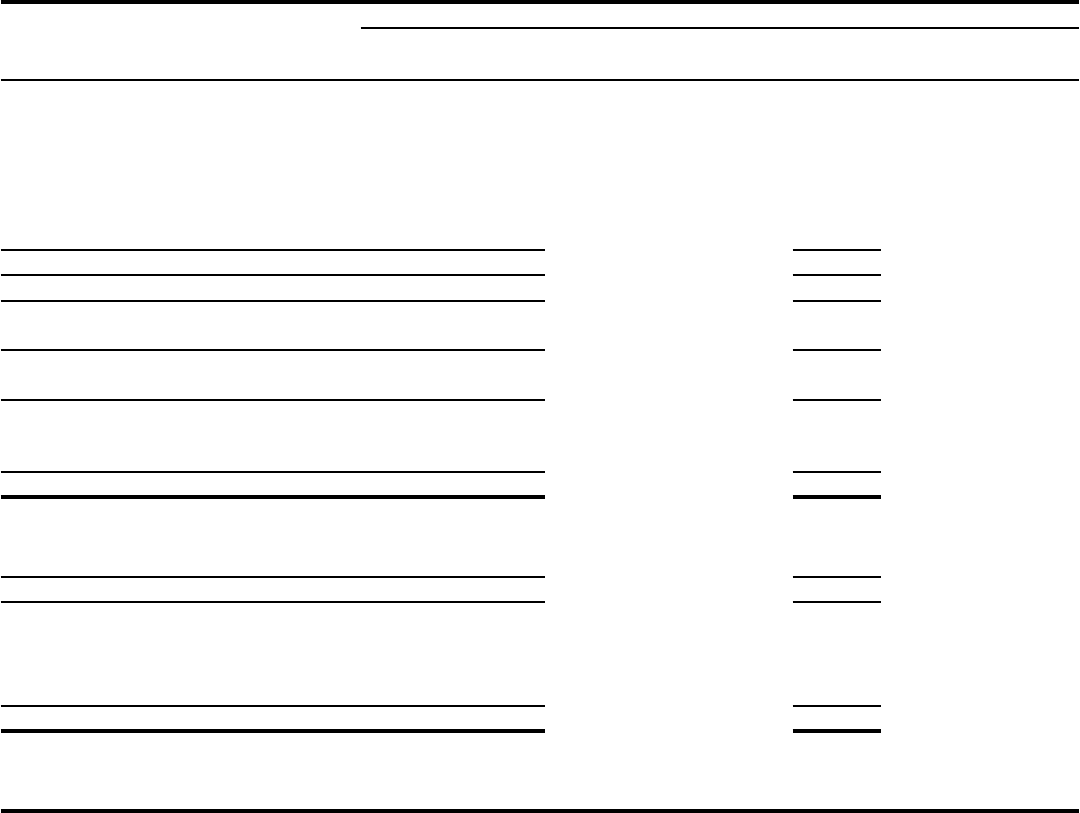
Commercial Banking provides financial solutions to private,
family owned and certain public companies. Products and
services include banking and credit products across multiple
industry sectors and municipalities, secured lending and lease
products, and treasury management. Table 9c and Table 9d
provide additional information for Commercial Banking.
Table 9c: Commercial Banking – Income Statement and Selected Metrics
Year ended December 31,
($ in millions) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Income Statement
Net interest income $ 7,289 4,960 2,329 47 % $ 6,134 (1,174) (19) %
Noninterest income:
Deposit-related fees 1,131 1,285 (154) (12) 1,219 66 5
Lending-related fees 491 532 (41) (8) 531 1 —
Lease income 710 682 28 4 646 36 6
Other 1,299 1,090 209 19 645 445 69
Total noninterest income 3,631 3,589 42 1 3,041 548 18
Total revenue 10,920 8,549 2,371 28 9,175 (626) (7)
Net charge-offs 4 101 (97) (96) 590 (489) (83)
Change in the allowance for credit losses (538) (1,601) 1,063 66 3,154 (4,755) NM
Provision for credit losses (534) (1,500) 966 64 3,744 (5,244) NM
Noninterest expense 6,058 5,862 196 3 6,323 (461) (7)
Income (loss) before income tax expense (benefit) 5,396 4,187 1,209 29 (892) 5,079 569
Income tax expense (benefit) 1,366 1,045 321 31 (208) 1,253 602
Less: Net income from noncontrolling interests 12 8 4 50 5 3 60
Net income (loss) $ 4,018 3,134 884 28 $ (689) 3,823 555
Revenue by Line of Business
Middle Market Banking $ 6,574 4,642 1,932 42
$ 5,067 (425) (8)
Asset-Based Lending and Leasing 4,346 3,907 439 11 4,108 (201) (5)
Total revenue $ 10,920 8,549 2,371 28 $ 9,175 (626) (7)
Revenue by Product
Lending and leasing $ 5,253 4,835 418 9 $ 5,432 (597) (11)
Treasury management and payments 4,483 2,825 1,658 59 3,205 (380) (12)
Other 1,184 889 295 33 538 351 65
Total revenue $ 10,920 8,549 2,371 28 $ 9,175 (626) (7)
Selected Metrics
Return on allocated capital 19.7 % 15.1 (4.5) %
Efficiency ratio 55 69 69
NM – Not meaningful
Full year 2022 vs. full year 2021
Revenue increased driven by:
• higher net interest income reflecting higher interest rates
and deposit spreads as well as higher loan balances; and
• higher other noninterest income driven by higher net gains
from equity securities and higher income from renewable
energy investments;
partially offset by:
• lower deposit-related fees driven by the impact of higher
earnings credit rates, which result in lower fees for
commercial customers.
Provision for credit losses reflected loan growth and a less
favorable economic environment, partially offset by lower net
charge-offs.
Noninterest expense increased driven by higher operating costs
and operating losses, partially offset by the impact of efficiency
initiatives.
Wells Fargo & Company 17
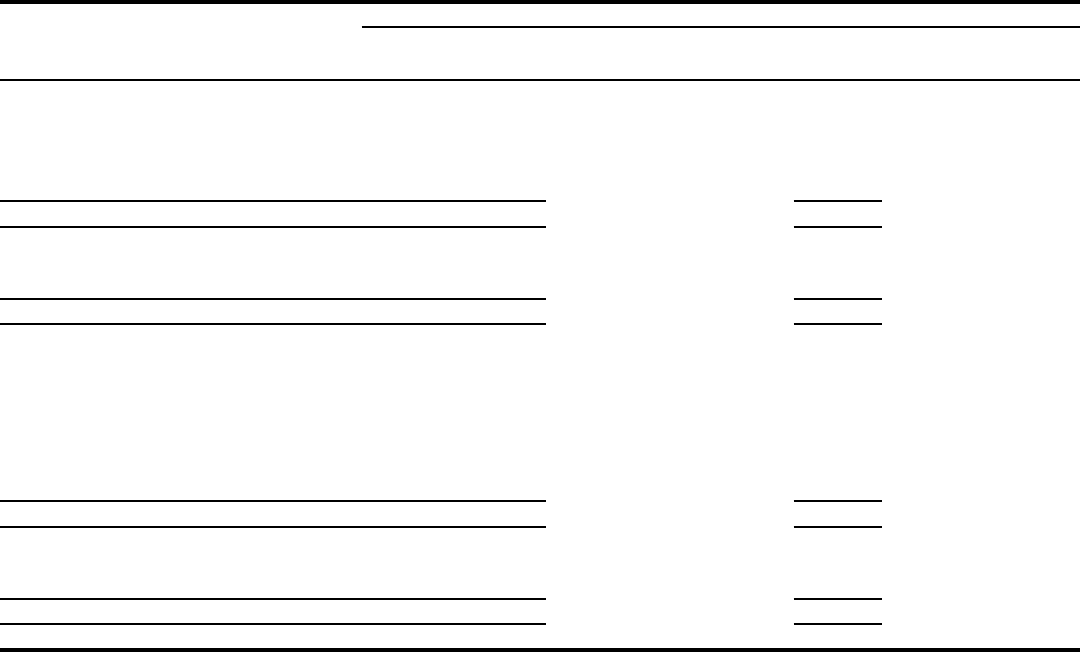
Table 9d: Commercial Banking – Balance Sheet
Year ended December 31,
(in millions) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Selected Balance Sheet Data (average)
Loans:
Commercial and industrial $ 147,379 120,396 26,983 22 % $ 143,263 (22,867) (16) %
Commercial real estate 45,130 47,018 (1,888) (4) 52,220 (5,202) (10)
Lease financing and other
13,523
13,823
(300) (2) 15,953 (2,130) (13)
Total loans $ 206,032 181,237 24,795 14 $ 211,436 (30,199) (14)
Loans by Line of Business:
Middle Market Banking $ 114,634 102,882 11,752 11 $ 112,848 (9,966) (9)
Asset-Based Lending and Leasing 91,398 78,355 13,043 17 98,588 (20,233) (21)
Total loans $ 206,032 181,237 24,795 14 $ 211,436 (30,199) (14)
Total deposits 186,079 197,269 (11,190) (6) 178,946 18,323 10
Allocated capital 19,500 19,500 — — 19,500 — —
Selected Balance Sheet Data (period-end)
Loans:
Commercial and industrial $ 163,797 131,078 32,719 25 $ 124,253 6,825 5
Commercial real estate 45,816 45,467 349 1 49,903 (4,436) (9)
Lease financing and other 13,916 13,803 113 1 14,821 (1,018) (7)
Total loans $ 223,529 190,348 33,181 17 $ 188,977 1,371 1
Loans by Line of Business:
Middle Market Banking $ 121,192 106,834 14,358 13 $ 101,193 5,641 6
Asset-Based Lending and Leasing 102,337 83,514 18,823 23 87,784 (4,270) (5)
Total loans
$ 223,529 190,348 33,181 17 $ 188,977 1,371 1
Total
deposits 173,942 205,428 (31,486) (15) 188,292 17,136 9
Full year 2022 vs. full year 2021
Total loans (average and period-end) increased driven by
growth in new commitments with existing and new customers as
well as higher line utilization and increased originations.
Total deposits (average and period-end) decreased reflecting:
• customers continuing to allocate more cash into higher
yielding liquid alternatives;
• the transfer of certain customer accounts to the Consumer
Banking and Lending operating segment in first quarter
2022; and
• actions taken in 2021 and early 2022 to manage under the
asset cap.
Earnings Performance (continued)
18 Wells Fargo & Company
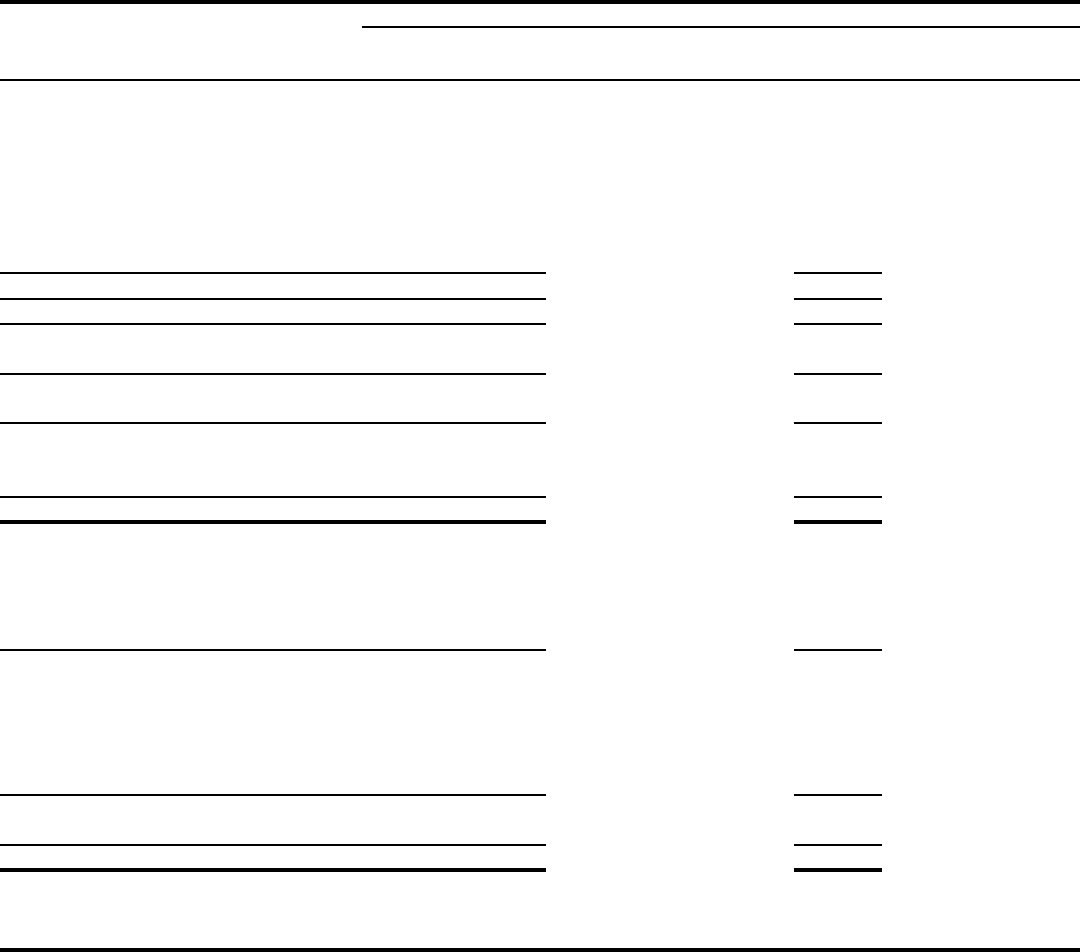
Corporate and Investment Banking delivers a suite of capital
markets, banking, and financial products and services to
corporate, commercial real estate, government and institutional
clients globally. Products and services include corporate banking,
investment banking, treasury management, commercial real
estate lending and servicing, equity and fixed income solutions as
well as sales, trading, and research capabilities. Table 9e and
Table 9f provide additional information for Corporate and
Investment Banking.
Table 9e: Corporate and Investment Banking – Income Statement and Selected Metrics
Year ended December 31,
($ in millions) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Income Statement
Net interest income $ 8,733 7,410 1,323 18 % $ 7,509 (99) (1) %
Noninterest income:
Deposit-related fees 1,068 1,112 (44) (4) 1,062 50 5
Lending-related fees 769 761 8 1 684 77 11
Investment banking fees 1,492 2,405 (913) (38) 1,952 453 23
Net gains from trading activities 1,886 272 1,614 593 1,190 (918) (77)
Other 1,294 1,879 (585) (31) 1,531 348 23
Total noninterest income 6,509 6,429 80 1 6,419 10 —
Total revenue 15,242 13,839 1,403 10 13,928 (89) (1)
Net charge-offs (48) (22) (26) NM 742 (764) NM
Change in the allowance for credit losses (137) (1,417) 1,280 90 4,204 (5,621) NM
Provision for credit losses (185) (1,439) 1,254 87 4,946 (6,385) NM
Noninterest expense 7,560 7,200 360 5 7,703 (503) (7)
Income before income tax expense 7,867 8,078 (211) (3) 1,279 6,799 532
Income tax expense 1,989 2,019 (30) (1) 330 1,689 512
Less: Net loss from noncontrolling interests — (3) 3 100 (1) (2) NM
Net income $ 5,878 6,062
(184) (3) $ 950 5,112 538
Revenu
e by Line of Business
Banking:
Lending $ 2,222 1,948 274 14 $ 1,767 181 10
Treasury Management and Payments 2,369 1,468 901 61 1,680 (212) (13)
Investment Banking 1,206 1,654 (448) (27) 1,448 206 14
Total Banking 5,797 5,070 727 14 4,895 175 4
Commercial Real Estate 4,534 3,963 571 14 3,607 356 10
Markets:
Fixed Income, Currencies, and Commodities (FICC) 3,660 3,710 (50) (1) 4,314 (604) (14)
Equities 1,115 897 218 24 1,204 (307) (25)
Credit Adjustment (CVA/DVA) and Other 20 91 (71) (78) 26 65 250
Total Markets 4,795 4,698 97 2 5,544 (846) (15)
Other 116 108 8 7 (118) 226 192
Total revenue $ 15,242 13,839 1,403 10 $ 13,928 (89) (1)
Selected Metrics
Return on allocated capital 15.3 % 16.9 1.8 %
Efficiency ratio 50 52 55
NM – Not meaningful
Full year 2022 vs. full year 2021
Revenue increased driven by:
• higher net interest income reflecting higher interest rates as
well as higher loan balances; and
• higher net gains from trading activities driven by higher
commodities, foreign exchange, rates, and equities trading
revenue;
partially offset by:
• lower investment banking fees due to lower market activity;
and
• lower other noninterest income driven by lower mortgage
banking income due to lower commercial MBS gain on sale
margins and volumes.
Provision for credit losses reflected loan growth and a less
favorable economic environment.
Noninterest expense increased driven by higher operating costs
and operating losses, partially offset by the impact of efficiency
initiatives.
Wells Fargo & Company 19
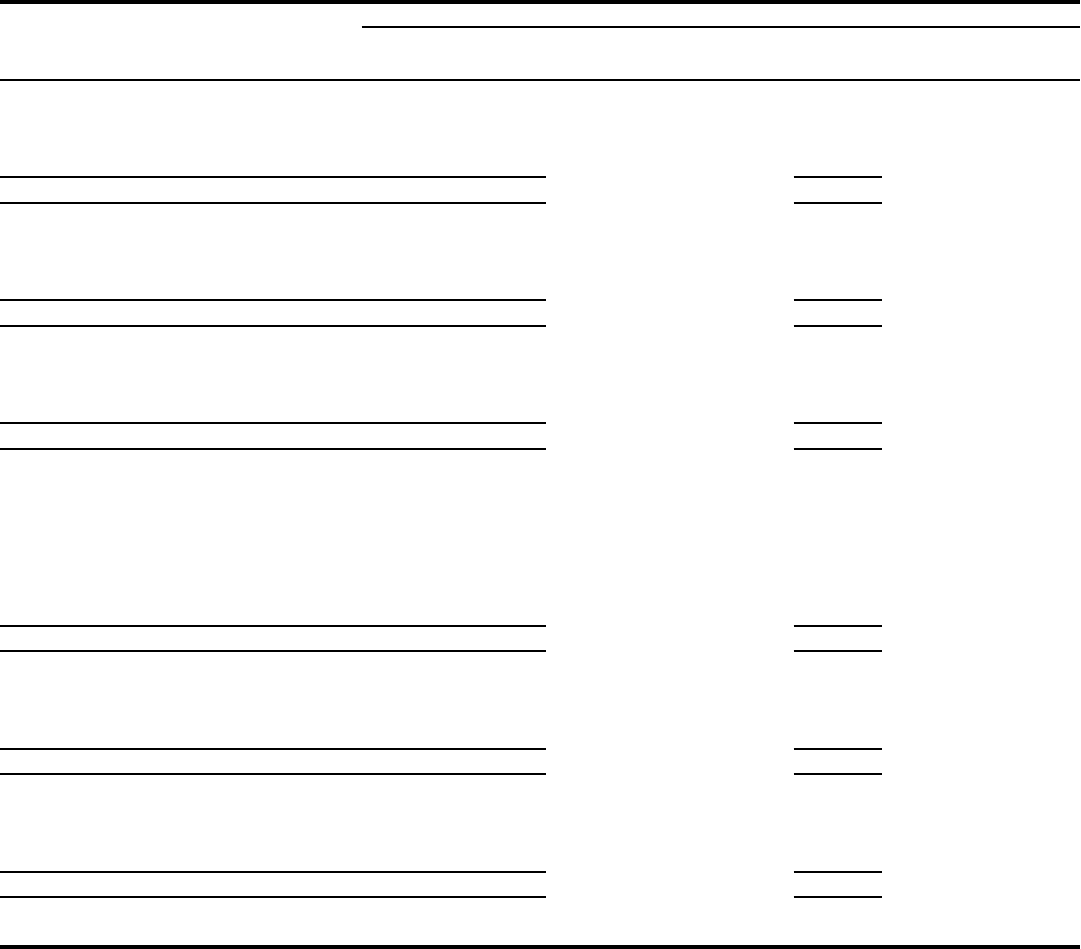
Table 9f: Corporate and Investment Banking – Balance Sheet
Year ended December 31,
(in millions) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Selected Balance Sheet Data (average)
Loans:
Commercial and industrial $ 198,424 170,713 27,711 16 % $ 172,492 (1,779) (1) %
Commercial real estate 98,560 86,323 12,237 14 82,832 3,491 4
Total loans $ 296,984 257,036 39,948 16 $ 255,324 1,712 1
Loans by Line of Business:
Banking $ 106,440 93,766 12,674 14 $ 93,501 265 —
Commercial Real Estate 133,719 110,978 22,741 20 108,279 2,699 2
Markets 56,825 52,292 4,533 9 53,544 (1,252) (2)
Total loans $ 296,984 257,036 39,948 16 $ 255,324 1,712 1
Trading-related assets:
Trading account securities $ 112,213 110,386 1,827 2 $ 109,803 583 1
Reverse repurchase agreements/securities borrowed 50,491 59,044 (8,553) (14) 71,485 (12,441) (17)
Derivative assets 27,421 25,315 2,106 8 21,986 3,329 15
Total trading-related assets $ 190,125 194,745 (4,620) (2) $ 203,274 (8,529) (4)
Total assets 557,396 523,344 34,052 7 521,514 1,830 —
Total deposits 161,720 189,176 (27,456) (15) 234,332 (45,156) (19)
Allocated capital 36,000 34,000 2,000 6 34,000 — —
Selected Balance Sheet Data (period-end)
Loans:
Commercial and industrial $ 196,529
191,391 5,138 3 $ 160,000 31,391 20
Commercial real estate 101,848 92,983 8,865 10 84,456 8,527 10
Total loans $ 298,377 284,374 14,003 5 $ 244,456 39,918 16
Loans by Line of Business:
Banking $ 101,183 101,926 (743) (1) $ 84,640 17,286 20
Commercial Real Estate 137,495 125,926 11,569 9 107,207 18,719 17
Markets 59,699 56,522 3,177 6 52,609 3,913 7
Total loans $ 298,377 284,374 14,003 5 $ 244,456 39,918 16
Trading-related assets:
Trading account securities $ 111,801 108,697 3,104 3 $ 109,311 (614) (1)
Reverse repurchase agreements/securities borrowed 55,407 55,973 (566) (1) 57,248 (1,275) (2)
Derivative assets 22,218 21,398 820 4 25,916 (4,518) (17)
Total trading-related assets $ 189,426 186,068 3,358 2 $ 192,475 (6,407) (3)
Total assets 550,177 546,549 3,628 1 508,518 38,031 7
Total deposits 157,217 168,609 (11,392) (7) 203,004 (34,395) (17)
Full year 2022 vs. full year 2021
Total assets (average and period-end) increased driven by
higher loan balances reflecting broad-based loan demand driven
by a modest increase in utilization rates due to increased client
working capital needs.
Total deposits (average) decreased driven by customers
continuing to allocate more cash into higher yielding liquid
alternatives as well as actions taken in 2021 and early 2022 to
manage under the asset cap.
Total deposits (period-end) decreased driven by customers
continuing to allocate more cash into higher yielding liquid
alternatives.
Earnings Performance (continued)
20 Wells Fargo & Company
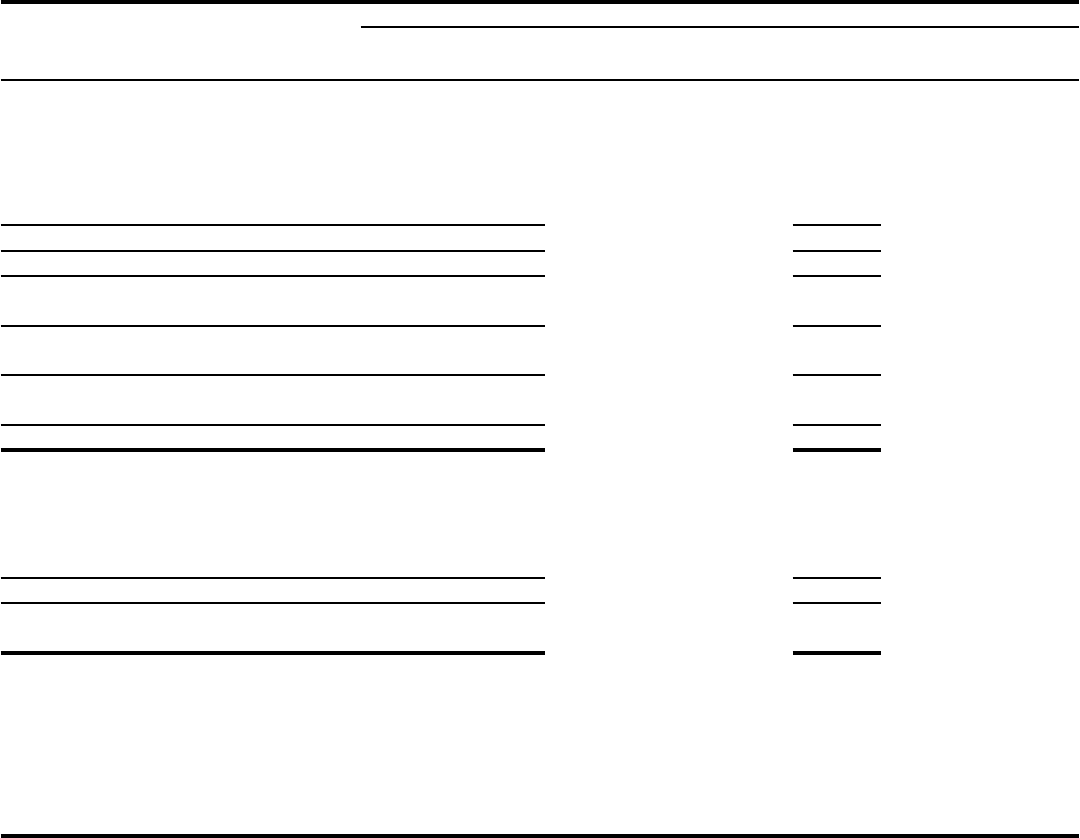
Wealth and Investment Management provides personalized
wealth management, brokerage, financial planning, lending,
private banking, trust and fiduciary products and services to
affluent, high-net worth and ultra-high-net worth clients. We
operate through financial advisors in our brokerage and wealth
offices, consumer bank branches, independent offices, and
digitally through WellsTrade® and Intuitive Investor®. Table 9g
and Table 9h provide additional information for Wealth and
Investment Management (WIM).
Table 9g: Wealth and Investment Management
Year ended December 31,
($ in millions, unless otherwise noted) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Income Statement
Net interest income $ 3,927 2,570 1,357 53 % $ 2,988 (418) (14) %
Noninterest income:
Investment advisory and other asset-based fees 8,847 9,574 (727) (8) 8,085 1,489 18
Commissions and brokerage services fees 1,931 2,010 (79) (4) 2,078 (68) (3)
Other 117 192 (75) (39) 62 130 210
Total noninterest income 10,895 11,776 (881) (7) 10,225 1,551 15
Total revenue 14,822 14,346 476 3 13,213 1,133 9
Net charge-offs (7) 10 (17) NM (3) 13 433
Change in the allowance for credit losses (18) (105) 87 83 252 (357) NM
Provision for credit losses (25) (95) 70 74 249 (344) NM
Noninterest expense 11,613 11,734 (121) (1) 10,912 822 8
Income before income tax expense 3,234 2,707 527 19 2,052 655 32
Income tax expense 812 680 132 19 514 166 32
Net income $ 2,422 2,027 395 19 $ 1,538 489 32
Selected Metrics
Return on allocated capital 27.1 % 22.6 17.0 %
Efficiency ratio 78 82 83
Advisory assets ($ in billions) $ 797 964 (167) (17) $ 853 111
13
Other brokerage assets and deposits ($ in billions) 1,064 1,219 (155) (13) 1,152 67 6
Total client assets ($ in billions) $ 1,861 2,183 (322) (15) $ 2,005 178 9
Annualized revenue per advisor ($ in thousands) (1) 1,219 1,114 105 9 939 175 19
Total financial and wealth advisors (#) (period-end) 12,027 12,367 (3) 13,513 (8)
Selected Balance Sheet Data (average)
Total loans $ 85,228 82,364 2,864 3 $ 78,775 3,589 5
Total deposits 164,883 176,562 (11,679) (7) 162,476 14,086 9
Allocated capital 8,750 8,750 — — 8,750 — —
Selected Balance Sheet Data (period-end)
Total loans $ 84,273 84,101 172 — $ 80,785 3,316 4
Total deposits 138,760 192,548 (53,788) (28) 175,483 17,065 10
NM – Not meaningful
(1) Represents annualized segment total revenue divided by average total financial and wealth advisors for the period.
Full year 2022 vs. full year 2021
Revenue increased driven by:
• higher net interest income driven by higher interest rates,
partially offset by lower deposit balances;
partially offset by:
• lower investment advisory and other asset-based fees due
to lower average market valuations and net outflows of
advisory assets; and
• lower commissions and brokerage services fees driven by
lower transactional revenue.
Provision for credit losses reflected loan growth and a less
favorable economic environment.
Noninterest expense decreased driven by:
• lower personnel expense driven by lower revenue-related
compensation; and
• the impact of efficiency initiatives.
Total deposits (period-end) decreased as customers continued
to allocate more cash into higher yielding liquid alternatives.
Wells Fargo & Company 21
WIM Advisory Assets In addition to transactional accounts,
WIM offers advisory account relationships to brokerage
customers. Fees from advisory accounts are based on a
percentage of the market value of the assets as of the beginning
of the quarter, which vary across the account types based on the
distinct services provided, and are affected by investment
performance as well as asset inflows and outflows. Advisory
accounts include assets that are financial advisor-directed and
separately managed by third-party managers as well as certain
client-directed brokerage assets where we earn a fee for advisory
and other services, but do not have investment discretion.
WIM also manages personal trust and other assets for high
net worth clients, with fee income earned based on a percentage
of the market value of these assets. Table 9h presents advisory
assets activity by WIM line of business. Management believes
that advisory assets is a useful metric because it allows
management, investors, and others to assess how changes in
asset amounts may impact the generation of certain asset-based
fees.
For the years ended December 31, 2022, 2021 and 2020,
the average fee rate by account type ranged from 50 to 120
basis points.
Table 9h: WIM Advisory Assets
Year ended
(in billions)
Balance, beginning
of period Inflows (1) Outflows (2) Market impact (3)
Balance, end of
period
December 31, 2022
Client-directed (4) $ 205.6 31.8 (39.0) (33.2) 165.2
Financial advisor-directed (5) 255.5 41.6 (44.2) (30.0) 222.9
Separate accounts (6) 203.3 24.6 (26.5) (24.9) 176.5
Mutual fund advisory (7) 102.1 8.7 (15.0) (17.2) 78.6
Total Wells Fargo Advisors $ 766.5 106.7 (124.7) (105.3)
643.2
The Private Bank (8) 198.0 27.4 (47.1) (24.7) 153.6
Total WIM advisory assets $ 964.5 134.1 (171.8) (130.0)
796.8
December 31, 2021
Client-directed (4) $ 186.3 41.5 (45.0) 22.8 205.6
Financial advisor-directed (5) 211.0 48.7 (41.1) 36.9 255.5
Separate accounts (6) 174.6 31.8 (30.7) 27.6 203.3
Mutual fund advisory (7) 91.4 15.6 (15.0) 10.1 102.1
Total Wells Fargo Advisors $ 663.3 137.6 (131.8) 97.4
766.5
The Private Bank (8) 189.4 40.0 (51.1) 19.7 198.0
Total WIM advisory assets $ 852.7 177.6 (182.9) 117.1
964.5
December 31, 2020
Client directed (4) $ 169.4 36.4 (38.2) 18.7 186.3
Financial advisor directed (5) 176.3 40.6 (33.6) 27.7 211.0
Separate accounts (6) 160.1 24.6 (27.4) 17.3 174.6
Mutual fund advisory (7) 83.7 11.3 (13.9) 10.3 91.4
Total Wells Fargo Advisors $ 589.5 112.9 (113.1) 74.0
663.3
The Private Bank (8) 188.0 34.0 (45.8) 13.2 189.4
Total WIM advisory assets $ 777.5 146.9 (158.9) 87.2
852.7
(1)
Inflows include new advisory account assets, contributions, dividends and interest.
(2) Outflows include closed advisory account assets, withdrawals and client management fees.
(3) Market impact reflects gains and losses on portfolio investments.
(4) Investment advice and other services are provided to client, but decisions are made by the client and the fees earned are based on a percentage of the advisory account assets, not the number and
size of transactions executed by the client.
(5) Professionally managed portfolios with fees earned based on respective strategies and as a percentage of certain client assets.
(6) Professional advisory portfolios managed by third-party asset managers. Fees are earned based on a percentage of certain client assets.
(7) Program with portfolios constructed of load-waived, no-load and institutional share class mutual funds. Fees are earned based on a percentage of certain client assets.
(8) Discretionary and non-discretionary portfolios held in personal trusts, investment agency, or custody accounts with fees earned based on a percentage of client assets.
Earnings Performance (continued)
Wells Fargo & Company
22
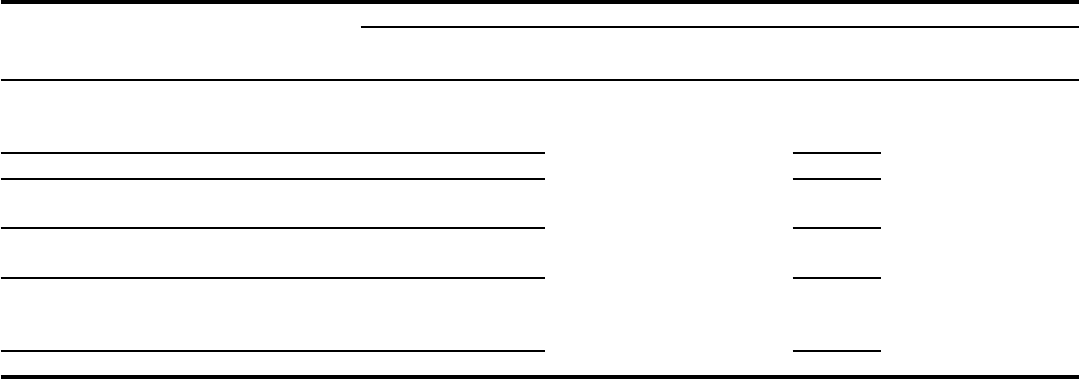
Corporate includes corporate treasury and enterprise functions,
net of allocations (including funds transfer pricing, capital,
liquidity and certain expenses), in support of the reportable
operating segments as well as our investment portfolio and
affiliated venture capital and private equity businesses. In
addition, Corporate includes all restructuring charges related to
our efficiency initiatives. See Note 20 (Revenue and Expenses) to
Financial Statements in this Report for additional information on
restructuring charges. Corporate also includes certain lines of
business that management has determined are no longer
consistent with the long-term strategic goals of the Company as
well as results for previously divested businesses. In fourth
quarter 2021, we completed the sales of Wells Fargo Asset
Management (WFAM) and our Corporate Trust Services
business; however, we continue to provide certain services
related to these businesses pursuant to transition services
agreements. The transition services agreement related to the
sale of our Institutional Retirement and Trust business
terminated in June 2022. Table 9i and Table 9j provide additional
information for Corporate.
Table 9i: Corporate – Income Statement
Year ended December 31,
(in millions) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Income Statement
Net interest income $ (1,607) (1,541) (66) (4)% $ 441 (1,982) NM
Noninterest income 609 10,036 (9,427) (94) 4,916 5,120 104 %
Total revenue (998) 8,495 (9,493) NM 5,357 3,138 59
Net charge-offs (33) 54 (87) NM 166 (112) (67)
Change in the allowance for credit losses 35 3 32 NM (638) 641 100
Provision for credit losses 2 57 (55) (96) (472) 529 112
Noninterest expense 5,774 4,387 1,387 32 5,716 (1,329) (23)
Income (loss) before income tax expense (benefit) (6,774) 4,051 (10,825) NM 113 3,938 NM
Income tax expense (benefit) (1,885) 596 (2,481) NM (670) 1,266 189
Less: Net income (loss) from noncontrolling interests (1) (312) 1,685 (1,997) NM 281 1,404 500
Net income (loss) $ (4,577) 1,770 (6,347) NM $ 502 1,268 253
NM – Not meaningful
(1) Reflects results attributable to noncontrolling interests predominantly associated with the Company’s consolidated venture capital investments.
Full year 2022 vs. full year 2021
Revenue decreased driven by:
• lower net gains from equity securities due to lower
unrealized and realized gains on nonmarketable equity
securities from our affiliated venture capital and private
equity businesses, and higher impairment driven by market
conditions;
• lower investment advisory and other asset-based fees
reflecting divestitures in 2021;
• lower gains on sales of corporate debt securities; and
• gains in 2021 on the sales of our Corporate Trust Services
business, our student loan portfolio, and WFAM;
partially offset by:
• higher net gains from trading activities;
• lower valuation losses related to the retained litigation risk
associated with shares of Visa Class B common stock that
we sold; and
• higher lease income driven by a $268 million impairment in
2021 of certain rail cars in our rail car leasing business that
are used for the transportation of coal products.
Provision for credit losses decreased due to lower net charge-
offs driven by the sale of our student loan portfolio in 2021.
Noninterest expense increased due to:
• higher operating losses reflecting higher expenses primarily
related to a variety of historical matters, including litigation
and regulatory matters;
partially offset by:
• the impact of divestitures;
• a write-down of goodwill in 2021 related to the sale of our
student loan portfolio;
• lower lease expense driven by lower depreciation expense
from a reduction in the size of our rail car leasing business;
and
• lower restructuring charges.
Corporate includes our rail car leasing business, which had
long-lived operating lease assets, net of accumulated
depreciation, of $4.7 billion and $5.1 billion as of December 31,
2022, and December 31, 2021, respectively. The average age of
our rail cars is 22 years and the rail cars are typically leased to
customers under short-term leases of 3 to 5 years. Our three
largest concentrations, which represented 55% of our rail car
fleet as of December 31, 2022, were rail cars used for the
transportation of agricultural grain, coal, and cement/sand
products. Impairment may result in the future based on changing
economic and market conditions affecting the long-term
demand and utility of specific types of rail cars. Our assumptions
for impairment are sensitive to estimated utilization and rental
rates as well as the estimated economic life of the leased asset.
For additional information on the accounting for impairment of
operating lease assets, see Note 1 (Summary of Significant
Accounting Policies) and Note 8 (Leasing Activity) to Financial
Statements in this Report.
Wells Fargo & Company 23
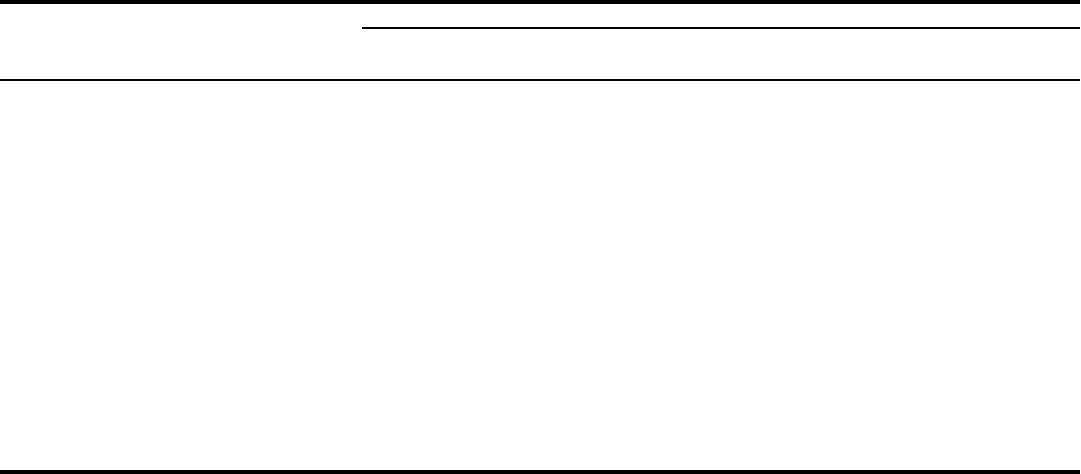
Earnings Performance (continued)
Table 9j: Corporate – Balance Sheet
Year ended December 31,
(in millions) 2022 2021
$ Change
2022/
2021
% Change
2022/
2021 2020
$ Change
2021/
2020
% Change
2021/
2020
Selected Balance Sheet Data (average)
Cash, cash equivalents, and restricted cash $ 147,192 236,124 (88,932) (38)% $ 183,420 52,704 29 %
Available-for-sale debt securities 124,308 181,841 (57,533) (32) 221,493 (39,652) (18)
Held-to-maturity debt securities 290,087 244,735 45,352 19 172,755 71,980 42
Equity securities 15,695 12,720 2,975 23 12,445 275 2
Total loans 9,143 9,766 (623) (6) 19,790 (10,024) (51)
Total assets 638,017 743,089 (105,072) (14) 675,250 67,839 10
Total deposits 28,457 40,066 (11,609) (29) 78,172 (38,106) (49)
Selected Balance Sheet Data (period-end)
Cash, cash equivalents, and restricted cash $ 127,106 209,696 (82,590) (39) $ 235,262 (25,566) (11)
Available-for-sale debt securities 102,669 165,926 (63,257) (38) 208,694 (42,768) (20)
Held-to-maturity debt securities 294,141 269,285 24,856 9 204,858 64,427 31
Equity securities 15,508 16,549 (1,041) (6) 10,305 6,244 61
Total loans 9,163 9,997 (834) (8) 10,623 (626) (6)
Total assets 601,214 721,335 (120,121) (17) 728,667 (7,332) (1)
Total deposits 54,371 32,220 22,151 69 53,037 (20,817) (39)
Full year 2022 vs. full year 2021
Total assets (average and period-end) decreased reflecting:
• a decrease in cash, cash equivalents, and restricted cash
managed by corporate treasury as a result of payments on
long-term debt and an increase in loans originated in the
operating segments; and
• lower available-for-sale debt securities due to sales and net
unrealized losses as well as a transfer from available-for-sale
debt securities to held-to-maturity debt securities related
to portfolio rebalancing to manage liquidity and interest rate
risk.
Total deposits (average) decreased driven by the transition of
deposits related to divested businesses.
Total deposits (period-end) increased driven by issuances of
certificates of deposit (CDs), partially offset by the transition of
deposits related to divested businesses.
Wells Fargo & Company 24
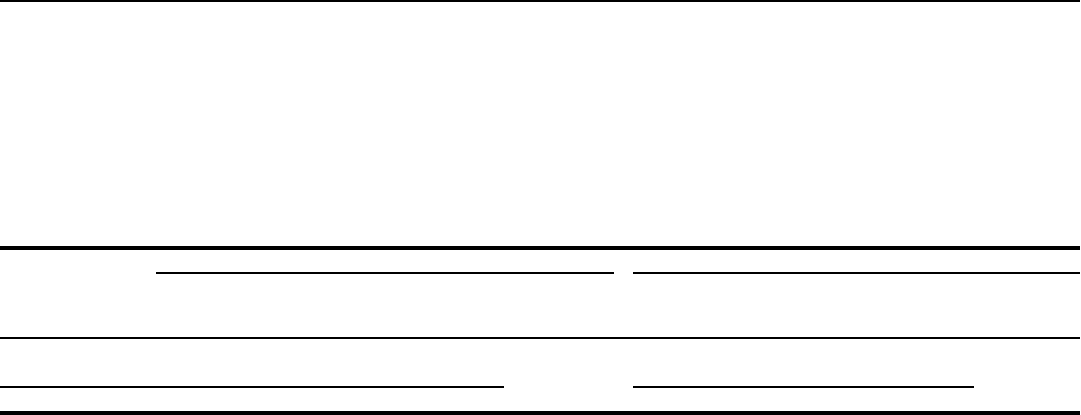
Balance Sheet Analysis
At December 31, 2022, our assets totaled $1.88 trillion, down
$67.1 billion from December 31, 2021.
The following discussion provides additional information
about the major components of our consolidated balance sheet.
See the “Capital Management” section in this Report for
information on changes in our equity.
Available-for-Sale and Held-to-Maturity Debt Securities
Table 10: Available-for-Sale and Held-to-Maturity Debt Securities
December 31, 2022 December 31, 2021
($ in millions)
Amortized
cost, net (1)
Net
unrealized gains
(losses) Fair value
Weighted
average
expected
maturity (yrs)
Amortized
cost, net (1)
Net
unrealized gains
(losses) Fair value
Weighted
average
expected
maturity (yrs)
Available-for-sale (2) $ 121,725 (8,131) 113,594 5.4 $ 175,463 1,781 177,244 5.2
Held-to-maturity (3) 297,059 (41,538) 255,521 8.1 272,022 364 272,386 6.3
Total $ 418,784 (49,669) 369,115 n/a $ 447,485 2,145 449,630 n/a
(1) Represents amortized cost of the securities, net of the allowance for credit losses of $6 million and $8 million related to available-for-sale debt securities and $85 million and $96 million related to
held-to-maturity debt securities at December 31, 2022 and 2021, respectively.
(2) Available-for-sale debt securities are carried on our consolidated balance sheet at fair value.
(3) Held-to-maturity debt securities are carried on our consolidated balance sheet at amortized cost, net of the allowance for credit losses.
Table 10 presents a summary of our portfolio of
investments in available-for-sale (AFS) and held-to-maturity
(HTM) debt securities. The size and composition of our AFS and
HTM debt securities is dependent upon the Company’s liquidity
and interest rate risk management objectives. The AFS debt
securities portfolio can be used to meet funding needs that arise
in the normal course of business or due to market stress.
Changes in our interest rate risk profile may occur due to changes
in overall economic or market conditions, which could influence
loan origination demand, prepayment rates, or deposit balances
and mix. In response, the AFS debt securities portfolio can be
rebalanced to meet the Company’s interest rate risk
management objectives. In addition to meeting liquidity and
interest rate risk management objectives, the AFS and HTM debt
securities portfolios may provide yield enhancement over other
short-term assets. See the “Risk Management – Asset/Liability
Management” section in this Report for additional information
on liquidity and interest rate risk.
The AFS debt securities portfolio predominantly consists of
liquid, high-quality U.S. Treasury and federal agency debt, and
agency MBS. The portfolio also includes securities issued by U.S.
states and political subdivisions and highly rated collateralized
loan obligations (CLOs).
The HTM debt securities portfolio predominantly consists of
liquid, high-quality U.S. Treasury and federal agency debt, and
agency MBS. The portfolio also includes securities issued by U.S.
states and political subdivisions and highly rated CLOs. Debt
securities are classified as HTM at the time of purchase or when
transferred from the AFS debt securities portfolio. Our intent is
to hold these securities to maturity and collect the contractual
cash flows. In January 2023, we changed our intent with respect
to HTM debt securities with an amortized cost of $23.9 billion
and reclassified them to AFS in connection with the adoption of a
new accounting standard. For additional information, see the
“Current Accounting Developments” section in this Report.
The amortized cost, net of the allowance for credit losses, of
AFS and HTM debt securities decreased from December 31,
2021. Purchases of AFS and HTM debt securities were more than
offset by portfolio runoff and AFS debt security sales. In addition,
we transferred AFS debt securities with a fair value of
$50.1 billion to HTM debt securities in 2022 due to actions taken
to reposition the overall portfolio for capital management
purposes. Debt securities transferred from AFS to HTM in 2022
had $4.5 billion of pre-tax unrealized losses at the time of the
transfers.
The total net unrealized losses on AFS and HTM debt
securities at December 31, 2022, were driven by higher interest
rates and wider credit spreads.
At December 31, 2022 , 99% of the combined AFS and HTM
debt securities portfolio was rated AA- or above. Ratings are
based on external ratings where available and, where not
available, based on internal credit grades. See Note 3 (Available-
for-Sale and Held-to-Maturity Debt Securities ) to Financial
Statements in this Report for additional information on AFS an d
HTM debt securities, including a summary of debt securities by
security type.
Wells Fargo & Company 25
Balance Sheet Analysis (continued)
Loan Portfolios
Table 11 provides a summary of total outstanding loans by
portfolio segment. Commercial loans increased from
December 31, 2021, predominantly due to an increase in the
commercial and industrial loan portfolio, driven by higher loan
demand resulting in increased originations and loan draws,
partially offset by paydowns. Consumer loans increased from
December 31, 2021, primarily driven by an increase in the
residential mortgage portfolio due to loan originations,
partially
offset by loan paydowns and the transfer of first lien mortgage
loans to loans held for sale (LHFS), which predominantly related
to loans purchased from GNMA loan securitization pools in prior
periods.
Table 11: Loan Portfolios
($ in millions) December 31, 2022 December 31, 2021 $ Change % Change
Commercial $ 557,516 513,120 44,396 9 %
Consumer 398,355 382,274 16,081 4
Total loans $ 955,871 895,394 60,477 7
Average loan balances and a comparative detail of average
loan balances is included in Table 3 under “Earnings Performance
– Net Interest Income” earlier in this Report. Additional
information on total loans outstanding by portfolio segment and
class of financing receivable is included in the “Risk Management
– Credit Risk Management” section in this Report. Period-end
balances and other loan related information are in Note 5 (Loans
and Related Allowance for Credit Losses) to Financial Statements
in this Report.
Table 12 shows loan maturities based on contractually
scheduled repayment timing and the distribution by changes in
interest rates for loans with a contractual maturity greater than
one year. Nonaccrual loans and loans with indeterminate
maturities have been classified as maturing within one year.
Table 12: Loan Maturities
December 31, 2022
Loan maturities
Loans maturing
after one year
(in millions)
Within
one
year
After
one year
through
five years
After five
years
through
fifteen
years
After
fifteen
years Total
Fixed
interest
rates
Floating/
variable
interest
rates
Commercial and industrial $ 134,858 229,197 21,255 1,496 386,806 21,507 230,441
Commercial real estate 43,307 88,576 22,431 1,488 155,802 19,679 92,816
Lease financing 3,283 10,159 1,400 66 14,908 11,625 —
Total commercial 181,448 327,932 45,086 3,050 557,516 52,811 323,257
Residential mortgage 10,666 30,464 87,675 140,312 269,117 179,246 79,205
Credit card 46,293 — — — 46,293 — —
Auto 12,672 38,812 2,185 — 53,669 40,997 —
Other consumer 24,995 3,775 483 23 29,276 3,851 430
Total consumer 94,626 73,051 90,343 140,335 398,355 224,094 79,635
Total loans $ 276,074 400,983 135,429 143,385 955,871 276,905 402,892
Deposits
Deposits decreased from December 31, 2021, reflecting:
• customers continuing to allocate more cash into higher
yielding liquid alternatives;
• increased consumer spending; and
• the transition of deposits related to divested businesses;
partially offset by:
• higher time deposits driven by issuances of certificates of
deposit (CDs).
Table 13 provides additional information regarding deposit
balances. Information regarding the impact of deposits on net
interest income and a comparison of average deposit balances i
s
provided in the “Earnings Performance – Net Interest Income”
section and Table 3 earlier in this Report. In response to rising
interest rates in 2022, our average deposit cost in fourth quarter
2022 increased to 0.46%, compared with 0.02% in fourth quarter
2021.
Table 13: Deposits
($ in millions)
Dec 31,
2022
% of
total
deposits
Dec 31,
2021
% of
total
deposits
$ Change
% Change
Noninterest-bearing demand deposits
$ 458,010
33 %
$ 527,748
36 %
$ (69,738)
(13)%
Interest-bearing demand deposits
428,877
31
465,887
31
(37,010)
(8)
Savings deposits
410,139
30
439,600
30
(29,461)
(7)
Time deposits
66,197
5
29,461
2
36,736
125
Interest-bearing deposits in non-U.S. offices
20,762
1
19,783
1
979
5
Total deposits $
1,383,985
100 % $
1,482,479
100 % $
(98,494)
(7)
26 Wells Fargo & Company
As of December 31, 2022 and 2021, total deposits that
exceed Federal Deposit Insurance Corporation (FDIC) insurance
limits, or are otherwise uninsured, were estimated to be $510
billion and $590 billion, respectively. Estimated uninsured
domestic deposits reflect amounts disclosed in the U.S.
regulatory reports of our subsidiary banks, with adjustments for
amounts related to consolidated subsidiaries. All non-U.S.
deposits are treated for these purposes as uninsured.
Table 14 presents the contractual maturities of estimated
time deposits that exceed FDIC insurance limits, or are otherwise
uninsured. All non-U.S. time deposits are uninsured.
Table 14: Uninsured Time Deposits by Maturity
(in millions)
Three months
or less
After three
months
through six
months
After six
months
through
twelve months
After twelve
months Total
December 31, 2022
Domestic time deposits $ 4,514 826 857 906 7,103
Non-U.S. time deposits 499 176 — 15 690
Total $ 5,013 1,002 857 921 7,793
Off-Balance Sheet Arrangements
In the ordinary course of business, we engage in financial
transactions that are not recorded on our consolidated balance
sheet, or may be recorded on our consolidated balance sheet in
amounts that are different from the full contract or notional
amount of the transaction. Our off-balance sheet arrangements
include unfunded credit commitments, transactions with
unconsolidated entities, guarantees, commitments to purchase
debt and equity securities, derivatives, and other commitments.
These transactions are designed to (1) meet the financial needs
of customers, (2) manage our credit, market or liquidity risks,
and/or (3) diversify our funding sources.
Unfunded Credit Commitments
Unfunded credit commitments are legally binding agreements to
lend to customers with terms covering usage of funds,
contractual interest rates, expiration dates, and any required
collateral. The maximum credit risk for these commitments will
generally be lower than the contractual amount because these
commitments may expire without being used or may be
cancelled at the customer’s request. Our credit risk monitoring
activities include managing the amount of commitments, both to
individual customers and in total, and the size and maturity
structure of these commitments. For additional information, see
Note 5 (Loans and Related Allowance for Credit Losses) to
Financial Statements in this Report.
Transactions with Unconsolidated Entities
In the normal course of business, we enter into various types of
on- and off-balance sheet transactions with special purpose
entities (SPEs), which are corporations, trusts, limited liability
companies or partnerships that are established for a limited
purpose. Generally, SPEs are formed in connection with
securitization transactions and are considered variable interest
entities (VIEs). For additional information, see Note 16
(Securitizations and Variable Interest Entities) to Financial
Statements in this Report.
Guarantees and Other Arrangements
Guarantees are contracts that contingently require us to make
payments to a guaranteed party based on an event or a change in
an underlying asset, liability, rate or index. Guarantees are
generally in the form of standby and direct pay letters of credit,
written options, recourse obligations, exchange and clearing
house guarantees, indemnifications, and other types of similar
arrangements. For additional information, see Note 17
(Guarantees and Other Commitments) to Financial Statements
in this Report.
Commitments to Purchase Debt and Equity Securities
We enter into commitments to purchase securities under resale
agreements. We also may enter into commitments to purchase
debt and equity securities to provide capital for customers’
funding, liquidity or other future needs. For additional
information, see Note 17 (Guarantees and Other Commitments)
to Financial Statements in this Report.
Derivatives
We use derivatives to manage exposure to market risk, including
interest rate risk, credit risk and foreign currency risk, and to
assist customers with their risk management objectives.
Derivatives are recorded on our consolidated balance sheet at
fair value, and volume can be measured in terms of the notional
amount, which is generally not exchanged, but is used only as the
basis on which interest and other payments are determined. The
notional amount is not recorded on our consolidated balance
sheet and is not, when viewed in isolation, a meaningful measure
of the risk profile of the instruments. For additional information,
see Note 14 (Derivatives) to Financial Statements in this Report.
Wells Fargo & Company 27

Risk Management
Wells Fargo manages a variety of risks that can significantly
affect our financial performance and our ability to meet the
expectations of our customers, shareholders, regulators and
other stakeholders.
Risk is Part of our Business Model. Risk is the possibility of an
event occurring that could adversely affect the Company’s ability
to achieve its strategic or business objectives. The Company
routinely takes risks to achieve its business goals and to serve its
customers. These risks include financial risks, such as interest
rate, credit, liquidity, and market risks, and non-financial risks,
such as operational risk, which includes compliance and model
risks, and strategic and reputation risks.
Risk Profile. The Company’s risk profile is an assessment of the
aggregate risks associated with the Company’s exposures and
business activities after taking into consideration risk
management effectiveness. The Company monitors its risk
profile, and the Board reviews risk profile reports and analysis.
Risk Capacity. Risk capacity is the maximum level of risk that
the Company could assume given its current level of resources
before triggering regulatory and other constraints on its capital
and liquidity needs.
Risk Appetite. Risk appetite is the amount of risk, within its risk
capacity, the Company is comfortable taking given its current
level of resources. Risk appetite is articulated in our Statement of
Risk Appetite, which establishes acceptable risks and at what
level and includes risk appetite principles. The Company’s
Statement of Risk Appetite is defined by senior management,
approved at least annually by the Board, and helps guide the
Company’s business and risk leaders. The Company continuously
monitors its risk appetite, and the Board reviews reports which
include risk appetite information and analysis.
Risk and Strategy. The Chief Executive Officer (CEO) drives the
Company’s strategic planning process, which identifies the
Company’s most significant opportunities and challenges,
develops options to address them, and evaluates the risks and
trade-offs of each. The Company’s risk profile, risk capacity, risk
appetite, and risk management effectiveness are considered in
the strategic planning process, which is linked with the
Company’s capital planning process. The Company’s Independent
Risk Management (IRM) organization participates in strategic
planning, providing challenge to and independent assessment of
the risks associated with strategic initiatives. IRM also
independently assesses and challenges the impact of the
strategic plan on risk capacity, risk appetite, and risk
management effectiveness at the principal lines of business,
enterprise functions, and aggregate Company level. After review,
the strategic plan is presented to the Board each year with IRM’s
evaluation.
Risk and Climate Change. The Company is committed to helping
mitigate the impacts of climate change related to its activities
and to partner with key stakeholders, including communities and
customers, to do the same. The Company expects that climate
change will increasingly impact the risk types it manages, and the
Company will continue to integrate climate considerations into
its risk management framework as its understanding of climate
change and risks driven by it evolve.
Risk is Managed by Everyone. Every employee, in the course of
their daily activities, creates risk and is responsible for managing
risk. Every employee has a role to play in risk management,
including establishing and maintaining the Company’s control
environment. Every employee must comply with applicable laws,
regulations, and Company policies.
Risk and Culture. Senior management sets the tone at the top
by supporting a strong culture, defined by the Company’s
expectations, that guides how employees conduct themselves
and make decisions. The Board oversees senior management in
establishing and maintaining this culture and effectively
managing risk. Senior management expects employees to speak
up when they see something that could cause harm to the
Company’s customers, communities, employees, shareholders,
or reputation. Because risk management is everyone’s
responsibility, all employees are empowered to and expected to
challenge risk decisions when appropriate and to escalate their
concerns when they have not been addressed. The Company’s
performance management and incentive compensation
programs are designed to establish a balanced framework for risk
and reward under core principles that employees are expected to
know and practice. The Board, through its Human Resources
Committee, plays an important role in overseeing and providing
credible challenge to the Company’s performance management
and incentive compensation programs. Effective risk
management is a central component of employee performance
evaluations.
Risk Management Framework. The Company’s risk
management framework sets forth the Company’s core
principles for managing and governing its risk. It is approved by
the Board’s Risk Committee and reviewed and updated annually.
Many other documents and policies flow from its core principles.
Wells Fargo’s top priority is to strengthen our company by
building an appropriate risk and control infrastructure. We
continue to enhance and mature our risk management programs,
including operational and compliance risk management programs
as required by the FRB’s February 2, 2018, and the CFPB/OCC’s
April 20, 2018, consent orders.
Risk Governance
Role of the Board. The Board oversees the Company’s business,
including its risk management. It assesses senior management’s
performance and holds senior management accountable for
maintaining and adhering to an effective risk management
program.
Board Committee Structure. The Board carries out its risk
oversight responsibilities directly and through its committees.
The Risk Committee reviews and approves the Company’s risk
management framework and oversees management’s
implementation of the framework, including how the Company
manages and governs risk. The Risk Committee also oversees the
Company’s adherence to its risk appetite. In addition, the Risk
Committee supports the stature, authority and independence of
IRM and oversees and receives reports on its operation. The Chief
Risk Officer (CRO) reports functionally to the Risk Committee
and administratively to the CEO.
Wells Fargo & Company 28
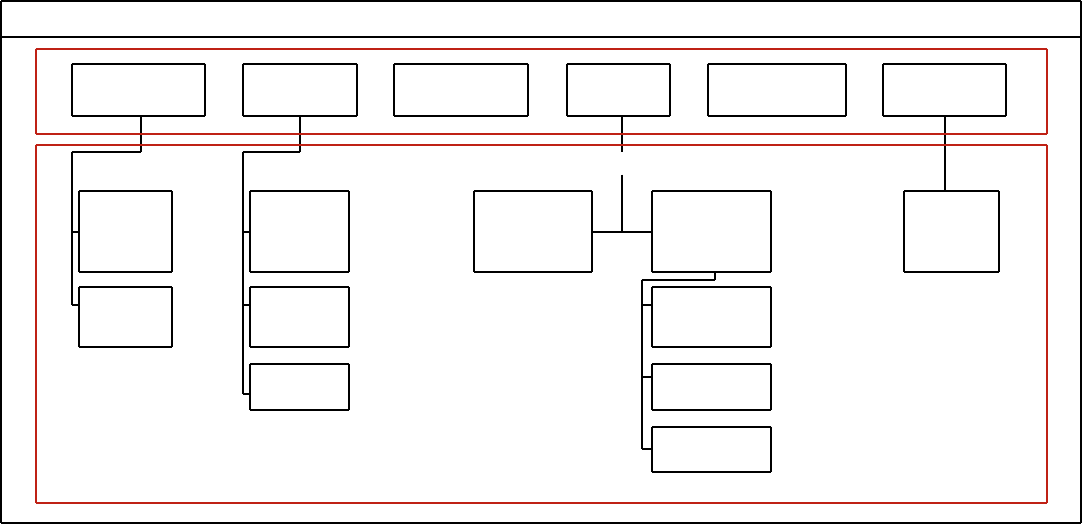
Management Committee Structure. The Company has
established management committees, including those focused
on risk, that support management in carrying out its governance
and risk management responsibilities. One type of management
committee is a governance committee, which is a decision-
making body that operates for a particular purpose and may
report to a Board committee.
Each management governance committee, in accordance
with its charter, is expected to discuss, document, and make
decisions regarding high priority and significant risks, emerging
risks, risk acceptances, and risks and issues escalated to it; review
and monitor progress related to critical and high-risk issues and
remediation efforts, including lessons learned; and report key
challenges, decisions, escalations, other actions, and open issues
as appropriate.
Table 15 presents, as of December 31, 2022, the structure
of the Company’s Board committees and escalation paths of
relevant management governance committees reporting to a
Board committee.
Table 15: Board and Relevant Management-level Governance Committee Structure
Wells Fargo & Company
Audit
Committee (1)
Disclosure
Committee
Regulatory
Reporting
Oversight
Committee
Finance
Committee
Capital
Management
Committee
Corporate
Asset/Liability
Committee
Recovery &
Resolution
Committee
Corporate
Responsibility
Committee
Risk
Committee
Management G overnance Committees
Allowance for Credit
Losses Approval
Governance
Committee
Governance &
Nominating
Committee
Enterprise Risk &
Control C ommittee
Risk & Control
Committees
Risk Type
Committees
Risk Topic
Committees
Human
Resources
Committee
Incentive
Compensation
& Performance
Management
Committee
(1) The Audit Committee assists the Board in its oversight of the Company’s financial statements and disclosures to shareholders and regulatory agencies; oversees the internal audit function and
external auditor independence, activities, and performance; and assists the Board and the Risk Committee in the oversight of the Company’s compliance with legal and regulatory requirements.
Management Governance Committees Reporting to the Risk
Committee of the Board. The Enterprise Risk & Control
Committee (ERCC) is a decision-making and escalation body that
governs the management of all risk types. The ERCC receives
information about risk and control issues, addresses escalated
risks and issues, and actively oversees risk controls. The ERCC
also makes decisions related to significant risks and changes to
the Company’s risk appetite. The Risk Committee receives
regular updates from the ERCC chairs and senior management
regarding current and emerging risks and senior management’s
assessment of the effectiveness of the Company’s risk
management program.
The ERCC is co-chaired by the CEO and CRO, and its
membership is comprised of principal line of business and certain
enterprise function heads. The Chief Auditor or a designee
attends all meetings of the ERCC. The ERCC has a direct
escalation path to the Risk Committee. The ERCC also has an
escalation path for certain human capital risks and issues to the
Human Resources Committee. In addition, the CRO may escalate
anything directly to the Board. Risks and issues are escalated to
the ERCC in accordance with the Company’s escalation
management policy.
Each principal line of business and enterprise function has a
risk and control committee, which is a management governance
committee with a mandate that aligns with the ERCC but with its
scope limited to the respective principal line of business or
enterprise function. These committees focus on and consider
risks that the respective principal line of business or enterprise
function generate and manage, and the controls the principal line
of business or enterprise function are expected to have in place.
As a complement to these risk and control committees,
management governance committees dedicated to specific risk
types and risk topics also report to the ERCC to enable more
comprehensive governance of risks.
Risk Operating Model – Roles and Responsibilities
The Company has three lines of defense for managing risk: the
Front Line, Independent Risk Management, and Internal Audit.
• Front Line The Front Line, which comprises principal line of
business and certain enterprise function activities, is the first
line of defense. The Front Line is responsible for
understanding the risks generated by its activities, applying
adequate controls, and managing risk in the course of its
business activities. The Front Line identifies, measures and
assesses, controls, monitors, and reports on risk generated
by or associated with its business activities and balances risk
and reward in decision making while operating within the
Company’s risk appetite.
• Independent Risk Management IRM is the second line of
defense. It establishes and maintains the Company’s risk
management program and provides oversight, including
Wells Fargo & Company 29
Risk Management (continued)
challenge to and independent assessment of, the Front
Line’s execution of its risk management responsibilities.
• Internal Audit Internal Audit is the third line of defense. It is
responsible for acting as an independent assurance function
and validates that the risk management program is
adequately designed and functioning effectively.
Risk Type Classifications
The Company uses common classifications, hierarchies, and
ratings to enable consistency across risk management programs
and aggregation of information. Risk type classifications permit
the Company to identify and prioritize its risk exposures,
including emerging risk exposures.
Operational Risk Management
Operational risk, which in addition to those discussed in this
section, includes compliance risk and model risk, is the risk
resulting from inadequate or failed internal processes, people
and systems, or from external events.
The Board’s Risk Committee has primary oversight
responsibility for all aspects of operational risk, including
significant supporting programs and/or policies regarding the
Company’s business resiliency and disaster recovery, change
management, data management, information security,
technology, and third-party risk management. As part of its
oversight responsibilities, the Board’s Risk Committee reviews
and approves significant operational risk policies and oversees
the Company’s operational risk management program.
At the management level, Operational Risk Management,
which is part of IRM, has oversight responsibility for operational
risk. Operational Risk Management reports to the CRO and
provides periodic reports related to operational risk to the
Board’s Risk Committee. Operational Risk Management’s
oversight responsibilities include change management risk, data
management risk, fraud risk, human capital risk, information
management risk, information security risk, technology risk, and
third-party risk.
Information security is a significant operational risk for
financial institutions such as Wells Fargo and includes the risk
arising from unauthorized access, use, disclosure, disruption,
modification, or destruction of information or information
systems. The Board is actively engaged in the oversight of the
Company’s information security risk management and cyber
defense programs. The Board’s Risk Committee has primary
oversight responsibility for information security risk and
approves the Company’s information security program, which
includes the information security policy and the cyber defense
program.
Wells Fargo and other financial institutions, as well as our
third-party service providers, continue to be the target of various
evolving and adaptive information security threats, including
cyber attacks, malware, ransomware, other malicious software
intended to exploit hardware or software vulnerabilities,
phishing, credential validation, and distributed denial-of-service,
in an effort to disrupt the operations of financial institutions, test
their cybersecurity capabilities, commit fraud, or obtain
confidential, proprietary or other information. Cyber attacks
have also focused on targeting online applications and services,
such as online banking, as well as cloud-based and other products
and services provided by third parties, and have targeted the
infrastructure of the internet causing the widespread
unavailability of websites and degrading website performance. As
a result, information security and the continued development
and enhancement of our controls, processes and systems
designed to protect our networks, computers, software and data
from attack, damage or unauthorized access remain a priority for
Wells Fargo. Wells Fargo is also proactively involved in industry
cybersecurity efforts and working with other parties, including
our third-party service providers and governmental agencies, to
continue to enhance defenses and improve resiliency to
information security threats. See the “Risk Factors” section in
this Report for additional information regarding the risks
associated with a failure or breach of our operational or security
systems or infrastructure, including as a result of cyber attacks.
Compliance Risk Management
Compliance risk (a type of operational risk) is the risk resulting
from the failure to comply with laws (legislation, regulations and
rules) and regulatory guidance, and the failure to appropriately
address associated impact, including to customers. Compliance
risk encompasses violations of applicable internal policies,
program requirements, procedures, and standards related to
ethical principles applicable to the Company.
The Board’s Risk Committee has primary oversight
responsibility for all aspects of compliance risk, including financial
crimes risk. As part of its oversight responsibilities, the Board’s
Risk Committee reviews and approves significant supporting
compliance risk and financial crimes risk policies and programs
and oversees the Company’s compliance risk management and
financial crimes risk management programs.
Conduct risk, a sub-category of compliance risk, is the risk of
inappropriate, unethical, or unlawful behavior on the part of
employees or individuals acting on behalf of the Company,
caused by deliberate or unintentional actions or business
practices. In connection with its oversight of conduct risk, the
Board oversees the alignment of employee conduct to the
Company’s risk appetite (which the Board approves annually).
The Board’s Risk Committee has primary oversight responsibility
for conduct risk and risk management components of the
Company’s culture, while the responsibilities of the Board’s
Human Resources Committee include oversight of the
Company’s culture, Code of Ethics and Business Conduct,
human capital management (including talent management and
succession planning), performance management program, and
incentive compensation risk management program.
At the management level, the Compliance function, which is
part of IRM, monitors the implementation of the Company’s
compliance and conduct risk programs. Financial Crimes Risk
Management, which is part of the Compliance function, oversees
and monitors financial crimes risk. The Compliance function
reports to the CRO and provides periodic reports related to
compliance risk to the Board’s Risk Committee.
Model Risk Management
Model risk (a type of operational risk) is the risk arising from the
potential for adverse consequences of decisions made based on
model output that may be incorrect or used inappropriately.
The Board’s Risk Committee has primary oversight
responsibility for model risk. As part of its oversight
responsibilities, the Board’s Risk Committee oversees the
Company’s model risk management policy, model governance,
model performance, model issue remediation status, and
adherence to model risk appetite metrics.
At the management level, the Model Risk function, which is
part of IRM, has oversight responsibility for model risk and is
responsible for governance, validation and monitoring of model
risk across the Company. The Model Risk function reports to the
CRO and provides periodic reports related to model risk to the
Board’s Risk Committee.
Wells Fargo & Company 30
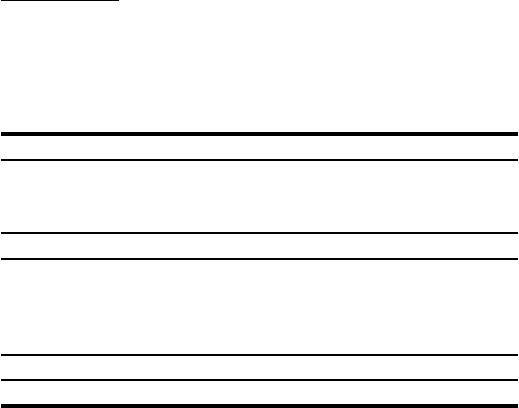
Strategic Risk Management
Strategic risk is the risk to earnings, capital, or liquidity arising
from adverse business decisions, improper implementation of
strategic initiatives, or inadequate responses to changes in the
external operating environment.
The Board has primary oversight responsibility for strategic
planning and oversees management’s development and
implementation of and approves the Company’s strategic plan,
and considers whether it is aligned with the Company’s risk
appetite and risk management effectiveness. Management
develops, executes and recommends significant strategic
corporate transactions and the Board evaluates management’s
proposals, including their impact on the Company’s risk profile
and financial position. The Board’s Risk Committee has primary
oversight responsibility for the Company’s strategic risk and the
adequacy of the Company’s strategic risk management program,
including associated risk management practices, processes and
controls. The Board’s Risk Committee also receives updates from
management regarding new business initiatives activity and risks
related to new or changing products, as appropriate.
At the management level, the Strategic Risk Oversight
function, which is part of IRM, has oversight responsibility for
strategic risk. The Strategic Risk Oversight function reports into
the CRO and supports periodic reports related to strategic risk
provided to the Board’s Risk Committee.
Reputation Risk Management
Reputation risk is the risk arising from the potential that
negative stakeholder opinion or negative publicity regarding the
Company’s business practices, whether true or not, will adversely
impact current or projected financial conditions and resilience,
cause a decline in the customer base, or result in costly litigation.
Key stakeholders include customers, employees, communities,
shareholders, regulators, elected officials, advocacy groups, and
media organizations.
The Board’s Risk Committee has primary oversight
responsibility for reputation risk, while each Board committee
has reputation risk oversight responsibilities related to their
primary oversight responsibilities. As part of its oversight
responsibilities, the Board’s Risk Committee receives reports
from management that help it monitor how effectively the
Company is managing reputation risk. As part of its oversight
responsibilities for social and public responsibility matters, the
Board’s Corporate Responsibility Committee receives reports
from management relating to stakeholder perceptions of the
Company.
At the management level, the Reputation Risk Oversight
function, which is part of IRM, has oversight responsibility for
reputation risk. The Reputation Risk Oversight function reports
into the CRO and supports periodic reports related to reputation
risk provided to the Board’s Risk Committee.
Credit Risk Management
We define credit risk as the risk of loss associated with a
borrower or counterparty default (failure to meet obligations in
accordance with agreed upon terms). Credit risk exists with many
of the Company’s assets and exposures such as debt security
holdings, certain derivatives, and loans.
The Board’s Risk Committee has primary oversight
responsibility for credit risk. A Credit Subcommittee of the Risk
Committee assists the Risk Committee in providing oversight of
credit risk. At the management level, Corporate Credit Risk,
which is part of Independent Risk Management, has oversight
responsibility for credit risk. Corporate Credit Risk reports to the
CRO and supports periodic reports related to credit risk provided
to the Board’s Risk Committee or its Credit Subcommittee.
Loan Portfolio Our loan portfolios represent the largest
component of assets on our consolidated balance sheet for which
we have credit risk. Table 16 presents our total loans outstanding
by portfolio segment and class of financing receivable.
Table 16: Total Loans Outstanding by Portfolio Segment and Class of
Financing Receivable
(in millions) Dec 31, 2022 Dec 31, 2021
Commercial and industrial $ 386,806 350,436
Commercial real estate 155,802 147,825
Lease financing 14,908 14,859
Total commercial 557,516 513,120
Residential mortgage 269,117 258,888
Credit card 46,293 38,453
Auto 53,669 56,659
Other consumer 29,276 28,274
Total consumer 398,355 382,274
Total loans $ 955,871 895,394
We manage our credit risk by establishing what we believe
are sound credit policies for underwriting new business, while
monitoring and reviewing the performance of our existing loan
portfolios. We employ various credit risk management and
monitoring activities to mitigate risks associated with multiple
risk factors affecting loans we hold including:
• Loan concentrations and related credit quality;
• Counterparty credit risk;
• Economic and market conditions;
• Legislative or regulatory mandates;
• Changes in interest rates;
• Merger and acquisition activities; and
• Reputation risk.
In addition, the Company will continue to integrate climate
considerations into its credit risk management activities.
Our credit risk management oversight process is governed
centrally, but provides for direct management and accountability
by our lines of business. Our overall credit process includes
comprehensive credit policies, disciplined credit underwriting,
frequent and detailed risk measurement and modeling, extensive
credit training programs, and a continual loan review and audit
process.
A key to our credit risk management is adherence to a well-
controlled underwriting process, which we believe is appropriate
for the needs of our customers as well as investors who purchase
the loans or securities collateralized by the loans.
Wells Fargo & Company 31
Risk Management – Credit Risk Management (continued)
Credit Quality Overview Table 17 provides credit quality trends .
Table 17: Credit Quality Overview
(in millions) Dec 31, 2022 Dec 31, 2021
Nonaccrual loans
Commercial loans $ 1,823 2,376
Consumer loans 3,803 4,836
Total nonaccrual loans $ 5,626 7,212
Nonaccrual loans as a % of total loans 0.59% 0.81
Net loan charge-offs as a % of:
Average commercial loans 0.01% 0.06
Average consumer loans 0.39 0.33
Allowance for credit losses (ACL) for loans $ 13,609 13,788
ACL for loans as a % of total loans 1.42% 1.54
Additional information on our loan portfolios and our credit
quality trends follows.
Significant Loan Portfolio Reviews Measuring and monitoring
our credit risk is an ongoing process that tracks delinquencies,
collateral values, Fair Isaac Corporation (FICO) scores, economic
trends by geographic areas, loan-level risk grading for certain
portfolios (typically commercial) and other indications of credit
risk. Our credit risk monitoring process is designed to enable
early identification of developing risk and to support our
determination of an appropriate allowance for credit losses. The
following discussion provides additional characteristics and
analysis of our significant portfolios. See Note 5 (Loans and
Related Allowance for Credit Losses ) to Financial Statements in
this Report for more analysis and credit metric information for
each of the following portfolios.
COMMERCIAL AND INDUSTRIAL LOANS AND LEASE FINANCING
For purposes of portfolio risk management, we aggregate
commercial and industrial loans and lease financing according
to market segmentation and standard industry codes. We
generally subject commercial and industrial loans and lease
financing to individual risk assessment using our internal
borrower and collateral quality ratings. Our ratings are aligned to
regulatory definitions of pass and criticized categories with
criticized segmented among special mention, substandard,
doubtful and loss categories.
We had $12.6 billion of the commercial and industrial loans
and lease financing portfolio internally classified as criticized in
accordance with regulatory guidance at December 31, 2022,
compared with $13.0 billion at December 31, 2021. The decline
was driven by decreases in the technology, telecom and media,
real estate and construction, and oil, gas and pipelines industries,
as these industries continued to recover from the economic
impacts of the COVID-19 pandemic, partially offset by an
increase in the materials and commodities, and equipment,
machinery and parts manufacturing industries.
The majority of our commercial and industrial loans and
lease financing portfolio is secured by short-term assets, such as
accounts receivable, inventory and debt securities, as well as
long-lived assets, such as equipment and other business assets.
Generally, the primary source of repayment for this portfolio is
the operating cash flows of customers, with the collateral
securing this portfolio representing a secondary source of
repayment.
The portfolio increased at December 31, 2022, compared
with December 31, 2021, driven by higher loan demand resulting
in increased originations and loan draws, partially offset by
paydowns. Table 18 provides our commercial and industrial loans
and lease financing by industry. The industry categories are based
on the North American Industry Classification System.
Wells Fargo & Company 32
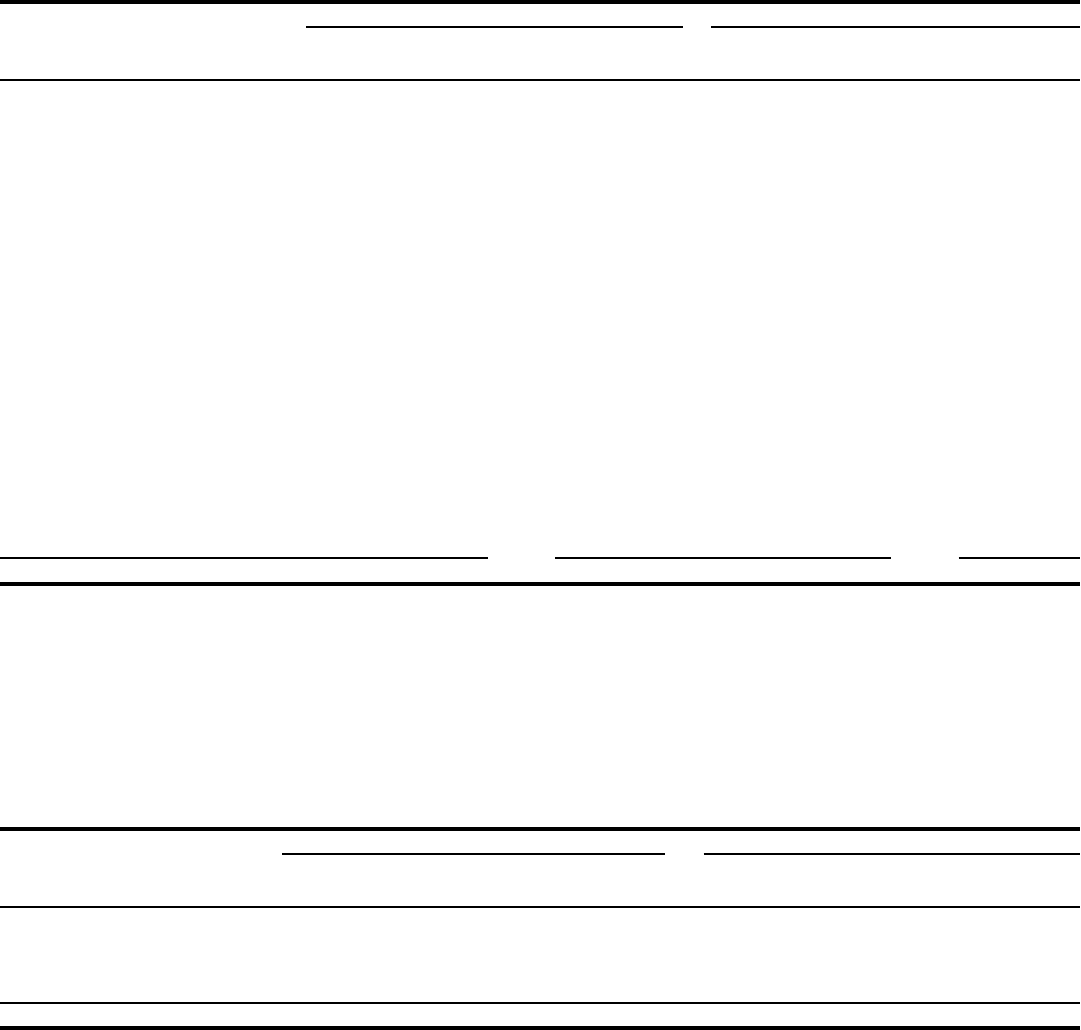
Table 18: Commercial a nd Industrial Lo ans a nd Lease Fina ncing by Ind ustry
December 31, 2022 December 31, 2021
($ in millions)
Nonaccrual
loans
Loans
outstanding
balance
% of
total
loans
Total
commitments (1)
Nonaccrual
loans
Loans
outstanding
balance
% of
total
loans
Total
commitments (1)
Financials except banks $ 44 147,171 15% $ 247,936 104 142,283 16% $ 236,133
Technology, telecom and media 31 27,767 3 78,230 64 23,345 3 62,984
Real estate and construction 73 24,478 3 57,138 78 25,035 3 55,304
Equipment, machinery and parts manufacturing 83 23,675 2 54,807 24 18,130 2 43,729
Retail 47 19,487 2 54,260 27 17,645 2 41,344
Materials and commodities 86 16,610 2 41,707 32 14,684 2 36,660
Oil, gas and pipelines 55 9,991 1 39,329 197 8,828 * 28,978
Food and beverage manufacturing 17 17,393 2 35,094 7 13,242 1 30,882
Health care and pharmaceuticals 21 14,861 2 30,463 24 12,847 1 28,808
Auto related 10 13,168 1 28,545 31 10,629 1 25,735
Commercial services 50 11,418 1 27,989 78 10,492 1 24,617
Utilities 18 9,457 * 26,918 77 6,982 * 22,406
Entertainment and recreation 28 13,085 1 24,535 23 9,907 1 17,893
Diversified or miscellaneous
2 8,161 * 22,432 3 7,493 * 18,317
Banks — 14,403 2 16,733 — 16,178 2 16,612
Transportation services 237 8,389 * 16,342 288 8,162 * 14,710
Insurance and fiduciaries 1 4,691 * 15,741 1 3,387 * 13,993
Agribusiness 24 6,180 * 14,063 35 6,086 * 11,576
Government and education 25 6,482 * 12,590 5 5,863 * 11,193
Other (2) 13 4,847 * 14,325 30 4,077 * 11,583
Total $ 865 401,714 42% $ 859,177 1,128 365,295 41% $ 753,457
* Less t han 1%.
(1) Total com mitments consist of loa ns ou tstanding plus u nfunded credit commitments, excluding issued letters of cr edit. For additional infor mation on issu ed letters of cr edit, see Note 17 (Guarantees
and Other Commitments) t o F inancial S tatements in t his Rep ort.
(2) No ot her single ind ustry had total loa ns in excess of $3.4 b illion and $3.1 b illion at December 31, 2022 and 2021, respectively.
Asset managers and funds (2) 52,254 5 % 1 60,518 7 %
Commercial finance (3) 31 53,269 5 76,334 82 46,043 5 69,923
Real estate finance (4) 8 24,620 3 41,589 9 23,231 3 37,997
Consumer finance (5) 4 17,028 2 29,476 12 12,491 1 27,178
Total 147,171 15% 104 142,283 16%
Table 18a provides further loan segmentation for our largest
industry category, financials except banks. This category inclu des
loans to investment firms, financial vehicles, nonbank creditor s,
rental and leasing companies, securities firms, and investment
banks. These loans are generally secured and have features to
help manage credit risk, such as structural credit enhancements ,
collateral eligibility requirements, contractual re-margining o f
collateral supporting the loans, and loan amounts limited to a
percentage of the value of the underlying assets considering
underlying credit risk, asset duration, and ongoing performance .
Table 18a : Financials Except Ba nks Ind ustry C ategory
December 31, 2022 December 31, 2021
Loans
outstanding
balance
% of
total
loans
Loans
outstanding
balance
% of
total
loans
Nonaccrual
loans
Total
commitments (1)
Nonaccrual
loans
Total
commitments (1) ($ in millions)
$ 1 $ 100,537 $ 101,035
$ 44 $ 247,936 $ 236,133
(1)
Total commitments consist of loans outstanding plus unfunded credit commitments, excluding issued letters of credit. For additional information on issued letters of credit, see Note 17 (Guarantees
and Other Commitments) to Financial Statements in this Report.
(2) Includes loans for subscription or capital calls and loans to prime brokerage customers and securities firms.
(3) Includes asset-based lending and leasing, including loans to special purpose entities, loans to commercial leasing entities, structured lending facilities to commercial loan managers, and also includes
collateralized loan obligations (CLOs) in loan form, all of which were rated AA or above, of $7.8 billion and $8.1 billion at December 31, 2022 and 2021, respectively.
(4) Includes originators or servicers of financial assets collateralized by commercial or residential real estate loans.
(5) Includes originators or servicers of financial assets collateralized by consumer loans such as auto loans and leases, and credit cards.
Our commercial and industrial loans and lease financing
portfolio also included non-U.S. loans of $79.7 billion and
$78.0 billion at December 31, 2022 and 2021, respectively.
Significant industry concentrations of non-U.S. loans at
December 31, 2022 and 2021, respectively, included:
•
$45.7 billion and $46.7 billion in the financials except banks
industry;
• $14.1 billion and $15.9 billion in the banks industry; and
• $1.2 billion and $1.7 billion in the oil, gas and pipelines
industry.
Risk mitigation actions, including the restructuring of
repayment terms, securing collateral or guarantees, and entering
into extensions, are based on a re-underwriting of the loan and
our assessment of the borrower’s ability to perform under the
agreed-upon terms. Extension terms generally range from six to
thirty-six months and may require that the borrower provide
additional economic support in the form of partial repayment, or
additional collateral or guarantees. In cases where the value of
collateral or financial condition of the borrower is insufficient to
Wells Fargo & Company 33
Risk Management – Credit Risk Management (continued)
repay our loan, we may rely upon the support of an outside
repayment guarantee in providing the extension.
Our ability to seek performance under a guarantee is directly
related to the guarantor’s creditworthiness, capacity and
willingness to perform, which is evaluated on an annual basis, or
more frequently as warranted. Our evaluation is based on the
most current financial information available and is focused on
various key financial metrics, including net worth, leverage, and
current and future liquidity. We consider the guarantor’s
reputation, creditworthiness, and willingness to work with us
based on our analysis as well as other lenders’ experience with
the guarantor. Our assessment of the guarantor’s credit strength
is reflected in our loan risk ratings for such loans. The loan risk
rating and accruing status are important factors in our allowance
for credit losses methodology.
In considering the accrual status of the loan, we evaluate
the collateral and future cash flows as well as the anticipated
support of any repayment guarantor. In many cases, the
strength of the guarantor provides sufficient assurance that full
repayment of the loan is expected. When full and timely
collection of the loan becomes uncertain, including the
performance of the guarantor, we place the loan on nonaccrual
status. As appropriate, we also charge the loan down in
accordance with our charge-off policies, generally to the net
realizable value of the collateral securing the loan, if any.
COMMERCIAL REAL ESTATE (CRE) Our CRE loan portfolio is
comprised of CRE mortgage and CRE construction loans. We
generally subject CRE loans to individual risk assessment using
our internal borrower and collateral quality ratings. We had
$11.3 billion of CRE mortgage loans classified as criticized at
December 31, 2022, compared with $13.1 billion at
December 31, 2021, and $1.1 billion of CRE construction loans
classified as criticized at December 31, 2022, compared with
$1.7 billion at December 31, 2021. The decrease in criticized CRE
loans was driven by the hotel/motel and shopping center
property types, as these property types continued to recover
from the economic impacts of the COVID-19 pandemic, partially
offset by an increase in the office buildings and apartment
property types. Criticized CRE loans at December 31, 2022,
increased compared with September 30, 2022, primarily due to
an increase in the office buildings property type. The credit
quality of the office buildings property type could continue to be
adversely affected if weakened demand for office space
continues to drive higher vacancy rates and deteriorating
operating performance. At December 31, 2022, nearly one-third
of the CRE loans in the office buildings property type had
recourse to a guarantor, typically through a repayment
guarantee, in addition to the related collateral.
The total CRE loan portfolio increased $8.0 billion from
December 31, 2021, predominantly driven by an increase in loans
for apartments and industrial/warehouse property types,
partially offset by a decrease in loans for the shopping center
property type. The CRE loan portfolio included $7.6 billion of
non-U.S. CRE loans at December 31, 2022, down from
$8.7 billion at December 31, 2021. The portfolio is diversified
both geographically and by property type. The largest geographic
concentrations of CRE loans are in California, New York, Texas,
and Florida, which represented a combined 49% of the total CRE
portfolio. The largest property type concentrations are
apartments at 26% and office buildings at 23% of the portfolio.
The unfunded credit commitments were $8.8 billion and
$11.5 billion at December 31, 2022 and 2021, respectively, for
CRE mortgage loans and $20.7 billion and $20.0 billion,
respectively, for CRE construction loans.
Wells Fargo & Company 34
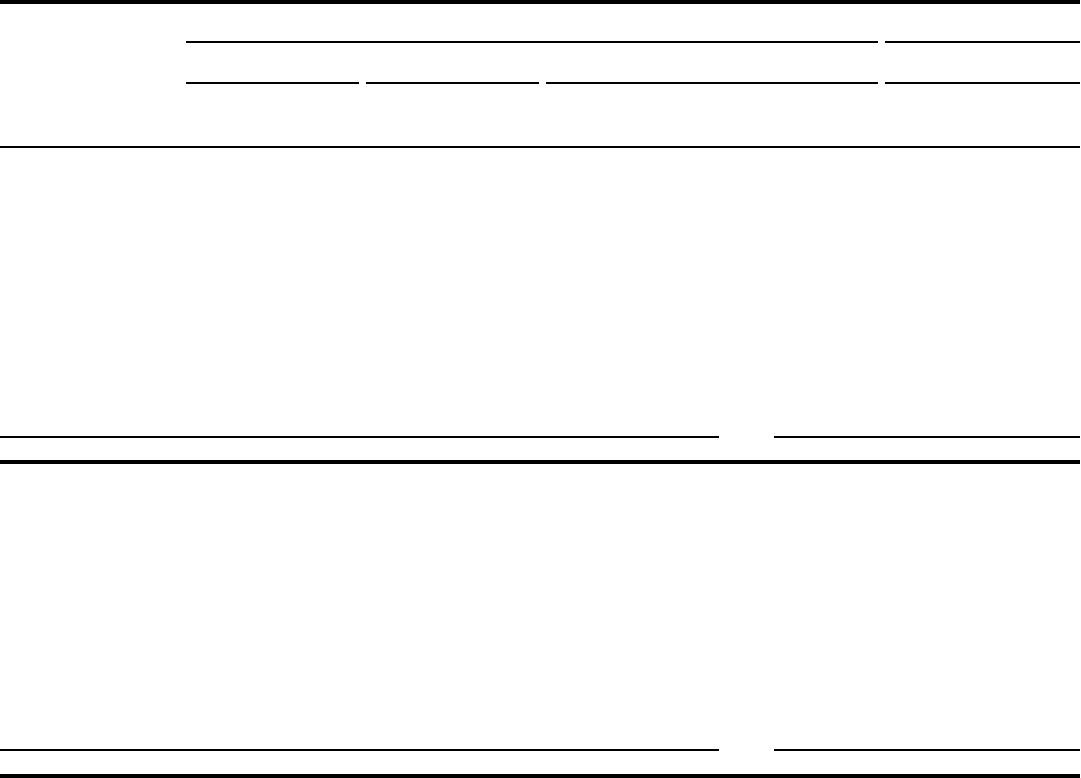
Table 19 provides our CRE loans by state and property type.
Table 19: CRE Lo ans by S tate a nd Property Type
Dec 31, 2022 Dec 31, 2021
Real estate mortgage Real estate construction Total commercial real estate Total commercial real estate
($ in millions)
Nonaccrual
loans
Loans
outstanding
balance
Nonaccrual
loans
Loans
outstanding
balance
Nonaccrual
loans
Loans
outstanding
balance
Loans
as % of
total
loans
Total
commitments
(1)
Loans
outstanding
balance
Total
commitments
(1)
By state:
California $ 121 29,531 1 4,754 122 34,285 4% $ 39,594 34,668 40,241
New York 106 15,009 — 2,285 106 17,294 2 19,360 15,636 17,967
Texas 23 11,564 — 1,243 23 12,807 1 14,941 10,605 12,263
Florida 10 9,833 — 1,585 10 11,418 1 14,690 10,435 13,219
Washington 80 4,253 — 1,350 80 5,603 * 6,868 5,301 7,013
Georgia 69 4,661 — 767 69 5,428 * 6,651 4,662 5,857
North Carolina 4 4,345 — 882 4 5,227 * 6,650 4,755 6,160
Arizona 14 4,761 — 541 14 5,302 * 6,288 5,046 5,975
New Jersey 7 2,738 — 1,381 7 4,119 * 5,660 3,625 4,793
Illinois 11 3,988 — 603 11 4,591 * 5,394 4,042 4,560
Other (2) 511 41,546 1 8,182 512 49,728 5 59,224 49,050 61,235
Total 132,229 2 23,573 958 155,802 16% 147,825 179,283
By property:
Apartments 31,205 — 8,538 8 39,743 4% 31,901 42,119
Office buildings 186 32,478 — 3,666 186 36,144 4 40,827 36,736 42,781
Industrial/warehouse 42 17,244 — 3,390 42 20,634 2 24,546 17,714 20,967
Hotel/motel 153 11,212 — 1,539 153 12,751 1 13,758 12,764 13,179
Retail (excl shopping center) 197 11,621 2 132 199 11,753 1 12,486 12,450 13,014
Shopping center 259 9,014 — 520 259 9,534 * 10,131 10,448 11,082
Institutional 33 5,201 — 2,524 33 7,725 * 9,178 7,743 9,588
Mixed use properties 54 4,906 — 981 54 5,887 * 7,139 6,303 10,718
Collateral pool — 3,031 — 31 — 3,062 * 3,662 3,509 4,106
Storage facility — 2,772 — 157 — 2,929 * 3,201 2,257 2,742
Other 24 3,545 — 2,095 24 5,640 * 8,825 6,000 8,987
Total 132,229 2 23,573 958 155,802 16 % $ 185,320 147,825 179,283
$ 956 $ 185,320
$ 8 $ 51,567
$ 956
* Less than 1%.
(1)
Total commitments consist of loans outstanding plus unfunded credit commitments, excluding issued letters of credit. For additional information on issued letters of credit, see
Note 17 (Guarantees and Other Commitments) to Financial Statements in this Report.
(2) Includes 40 states; no state in Other had loans in excess of $4.1 billion and $3.7 billion at December 31, 2022 and 2021, respectively.
NON-U.S. LOANS Our classification of non-U.S. loans is based on
whether the borrower’s primary address is outside of the United
States. At December 31, 2022, non-U.S. loans totaled
$87.5 billion, representing approximately 9% of our total
consolidated loans outstanding, compared with $86.9 billion, or
approximately 10% of our total consolidated loans outstanding,
at December 31, 2021. Non-U.S. loans were approximately 5%
and 4% of our total consolidated assets at December 31, 2022
and 2021, respectively.
COUNTRY RISK EXPOSURE Our country risk monitoring process
incorporates centralized monitoring of economic, political, social,
legal, and transfer risks in countries where we do or plan to do
business, along with frequent dialogue with our customers,
counterparties and regulatory agencies. We establish exposure
limits for each country through a centralized oversight process
based on customer needs, and through consideration of the
relevant and distinct risk of each country. We monitor exposures
closely and adjust our country limits in response to changing
conditions. We evaluate our individual country risk exposure
based on our assessment of the borrower’s ability to repay,
which gives consideration for allowable transfers of risk, such as
guarantees and collateral, and may be different from the
reporting based on the borrower’s primary address.
Our largest single country exposure outside the U.S. at
December 31, 2022, was the United Kingdom, which totaled
$33.2 billion, or approximately 2% of our total assets, and
included $5.5 billion of sovereign claims. Our United Kingdom
sovereign claims arise from deposits we have placed with the
Bank of England pursuant to regulatory requirements in support
of our London branch.
Table 20 provides information regarding our top 20
exposures by country (excluding the U.S.), based on our
assessment of risk, which gives consideration to the country of
any guarantors and/or underlying collateral. With respect to
Table 20:
• Lending and deposits exposure includes outstanding loans,
unfunded credit commitments, and deposits with non-U.S.
banks. These balances are presented prior to the deduction
of allowance for credit losses or collateral received under the
terms of the credit agreements, if any.
Wells Fargo & Company 35
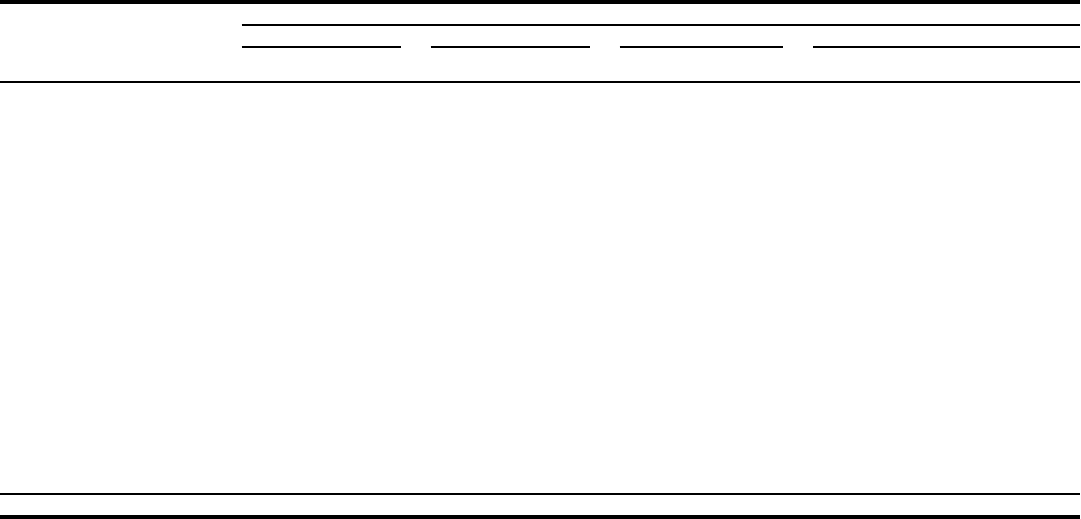
• Securities exposure represents debt and equity securities of
non-U.S. issuers. Long and short positions are netted, and
net short positions are reflected as negative exposure.
• Derivatives and other exposure represents foreign exchange
contracts, derivative contracts, securities resale agreements,
and securities lending agreements.
Table 20: Select C ountry Expo sures
December 31, 2022
Lending and deposits Securities Derivatives and other Total exposure
($ in millions) Sovereign
Non-
sovereign Sovereign
Non-
sovereign Sovereign
Non-
sovereign Sovereign
Non-
sovereign (1) Total
Top 20 country exposures:
United Kingdom $ 5,513 24,291 — 1,102 2 2,299 5,515 27,692 33,207
Canada 1 18,051 1 582 69 294 71 18,927 18,998
Cayman Islands — 8,464 — — — 179 — 8,643 8,643
Luxembourg — 6,719 — 32 — 177 — 6,928 6,928
Japan 5,658 700 — 365 — 46 5,658 1,111 6,769
Ireland 6 4,888 — 223 — 107 6 5,218 5,224
France 57 4,138 — 108 175 72 232 4,318 4,550
Germany — 3,910 — 29 — 202 — 4,141 4,141
Bermuda — 3,600 — 35 — 30 — 3,665 3,665
Guernsey — 3,375 — — — 12 — 3,387 3,387
South Korea — 2,983 (1) 381 1 15 — 3,379 3,379
China 17 2,966 1 259 17 35 35 3,260 3,295
Netherlands — 3,165 — (6) — 124 — 3,283 3,283
Chile — 1,939 — 212 — — — 2,151 2,151
Australia — 1,969 — 5 — 30 — 2,004 2,004
Brazil — 1,499 — 1 9 — 9 1,500 1,509
United Arab Emirates — 1,477 — 11 — — — 1,488 1,488
Switzerland — 1,202 — (4) — 170 — 1,368 1,368
India 250 1,072 (64) (5) — 1 186 1,068 1,254
Belgium — 1,103 — 1 — 4 — 1,108 1,108
Total top 20 country exposures 97,511 (63) 3,331 273 3,797 11,712 104,639 116,351
Risk Management – Credit Risk Management (continued)
$ 11,502
(1) Total non-sovereign exposure comprised $51.2 billion exposure to financial institutions and $53.4 billion to non-financial corporations at December 31, 2022.
RESIDENTIAL MORTGAGE LOANS Our residential mortgage loan
portfolio is comprised of 1–4 family first and junior lien mortgage
loans. Residential mortgage – first lien loans comprised 95% of
the total residential mortgage loan portfolio at December 31,
2022, compared with 94% at December 31, 2021.
The residential mortgage loan portfolio includes loans with
adjustable-rate features. We monitor the risk of default as a
result of interest rate increases on adjustable-rate mortgage
(ARM) loans, which may be mitigated by product features that
limit the amount of the increase in the contractual interest rate.
The default risk of these loans is considered in our ACL for loans.
ARM loans were 7% of total loans at both December 31, 2022
and 2021, with an initial reset date in 2025 or later for the
majority of this portfolio at December 31, 2022. We do not offer
option ARM products, nor do we offer variable-rate mortgage
products with fixed payment amounts, commonly referred to
within the financial services industry as negative amortizing
mortgage loans.
The residential mortgage – junior lien portfolio consists of
residential mortgage lines of credit and loans that are
subordinate in rights to an existing lien on the same property.
These lines and loans may have draw periods, interest-only
payments, balloon payments, adjustable rates and similar
features. Junior lien loan products are primarily amortizing
payment loans with fixed interest rates and repayment periods
between five to 30 years. We continuously monitor the credit
performance of our residential mortgage – junior lien portfolio
for trends and factors that influence the frequency and severity
of losses, such as junior lien performance when the first lien loan
is delinquent.
The outstanding balance of residential mortgage lines of
credit was $18.3 billion at December 31, 2022. The unfunded
credit commitments for these lines of credit totaled $35.5 billion
at December 31, 2022. Our residential mortgage lines of credit
(both first and junior lien) generally have draw periods of 10, 15
or 20 years with variable interest rate and payment options
available during the draw period of (1) interest-only or (2) 1.5%
of outstanding principal balance plus accrued interest. As of
December 31, 2022, a significant portion of the lines of credit in
a draw period used the interest-only option. The lines that enter
their amortization period may experience higher delinquencies
and higher loss rates than the ones in their draw or term period.
We have considered this increased risk in our ACL for loans
estimate. Interest-only lines and loans were approximately 2%
and 3% of total loans at December 31, 2022 and 2021,
respectively.
During the draw period, the borrower has the option of
converting all or a portion of the line from a variable interest rate
to a fixed rate with terms including interest-only payments for a
fixed period between three to seven years or a fully amortizing
payment with a fixed period between five to 30 years. At the end
of the draw period, a line of credit generally converts to an
amortizing payment schedule with repayment terms of up to
30 years based on the balance at time of conversion. Certain lines
and loans have been structured with a balloon payment, which
requires full repayment of the outstanding balance at the end of
the term period. The conversion of lines or loans to fully
amortizing or balloon payoff may result in a significant payment
increase, which can affect some borrowers’ ability to repay the
outstanding balance.
In anticipation of our residential mortgage line of credit
borrowers reaching the end of their draw period, we have created
a program to inform, educate and help these borrowers
transition from interest-only to fully-amortizing payments or full
repayment. We monitor the performance of the borrowers
moving through the program in an effort to refine our ongoing
program strategy.
Wells Fargo & Company 36
We monitor changes in real estate values and underlying
economic or market conditions for all geographic areas of our
residential mortgage portfolio as part of our credit risk
management process. Our periodic review of this portfolio
includes original appraisals adjusted for the change in Home Price
Index (HPI) or estimates from automated valuation models
(AVMs) to support property values. AVMs are computer-based
tools used to estimate the market value of homes. We have
processes to periodically validate AVMs and specific risk
management guidelines addressing the circumstances when
AVMs may be used. For additional information about our use of
appraisals and AVMs, see Note 5 (Loans and Related Allowance
for Credit Losses) to Financial Statements in this Report.
Part of our credit monitoring includes tracking delinquency,
current FICO scores and loan/combined loan to collateral values
(LTV/CLTV) on the entire residential mortgage loan portfolio.
CLTV represents the ratio of the total loan balance of first and
junior lien mortgages (including unused line amounts for credit
line products) to property collateral value. For additional
information regarding credit quality indicators, see Note 5 (Loans
and Related Allowance for Credit Losses) to Financial Statements
in this Report.
We continue to modify residential mortgage loans to assist
homeowners and other borrowers experiencing financial
difficulties. Under these programs, we may provide concessions
such as interest rate reductions, forbearance of principal, and in
some cases, principal forgiveness. These programs generally
include trial payment periods of three to four months, and after
successful completion and compliance with terms during this
period, the loan is permanently modified. Loans included under
these programs are accounted for as troubled debt
restructurings (TDRs) at the start of the trial period or at the
time of permanent modification, if no trial period is used.
Customer payment deferral activities instituted in response to
the COVID-19 pandemic could continue to delay the recognition
of delinquencies. For additional information on customer
accommodations, including loan modifications, in response to
the COVID-19 pandemic, see Note 1 (Summary of Significant
Accounting Policies) to Financial Statements in this Report.
Residential Mortgage – First Lien Portfolio Our residential
mortgage – first lien portfolio increased $13.5 billion from
December 31, 2021, driven by originations, partially offset by
loan paydowns and the transfer of first lien mortgage loans to
loans held for sale (LHFS), which predominantly related to loans
purchased from GNMA loan securitization pools in prior periods.
Table 21 shows certain delinquency and loss information for
the residential mortgage – first lien portfolio and lists the top
five states by outstanding balance.
Table 21: Residential Mortgage – First Lien Portfolio Performance
Outstanding balance % of total loans
% of loans 30 days
or more past due Net loan charge-off rate (1)
December 31, December 31, December 31, Year ended December 31,
($ in millions) 2022 2021 2022 2021 2022 2021 2022 2021
California (2) $ 110,877 100,933 11.60% 11.27 0.45 0.95 — (0.01)
New York 31,753 30,039 3.32 3.35 0.80 1.34 (0.02) 0.12
Florida 10,535 9,978 1.10 1.11 1.13 1.93 (0.08) 0.09
Washington 10,523 8,636 1.10 0.96 0.30 0.47 — —
New Jersey 10,416 10,205 1.09 1.14 1.24 1.95 0.01 0.08
Other (3) 72,843 69,321 7.62 7.74 0.93 1.48 0.01 0.01
Total 246,947 229,112 25.83 25.57 0.69 1.23 — 0.02
Government insured/guaranteed loans (4) 8,860 13,158 0.93 1.47
Total first lien mortgage portfolio 242,270 26.76% 27.04
$ 255,807
(1)
The net loan charge-off rate for the year ended December 31, 2021, includes $120 million of loan charge-offs related to a change in practice to fully charge-off certain delinquent legacy residential
mortgage loans.
(2) Our residential mortgage loans to borrowers in California are located predominantly within the larger metropolitan areas, with no single California metropolitan area consisting of more than 4% of
total loans.
(3) Consists of 45 states; no state in Other had loans in excess of $7.7 billion and $7.2 billion at December 31, 2022, and 2021, respectively.
(4) Represents loans, substantially all of which were purchased from GNMA loan securitization pools, where the repayment of the loans is predominantly insured by the Federal Housing Administration
(FHA) or guaranteed by the Department of Veterans Affairs (VA). For additional information on GNMA loan securitization pools, see the “Risk Management – Credit Risk Management – Mortgage
Banking Activities” section in this Report.
Wells Fargo & Company 37
Residential Mortgage – Junior Lien Portfolio Our residential
mortgage – junior lien portfolio decreased $3.3 billion from
December 31, 2021, driven by loan paydowns.
Table 22 shows certain delinquency and loss information for
the residential mortgage – junior lien portfolio and lists the top
five states by outstanding balance.
Table 22: Residential Mo rtgage – Junio r Lien Po rtfolio Performance
Outstanding balance % of total loans
% of loans 30 days
or more past due Net loan charge-off rate (1)
December 31, December 31, December 31, Year ended December 31,
($ in millions) 2022 2021 2022 2021 2022 2021 2022
2021
California $ 3,550 4,310 0.37 % 0.48 2.02 3.52 (0.26) (0.59)
New Jersey 1,383 1,728 0.14 0.19 2.76 2.98 0.10 0.04
Florida 1,165 1,533 0.12 0.17 2.69 2.54 (0.71) (0.13)
Pennsylvania 832 1,039 0.09 0.12 2.76 2.19 (0.17) (0.12)
New York 794 975 0.08 0.11 2.86 4.05 (0.09) 0.57
(2)Other 5,586 7,033 0.58 0.79 2.05 2.25 (0.53) (0.51)
Total junior lien mortgage portfolio $ 13,310 16,618 1.38 % 1.86 2.27 2.91 (0.36) (0.36)
December 31, 2022 December 31, 2021
% of
total
loans
% of
total
loans ($ in millions)
Outstanding
balance
Outstanding
balance
Credit card $ 46,293 4.84% $ 38,453 4.29%
Auto 53,669 5.61 56,659 6.33
(1)Other consumer 29,276 3.06 28,274 3.16
Total $ 129,238 13.51% $ 123,386 13.78%
Risk Management – Credit Risk Management (continued)
(1)
The net loan charge-off rate for the year ended December 31, 2021, includes $32 million of loan charge-offs related to a change in practice to fully charge-off certain delinquent legacy residential
mortgage loans.
(2) Consists of 45 states; no state in Other had loans in excess of $790 million and $980 million at December 31, 2022, and 2021, respectively.
CREDIT C ARD, AUTO, AND OTHER C ONSUMER LOANS Table 23
shows the outstanding balance of our credit card, auto, and oth er
consumer loan portfolios. For information regarding credit
quality indicators for these portfolios, see Note 5 (Loans and
Related Allowance for Credit Losses ) to Financial Statements in
this Report.
Credit Card The increase in the outstanding balance at
December 31, 2022 , compared with December 31, 2021 , was
due to higher purchase volume and the launch of new products.
Auto The decrease in the outstanding balance at December 31,
2022, compared with December 31, 2021 , was due to lower
origination volumes reflecting credit tightening actions and
continued price competition due to rising interest rates.
Other Consumer The increase in the outstanding balance at
December 31, 2022 , compared with December 31, 2021 , was
primarily due to originations of personal lines and loans.
Table 23: Credit C ard, Auto, and Other C onsumer Lo ans
(1) Includes $19.4 billion and $18.6 billion at December 31, 2022 and 2021, respectively, of
commercial and consumer securities-based loans originated by the WIM operating
segment.
Wells Fargo & Company 38
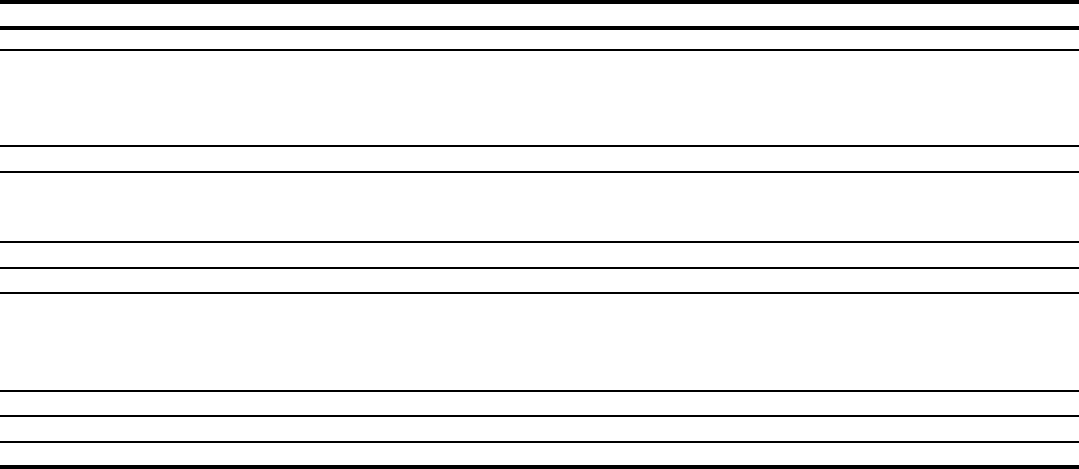
NONPERFORMING ASSETS (NONACCRUAL LOANS AND FORECLOSED
ASSETS) We generally place loans on nonaccrual status when:
• the full and timely collection of interest or principal becomes
uncertain (generally based on an assessment of the
borrower’s financial condition and the adequacy of collateral,
if any), such as in bankruptcy or other circumstances;
• they are 90 days (120 days with respect to residential
mortgage loans) past due for interest or principal, unless the
loan is both well-secured and in the process of collection;
• part of the principal balance has been charged off; or
• for junior lien mortgage loans, we have evidence that the
related first lien mortgage may be 120 days past due or in
the process of foreclosure regardless of the junior lien
delinquency status.
Certain nonaccrual loans may be returned to accrual status
after they perform for a period of time. Consumer credit card
loans are not placed on nonaccrual status, but are generally fu lly
charged off when the loan reaches 180 days past due.
Customer payment deferral activities in the residential
mortgage portfolio instituted in response to the COVID-19
pandemic could continue to delay the recognition of nonaccrual
loans for those residential mortgage customers who would have
otherwise moved into nonaccrual status.
For additional
information on customer accommodations, including loan
modifications, in response to the COVID-19 pandemic, see
Note 1 (Summary of Significant Accounting Policies) to Financial
Statements in this Report.
Table 24 summarizes nonperforming assets (NPAs).
Table 24: Nonperforming Assets (Nonaccrual Loans and Foreclosed Assets)
December 31,
($ in millions) 2022 2021
Nonaccrual loans:
Commercial and industrial $ 746 980
Commercial real estate 958 1,248
Lease financing 119 148
Total commercial 1,823 2,376
Residential mortgage (1) 3,611 4,604
Auto 153 198
Other consumer 39 34
Total consumer 3,803 4,836
Total nonaccrual loans $ 5,626 7,212
As a percentage of total loans
Foreclosed assets:
0.59 % 0.81
Government insured/guaranteed (2)
Non-government insured/guaranteed
$ 22
115
16
96
Total foreclosed assets 137
112
Total nonperforming assets $ 5,763 7,324
As a percentage of total loans 0.60 %
0.82
(1) Residential mortgage loans predominantly insured by the FHA or guaranteed by the VA are not placed on nonaccrual status because they are insured or guaranteed.
(2) Consistent with regulatory reporting requirements, foreclosed real estate resulting from government insured/guaranteed loans are classified as nonperforming. Both principal and interest related to
these foreclosed real estate assets are collectible because the loans were predominantly insured by the FHA or guaranteed by the VA. Receivables related to the foreclosure of certain government
guaranteed real estate mortgage loans are excluded from this table and included in Accounts Receivable in Other Assets. For additional information on the classification of certain government-
guaranteed mortgage loans upon foreclosure, see Note 1 (Summary of Significant Accounting Policies) to Financial Statements in this Report.
Commercial nonaccrual loans decreased $553 million from
December 31, 2021, due to improved credit quality across our
commercial loan portfolios. For additional information on
commercial nonaccrual loans, see the “Risk Management – Credit
Risk Management – Commercial and Industrial Loans and Lease
Financing” and “Risk Management – Credit Risk Management –
Commercial Real Estate” sections in this Report.
Consumer nonaccrual loans decreased $1.0 billion from
December 31, 2021, driven by a decrease in residential mortgage
nonaccrual loans primarily due to sustained payment
performance of borrowers after exiting COVID-19-related
accommodation programs.
Wells Fargo & Company
39
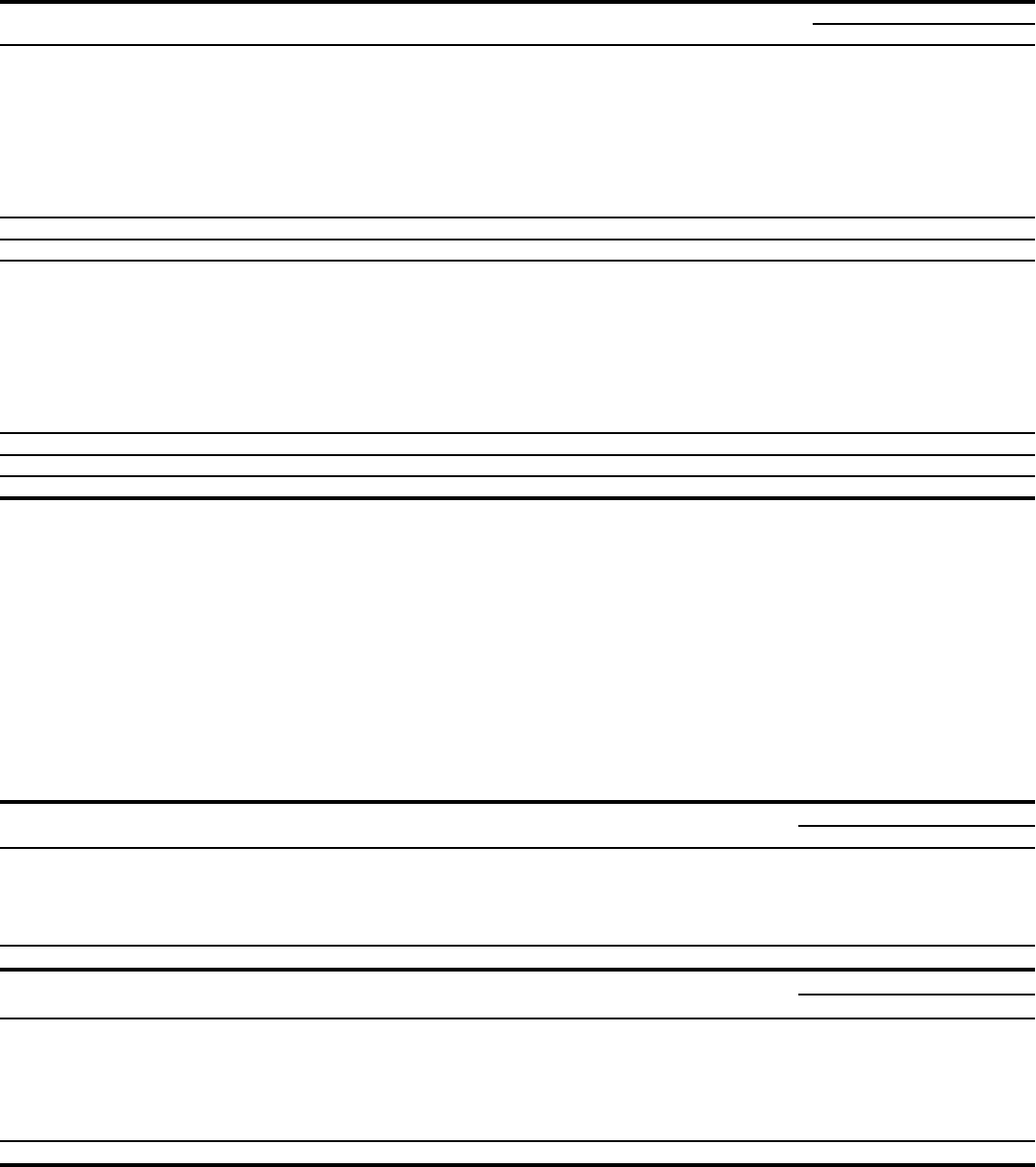
Table 25 provides an analysis of the changes in nonaccrual
loans. Typically, changes to nonaccrual loans period-over-perio d
represent inflows for loans that are placed on nonaccrual statu s
in accordance with our policies, offset by reductions for loan s
that are paid down, charged off, sold, foreclosed, or are no lo nger
classified as nonaccrual as a result of continued performance a nd
an improvement in the borrower’s financial condition and loan
repayment capabilities.
Table 25: Analysis o f C hanges in No naccrual Lo ans
Year ended December 31,
(in millions) 2022 2021
Commercial nonaccrual loans
Balance, beginning of period $ 2,376 4,779
Inflows 1,391 2,113
Outflows:
Returned to accruing (451) (1,003)
Foreclosures (20) (13)
Charge-offs (247) (533)
Payments, sales and other (1,226) (2,967)
Total outflows (1,944) (4,516)
Balance, end of period 1,823 2,376
Consumer nonaccrual loans
Balance, beginning of period 4,836 3,949
Inflows 1,728 3,281
Outflows:
Returned to accruing (1,599) (828)
Foreclosures (85) (69)
Charge-offs (245) (252)
Payments, sales and other (832) (1,245)
Total outflows (2,761) (2,394)
Balance, end of period 3,803 4,836
Total nonaccrual loans $ 5,626 7,212
Year ended December 31,
(in
millions) 2022 2021
Analysis of changes in foreclosed assets
Balance, beginning of period
$ 112 159
Net change in government insured/guaranteed (1) 6 (2)
Additions to foreclosed assets (2) 420 370
Reductions from sales and write-downs (401) (415)
Balance, end of period
$ 137 112
Risk Management – Credit Risk Management (continued)
We considered the risk of losses on nonaccrual loans in
developing our allowance for loan losses. We believe exposure to
losses on nonaccrual loans is mitigated by the following factors
at December 31, 2022:
•
97% of total commercial nonaccrual loans are secured, the
majority of which are secured by real estate.
• 81% of commercial nonaccrual loans were current on
interest and 77% of commercial nonaccrual loans were
current on both principal and interest, but were on
nonaccrual status because the full or timely collection of
interest or principal had become uncertain.
Table 26: Foreclosed Assets
• 99% of total consumer nonaccrual loans are secured, of
which 95% are secured by real estate and 98% have a
combined LTV (CLTV) ratio of 80% or less.
• $588 million of the $743 million of consumer loans in
bankruptcy or discharged in bankruptcy, and classified as
nonaccrual, were current.
Table 26 provides a summary of foreclosed assets and an
analysis of changes in foreclosed assets.
December 31,
(in millions) 2022 2021
Summary by loan segment
Government insured/guaranteed $
22
16
Commercial 65 54
Consumer 50 42
Total foreclosed assets $
137
112
(1)
Foreclosed government insured/guaranteed loans are temporarily transferred to and held by us as servicer, until reimbursement is received from FHA or VA.
(2) Includes loans moved into foreclosed assets from nonaccrual status and repossessed autos.
Wells Fargo & Company 40
As part of our actions to support customers during the
COVID-19 pandemic, we temporarily suspended certain
residential mortgage foreclosure activities through
December 31, 2021. Beginning January 1, 2022, we resumed
these mortgage foreclosure activities. For additional information
on loans in process of foreclosure, see Note 5 (Loans and Related
Allowance for Credit Losses) to Financial Statements in this
Report.
TROUBLED DEBT RESTRUCTURINGS (TDRs) Table 27 provides
information regarding the recorded investment of loans
modified in TDRs. TDRs decreased from December 31, 2021,
predominantly driven by a decrease in residential mortgage
loans, partially offset by an increase in trial modifications. The
decrease in residential mortgage loans was due to paydowns and
transfers to LHFS, which related to loans purchased from GNMA
loan securitization pools. In January 2023, we adopted a new
accounting standard that eliminates the accounting and
reporting guidance for TDRs. For additional information, see the
“Current Accounting Developments” section in this Report.
The amount of our TDRs at December 31, 2022, would have
otherwise been higher without the TDR relief provided by the
Coronavirus Aid, Relief, and Economic Security Act (CARES Act)
and the Interagency Statement on Loan Modifications and
Reporting for Financial Institutions Working with Customers
Affected by the Coronavirus (Revised) (Interagency Statement).
Customers who are unable to resume making their contractual
loan payments upon exiting from these deferral programs may
require further assistance and may receive or be eligible to
receive modifications, which may be classified as TDRs. For
additional information on customer accommodations, including
loan modifications, in response to the COVID-19 pandemic, see
Note 1 (Summary of Significant Accounting Policies) to Financial
Statements in this Report.
Table 27: TDR Balances
December 31,
(in millions) 2022 2021
Commercial and industrial $ 543 793
Commercial real estate 431 545
Lease financing 5 10
Total commercial TDRs 979 1,348
Residential mortgage 7,429 8,228
Credit card 407 309
Auto 118 169
Other consumer 58 57
Trial modifications 242 71
Total consumer TDRs 8,254 8,834
Total TDRs $ 9,233 10,182
TDRs on nonaccrual status $ 3,223 3,142
TDRs on accrual status:
Government insured/guaranteed 1,870 2,462
Non-government insured/guaranteed 4,140 4,578
Total TDRs $ 9,233 10,182
Our nonaccrual policies are generally the same for all loan
types when a restructuring is involved. We may re-underwrite
loans at the time of restructuring to determine whether there is
sufficient evidence of sustained repayment capacity based on the
borrower’s documented income, debt to income ratios, and other
factors. Loans that are not re-underwritten or loans that lack
sufficient evidence of sustained repayment capacity at the time
of modification are charged down to the fair value of the
collateral, if applicable. For an accruing loan that has been
modified, if the borrower has demonstrated performance under
the previous terms and the underwriting process shows the
capacity to continue to perform under the restructured terms,
the loan will generally remain in accruing status. Otherwise, the
loan will be placed in nonaccrual status and may be returned to
accruing status when the borrower demonstrates a sustained
period of performance, generally six consecutive months of
payments, or equivalent, inclusive of consecutive payments made
prior to modification. Loans will also be placed on nonaccrual
status, and a corresponding charge-off is recorded to the loan
balance, when we believe that principal and interest contractually
due under the modified agreement will not be collectible. See
Note 5 (Loans and Related Allowance for Credit Losses) to
Financial Statements in this Report for additional information
regarding TDRs.
Wells Fargo & Company 41
Table 28 provides an analysis of the changes in TDRs. Loans
modified more than once as a TDR are reported as inflows only i n
the period they are first modified. In addition to foreclosures ,
sales and transfers to held for sale, we may remove loans from
TDR classification, but only if they have been refinanced or
restructured at market terms and qualify as a new loan.
Table 28: Analysis of Changes in TDRs
Year ended December 31,
(in millions)
2022 2021
Commercial TDRs
Balance, beginning of period $ 1,348 2,731
Inflows (1) 544
746
Outflows
Charge-offs (10) (141)
Foreclosure — (5)
Payments, sales and other (2) (903) (1,983)
Balance, end of period 979 1,348
Consumer TDRs
Balance, beginning of period 8,834 11,792
Inflows (1) 1,892 1,665
Outflows
Charge-offs (150) (185)
Foreclosure (54) (56)
Payments, sales and other (2) (2,439) (4,363)
(3)Net change in trial modifications 171 (19)
Balance, end of period 8,254 8,834
Total TDRs
$ 9,233
Risk Management – Credit Risk Management (continued)
10,182
(1) Inflows include loans that modify, even if they resolve within the period, as well as gross advances on term loans that modified in a prior period and net advances on revolving TDRs that modified in a
prior period.
(2) Other outflows include normal amortization/accretion of loan basis adjustments and loans transferred to LHFS. Occasionally, loans that have been refinanced or restructured at market terms qualify
as new loans, which are also included as other outflows.
(3) Net change in trial modifications includes: inflows of new TDRs entering the trial payment period, net of outflows for modifications that either (i) successfully perform and enter into a permanent
modification or (ii) did not successfully perform according to the terms of the trial period plan and are subsequently charged-off, foreclosed upon, or otherwise resolved.
Wells Fargo & Company 42
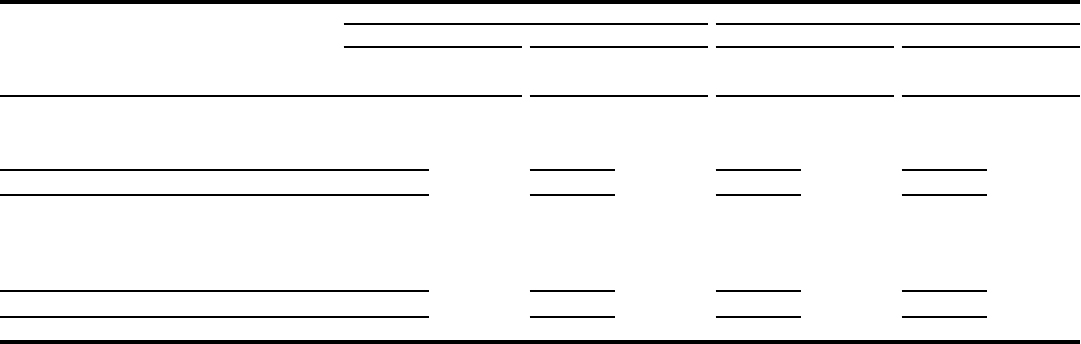
NET C HARGE-OFFS Table 29 presents net loan charge-offs.
Table 29: Net Loan Charge-offs
Quarter ended December 31, Year ended December 31,
2022 2021 2022 2021
($ in millions)
Net loan
charge-
offs
% of
avg.
loans (1)
Net loan
charge-
offs
% of
avg.
loans (1)
Net loan
charge-
offs
% of
avg.
loans
Net loan
charge-
offs
% of
avg.
loans
Commercial and industrial $ 66 0.07 % $ 3 — % $ 83 0.02 % $ 218 0.07 %
Commercial real estate 10 0.03 22 0.06 (11) (0.01) 53 0.04
Lease financing 3 0.06 3 0.09 7 0.04 24 0.15
Total commercial 79 0.06 28 0.02 79 0.01 295 0.06
Residential mortgage (12) (0.02) 118 0.18 (63) (0.02) (17) (0.01)
Credit card 274 2.42 150 1.61 851 2.06 800 2.26
Auto 137 1.00 58 0.41 422 0.76 181 0.35
Other consumer 82 1.13 67 0.96 319 1.11 315 1.22
Total consumer 481 0.48 393 0.41 1,529 0.39 1,279 0.33
Total $ 560 0.23 % $ 421 0.19 % $ 1,608 0.17 % $ 1,574 0.18 %
(1) Net loan charge-offs as a percentage of average respective loans are annualized.
The decrease in commercial net loan charge-offs in 2022,
compared with 2021, was driven by lower losses in our
commercial and industrial and commercial real estate mortgage
portfolios.
The increase in consumer net loan charge-offs in 2022,
compared with 2021, was predominantly due to higher losses in
our auto portfolio, driven by loans originated in 2021.
The COVID-19 pandemic may continue to impact the credit
quality of our loan portfolio. Although the potential impacts were
considered in our allowance for credit losses for loans, payment
deferral activities in our residential mortgage portfolio instituted
in response to the COVID-19 pandemic could continue to delay
the recognition of residential mortgage loan charge-offs. For
additional information on customer accommodations in
response to the COVID-19 pandemic, see Note 1 (Summary of
Significant Accounting Policies) to Financial Statements in this
Report.
ALLOWANCE FOR CREDIT LOSSES We maintain an allowance for
credit losses (ACL) for loans, which is management’s estimate of
the expected life-time credit losses in the loan portfolio and
unfunded credit commitments, at the balance sheet date,
excluding loans and unfunded credit commitments carried at fair
value or held for sale. Additionally, we maintain an ACL for debt
securities classified as either AFS or HTM, other financial assets
measured at amortized cost, net investments in leases, and other
off-balance sheet credit exposures.
We apply a disciplined process and methodology to establish
our ACL each quarter. The process for establishing the ACL for
loans takes into consideration many factors, including historic al
and forecasted loss trends, loan-level credit quality ratings a nd
loan grade-specific characteristics. The process involves
subjective and complex judgments. In addition, we review a
variety of credit metrics and trends. These credit metrics and
trends, however, do not solely determine the amount of the
allowance as we use several analytical tools. For additional
information on our ACL, see the “Critical Accounting Policies –
Allowance for Credit Losses” section and Note 1 (Summary of
Significant Accounting Policies ) to Financial Statements in this
Report. For additional information on our ACL for loans, see
Note 5 (Loans and Related Allowance for Credit Losses ) to
Financial Statements in this Report, and for additional
information on our ACL for debt securities, see Note 3 (Available-
for-Sale and Held-to-Maturity Debt Securities ) to Financial
Statements in this Report.
Table 30 presents the allocation of the ACL for loans by loan
portfolio segment and class.
Wells Fargo & Company 43
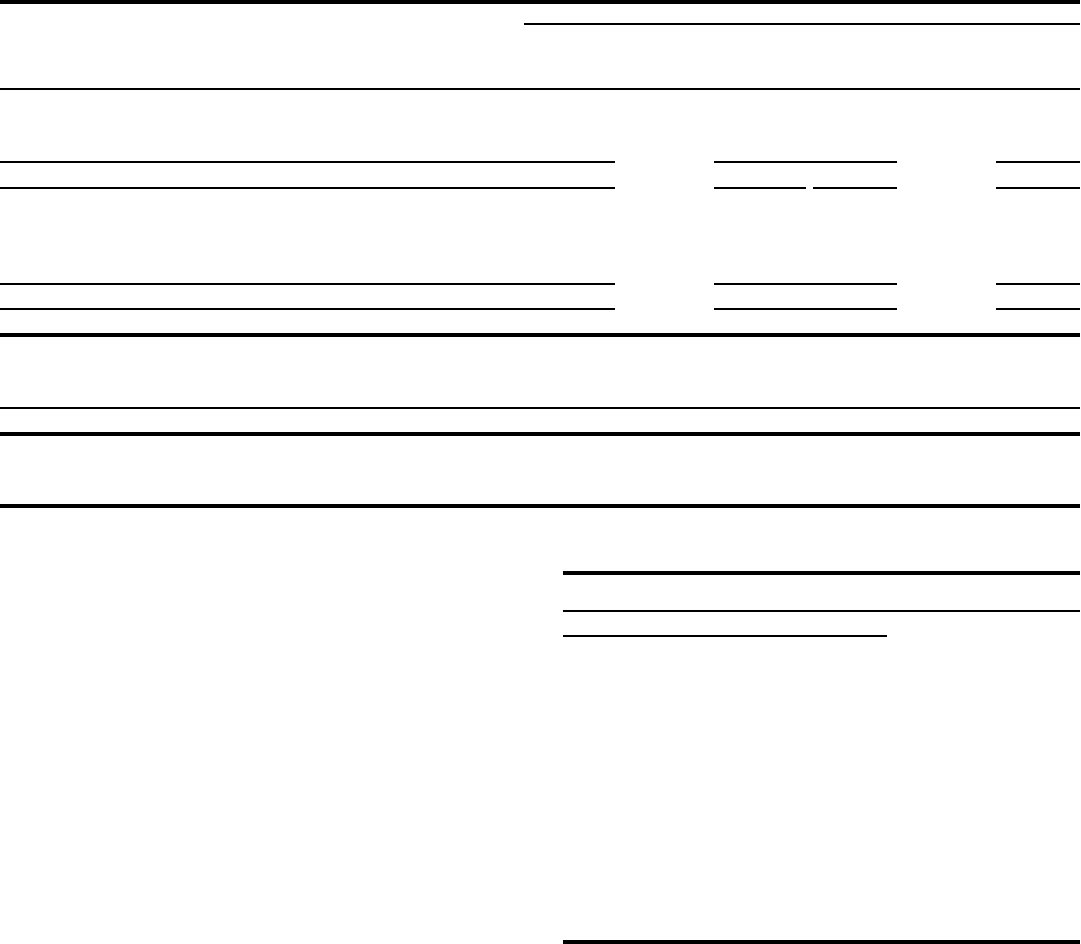
Risk Management – Credit Risk Management (continued)
Table 30: Allocation o f the AC L fo r Lo ans
Dec 31, 2022 Dec 31, 2021
($ in millions) ACL
ACL
as %
of loan
class
Loans
as %
of total
loans ACL
ACL
as %
of loan
class
Loans
as %
of total
loans
Commercial and industrial $ 4,507 1.17 % 40 $ 4,873 1.39 % 39
Commercial real estate 2,231 1.43 16 2,516 1.70 17
Lease financing 218 1.46 2 402 2.71 2
Total commercial 6,956 1.25 58 7,791 1.52 58
Residential mortgage (1) 1,096 0.41 28 1,286 0.50 29
Credit card 3,567 7.71 5 3,290 8.56 4
Auto 1,380 2.57 6 928 1.64 6
Other consumer 610 2.08 3 493 1.74 3
Total consumer 6,653 1.67 42 5,997 1.57 42
Total $ 13,609 1.42 % 100 $ 13,788 1.54 % 100
Components:
Allowance for loan losses $ 12,985 12,490
Allowance for unfunded credit commitments 624 1,298
Allowance for credit losses $ 13,609 13,788
Ratio of allowance for loan losses to total net loan charge-offs 8.08x 7.94
Ratio of allowance for loan losses to total nonaccrual loans 2.31 1.73
Allowance for loan losses as a percentage of total loans 1.36 % 1.39
(1) Includes negative allowance for expected recoveries of amounts previously charged off.
The ratios for the allowance for loan losses and the ACL for
loans presented in Table 30 may fluctuate from period to period
due to such factors as the mix of loan types in the portfolio,
borrower credit strength, and the value and marketability of
collateral.
The ACL for loans decreased $179 million, or 1%, from
December 31, 2021, reflecting reduced uncertainty around the
economic impact of the COVID-19 pandemic on our loan
portfolio. This decrease was partially offset by loan growth and a
less favorable economic environment. The detail of the changes
in the ACL for loans by portfolio segment (including charge-offs
and recoveries by loan class) is included in Note 5 (Loans and
Related Allowance for Credit Losses) to Financial Statements in
this Report.
We consider multiple economic scenarios to develop our
estimate of the ACL for loans, which generally include a base
scenario, along with an optimistic (upside) and one or more
pessimistic (downside) scenarios. We weighted the base scenario
and the downside scenarios in our estimate of the ACL for loans
at December 31, 2022. The base scenario assumed elevated
inflation and economic contraction in the near term, reflecting
increased unemployment rates from historically low levels. The
downside scenarios assumed a more substantial economic
contraction due to high inflation, declining property values, and
lower business and consumer confidence.
Additionally, we consider qualitative factors that represent
the risk of limitations inherent in our processes and assumptions
such as economic environmental factors, modeling assumptions
and performance, and other subjective factors, including industry
trends and emerging risk assessments.
The forecasted key economic variables used in our estimate
of the ACL for loans at December 31 and September 30, 2022,
are presented in Table 31.
Table 31: Forecasted Key Economic Variables
2Q
2023
4Q
2023
2Q
2024
Weighted blend of economic scenarios:
U.S. unemployment rate (1):
December 31, 2022 4.3 % 5.5 6.2
September 30, 2022 5.4 6.1 6.4
U.S. real GDP (2):
December 31, 2022 (2.5) (1.0) 1.1
September 30, 2022 (1.1) 1.0 1.9
Home price index (3):
December 31, 2022 (4.7) (7.0) (6.2)
September 30, 2022
(2.2) (3.7) (3.7)
Commercial real estate asset prices (3):
December 31, 2022 (3.8) (6.7) (5.8)
September 30, 2022 (1.7) (4.7) (4.2)
(1) Quarterly average.
(2) Percent change fr om the p receding period, seasonally adjusted annualized rate.
(3) Percent change y ear over year of na tional a verage; outlook differs b y geography and
property type.
Future amounts of the ACL for loans will be based on a
variety of factors, including loan balance changes, portfolio c redit
quality and mix changes, and changes in general economic
conditions and expectations (including for unemployment and
real GDP), among other factors.
Wells Fargo & Company 44
We believe the ACL for loans of $13.6 billion at
December 31, 2022, was appropriate to cover expected credit
losses, including unfunded credit commitments, at that date. The
entire allowance is available to absorb credit losses from the total
loan portfolio. The ACL for loans is subject to change and reflects
existing factors as of the date of determination, including
economic or market conditions and ongoing internal and external
examination processes. Due to the sensitivity of the ACL for
loans to changes in the economic and business environment,
it is possible that we will incur incremental credit losses not
anticipated as of the balance sheet date. Our process for
determining the ACL is discussed in the “Critical Accounting
Policies – Allowance for Credit Losses” section and Note 1
(Summary of Significant Accounting Policies) to Financial
Statements in this Report.
MORTGAGE BANKING ACTIVITIES We sell residential and
commercial mortgage loans to various parties, including (1)
government-sponsored entities (GSEs), Federal Home Loan
Mortgage Corporation (FHLMC) and Federal National Mortgage
Association (FNMA), who include the mortgage loans in GSE-
guaranteed mortgage securitizations, (2) SPEs that issue private
label MBS, and (3) other financial institutions that purchase
mortgage loans for investment or private label securitization. In
addition, we pool FHA-insured and VA-guaranteed residential
mortgage loans that are then used to back securities guaranteed
by the Government National Mortgage Association (GNMA). We
may be required to repurchase these mortgage loans, indemnify
the securitization trust, investor or insurer, or reimburse the
securitization trust, investor or insurer for credit losses incurred
on loans (collectively, repurchase) in the event of a breach of
contractual representations or warranties that is not remedied
within a period (usually 90 days or less) after we receive notice of
the breach.
In connection with our sales and securitization of residential
mortgage loans, we have established a mortgage repurchase
liability, initially at fair value, related to various representations
and warranties that reflect management’s estimate of losses for
loans for which we could have a repurchase obligation, whether or
not we currently service those loans, based on a combination of
factors. See Note 16 (Securitizations and Variable Interest
Entities) to Financial Statements in this Report for additional
information about our liability for mortgage loan repurchase
losses.
We provide recourse to GSEs for commercial mortgage
loans sold under various programs and arrangements. The terms
of these programs require that we incur a pro-rata share of actual
losses in the event of borrower default. See Note 17 (Guarantees
and Other Commitments) to Financial Statements in this Report
for additional information about our exposure to loss related to
these programs.
In addition to servicing loans in our portfolio, we act as
servicer and/or master servicer of residential and commercial
mortgage loans included in GSE-guaranteed mortgage
securitizations, GNMA-guaranteed mortgage securitizations of
FHA-insured/VA-guaranteed mortgages and private label
mortgage securitizations, as well as for unsecuritized loans
owned by institutional investors.
The loans we service were originated by us or by other
mortgage loan originators. As servicer, our primary duties are
typically to (1) collect payments due from borrowers, (2) advance
certain delinquent payments of principal and interest on the
mortgage loans, (3) maintain and administer any hazard, title or
primary mortgage insurance policies relating to the mortgage
loans, (4) maintain any required escrow accounts for payment of
taxes and insurance and administer escrow payments, and (5)
foreclose on defaulted mortgage loans or, to the extent
consistent with the related servicing agreement, consider
alternatives to foreclosure, such as loan modifications or short
sales, and for certain investors, manage the foreclosed property
through liquidation. As master servicer, our primary duties are
typically to (1) supervise, monitor and oversee the servicing of
the mortgage loans by the servicer, and (2) advance delinquent
amounts required by non-affiliated servicers who fail to perform
their advancing obligations. The amount and timing of
reimbursement for advances of delinquent payments vary by
investor and the applicable servicing agreements. See Note 6
(Mortgage Banking Activities) to Financial Statements in this
Report for additional information about residential and
commercial servicing rights, servicer advances and servicing fees.
In accordance with applicable servicing guidelines, upon
transfer as servicer, we retain the option to repurchase loans
from GNMA loan securitization pools, which generally becomes
exercisable when three scheduled loan payments remain unpaid
by the borrower. We generally repurchase these loans for cash
and as a result, our total consolidated assets do not change. At
December 31, 2022 and 2021, these repurchased loan balances
were $9.8 billion and $17.3 billion, respectively, which included
$8.6 billion and $12.9 billion, respectively, in loans held for
investment, with the remainder in loans held for sale.
Repurchased loans that regain current status or are
otherwise modified in accordance with applicable servicing
guidelines may be included in future GNMA loan securitization
pools. However, in accordance with guidance issued by GNMA,
certain loans repurchased after June 30, 2020, are ineligible for
inclusion in future GNMA loan securitization pools until the
borrower has timely made six consecutive payments. This
requirement may delay our ability to transfer loans into the
securitization market. See Note 16 (Securitizations and Variable
Interest Entities) to Financial Statements in this Report for
additional information about our involvement with mortgage
loan securitizations.
Each agreement under which we act as servicer or master
servicer generally specifies a standard of responsibility for
actions we take in such capacity. We are required to indemnify
the securitization trustee against any failure by us, as servicer or
master servicer, to perform our servicing obligations. In addition,
if we commit a breach of our obligations as servicer or master
servicer, we may be subject to termination if the breach is not
cured within a specified period. The standards governing
servicing in GSE-guaranteed securitizations, and the possible
remedies for violations of such standards, vary, and those
standards and remedies are determined by servicing guides
maintained by the GSEs, contracts between the GSEs and
individual servicers and topical guides published by the GSEs
from time to time. Such remedies could include indemnification
or repurchase of an affected mortgage loan. In addition, in
connection with our servicing activities, we could become subject
to consent orders and settlement agreements with federal and
state regulators for alleged servicing issues and practices. In
general, these can require us to provide customers with loan
modification relief, refinancing relief, and foreclosure prevention
and assistance, and can result in business restrictions or the
imposition of certain monetary penalties on us. For example, on
September 9, 2021, the Company entered into a consent order
with the OCC requiring the Company to improve the execution,
risk management, and oversight of loss mitigation activities in its
Home Lending business. For additional information on certain
consent orders applicable to the Company, see the “Overview”
section in this Report.
Wells Fargo & Company 45
Asset/Liability Management
Asset/liability management involves evaluating, monitoring and
managing interest rate risk, market risk, liquidity and funding.
Primary oversight of interest rate risk and market risk resides
with the Finance Committee of the Board, which oversees the
administration and effectiveness of financial risk management
policies and processes used to assess and manage these risks.
Primary oversight of liquidity and funding resides with the Risk
Committee of the Board.
At the management level, the Corporate Asset/Liability
Committee (Corporate ALCO), which consists of management
from finance, risk and business groups, oversees these risks and
supports periodic reports provided to the Board’s Finance
Committee and Risk Committee as appropriate. As discussed in
more detail for market risk activities below, we employ separate
management level oversight specific to market risk.
INTEREST RATE RISK Interest rate risk is the risk that market
fluctuations in interest rates, credit spreads, or foreign exchange
can cause a loss of the Company’s earnings and capital stemming
from mismatches in the Company’s asset and liability cash flows
primarily arising from customer-related activities such as lending
and deposit-taking. We are subject to interest rate risk because:
•
assets and liabilities may mature or reprice at different
times. If assets reprice faster than liabilities and interest
rates are generally rising, earnings will initially increase;
• assets and liabilities may reprice at the same time but by
different amounts;
• short-term and long-term market interest rates may change
by different amounts. For example, the shape of the yield
curve may affect yield for new loans and funding costs
differently;
• the remaining maturity for various assets or liabilities may
shorten or lengthen as interest rates change. For example, if
long-term mortgage interest rates increase sharply,
mortgage-related products may pay down at a slower rate
than anticipated, which could impact portfolio income; or
• interest rates may have a direct or indirect effect on loan
demand, collateral values, credit losses, mortgage
origination volume, and the fair value of MSRs and other
financial instruments.
We assess interest rate risk by comparing outcomes under
various net interest income simulations using many interest rate
scenarios that differ in the direction of interest rate changes, the
degree of change over time, the speed of change and the
projected shape of the yield curve. These simulations require
assumptions regarding drivers of earnings and balance sheet
composition such as loan originations, prepayment rates on loans
and debt securities, deposit flows and mix, as well as pricing
strategies.
Our most recent simulations, as presented in Table 32,
estimate net interest income sensitivity over the next 12 months
using instantaneous movements across the yield curve with both
lower and higher interest rates relative to our base scenario.
Steeper and flatter scenarios measure non-parallel changes in
the yield curve, with long-term interest rates defined as all tenors
three years and longer and short-term interest rates defined as
all tenors less than three years. Where applicable, U.S. dollar
interest rates are floored at 0.00%. The following describes the
simulation assumptions for the scenarios presented in Table 32:
•
Simulations are dynamic and reflect anticipated changes to
our assets and liabilities.
• Other macroeconomic variables that could be correlated
with the changes in interest rates are held constant.
•
Mortgage prepayment and origination assumptions vary
across scenarios and reflect only the impact of the higher or
lower interest rates.
• Our base scenario deposit forecast incorporates mix changes
consistent with the base interest rate trajectory. Deposit
mix is modeled to be the same in the base scenario and the
alternative scenarios. In higher interest rate scenarios,
customer deposit activity that shifts balances into higher
yielding products could impact expected net interest
income.
• The interest rate sensitivity of deposits is modeled using the
historical behavior of our deposits portfolio and reflects the
expectations of deposit products repricing as market
interest rates change (referred to as deposit betas). Our
actual experience in base and alternative scenarios may
differ from expectations due to the lag or acceleration of
deposit repricing, changes in consumer behavior, and other
factors.
• We hold the size of the projected debt and equity securities
portfolios constant across scenarios.
Table 32: Net Interest Inco me S ensitivity Over the Next 12 Mo nths
Using Insta ntaneous Mo vements
($ in billions) Dec 31, 2022 Dec 31, 2021
Parallel shift:
+100 bps shift in interest rates $ 2.3 7.1
-100 bps shift in interest rates (1.7) (3.3)
Steeper yield curve: (1)
+100 bps shift in long-term interest rates 0.8 n/a
-100 bps shift in short-term interest rates (1.0) n/a
+50 bps shift in long-term interest rates 0.4 1.2
-50 bps shift in short-term interest rates (0.5) (0.9)
(1) Flatter yield curve:
+100 bps shift in short-term interest rates 1.5 n/a
-100 bps shift in long-term interest rates (0.7) n/a
+50 bps shift in short-term interest rates 0.7 2.6
-50 bps shift in long-term interest rates (0.4) (1.0)
(1) In fourth quarter 2022, given the higher levels of interest rates and volatility, we presented
100 bps shifts in our steeper and flatter scenarios.
The changes in our interest rate sensitivity from
December 31, 2021, to December 31, 2022, in Table 32 reflected
updates to our base scenario, including expectations for balance
sheet composition and interest rates. Our interest rate
sensitivity indicates that we would expect to benefit from higher
interest rates as our assets would reprice faster and to a greater
degree than our liabilities, while in the case of lower interest
rates, our assets would reprice downward and to a greater degree
than our liabilities resulting in lower net interest income. For the
December 31, 2021, simulations with downward shifts in interest
rates, the 0.00% interest rate floor limited the amount of the
decline in net interest income.
The sensitivity results above do not capture noninterest
income or expense impacts. Our interest rate sensitive
noninterest income and expense are impacted by mortgage
banking activities that may have sensitivity impacts that move in
the opposite direction of our net interest income. See the “Risk
Management – Asset/Liability Management – Mortgage Banking
Interest Rate and Market Risk” section in this Report for
additional information.
Interest rate sensitive noninterest income is also impacted
by changes in earnings credit for noninterest-bearing deposits
that reduce treasury management deposit-related service fees
Wells Fargo & Company 46
on commercial accounts, and by trading assets. In addition, the
impact to net interest income does not include the fair value
changes of trading securities, which, along with the effects of
related economic hedges, are recorded in noninterest income. In
addition to changes in interest rates, net interest income and
noninterest income from trading securities may be impacted by
the actual composition of the trading portfolio. For additional
information on our trading assets and liabilities, see Note 2
(Trading Activities) to Financial Statements in this Report.
We use the debt securities portfolio and exchange-traded
and over-the-counter (OTC) interest rate derivatives to manage
our interest rate exposures. As interest rates increase, changes in
the fair value of AFS debt securities may negatively affect
accumulated other comprehensive income (AOCI), which lowers
the amount of our regulatory capital. AOCI also includes
unrealized gains or losses related to the transfer of debt
securities from AFS to HTM, which are subsequently amortized
into earnings over the life of the security with no further impact
from interest rate changes. See Note 1 (Summary of Significant
Accounting Policies) and Note 3 (Available-for-Sale and Held-to-
Maturity Debt Securities) to Financial Statements in this Report
for additional information on the debt securities portfolios. We
use derivatives for asset/liability management in two main ways:
•
to convert the cash flows from selected asset and/or liability
instruments/portfolios including investments, commercial
loans and long-term debt, from floating-rate payments to
fixed-rate payments, or vice versa; and
• to economically hedge our mortgage origination pipeline,
funded mortgage loans, and MSRs.
In 2022, we entered into interest rate swap hedges to
reduce AOCI sensitivity of our AFS debt securities portfolio.
Additionally, we entered into interest rate swaps to convert the
interest cash flows of some floating-rate assets, such as
commercial loans and certain interest-earning deposits with
banks, to fixed-rates. Derivatives used to hedge our interest rate
risk exposures are presented in Note 14 (Derivatives) to Financial
Statements in this Report.
MORTGAGE BANKING INTEREST RATE AND MARKET RISK We
originate, fund and service mortgage loans, which subjects us to
various risks, including market, interest rate, credit, and liquidity
risks that can be substantial. Based on market conditions and
other factors, we reduce credit and liquidity risks by selling or
securitizing mortgage loans. We determine whether mortgage
loans will be held for investment or held for sale at the time of
commitment, but may change our intent to hold loans for
investment or sale as part of our corporate asset/liability
management activities. We may also retain securities in our
investment portfolio at the time we securitize mortgage loans.
Changes in interest rates may impact mortgage banking
noninterest income, including origination and servicing fees, and
the fair value of our residential MSRs, LHFS, and derivative loan
commitments (interest rate “locks”) extended to mortgage
applicants. Interest rate changes will generally impact our
mortgage banking noninterest income on a lagging basis due to
the time it takes for the market to reflect a shift in customer
demand, as well as the time required for processing a new
application, providing the commitment, and securitizing and
selling the loan. The amount and timing of the impact will depend
on the magnitude, speed and duration of the changes in interest
rates.
The valuation of our residential MSRs can be highly
subjective and involve complex judgments by management
about matters that are inherently unpredictable. Changes in
interest rates influence a variety of significant assumptions
captured in the periodic valuation of residential MSRs, including
prepayment rates, expected returns and potential risks on the
servicing asset portfolio, costs to service, the value of escrow
balances and other servicing valuation elements. See the “Critical
Accounting Policies – Valuation of Residential Mortgage
Servicing Rights” section in this Report for additional
information on the valuation of our residential MSRs.
An increase in interest rates generally reduces the
propensity for refinancing, extends the expected duration of the
servicing portfolio, and therefore increases the estimated fair
value of the MSRs. However, an increase in interest rates can also
reduce mortgage loan demand, including refinancing activity,
which reduces noninterest income from origination activities. A
decline in interest rates would generally have an opposite impact.
To reduce our exposure to changes in interest rates, our
residential MSRs are economically hedged with a combination of
derivative instruments, including interest rate swaps, Eurodollar
futures, highly liquid mortgage forward contracts and interest
rate options. Hedging the various sources of interest rate risk in
mortgage banking is a complex process that requires
sophisticated modeling and constant monitoring. There are
several potential risks to earnings from mortgage banking
related to origination volumes and mix, valuation of MSRs and
associated hedging results, the relationship and degree of
volatility between short-term and long-term interest rates, and
changes in servicing and foreclosures costs. While we attempt to
balance our mortgage banking interest rate and market risks, the
financial instruments we use may not perfectly correlate with the
values and income being hedged.
The size of the hedge and the particular combination of
hedging instruments at any point in time is designed to reduce
the volatility of our earnings over various time frames within a
range of mortgage interest rates. Market factors, the
composition of the mortgage servicing portfolio, and the
relationship between the origination and servicing sides of our
mortgage businesses change continually, and therefore the types
of instruments used in our hedging are reviewed daily and
rebalanced based on our evaluation of current market factors and
the interest rate risk inherent in our portfolio.
For additional information on mortgage banking, including
key assumptions and the sensitivity of the fair value of MSRs, see
Note 6 (Mortgage Banking Activities), Note 14 (Derivatives), and
Note 15 (Fair Values of Assets and Liabilities) to Financial
Statements in this Report.
MARKET RISK Market risk is the risk of possible economic loss
from adverse changes in market risk factors such as interest
rates, credit spreads, foreign exchange rates, equity and
commodity prices, and the risk of possible loss due to
counterparty exposure. This applies to implied volatility risk,
basis risk, and market liquidity risk. It includes price risk in the
trading book, mortgage servicing rights and the hedge
effectiveness risk associated with mortgage loans held at fair
value, and impairment of private equity investments.
The Board’s Finance Committee has primary oversight
responsibility for market risk and oversees the Company’s
market risk exposure and market risk management strategies.
In addition, the Board’s Risk Committee has certain oversight
responsibilities with respect to market risk, including
counterparty risk. The Finance Committee reports key market
risk matters to the Risk Committee.
At the management level, the Market and Counterparty Risk
Management function, which is part of IRM, has oversight
responsibility for market risk across the enterprise. The Market
Wells Fargo & Company 47
Risk Management – Asset/Liability Management (continued)
and Counterparty Risk Management function reports into
Corporate and Investment Banking Risk and provides periodic
reports related to market risk to the Board’s Finance Committee.
MARKET RISK – TRADING ACTIVITIES We engage in trading
activities to accommodate the investment and risk management
activities of our customers and to execute economic hedging to
manage certain balance sheet risks. These trading activities
predominantly occur within our CIB businesses and, to a lesser
extent, other businesses of the Company. Debt securities held
for trading, equity securities held for trading, trading loans and
trading derivatives are financial instruments used in our trading
activities, and all are carried at fair value. Income earned on the
financial instruments used in our trading activities include net
interest income, changes in fair value and realized gains and
losses. Net interest income earned from our trading activities is
reflected in the interest income and interest expense
components of our consolidated statement of income. Changes
in fair value of the financial instruments used in our trading
activities are reflected in net gains from trading activities. For
additional information on the financial instruments used in our
trading activities and the income from these trading activities,
see Note 2 (Trading Activities) to Financial Statements in this
Report.
Value-at-risk (VaR) is a statistical risk measure used to
estimate the potential loss from adverse moves in the financial
markets. The Company uses VaR metrics complemented with
sensitivity analysis and stress testing in measuring and
monitoring market risk. These market risk measures are
monitored at both the business unit level and at aggregated
levels on a daily basis. Our corporate market risk management
function aggregates and monitors exposures against our
established risk appetite. Changes to the market risk profile are
analyzed and reported on a daily basis. The Company monitors
various market risk exposure measures from a variety of
perspectives, including line of business, product, risk type, and
legal entity.
Trading VaR is the measure used to provide insight into the
market risk exhibited by the Company’s trading positions. The
Company calculates Trading VaR for risk management purposes
to establish line of business and Company-wide risk limits.
Trading VaR is calculated based on all trading positions on our
consolidated balance sheet.
Table 33 shows the Company’s Trading General VaR by risk
category. Our Trading General VaR uses a historical simulation
model which assumes that historical changes in market values
are representative of the potential future outcomes and
measures the expected earnings loss of the Company over a
1-day time interval at a 99% confidence level. Our historical
simulation model is based on equally weighted data from a
12-month historical look-back period. We believe using a
12-month look-back period helps ensure the Company’s VaR is
responsive to current market conditions. The 99% confidence
level equates to an expectation that the Company would incur
single-day trading losses in excess of the VaR estimate on
average once every 100 trading days.
Average Company Trading General VaR was $35 million for
the year ended December 31, 2022, compared with $49 million
for the year ended December 31, 2021. The decrease in average
Company Trading General VaR for the year ended December 31,
2022, compared with the year ended December 31, 2021, was
primarily driven by changes in portfolio composition.
Table 33: Trading 1-Day 99% General VaR by Risk Category
Year ended December 31,
2022 2021
(in millions)
Period
end Average Low High
Period
end Average Low High
Company Trading General VaR Risk Categories
Credit $ 29 32 19 85 19 38 12 112
Interest rate 25 25 9 88 15 25 4 120
Equity 27 23 13 38 15 30 13 72
Commodity 4 6 2 20 10 7 2 28
Foreign exchange 1 1 0 2 1 1 0 1
Diversification benefit (1) (47) (52) (40) (52)
Company Trading General VaR $ 39 35 20 49
(1) The p eriod-end VaR wa s less t han t he su m of t he Va R com ponents d escribed above, which is d ue t o p ortfolio d iversification. The d iversification effect arises b ecause t he r isks a re not perfectly
correlated causing a portfolio of p ositions t o u sually be less r isky than t he su m of t he r isks of t he p ositions a lone. The d iversification b enefit is not meaningful for low a nd high metrics since t hey may
occur on d ifferent days.
Sensitivity Analysis Given the inherent limitations of the VaR
models, the Company uses other measures, including sensitivity
analysis, to measure and monitor risk. Sensitivity analysis is the
measure of exposure to a single risk factor, such as a 0.01%
increase in interest rates or a 1% increase in equity prices. We
conduct and monitor sensitivity on interest rates, credit spreads,
volatility, equity, commodity, and foreign exchange exposure.
Sensitivity analysis complements VaR as it provides an indication
of risk relative to each factor irrespective of historical market
moves.
Stress Testing While VaR captures the risk of loss due to
adverse changes in markets using recent historical market data,
stress testing is designed to capture the Company’s exposure to
extreme but low probability market movements. Stress scenarios
estimate the risk of losses based on management’s assumptions
of abnormal but severe market movements such as severe credit
spread widening or a large decline in equity prices. These
scenarios assume that the market moves happen
instantaneously and no repositioning or hedging activity takes
place to mitigate losses as events unfold (a conservative
approach since experience demonstrates otherwise).
An inventory of scenarios is maintained representing both
historical and hypothetical stress events that affect a broad
range of market risk factors with varying degrees of correlation
and differing time horizons. Hypothetical scenarios assess the
impact of large movements in financial variables on portfolio
values. Typical examples include a 1% (100 basis point) increase
across the yield curve or a 10% decline in equity market indexes.
Historical scenarios utilize an event-driven approach: the stress
Wells Fargo & Company 48
scenarios are based on plausible but rare events, and the analysis
addresses how these events might affect the risk factors
relevant to a portfolio.
The Company’s stress testing framework is also used in
calculating results in support of the Federal Reserve Board’s
Comprehensive Capital Analysis and Review (CCAR) and internal
stress tests. Stress scenarios are regularly reviewed and updated
to address potential market events or concerns. For more detail
on the CCAR process, see the “Capital Management” section in
this Report.
MARKET RISK – EQUITY SECURITIES We are directly and indirectly
affected by changes in the equity markets. We make and manage
direct investments in start-up businesses, emerging growth
companies, management buy-outs, acquisitions and corporate
recapitalizations. We also invest in non-affiliated funds that
make similar private equity investments. These private equity
investments are made within capital allocations approved by
management and the Board. The Board reviews business
developments, key risks and historical returns for the private
equity investment portfolio at least annually. Management
reviews these investments at least quarterly to assess them for
impairment and observable price changes. For nonmarketable
equity securities, the analysis is based on facts and circumstances
of each individual investment and the expectations for that
investment’s cash flows, capital needs, the viability of its business
model, our exit strategy, and observable price changes that are
similar to the investments held. Investments in nonmarketable
equity securities include private equity investments accounted
for under the equity method, fair value through net income, and
the measurement alternative.
As part of our business to support our customers, we trade
public equities, listed/OTC equity derivatives and convertible
bonds. We have parameters that govern these activities. We also
have marketable equity securities that include investments
relating to our venture capital activities. We manage these
marketable equity securities within capital risk limits approved by
management and the Board and monitored by Corporate ALCO
and the Market Risk Committee. The fair value changes in these
marketable equity securities are recognized in net income. For
additional information, see Note 4 (Equity Securities) to Financial
Statements in this Report.
Changes in equity market prices may also indirectly affect
our net income by (1) the value of third-party assets under
management and, hence, fee income, (2) borrowers whose ability
to repay principal and/or interest may be affected by the stock
market, or (3) brokerage activity, related commission income and
other business activities. Each business line monitors and
manages these indirect risks.
LIQUIDITY RISK AND FUNDING Liquidity risk is the risk arising from
the inability of the Company to meet obligations when they
come due, or roll over funds at a reasonable cost, without
incurring heightened costs. In the ordinary course of business, we
enter into contractual obligations that may require future cash
payments, including funding for customer loan requests,
customer deposit maturities and withdrawals, debt service,
leases for premises and equipment, and other cash
commitments. The objective of effective liquidity management is
to ensure that we can meet our contractual obligations and other
cash commitments efficiently under both normal operating
conditions and under periods of Wells Fargo-specific and/or
market stress. For additional information on these obligations,
see the following sections and Notes to Financial Statements in
this Report:
• “Unfunded Credit Commitments” section within Loans and
Related Allowance for Credit Losses (Note 5)
• Leasing Activity (Note 8)
• Deposits (Note 9)
• Long-Term Debt (Note 10)
• Guarantees and Other Commitments (Note 17)
• Employee Benefits (Note 21)
• Income Taxes (Note 22)
To help achieve this objective, the Board establishes liquidit y
guidelines that require sufficient asset-based liquidity to cov er
potential funding requirements and to avoid over-dependence
on volatile, less reliable funding markets. These guidelines ar e
monitored on a monthly basis by the Corporate ALCO and on a
quarterly basis by the Board. These guidelines are established and
monitored for both the Company and the Parent on a stand -
alone basis so that the Parent is a source of strength for its
banking subsidiaries.
Liquidity Stress Tests Liquidity stress tests are performed to
help ensure that the Company has sufficient liquidity to meet
contractual and contingent outflows modeled under a variety of
stress scenarios. Our scenarios utilize market-wide as well as
corporate-specific events, including a range of stress conditions
and time horizons. Stress testing results facilitate evaluation of
the Company’s projected liquidity position during stress and
inform future needs in the Company’s funding plan.
Contingency Funding Plan Our contingency funding plan (CFP),
which is approved by Corporate ALCO and the Board’s Risk
Committee, sets out the Company’s strategies and action plans
to address potential liquidity needs during market-wide or
idiosyncratic liquidity events. The CFP establishes measures for
monitoring emerging liquidity events and describes the
processes for communicating and managing stress events should
they occur. The CFP also identifies alternate funding and liquidity
strategies available to the Company in a period of stress.
Liquidity Standards We are subject to a rule issued by the FRB,
OCC and FDIC that establishes a quantitative minimum liquidity
requirement consistent with the liquidity coverage ratio (LCR)
established by the Basel Committee on Banking Supervision
(BCBS). The rule requires a covered banking organization to hold
high-quality liquid assets (HQLA) in an amount equal to or
greater than its projected net cash outflows during a 30-day
stress period. Our HQLA under the rule predominantly consists
of central bank deposits, government debt securities, and
mortgage-backed securities of federal agencies. The LCR applies
to the Company and to our insured depository institutions (IDIs)
with total assets of $10 billion or more. In addition, rules issued
by the FRB impose enhanced liquidity risk management
standards on large bank holding companies (BHCs), such as
Wells Fargo.
The FRB, OCC and FDIC have also issued a rule implementing
a stable funding requirement, known as the net stable funding
ratio (NSFR), which requires a covered banking organization, such
as Wells Fargo, to maintain a minimum amount of stable funding,
including common equity, long-term debt and most types of
deposits, in relation to its assets, derivative exposures and
commitments over a one-year horizon period. The NSFR applies
to the Company and to our IDIs with total assets of $10 billion or
more. As of December 31, 2022, we were compliant with the
NSFR requirement.
Wells Fargo & Company 49
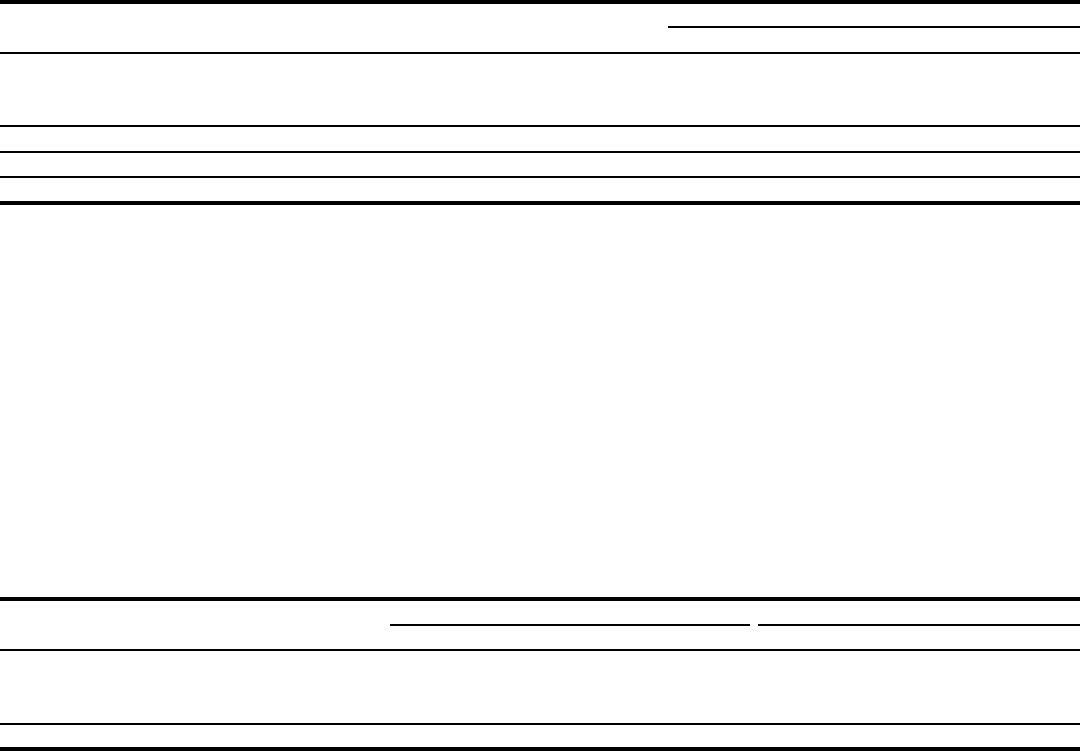
Risk Management – Asset/Liability Management (continued)
Liquidity Coverage Ratio As of December 31, 2022 , the
Company, Wells Fargo Bank, N.A., and Wells Fargo National Bank
West exceeded the minimum LCR requirement of 100%.
Table 34 presents the Company’s quarterly average values for
the daily-calculated LCR and its components calculated pursuan t
to the LCR rule requirements. The LCR represents average HQLA
divided by average projected net cash outflows, as each is
defined under the LCR rule.
Table 34: Liquidity Coverage Ratio
Average for quarter ended
(in millions, except ratio) Dec 31, 2022 Sep 30, 2022 Dec 31, 2021
HQLA (1):
Eligible cash $ 123,446 125,576 210,527
(2)Eligible securities 231,337 238,678 172,761
Total HQLA 354,783 364,254 383,288
Projected net cash outflows (3) 292,001 296,495 325,015
LCR 122% 123 118
(1) Excludes excess HQLA at certain subsidiaries that are not transferable to other Wells Fargo entities.
(2) Net of applicable haircuts required under the LCR rule.
(3) Projected net cash outflows are calculated by applying a standardized set of outflow and inflow assumptions, defined by the LCR rule, to various exposures and liability types, such as deposits and
unfunded loan commitments, which are prescribed based on a number of factors including the type of customer and the nature of the account.
Liquidity Sources We maintain liquidity in the form of cash,
interest-earning deposits with banks, and unencumbered high-
quality, liquid debt securities. These assets make up our primary
sources of liquidity. Our primary sources of liquidity are
substantially the same in composition as HQLA under the LCR
rule; however, our primary sources of liquidity will generally
exceed HQLA calculated under the LCR rule due to the applicable
haircuts to HQLA and the exclusion of excess HQLA at our
subsidiary IDIs required under the LCR rule. Our primary sources
of liquidity are presented in Table 35 at fair value, which also
includes encumbered securities that are not included as available
HQLA in the calculation of the LCR.
Our cash is predominantly on deposit with the Federal
Reserve. Debt securities included as part of our primary source s
of liquidity are comprised of U.S. Treasury and federal agency
debt, and MBS issued by federal agencies within our debt
securities portfolio. We believe these debt securities provide
quick sources of liquidity through sales or by pledging to obta in
financing, regardless of market conditions. Some of these debt
securities are within our HTM portfolio and, as such, are not
intended for sale but may be pledged to obtain financing.
Table 35: Primary Sources of Liquidity
December 31, 2022 December 31, 2021
(in millions)
Total
Encumbered
Unencumbered
Total
Encumbered
Unencumbered
Interest-earning deposits with banks
$
124,561
—
124,561
209,614
—
209,614
Debt securities of U.S. Treasury and federal agencies
59,570
12,080
47,490
56,486
4,066
52,420
Federal agency mortgage-backed securities
230,881
34,151
196,730
293,870
58,955
234,915
Total $
415,012
46,231
368,781
559,970
63,021
496,949
In addition to our primary sources of liquidity shown in
Table 35, liquidity is also available through the sale or financing of
other debt securities including trading and/or AFS debt securities
as well as through the sale, securitization or financing of loans, to
the extent such debt securities and loans are not encumbered.
Funding Sources The Parent acts as a source of funding for the
Company through the issuance of long-term debt and equity.
WFC Holdings, LLC (the “IHC”) is an intermediate holding
company and subsidiary of the Parent, which provides funding
support for the ongoing operational requirements of the Parent
and certain of its direct and indirect subsidiaries. For additional
information on the IHC, see the “Regulatory Matters – ‘Living
Will’ Requirements and Related Matters” section in this Report.
Additional subsidiary funding is provided by deposits, short-term
borrowings and long-term debt.
Deposits have historically provided a sizable source of
relatively low-cost funds. Deposits were 145% and 166% of total
loans at December 31, 2022 and 2021, respectively.
As of December 31, 2022, we had approximately
$209.0 billion of available borrowing capacity at various Federal
Home Loan Banks and the Federal Reserve Discount Window.
Although available, we do not view the borrowing capacity at the
Federal Reserve Discount Window as a primary source of
liquidity. Table 36 presents a summary of our short-term
borrowings, which generally mature in less than 30 days. For
additional information on the classification of our short-term
borrowings, see Note 1 (Summary of Significant Accounting
Policies) to Financial Statements in this Report. We pledge
certain financial instruments that we own to collateralize
repurchase agreements and other securities financings. For
additional information, see the “Pledged Assets” section of Note
18 (Pledged Assets and Collateral) to Financial Statements in this
Report.
Wells Fargo & Company 50
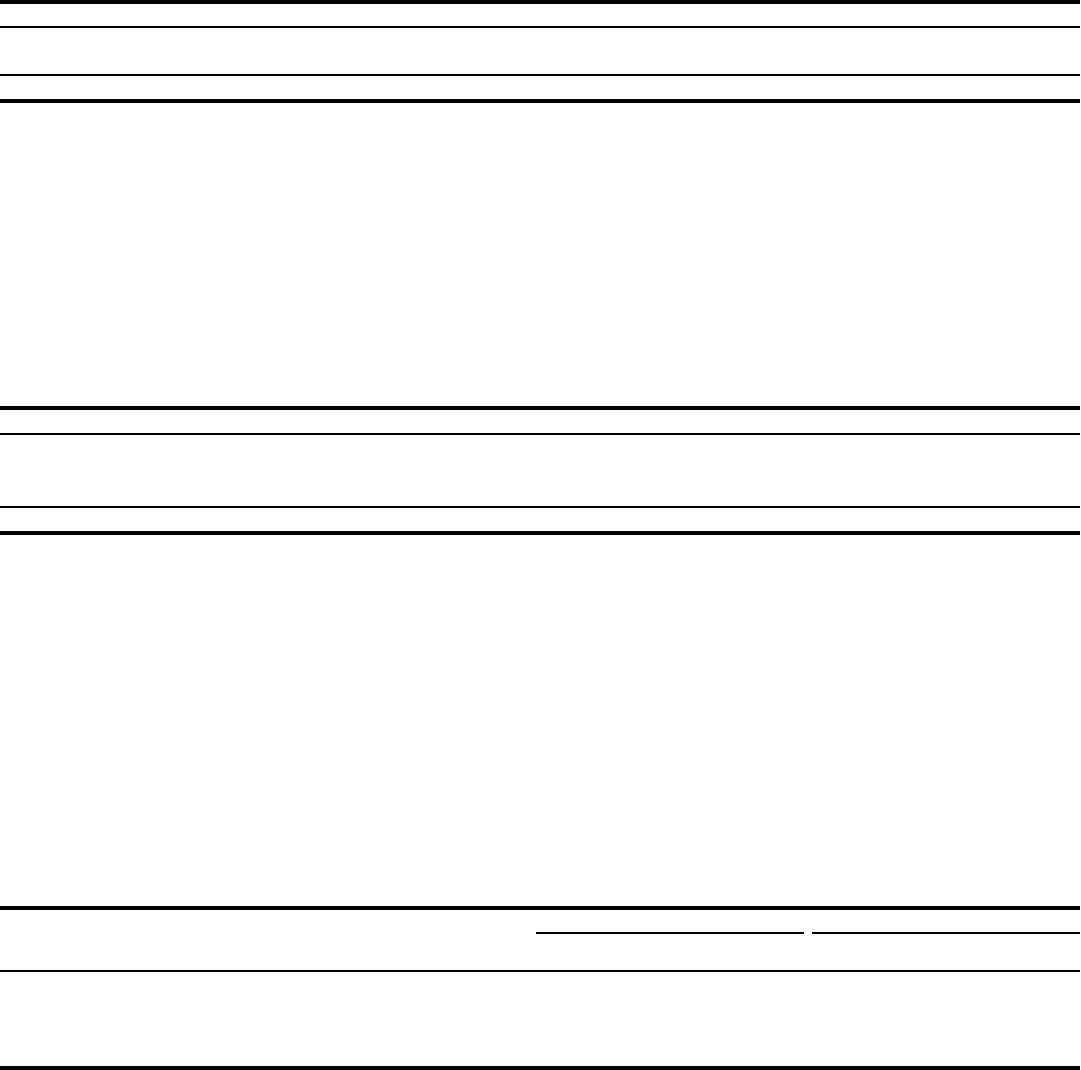
Table 36: Short-Term Bo rrowings
(in millions) December 31, 2022 December 31, 2021
Federal funds purchased and securities sold under agreements to repurchase $ 30,623 21,191
Other short-term borrowings (1) 20,522 13,218
Total $ 51,145 34,409
(1) Includes $7.0 billion and $0 of Federal Home Loan Bank (FHLB) advances at December 31, 2022 and 2021, respectively.
We access domestic and international capital markets for
long-term funding through issuances of registered debt
securities, private placements and asset-backed secured funding .
We issue long-term debt in a variety of maturities and currenci es
to achieve cost-efficient funding and to maintain an appropriat e
maturity profile. Proceeds from securities issued were used fo r
general corporate purposes unless otherwise specified in the
applicable prospectus or prospectus supplement, and we expect
the proceeds from securities issued in the future will be used for
the same purposes. Depending on market conditions and our
liquidity position, we may redeem or repurchase, and
subsequently retire, our outstanding debt securities in privately
negotiated or open market transactions, by tender offer, or
otherwise.
Table 37 presents a summary of our long-term debt. For
additional information on our long-term debt, including
contractual maturities, see Note 10 (Long-Term Debt ), and for
information on the classification of our long-term debt, see Note
1 ( Summary of Significant Accounting Policies ) to Financial
Statements in this Report .
Table 37: Long-Term Debt
(in millions) December 31, 2022 December 31, 2021
Wells Fargo & Company (Parent Only) $ 134,401 146,286
Wells Fargo Bank, N.A., and other bank entities (Bank) (1) 39,189 12,858
Other consolidated subsidiaries 1,280 1,545
Total $ 174,870 160,689
(1) Includes $27.0 billion and $0 of FHLB advances at December 31, 2022 and 2021, respectively. For additional information, see Note 10 (Long-Term Debt) to Financial Statements in this Report.
Credit Ratings Investors in the long-term capital markets, as
well as other market participants, generally will consider, among
other factors, a company’s debt rating in making investment
decisions. Rating agencies base their ratings on many
quantitative and qualitative factors, including capital adequacy,
liquidity, asset quality, business mix, the level and quality of
earnings, and rating agency assumptions regarding the
probability and extent of federal financial assistance or support
for certain large financial institutions. Adverse changes in these
factors could result in a reduction of our credit rating; however,
our debt securities do not contain credit rating covenants.
There were no actions undertaken by the rating agencies
with regard to our credit ratings during fourth quarter 2022.
See the “Risk Factors” section in this Report for additional
information regarding our credit ratings and the potential impact
a credit rating downgrade would have on our liquidity and
operations as well as Note 14 (Derivatives) to Financial
Statements in this Report for information regarding additional
collateral and funding obligations required for certain derivative
instruments in the event our credit ratings were to fall below
investment grade.
The credit ratings of the Parent and Wells Fargo Bank, N.A.,
as of December 31, 2022, are presented in Table 38.
Table 38: Credit Ratings as of December 31, 2022
Wells Fargo & Company Wells Fargo Bank, N.A.
Senior debt
Short-term
borrowings
Long-term
deposits
Short-term
borrowings
Moody’s A1 P-1 Aa1 P-1
S&P Global Ratings BBB+ A-2 A+ A-1
Fitch Ratings A+ F1 AA F1+
DBRS Morningstar AA (low) R-1 (middle) AA R-1 (high)
Wells Fargo & Company 51
Capital Management
We have an active program for managing capital through a
comprehensive process for assessing the Company’s overall
capital adequacy. Our objective is to maintain capital at an
amount commensurate with our risk profile and risk tolerance
objectives, and to meet both regulatory and market
expectations. We primarily fund our capital needs through the
retention of earnings net of both dividends and share
repurchases, as well as through the issuance of preferred stock
and long- and short-term debt. Retained earnings at
December 31, 2022, increased $7.3 billion from December 31,
2021, predominantly as a result of $13.2 billion of Wells Fargo
net income, partially offset by $5.4 billion of common and
preferred stock dividends. During 2022, we issued $1.8 billion of
common stock, substantially all of which was issued in
connection with employee compensation and benefits. In 2022,
we repurchased 110 million shares of common stock at a cost of
$6 billion. In 2022, our AOCI decreased $11.7 billion,
predominantly due to net unrealized losses on AFS debt
securities. As interest rates increase, changes in the fair value of
AFS debt securities may negatively affect AOCI, which lowers the
amount of our risk-based capital. For additional information
about capital planning, see the “Capital Planning and Stress
Testing” section below.
In 2022, we redeemed $609 million of preferred stock. For
additional information, see Note 11 (Preferred Stock) to
Financial Statements in this Report.
Regulatory Capital Requirements
The Company and each of our IDIs are subject to various
regulatory capital adequacy requirements administered by the
FRB and the OCC. Risk-based capital rules establish risk-adjusted
ratios relating regulatory capital to different categories of assets
and off-balance sheet exposures as discussed below.
RISK-BASED CAPITAL AND RISK-WEIGHTED ASSETS The Company
is subject to rules issued by federal banking regulators to
implement Basel III capital requirements for U.S. banking
organizations. The rules contain two frameworks for calculating
capital requirements, a Standardized Approach and an Advanced
Approach applicable to certain institutions, including Wells Fargo,
and we must calculate our risk-based capital ratios under both
approaches. The Company is required to satisfy the risk-based
capital ratio requirements to avoid restrictions on capital
distributions and discretionary bonus payments. Table 39 and
Table 40 present the risk-based capital requirements applicable
to the Company under the Standardized Approach and Advanced
Approach, respectively, as of December 31, 2022.
Table 39: Risk-Based Capital Requirements – Standardized Approach
as of December 31, 2022
Standardized Approach
9.20%
10.70%
12.70%
4.50%
6.00%
8.00%
3.20%
3.20%
3.20%
1.50%
1.50%
1.50%
Minimum requirement Stress capital buffer
G-SIB capital surcharge
Common Equity Tier 1
(CET1) ratio
Tier 1 capital ratio
Total capital ratio
Table 40: Risk-Based Capital Requirements – Advanced Approach as of
December 31, 2022
Advanced Approach
8.50%
10.00%
12.00%
4.50%
6.00%
8.00%
2.50%
2.50%
2.50%
1.50%
1.50%
1.50%
Minimum requirement Capital conservation buffer
G-SIB capital surcharge
Common Equity Tier 1
(CET1) ratio
Tier 1 capital ratio
Total capital ratio
In addition to the risk-based capital requirements described
in Table 39 and Table 40, if the FRB determines that a period of
excessive credit growth is contributing to an increase in systemic
risk, a countercyclical buffer of up to 2.50% could be added to the
risk-based capital ratio requirements under federal banking
regulations. The countercyclical buffer in effect at December 31,
2022, was 0.00%.
The capital conservation buffer is applicable to certain
institutions, including Wells Fargo, under the Advanced Approach
and is intended to absorb losses during times of economic or
financial stress.
Wells Fargo & Company 52
The stress capital buffer is calculated based on the decrease
in a BHC’s risk-based capital ratios under the severely adverse
scenario in the FRB’s annual supervisory stress test and related
Comprehensive Capital Analysis and Review (CCAR), plus four
quarters of planned common stock dividends. Because the stress
capital buffer is calculated annually based on data that can differ
over time, our stress capital buffer, and thus our risk-based
capital ratio requirements under the Standardized Approach, are
subject to change in future periods. Our stress capital buffer for
the period October 1, 2022, through September 30, 2023, is
3.20%.
As a global systemically important bank (G-SIB), we are also
subject to the FRB’s rule implementing an additional capital
surcharge between 1.00-4.50% on the risk-based capital ratio
requirements of G-SIBs. Under the rule, we must annually
calculate our surcharge under two methods and use the higher
of the two surcharges. The first method (method one) considers
our size, interconnectedness, cross-jurisdictional activity,
substitutability, and complexity, consistent with the
methodology developed by the BCBS and the Financial Stability
Board (FSB). The second method (method two) uses similar
inputs, but replaces substitutability with use of short-term
wholesale funding and will generally result in higher surcharges
than under method one. Because the G-SIB capital surcharge is
calculated annually based on data that can differ over time, the
amount of the surcharge is subject to change in future years. If
our annual calculation results in a decrease to our G-SIB capital
surcharge, the decrease takes effect the next calendar year. If our
annual calculation results in an increase to our G-SIB capital
surcharge, the increase takes effect in two calendar years. Our
G-SIB capital surcharge will continue to be 1.50% in 2023.
Under the risk-based capital rules, on-balance sheet assets
and credit equivalent amounts of derivatives and off-balance
sheet items are assigned to one of several broad risk categories
according to the obligor, or, if relevant, the guarantor or the
nature of any collateral. The aggregate dollar amount in each risk
category is then multiplied by the risk weight associated with
that category. The resulting weighted values from each of the
risk categories are aggregated for determining total risk-
weighted assets (RWAs).
The tables that follow provide information about our risk-
based capital and related ratios as calculated under Basel III
capital rules. Table 41 summarizes our CET1, Tier 1 capital, total
capital, RWAs and capital ratios.
Table 41: Capital Components and Ratios
Standardized Approach Advanced Approach
($ in millions)
Required
Capital
Ratios (1)
Dec 31,
2022
Dec 31,
2021
Required
Capital
Ratios (1)
Dec 31,
2022
Dec 31,
2021
Common Equity Tier 1 (A) $ 133,527 140,643 133,527 140,643
Tier 1 capital (B) 152,567 159,671 152,567 159,671
Total capital (C) 186,747 196,281 177,258 186,553
Risk-weighted assets (D) 1,259,889 1,239,026 1,112,307 1,116,068
Common Equity Tier 1 capital ratio (A)/(D) 9.20 % 10.60 * 11.35 8.50 12.00 12.60
Tier 1 capital ratio (B)/(D) 10.70 12.11 * 12.89 10.00 13.72 14.31
Total capital ratio (C)/(D) 12.70 14.82 * 15.84 12.00 15.94 16.72
* Denotes t he b inding ratio u nder the S tandardized and Advanced Approaches a t December 31, 2022.
(1) Represents t he m inimum ratios r equired to a void restrictions on ca pital d istributions a nd discretionary bonus p ayments a t December 31, 2022.
Wells Fargo & Company 53
Capital Management (continued)
Table 42 provides information regarding the calculation and
composition of our risk-based capital under the Standardized an d
Advanced Approaches .
Table 42: Risk-Based Capital C alculation a nd Components
(in millions)
Dec 31,
2022
Dec 31,
2021
Total equity $ 181,875 190,110
Adjustments:
Preferred stock (1) (19,448) (20,057)
Additional paid-in capital on preferred stock (1) 173 136
Unearned Employee Stock Ownership Plan (ESOP) shares (1) — 646
Noncontrolling interests (1,986) (2,504)
Total common stockholders’ equity $ 160,614 168,331
Adjustments:
Goodwill (25,173) (25,180)
Certain identifiable intangible assets (other than MSRs) (152) (225)
Goodwill and other intangibles on investments in consolidated portfolio companies (included in other assets) (2,427) (2,437)
Applicable deferred taxes related to goodwill and other intangible assets (2) 890 765
CECL transition provision (3) 180 241
Other (405) (852)
Common Equity Tier 1 under the Standardized and Advanced Approaches $ 133,527 140,643
Preferred stock (1) 19,448 20,057
Additional paid-in capital on preferred stock (1) (173) (136)
Unearned ESOP shares (1) — (646)
Other (235) (247)
Total Tier 1 capital under the Standardized and Advanced Approaches (A) $ 152,567 159,671
Long-term debt and other instruments qualifying as Tier 2 20,503 22,740
Qualifying allowance for credit losses (4) 13,959 14,149
Other (282) (279)
Total Tier 2 capital under the Standardized Approach (B) $ 34,180 36,610
Total qualifying capital under the Standardized Approach (A)+(B) $ 186,747 196,281
Long-term debt and other instruments qualifying as Tier 2 20,503 22,740
Qualifying allowance for credit losses (4) 4,470 4,421
Other (282) (279)
Total Tier 2 capital under the Advanced Approach (C) $ 24,691 26,882
Total qualifying capital under the Advanced Approach (A)+(C) $ 177,258 186,553
(1) In fou rth quarter 2022, we r edeemed all ou tstanding shares of ou r ESOP Cumulative C onvertible Pr eferred Stock in exch ange for shares of t he C ompany’s com mon st ock. For additional infor mation,
see Note 11 (Preferred Stock) t o F inancial S tatements in t his Rep ort.
(2) Determined by applying the com bined federal st atutory rate a nd composite st ate incom e t ax r ates t o t he d ifference b etween b ook and tax b asis of t he r espective g oodwill a nd intangible a ssets a t
period-end.
(3) In second quarter 2020, the C ompany elected to a pply a modified transition p rovision issu ed by federal b anking regulators r elated to t he im pact of t he cu rrent expected credit loss a ccounting
standard (CECL) on r egulatory capital. The r ule p ermits cer tain b anking organizations t o exclu de fr om regulatory capital t he init ial a doption im pact of C ECL, plus 25% of t he cu mulative ch anges in t he
allowance for credit losses (AC L) u nder CECL for each period until D ecember 31, 2021, followed by a three-year phase-out period in wh ich the b enefit is r educed by 25% in y ear one, 50% in y ear two
and 75% in y ear three.
(4) Differences b etween t he a pproaches a re d riven b y the q ualifying amounts of AC L includable in Tier 2 ca pital. Under the Ad vanced Approach, eligible cr edit reserves r epresented by the a mount of
qualifying ACL in excess of exp ected credit losses (u sing regulatory definitions) is lim ited to 0. 60% of Ad vanced credit RWAs, whereas t he S tandardized Approach includes AC L in Tier 2 ca pital u p to
1.25% of S tandardized credit RWAs. Under both approaches, any excess AC L is d educted from the r espective t otal RWAs.
Table 43 provides the composition of our RWAs under the
Standardized and Advanced Approaches.
Table 43: Risk-Weighted Assets
Standardized Approach Advanced Approach (1)
Dec 31,
2022
Dec 31,
2021
Dec 31,
2022
Dec 31,
2021 (in millions)
Risk-weighted assets (RWAs):
Credit risk 1,186,810 757,436 747,714
Market risk 41,883 52,216 41,883 52,216
Operational risk — — 312,988 316,138
Total RWAs $ 1,259,889 1,239,026 1,112,307 1,116,068
$ 1,218,006
(1) RWAs ca lculated under the Ad vanced Approach utilize a risk-sensitive m ethodology, which relies u pon t he u se of int ernal cr edit models b ased upon ou r experience wit h internal r ating grades.
Advanced Approach also inclu des a n op erational r isk component, which reflects t he r isk of loss r esulting from inadequate or failed internal p rocesses, people a nd systems, or from external ev ents.
Wells Fargo & Company 54
Table 44 provides an analysis of the changes in CET1.
Table 44: Analysis o f C hanges in C ommon Equity Tier 1
(in millions)
Common Equity Tier 1 at December 31, 2021 $ 140,643
Net income applicable to common stock 12,067
Common stock dividends (4,184)
Common stock issued, repurchased, and stock compensation-related items (3,930)
Changes in accumulated other comprehensive income (11,677)
Goodwill 7
Certain identifiable intangible assets (other than MSRs) 73
Goodwill and other intangibles on investments in consolidated portfolio companies (included in other assets) 10
Applicable deferred taxes related to goodwill and other intangible assets (1) 125
CECL transition provision (2) (61)
Other 454
Change in Common Equity Tier 1 (7,116)
Common Equity Tier 1 at December 31, 2022 $ 133,527
(1) Determined by applying the com bined federal st atutory rate a nd composite st ate incom e t ax r ates t o t he d ifference b etween b ook and tax b asis of t he r espective g oodwill a nd intangible a ssets a t
period-end.
(2) In second quarter 2020, the C ompany elected to a pply a modified transition p rovision issu ed by federal b anking regulators r elated to t he im pact of C ECL on r egulatory capital. The r ule p ermits
certain b anking organizations t o exclu de fr om regulatory capital t he init ial a doption im pact of C ECL, plus 25% of t he cu mulative ch anges in t he a llowance for credit losses (AC L) u nder CECL for each
period until D ecember 31, 2021, followed by a three-year phase-out period in wh ich the b enefit is r educed by 25% in y ear one, 50% in y ear two a nd 75% in y ear three.
Table 45 presents net changes in the components of RWAs
under the Standardized and Advanced Approaches.
Table 45: Analysis o f C hanges in RWAs
(in millions) Standardized Approach Advanced Approach
Risk-weighted assets (RWAs) at December 31, 2021 $ 1,239,026 1,116,068
Net change in credit risk RWAs 31,196 9,722
Net change in market risk RWAs (10,333) (10,333)
Net change in operational risk RWAs — (3,150)
Total change in RWAs 20,863 (3,761)
RWAs at December 31, 2022 $ 1,259,889 1,112,307
Wells Fargo & Company 55
TANGIBLE COMMON EQUITY We also evaluate our business based
on certain ratios that utilize tangible common equity. Tangible
common equity is a non-GAAP financial measure and represents
total equity less preferred equity, noncontrolling interests,
goodwill, certain identifiable intangible assets (other than MSRs)
and goodwill and other intangibles on investments in
consolidated portfolio companies, net of applicable deferred
taxes. The ratios are (i) tangible book value per common share,
which represents tangible common equity divided by common
shares outstanding; and (ii) return on average tangible common
equity (ROTCE), which represents our annualized earnings as a
percentage of tangible common equity. The methodology of
determining tangible common equity may differ among
companies. Management believes that tangible book value per
common share and return on average tangible common equity,
which utilize tangible common equity, are useful financial
measures because they enable management, investors, and
others to assess the Company’s use of equity.
Table 46 provides a reconciliation of these non-GAAP
financial measures to GAAP financial measures.
Table 46: Tangible Common Equity
Balance at period-end Average balance
Quarter ended Year ended
(in millions, except ratios)
Dec 31,
2022
Dec 31,
2021
Dec 31,
2020
Dec 31,
2022
Dec 31,
2021
Dec 31,
2020
Total equity
$
181,875
190,110
185,712
183,224
191,219
184,689
Adjustments:
Preferred stock (1)
(19,448)
(20,057)
(21,136)
(19,930)
(21,151)
(21,364)
Additional paid-in capital on preferred stock (1)
173
136
152
143
137
148
Unearned ESOP shares (1)
—
646
875
512
874
1,007
Noncontrolling interests
(1,986)
(2,504)
(1,033)
(2,323)
(1,601)
(769)
Total common stockholders’ equity (A)
160,614
168,331
164,570
161,626
169,478
163,711
Adjustments:
Goodwill
(25,173)
(25,180)
(26,392)
(25,177)
(26,087)
(26,387)
Certain identifiable intangible assets (other than MSRs)
(152)
(225)
(342)
(190)
(294)
(389)
Goodwill and other intangibles on investments in consolidated
portfolio companies (included in other assets)
(2,427) (2,437) (1,965)
(2,359)
(2,226) (2,002)
Applicable deferred taxes related to goodwill and other intangible
assets (2)
890
765
856
864
867
834
Tangible common equity
(B)
141,254
136,727
134,764
141,738
135,767
Common shares outstanding
(C)
3,833.8
3,885.8
4,144.0
N/A
N/A
N/A
Net income applicable to common stock
(D)
N/A
N/A
N/A
20,256
1,786
Book value per common share
(A)/(C)
43.32
39.71
N/A
N/A
N/A
Tangible book value per common share
(B)/(C)
34.89
36.35
32.99
N/A
N/A
N/A
Return on average common stockholders’ equity (ROE)
(D)/(A)
N/A
N/A
N/A
7.47 %
11.95
1.09
Return on average tangible common equity (ROTCE)
(D)/(B)
N/A
N/A
N/A
8.95
14.29
1.32
Capital Management (continued)
$
133,752
$
41.89
$
12,067
(1) In fou rth quarter 2022, we r edeemed all ou tstanding shares of ou r ESOP C umulative C onvertible Pr eferred Stock in exch ange for shares of t he C ompany’s com mon st ock. For additional infor mation,
see Note 11 (Preferred Stock) t o F inancial S tatements in t his Rep ort.
(2) Determined by applying the com bined federal st atutory rate a nd composite st ate incom e t ax r ates t o t he d ifference b etween b ook and tax b asis of t he r espective g oodwill a nd intangible a ssets a t
period-end.
LEVERAGE REQUIREMENTS As a BHC, we are required to maintain
a supplementary leverage ratio (SLR) to avoid restrictions on
capital distributions and discretionary bonus payments and
maintain a minimum Tier 1 leverage ratio. Table 47 presents the
leverage requirements applicable to the Company as of
December 31, 2022 .
In addition, our IDIs are required to maintain an SLR of at
least 6.00% to be considered well capitalized under applicable
regulatory capital adequacy rules and maintain a minimum Tier 1
leverage ratio of 4.00%.
The FRB and OCC have proposed amendments to the SLR
rules (Proposed SLR rules) that would replace the 2.00%
supplementary leverage buffer with a buffer equal to one-half o f
our G-SIB capital surcharge. The Proposed SLR rules would
similarly tailor the current 6.00% SLR requirement for our IDIs .
Table 47: Leverage Requirements Applica ble to the C ompany
4.00%
5.00%
3.00%
4.00%
2.00%
Minimum requirement
Supplementary leverage buffer
Supplementary leverage
ratio
Tier 1 leverage ratio
Wells Fargo & Company 56
At December 31, 2022, the Company’s SLR was 6.86%, and
each of our IDIs exceeded their applicable SLR requirements.
Table 48 presents information regarding the calculation and
components of the Company’s SLR and Tier 1 leverage ratio.
Table 48: Leverage Ratios for the Company
($ in millions)
Quarter
ended
December
31,
2022
Tier 1 capital
(A)
$
152,567
Total average assets
1,875,396
Less: Goodwill and other permitted Tier 1 capital
deductions (net of deferred tax liabilities)
28,442
Total adjusted average assets
1,846,954
Plus adjustments for off-balance sheet exposures:
Derivatives (1)
63,277
Repo-style transactions (2)
3,250
Other (3)
311,308
Total off-balance sheet exposures
377,835
Total leverage exposure
(B)
$
2,224,789
Supplementary leverage ratio
(A)/(B)
6.86%
Tier 1 leverage ratio (4)
8.26%
(1)
(3)
(1) Adjustment represents d erivatives a nd collateral net ting exposures a s d efined for
supplementary leverage r atio d etermination p urposes.
(2) Adjustment represents cou nterparty credit risk for repo-style t ransactions wh ere
Wells F argo & Company is t he p rincipal cou nterparty facing the client .
(3) Adjustment represents cr edit equivalent amounts of ot her off-balance sh eet exposures
not already included as d erivatives a nd repo-style t ransactions exp osures.
(4) The Tier 1 lev erage r atio consist s of Tier 1 ca pital d ivided by total a verage a ssets, excluding
goodwill a nd certain ot her items a s d etermined under the r ule.
TOTAL LOSS ABSORBING CAPACITY As a G-SIB, we are required to
have a minimum amount of equity and unsecured long-term
debt for purposes of resolvability and resiliency, often referred to
as Total Loss Absorbing Capacity (TLAC). U.S. G-SIBs are required
to have a minimum amount of TLAC (consisting of CET1 capital
and additional Tier 1 capital issued directly by the top-tier or
covered BHC plus eligible external long-term debt) to avoid
restrictions on capital distributions and discretionary bonus
payments as well as a minimum amount of eligible unsecured
long-term debt. The components used to calculate our minimum
TLAC and eligible unsecured long-term debt requirements as of
December 31, 2022, are presented in Table 49.
Table 49: Components Used to Calculate TLAC and Eligible Unsecured
Long-Term Debt Requirements
TLAC requirement
Greater of:
7.50% of total leverage exposure
(the denominator of the SLR
calculation)
+
External TLAC leverage buffer
(equal to 2.00% of total leverage
exposure)
18.00% of RWAs
+
TLAC buffer (equal to 2.50% of RWAs
+ method one G-SIB capital surcharge
+ any countercyclical buffer)
Minimum amount of eligible unsecured long-term debt
Greater of:
6.00% of RWAs
+
Greater of method one and method
two G-SIB capital surcharge
4.50% of total leverage exposure
Under the Proposed SLR rules, the 2.00% external TLAC
leverage buffer would be replaced with a buffer equal to one-half
of our applicable G-SIB capital surcharge, and the leverage
component for calculating the minimum amount of eligible
unsecured long-term debt would be modified from 4.50% of
total leverage exposure to 2.50% of total leverage exposure plus
one-half of our applicable G-SIB capital surcharge.
Table 50 provides our TLAC and eligible unsecured long -
term debt and related ratios.
Table 50: TLAC and Eligible Unsecured Long-Term Debt
December 31, 2022
($ in millions) TLAC
Regulatory
Minimum
(2)
Eligible
Unsecured
Long-term
Debt
Regulatory
Minimum
Total eligible amount $ 293,152 134,521
Percentage of RWAs 23.27 % 21.50 10.68 7.50
Percentage of total
leverage exposure 13.18 9.50 6.05 4.50
(1) TLAC ratios a re ca lculated using the C ECL transition p rovision issu ed by federal b anking
regulators.
(2) Represents t he m inimum required to a void restrictions on ca pital d istributions a nd
discretionary bonus p ayments.
(3) Our minimum TLAC and eligible u nsecured long-term debt requirements a re ca lculated
based on t he g reater of RWAs d etermined under the S tandardized and Advanced
Approaches.
OTHER REGULATORY CAPITAL AND LIQUIDITY MATTERS For
information regarding the U.S. implementation of the Basel III
LCR and NSFR, see the “Risk Management – Asset/ Liability
Management – Liquidity Risk and Funding – Liquidity Standards”
section in this Report.
Our principal U.S. broker-dealer subsidiaries, Wells Fargo
Securities, LLC, and Wells Fargo Clearing Services, LLC, are
subject to regulations to maintain minimum net capital
requirements. As of December 31, 2022, these broker-dealer
subsidiaries were in compliance with their respective regulatory
minimum net capital requirements.
Capital Planning and Stress Testing
Our planned long-term capital structure is designed to meet
regulatory and market expectations. We believe that our long -
term targeted capital structure enables us to invest in and gro w
our business, satisfy our customers’ financial needs in varyin g
environments, access markets, and maintain flexibility to retur n
capital to our shareholders. Our long-term targeted capital
structure also considers capital levels sufficient to exceed ca pital
requirements, including the G-SIB capital surcharge and the
stress capital buffer, as well as potential changes to regulato ry
requirements for our capital ratios, planned capital actions,
changes in our risk profile and other factors . Accordingly, our
long-term target capital levels are set above their respective
regulatory minimums plus buffers.
The FRB capital plan rule establishes capital planning and
other requirements that govern capital distributions, including
dividends and share repurchases, by certain BHCs, including
Wells Fargo. The FRB assesses, among other things, the overall
financial condition, risk profile, and capital adequacy of BHCs
when evaluating their capital plans.
As part of the annual Comprehensive Capital Analysis and
Review, the FRB generates a supervisory stress test. The FRB
reviews the supervisory stress test results as required under the
Dodd-Frank Act using a common set of capital actions for all
large BHCs and also reviews the Company’s proposed capital
actions.
Federal banking regulators also require large BHCs and
banks to conduct their own stress tests to evaluate whether the
institution has sufficient capital to continue to operate during
periods of adverse economic and financial conditions.
Wells Fargo & Company 57

Capital Management (continued)
Securities Repurchases
From time to time the Board authorizes the Company to
repurchase shares of our common stock. Although we announce
when the Board authorizes share repurchases, we typically do not
give any public notice before we repurchase our shares. Various
factors determine the amount of our share repurchases,
including our capital requirements, the number of shares we
expect to issue for employee benefit plans and any acquisitions,
market conditions (including the trading price of our stock), and
regulatory and legal considerations, including under the FRB’s
capital plan rule. Due to the various factors that may impact the
amount of our share repurchases and the fact that we tend to be
in the market regularly to satisfy repurchase considerations
under our capital plan, our share repurchases occur at various
price levels. We may suspend share repurchase activity at any
time.
At December 31, 2022, we had remaining Board authority to
repurchase approximately 250 million shares, subject to
regulatory and legal conditions. For additional information about
share repurchases during fourth quarter 2022, see Part II, Item 5
in our 2022 Form 10-K.
Regulatory Matters
The U.S. financial services industry is subject to significant
regulation and regulatory oversight initiatives. This regulation
and oversight may continue to impact how U.S. financial services
companies conduct business and may continue to result in
increased regulatory compliance costs. The following highlights
the more significant regulations and regulatory oversight
initiatives that have affected or may affect our business. For
additional information about the regulatory matters discussed
below and other regulations and regulatory oversight matters,
see Part I, Item 1 “Regulation and Supervision” of our 2022 Form
10-K, and the “Overview,” “Capital Management,” “Forward-
Looking Statements” and “Risk Factors” sections and Note 25
(Regulatory Capital Requirements and Other Restrictions) to
Financial Statements in this Report.
Dodd-Frank Act
The Dodd-Frank Act is the most significant financial reform
legislation since the 1930s. The following provides additional
information on the Dodd-Frank Act, including certain of its
rulemaking initiatives.
• Enhanced supervision and regulation of systemically important
firms. The Dodd-Frank Act grants broad authority to federal
banking regulators to establish enhanced supervisory and
regulatory requirements for systemically important firms.
The FRB has finalized a number of regulations implementing
enhanced prudential requirements for large bank holding
companies (BHCs) like Wells Fargo regarding risk-based
capital and leverage, risk and liquidity management, single
counterparty credit limits, and imposing debt-to-equity
limits on any BHC that regulators determine poses a grave
threat to the financial stability of the United States. The FRB
and OCC have also finalized rules implementing stress
testing requirements for large BHCs and national banks. In
addition, the FRB has proposed a rule to establish
remediation requirements for large BHCs experiencing
financial distress. Furthermore, to promote a BHC’s safety
and soundness and the financial and operational resilience of
its operations, the FRB has finalized guidance regarding
effective boards of directors of large BHCs and has proposed
related guidance identifying core principles for effective
senior management. The OCC, under separate authority, has
finalized guidelines establishing heightened governance and
risk management standards for large national banks such as
Wells Fargo Bank, N.A. The OCC guidelines require covered
banks to establish and adhere to a written risk governance
framework to manage and control their risk-taking
activities. The guidelines also formalize roles and
responsibilities for risk management practices within
covered banks and create certain risk oversight
responsibilities for their boards of directors. In addition to
the authorization of enhanced supervisory and regulatory
requirements for systemically important firms, the Dodd-
Frank Act also established the Financial Stability Oversight
Council and the Office of Financial Research, which may
recommend new systemic risk management requirements
and require new reporting of systemic risks.
• Regulation of consumer financial products. The Dodd-Frank
Act established the Consumer Financial Protection Bureau
(CFPB) to ensure that consumers receive clear and accurate
disclosures regarding financial products and are protected
from unfair, deceptive or abusive practices. The CFPB has
issued a number of rules impacting consumer financial
products, including rules regarding the origination, servicing,
notification, disclosure and other requirements with respect
to residential mortgage lending, as well as rules impacting
prepaid cards, credit cards, and other financial products and
banking-related activities. In addition to these rulemaking
activities, the CFPB is continuing its ongoing supervisory
examination activities of the financial services industry with
respect to a number of consumer businesses and products,
including mortgage lending and servicing, fair lending
requirements, and auto finance.
• Regulation of swaps and other derivatives activities. The
Dodd-Frank Act established a comprehensive framework for
regulating over-the-counter derivatives, and, pursuant to
authority granted by the Dodd-Frank Act, the Commodity
Futures Trading Commission (CFTC) and the Securities and
Exchange Commission (SEC) have adopted comprehensive
sets of rules regulating swaps and security-based swaps,
respectively, and the OCC and other federal regulatory
agencies have adopted margin requirements for uncleared
swaps and security-based swaps. As a provisionally-
registered swap dealer and a conditionally-registered
security-based swap dealer, Wells Fargo Bank, N.A., is
subject to these rules. These rules, as well as others adopted
or under consideration by regulators in the United States
and other jurisdictions, may negatively impact customer
demand for over-the-counter derivatives, impact our ability
to offer customers new derivatives or amendments to
existing derivatives, and may increase our costs for engaging
in swaps, security-based swaps, and other derivatives
activities.
Regulatory Capital, Leverage, and Liquidity Requirements
The Company and each of our IDIs are subject to various
regulatory capital adequacy requirements administered by the
FRB and the OCC. For example, the Company is subject to rules
issued by federal banking regulators to implement Basel III risk-
based capital requirements for U.S. banking organizations. The
Company and its IDIs are also required to maintain specified
Wells Fargo & Company 58
leverage and supplementary leverage ratios. In addition, the
Company is required to have a minimum amount of total loss
absorbing capacity for purposes of resolvability and resiliency.
Federal banking regulators have also issued final rules requiring a
liquidity coverage ratio and a net stable funding ratio. For
additional information on the final risk-based capital, leverage
and liquidity rules, and additional capital requirements applicable
to us, see the “Capital Management” and “Risk Management –
Asset/Liability Management – Liquidity Risk and Funding –
Liquidity Standards” sections in this Report.
“Living Will” Requirements and Related Matters
Rules adopted by the FRB and the FDIC under the Dodd-Frank
Act require large financial institutions, including Wells Fargo , to
prepare and periodically submit resolution plans, also known a s
“living wills,” that would facilitate their rapid and orderly
resolution in the event of material financial distress or failu re.
Under the rules, rapid and orderly resolution means a
reorganization or liquidation of the covered company under the
U.S. Bankruptcy Code that can be accomplished in a reasonable
period of time and in a manner that substantially mitigates th e
risk that failure would have serious adverse effects on the
financial stability of the United States. In addition to the
Company’s resolution plan, our national bank subsidiary,
Wells Fargo Bank, N.A. (the “Bank”), is also required to prepar e
and periodically submit a resolution plan. If the FRB and/or FD IC
determine that our resolution plan has deficiencies, they may
impose more stringent capital, leverage or liquidity requiremen ts
on us or restrict our growth, activities or operations until w e
adequately remedy the deficiencies. If the FRB and/or FDIC
ultimately determine that we have been unable to remedy any
deficiencies, they could require us to divest certain assets o r
operations. On November 23, 2022, the FRB and FDIC
announced that the Company’s most recent resolution plan did
not have any shortcomings or deficiencies.
If Wells Fargo were to fail, it may be resolved in a bankruptcy
proceeding or, if certain conditions are met, under the resolution
regime created by the Dodd-Frank Act known as the “orderly
liquidation authority.” The orderly liquidation authority allows for
the appointment of the FDIC as receiver for a systemically
important financial institution that is in default or in danger of
default if, among other things, the resolution of the institution
under the U.S. Bankruptcy Code would have serious adverse
effects on financial stability in the United States. If the FDIC is
appointed as receiver for the Parent, then the orderly liquidation
authority, rather than the U.S. Bankruptcy Code, would
determine the powers of the receiver and the rights and
obligations of our security holders. The FDIC’s orderly liquidation
authority requires that security holders of a company in
receivership bear all losses before U.S. taxpayers are exposed to
any losses. There are substantial differences in the rights of
creditors between the orderly liquidation authority and the U.S.
Bankruptcy Code, including the right of the FDIC to disregard the
strict priority of creditor claims under the U.S. Bankruptcy Code
in certain circumstances and the use of an administrative claims
procedure instead of a judicial procedure to determine creditors’
claims.
The strategy described in our most recent resolution plan is
a single point of entry strategy, in which the Parent would be the
only material legal entity to enter resolution proceedings.
However, the strategy described in our resolution plan is not
binding in the event of an actual resolution of Wells Fargo,
whether conducted under the U.S. Bankruptcy Code or by the
FDIC under the orderly liquidation authority. The FDIC has
announced that a single point of entry strategy may be a
desirable strategy under its implementation of the orderly
liquidation authority, but not all aspects of how the FDIC might
exercise this authority are known and additional rulemaking is
possible.
To facilitate the orderly resolution of systemically important
financial institutions in case of material distress or failure, federal
banking regulations require that institutions, such as Wells Fargo,
maintain a minimum amount of equity and unsecured debt to
absorb losses and recapitalize operating subsidiaries. Federal
banking regulators have also required measures to facilitate the
continued operation of operating subsidiaries notwithstanding
the failure of their parent companies, such as limitations on
parent guarantees, and have issued guidance encouraging
institutions to take legally binding measures to provide capital
and liquidity resources to certain subsidiaries to facilitate an
orderly resolution. In response to the regulators’ guidance and to
facilitate the orderly resolution of the Company, on June 28,
2017, the Parent entered into a support agreement, as amended
and restated on June 26, 2019 (the “Support Agreement”), with
WFC Holdings, LLC, an intermediate holding company and
subsidiary of the Parent (the “IHC”), the Bank, Wells Fargo
Securities, LLC (“WFS”), Wells Fargo Clearing Services, LLC
(“WFCS”), and certain other subsidiaries of the Parent designated
from time to time as material entities for resolution planning
purposes (the “Covered Entities”) or identified from time to time
as related support entities in our resolution plan (the “Related
Support Entities”). Pursuant to the Support Agreement, the
Parent transferred a significant amount of its assets, including
the majority of its cash, deposits, liquid securities and
intercompany loans (but excluding its equity interests in its
subsidiaries and certain other assets), to the IHC and will
continue to transfer those types of assets to the IHC from time
to time. In the event of our material financial distress or failure,
the IHC will be obligated to use the transferred assets to provide
capital and/or liquidity to the Bank, WFS, WFCS, and the Covered
Entities pursuant to the Support Agreement. Under the Support
Agreement, the IHC will also provide funding and liquidity to the
Parent through subordinated notes and a committed line of
credit, which, together with the issuance of dividends, is expected
to provide the Parent, during business as usual operating
conditions, with the same access to cash necessary to service its
debts, pay dividends, repurchase its shares, and perform its other
obligations as it would have had if it had not entered into these
arrangements and transferred any assets. If certain liquidity and/
or capital metrics fall below defined triggers, or if the Parent’s
board of directors authorizes it to file a case under the U.S.
Bankruptcy Code, the subordinated notes would be forgiven, the
committed line of credit would terminate, and the IHC’s ability to
pay dividends to the Parent would be restricted, any of which
could materially and adversely impact the Parent’s liquidity and
its ability to satisfy its debts and other obligations, and could
result in the commencement of bankruptcy proceedings by the
Parent at an earlier time than might have otherwise occurred if
the Support Agreement were not implemented. The respective
obligations under the Support Agreement of the Parent, the IHC,
the Bank, and the Related Support Entities are secured pursuant
to a related security agreement.
In addition to our resolution plans, we must also prepare and
periodically submit to the FRB a recovery plan that identifies a
range of options that we may consider during times of
idiosyncratic or systemic economic stress to remedy any financial
weaknesses and restore market confidence without
extraordinary government support. Recovery options include the
possible sale, transfer or disposal of assets, securities, loan
portfolios or businesses. The Bank must also prepare and
Wells Fargo & Company 59
Regulatory Matters (continued)
periodically submit to the OCC a recovery plan that sets forth the
Bank’s plan to remain a going concern when the Bank is
experiencing considerable financial or operational stress, but has
not yet deteriorated to the point where liquidation or resoluti on
is imminent. If either the FRB or the OCC determines that our
recovery plan is deficient, they may impose fines, restriction s on
our business or ultimately require us to divest assets.
Other Regulatory Related Matters
• Regulatory actions. The Company is subject to a number of
consent orders and other regulatory actions, which may
require the Company, among other things, to undertake
certain changes to its business, operations, products and
services, and risk management practices, and include the
following:
◦ Consent Orders Discussed in the “Overview” Section in this
Report. For a discussion of certain consent orders
applicable to the Company, see the “Overview” section
in this Report.
◦ OCC approval of director and senior executive officer
appointments and certain post-termination payments.
Under the April 2018 consent order with the OCC,
Wells Fargo Bank, N.A., remains subject to requirements
that were originally imposed in November 2016 to
provide prior written notice to, and obtain non-
objection from, the OCC with respect to changes in
directors and senior executive officers, and remains
subject to certain regulatory limitations on post-
termination payments to certain individuals and
employees.
• Regulatory Developments Related to COVID-19. In response
to the COVID-19 pandemic and related events, federal
banking regulators undertook a number of measures to help
stabilize the banking sector, support the broader economy,
and facilitate the ability of banking organizations like
Wells Fargo to continue lending to consumers and
businesses. In addition, the OCC and the FRB issued
guidelines for banks and BHCs related to working with
customers affected by the COVID-19 pandemic, including
guidance with respect to waiving fees, offering repayment
accommodations, and providing payment deferrals. Any
current or future rules, regulations, and guidance related to
the COVID-19 pandemic and its impacts could require us to
change certain of our business practices, reduce our revenue
and earnings, impose additional costs on us, or otherwise
adversely affect our business operations and/or competitive
position.
• Regulatory Developments in Response to Climate Change.
Federal and state governments and government agencies
have demonstrated increased attention to the impacts and
potential risks associated with climate change. For example,
federal banking regulators are reviewing the implications of
climate change on the financial stability of the United States
and the identification and management by large banks of
climate-related financial risks. In addition, the SEC has
proposed rules that would require public companies to
disclose certain climate-related information, including
greenhouse gas emissions, climate-related targets and
goals, and governance of climate-related risks and relevant
risk management processes. The approaches taken by
various governments and government agencies can vary
significantly, evolve over time, and sometimes conflict. Any
current or future rules, regulations, and guidance related to
climate change and its impacts could require us to change
certain of our business practices, reduce our revenue and
earnings, impose additional costs on us, or otherwise
adversely affect our business operations and/or competitive
position.
Wells Fargo & Company 60

Critical Accounting Policies
Our significant accounting policies (see Note 1 (Summary of
Significant Accounting Policies) to Financial Statements in this
Report) are fundamental to understanding our results of
operations and financial condition because they require that we
use estimates and assumptions that may affect the value of our
assets or liabilities and financial results. Six of these policies are
critical because they require management to make difficult,
subjective and complex judgments about matters that are
inherently uncertain and because it is likely that materially
different amounts would be reported under different conditions
or using different assumptions. These policies govern:
• the allowance for credit losses;
• the valuation of residential MSRs;
• the fair value of financial instruments;
• income taxes;
• liability for contingent litigation losses; and
• goodwill impairment.
Management has discussed these critical accounting policies
and the related estimates and judgments with the Board’s Audit
Committee.
Allowance for Credit Losses
We maintain an allowance for credit losses (ACL) for loans, which
is management’s estimate of the expected credit losses in the
loan portfolio and unfunded credit commitments, at the balance
sheet date, excluding loans and unfunded credit commitments
carried at fair value or held for sale. Additionally, we maintain an
ACL for debt securities classified as either HTM or AFS, other
financial assets measured at amortized cost, net investments in
leases, and other off-balance sheet credit exposures. For
additional information, see Note 1 (Summary of Significant
Accounting Policies) and Note 5 (Loans and Related Allowance
for Credit Losses) to Financial Statements in this Report.
For loans and HTM debt securities, the ACL is measured
based on the remaining contractual term of the financial asset
(including off-balance sheet credit exposures) adjusted, as
appropriate, for prepayments and permitted extension options
using historical experience, current conditions, and forecasted
information. For AFS debt securities, the ACL is measured using a
discounted cash flow approach and is limited to the difference
between the fair value of the security and its amortized cost.
Changes in the ACL and, therefore, in the related provision
for credit losses can materially affect net income. In applying the
judgment and review required to determine the ACL,
management considerations include the evaluation of past
events, historical experience, changes in economic forecasts and
conditions, customer behavior, collateral values, the length of the
initial loss forecast period, and other influences. From time to
time, changes in economic factors or assumptions, business
strategy, products or product mix, or debt security investment
strategy, may result in a corresponding increase or decrease in
our ACL. While our methodology attributes portions of the ACL
to specific financial asset classes (loan and debt security
portfolios) or loan portfolio segments (commercial and
consumer), the entire ACL is available to absorb credit losses of
the Company.
Judgment is specifically applied in:
• Economic assumptions and the length of the initial loss forecast
period. We forecast a wide range of economic variables to
estimate expected credit losses. Our key economic variables
include gross domestic product (GDP), unemployment rate,
and collateral asset prices. While many of these economic
variables are evaluated at the macro-economy level, some
economic variables are forecasted at more granular levels,
for example, using the metro statistical area (MSA) level for
unemployment rates, home prices and commercial real
estate prices. At least annually, we assess the length of the
initial loss forecast period and have currently set the period
to two years. For the initial loss forecast period, we forecast
multiple economic scenarios that generally include a base
scenario with an optimistic (upside) and one or more
pessimistic (downside) scenarios. Management exercises
judgment when assigning weight to the economic scenarios
that are used to estimate future credit losses.
• Reversion to historical loss expectations. Our long-term
average loss expectations are estimated by reverting to the
long-term average, on a linear basis, for each of the
forecasted economic variables. These long-term averages
are based on observations over multiple economic cycles.
The reversion period, which may be up to two years, is
assessed on a quarterly basis.
• Credit risk ratings applied to individual commercial loans,
unfunded credit commitments, and debt securities. Individually
assessed credit risk ratings are considered key credit
variables in our modeled approaches to help assess
probability of default and loss given default. Borrower
quality ratings are aligned to the borrower’s financial
strength and contribute to forecasted probability of default
curves. Collateral quality ratings combined with forecasted
collateral prices (as applicable) contribute to the forecasted
severity of loss in the event of default. These credit risk
ratings are reviewed by experienced senior credit officers
and subjected to reviews by an internal team of credit risk
specialists.
• Usage of credit loss estimation models. We use internally
developed models that incorporate credit attributes and
economic variables to generate credit loss estimates.
Management uses judgment and quantitative analytics in
the determination of segmentation, modeling approach, and
variables that are leveraged in the models. These models are
independently validated in accordance with the Company’s
policies. We routinely assess our model performance and
apply adjustments when necessary to improve the accuracy
of loss estimation. We also assess our models for limitations
against the company-wide risk inventory to help
appropriately capture known and emerging risks in our
estimate of expected credit losses and apply overlays as
needed.
• Valuation of collateral. The current fair value of collateral is
utilized to assess the expected credit losses when a financial
asset is considered to be collateral dependent. We apply
judgment when valuing the collateral either through
appraisals, evaluation of the cash flows of the property, or
other quantitative techniques. Decreases in collateral
valuations support incremental charge-downs and increases
in collateral valuation are included in the ACL as a negative
allowance when the financial asset has been previously
written-down below current recovery value.
• Contractual term considerations. The remaining contractual
term of a loan is adjusted for expected prepayments and
certain expected extensions, renewals, or modifications. We
extend the contractual term when we are not able to
unconditionally cancel contractual renewals or extension
Wells Fargo & Company 61

Critical Accounting Policies (continued)
options. We also incorporate any scenarios where we
reasonably expect to provide an extension through a
troubled debt restructuring (TDR). Credit card loans have
indeterminate maturities, which requires that we determine
a contractual life by estimating the application of future
payments to the outstanding loan amount.
• Qualitative factors which may not be adequately captured in
the loss models. These amounts represent management’s
judgment of risks inherent in the processes and assumptions
used in establishing the ACL. We also consider economic
environmental factors, modeling assumptions and
performance, process risk, and other subjective factors,
including industry trends and emerging risk assessments.
Sensitivity The ACL for loans is sensitive to changes in key
assumptions which requires significant management judgment.
Future amounts of the ACL for loans will be based on a variety of
factors, including loan balance changes, portfolio credit quali ty,
and general forecasted economic conditions. The forecasted
economic variables used could have varying impacts on differen t
financial assets or portfolios. Additionally, throughout numero us
credit cycles, there are observed changes in economic variable s
such as the unemployment rate, GDP and real estate prices whic h
may not move in a correlated manner as variables may move in
opposite directions or differ across portfolios or geography.
Our sensitivity analysis does not represent management’s
view of expected credit losses at the balance sheet date. We
applied a 100% weight to a more severe downside scenario in our
sensitivity analysis to reflect the potential for further economic
deterioration. The outcome of the scenario was influenced by the
duration, severity, and timing of changes in economic variables
within the scenario. The sensitivity analysis resulted in a
hypothetical increase in the ACL for loans of approximately
$7.0 billion at December 31, 2022. The hypothetical increase in
our ACL for loans does not incorporate the impact of
management judgment for qualitative factors applied in the
current ACL for loans, which may have a positive or negative
effect on the results. It is possible that others performing similar
sensitivity analyses could reach different conclusions or results.
The sensitivity analysis excludes the ACL for debt securities
and other financial assets given its size relative to the overall
ACL. Management believes that the estimate for the ACL for
loans was appropriate at the balance sheet date.
Valuation of Residential Mortgage Servicing Rights
(MSRs)
MSRs are assets that represent the rights to service mortgage
loans for others. We recognize MSRs when we retain servicing
rights in connection with the sale or securitization of loans we
originate (asset transfers), or purchase servicing rights from
third parties. We also have acquired MSRs in the past under co-
issuer agreements that provide for us to service loans that were
originated and securitized by third-party correspondents.
We carry our MSRs related to residential mortgage loans
at fair value. Periodic changes in our residential MSRs and the
economic hedges used to hedge our residential MSRs are
reflected in earnings.
We use a model to estimate the fair value of our
residential MSRs. The model is validated in accordance with
Company policies by an internal model validation group. The
model calculates the present value of estimated future net
servicing income and incorporates inputs and assumptions
that market participants use in estimating fair value. Certain
significant inputs and assumptions generally are not
observable in the market and require judgment to determine.
If observable market indications do become available, these
are factored into the estimates as appropriate:
• The mortgage loan prepayment rate used to estimate future
net servicing income. The prepayment rate is the annual rate
at which borrowers are forecasted to repay their mortgage
loan principal; this rate also includes estimated borrower
defaults. We use models to estimate prepayment rate and
borrower defaults which are influenced by changes in
mortgage interest rates and borrower behavior.
• The discount rate used to present value estimated future net
servicing income. The discount rate is the required rate of
return investors in the market would expect for an asset
with similar risk. To determine the discount rate, we consider
the risk premium for uncertainties in the cash flow estimates
such as from servicing operations (e.g., possible changes in
future servicing costs, ancillary income and earnings on
escrow accounts). In 2022, we enhanced our approach for
estimating the discount rate to a more dynamic
methodology for market curves and volatility.
• The expected cost to service loans used to estimate future net
servicing income. The cost to service loans includes
estimates for unreimbursed expenses, such as delinquency
and foreclosure costs, which considers the number of
defaulted loans as well as the incremental cost to service
loans in default and foreclosure. We use a market
participant’s view for our estimated cost to service and our
actual costs may vary from that estimate.
Both prepayment rate and discount rate assumptions can,
and generally will, change quarterly as market conditions and
mortgage interest rates change. For example, an increase in
either the prepayment rate or discount rate assumption results
in a decrease in the fair value of the MSRs, while a decrease in
either assumption would result in an increase in the fair value of
the MSRs. In recent years, there have been significant market-
driven fluctuations in loan prepayment rate and the discount
rate. These fluctuations can be rapid and may be significant in the
future. Additionally, future regulatory or investor changes in
servicing standards as well as changes in individual state
foreclosure legislation or changes in market participant
information regarding servicing cost assumptions, may have an
impact on our servicing cost assumption and our MSR valuation
in future periods. We periodically benchmark our MSR fair value
estimate to independent appraisals.
For a description of our valuation and sensitivity of MSRs,
see Note 1 (Summary of Significant Accounting Policies), Note 6
(Mortgage Banking Activities), Note 15 (Fair Values of Assets
and Liabilities) and Note 16 (Securitizations and Variable Interest
Entities) to Financial Statements in this Report.
Fair Value of Financial Instruments
Fair value represents the price that would be received to sell a
financial asset or paid to transfer a financial liability in an orderly
transaction between market participants at the measurement
date.
We use fair value measurements to record fair value
adjustments to certain financial instruments and to fulfill fair
value disclosure requirements. For example, assets and liabilities
held for trading purposes, marketable equity securities, AFS
debt securities, derivatives and a majority of our LHFS are
carried at fair value each period. Other financial instruments,
such as certain LHFS, substantially all nonmarketable equity
securities, and loans held for investment, are not carried at fair
value each period but may require nonrecurring fair value
adjustments through the application of an accounting method
Wells Fargo & Company 62
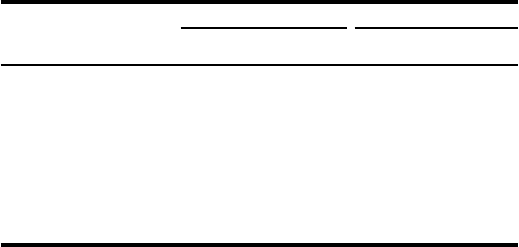
such as lower-of-cost-or-fair value (LOCOM), write-downs of
individual assets, or application of the measurement alternative
for certain nonmarketable equity securities. We also disclose our
estimate of fair value for financial instruments not carried at fair
value, such as HTM debt securities, loans held for investment,
and long-term debt.
The accounting requirements for fair value measurements
include a three-level hierarchy for disclosure of assets and
liabilities recorded at fair value. The classification of assets and
liabilities within the hierarchy is based on whether the inputs to
the valuation methodology used for measurement are
observable or unobservable. Observable inputs reflect market-
derived or market-based information obtained from
independent sources, while unobservable inputs reflect our
estimates about market data.
When developing fair value measurements, we maximize the
use of observable inputs and minimize the use of unobservable
inputs. When available, we use quoted prices in active markets to
measure fair value. If quoted prices in active markets are not
available, fair value measurement is based upon models that
generally use market-based or independently sourced market
parameters, including interest rate yield curves, prepayment
rates, option volatilities and currency rates. However, when
observable market data is limited or not available, fair value
estimates are typically determined using internal models based
on unobservable inputs. Internal models used to determine fair
value are validated in accordance with Company policies by an
internal model validation group. Additionally, we use third-party
pricing services to obtain fair values, which are used to either
record the price of an instrument or to corroborate internal
prices. Third-party price validation procedures are performed
over the reasonableness of the fair value measurements.
When using internal models based on unobservable inputs,
management judgment is necessary as we make judgments
about significant assumptions that market participants would
use to estimate fair value. Determination of these assumptions
includes consideration of many factors, including market
conditions and liquidity levels. Changes in the market conditions,
such as reduced liquidity in the capital markets or changes in
secondary market activities, may reduce the availability and
reliability of quoted prices or observable data used to determine
fair value. In such cases, it may be appropriate to adjust available
quoted prices or observable market data. For example, we may
adjust a price received from a third-party pricing service using
internal models based on discounted cash flows when the impact
of illiquid markets has not already been incorporated in the fair
value measurement. Additionally, for certain residential LHFS and
certain debt and equity securities where the significant inputs
have become unobservable due to illiquid markets and a third-
party pricing service is not used, our discounted cash flow model
uses a discount rate that reflects what we believe a market
participant would require in light of the illiquid market.
We continually assess the level and volume of market
activity in our debt and equity security classes in determining
adjustments, if any, to quoted prices. Given market conditions
can change over time, our determination of which securities
markets are considered active or inactive can change. If we
determine a market to be inactive, the degree to which quoted
prices require adjustment, can also change.
Significant judgment is also applied in the determination of
whether certain assets measured at fair value are classified as
Level 2 or Level 3 of the fair value hierarchy. When making this
judgment, we consider available information, including
observable market data, indications of market liquidity and
orderliness, and our understanding of the valuation techniques
and significant inputs used to estimate fair value. The
classification as Level 2 or Level 3 is based upon the specific facts
and circumstances of each instrument or instrument category
and judgments are made regarding the significance of
unobservable inputs to each instrument’s fair value
measurement in its entirety. If unobservable inputs are
considered significant to the fair value measurement, the
instrument is classified as Level 3.
Table 51 presents our (1) assets and liabilities recorded at
fair value on a recurring basis and (2) Level 3 assets and liabilities
recorded at fair value on a recurring basis, both presented as a
percentage of our total assets and total liabilities.
Table 51: Fair Va lue Level 3 S ummary
December 31, 2022 December 31, 2021
($ in billions)
Total
balance Level 3 (1)
Total
balance Level 3 (1)
Assets recorded at fair
value on a recurring
basis
$ 264.4 11.5 348.9 19.6
As a percentage
of total assets
14 % * 18 1
Liabilities recorded at fair
value on a recurring
basis
$ 41.7 4.7 30.1 2.6
As a percentage of
total liabilities
2 % * 2 *
* Less t han 1%.
(1) Before d erivative net ting adjustments.
See Note 15 (Fair Values of Assets and Liabilities ) to
Financial Statements in this Report for a complete discussion o n
our fair value of financial instruments, our related measuremen t
techniques and the impact to our financial statements.
Income Taxes
We file income tax returns in the jurisdictions in which we
operate and evaluate income tax expense in two components:
current and deferred income tax expense. Current income tax
expense represents our estimated taxes to be paid or refunded
for the current period and includes income tax expense related to
uncertain tax positions. Uncertain tax positions that meet the
more likely than not recognition threshold are measured to
determine the amount of benefit to recognize. An uncertain tax
position is measured at the largest amount of benefit that
management believes has a greater than 50% likelihood of
realization upon settlement. Tax benefits not meeting our
realization criteria represent unrecognized tax benefits.
Deferred income taxes are based on the balance sheet
method and deferred income tax expense results from changes
in deferred tax assets and liabilities between periods. Under the
balance sheet method, the net deferred tax asset or liability is
based on the tax effects of the differences between the book and
tax basis of assets and liabilities, and recognizes enacted changes
in tax rates and laws in the period in which they occur. Deferred
tax assets are recognized subject to management’s judgment
that realization is more likely than not. A valuation allowance
reduces deferred tax assets to the realizable amount.
The income tax laws of the jurisdictions in which we operate
are complex and subject to different interpretations by
management and the relevant government taxing authorities. In
establishing a provision for income tax expense, we must make
judgments about the application of these inherently complex tax
laws. We must also make estimates about when in the future
certain items will affect taxable income in the various tax
jurisdictions. Our interpretations may be subjected to review
during examination by taxing authorities and disputes may arise
Wells Fargo & Company 63
Critical Accounting Policies (continued)
over the respective tax positions. We attempt to resolve these
disputes during the tax examination and audit process and
ultimately through the court systems when applicable.
We monitor relevant tax authorities and revise our estimate
of accrued income taxes due to changes in income tax laws and
their interpretation by the courts and regulatory authorities on a
quarterly basis. Revisions of our estimate of accrued income
taxes also may result from our own income tax planning and from
the resolution of income tax controversies. Such revisions in our
estimates may be material to our operating results for any given
quarter.
See Note 22 (Income Taxes) to Financial Statements in this
Report for a further description of our provision for income taxes
and related income tax assets and liabilities.
Liability for Contingent Litigation Losses
The Company is involved in a number of judicial, regulatory,
governmental, arbitration and other proceedings or
investigations concerning matters arising from the conduct of its
business activities, and many of those proceedings and
investigations expose the Company to potential financial loss or
other adverse consequences. We establish accruals for legal
actions when potential losses associated with the actions
become probable and the costs can be reasonably estimated. For
such accruals, we record the amount we consider to be the best
estimate within a range of potential losses that are both
probable and estimable; however, if we cannot determine a best
estimate, then we record the low end of the range of those
potential losses. The actual costs of resolving legal actions may
be substantially higher or lower than the amounts accrued for
those actions.
We apply judgment when establishing an accrual for
potential losses associated with legal actions and in establishing
the range of reasonably possible losses in excess of the accrual.
Our judgment in establishing accruals and the range of
reasonably possible losses in excess of the Company’s accrual for
probable and estimable losses is influenced by our understanding
of information currently available related to the legal evaluation
and potential outcome of actions, including input and advice on
these matters from our internal counsel, external counsel and
senior management. These matters may be in various stages of
investigation, discovery or proceedings. They may also involve a
wide variety of claims across our businesses, legal entities and
jurisdictions. The eventual outcome may be a scenario that was
not considered or was considered remote in anticipated
occurrence. Accordingly, our estimate of potential losses will
change over time and the actual losses may vary significantly.
The outcomes of legal actions are unpredictable and subject
to significant uncertainties, and it is inherently difficult to
determine whether any loss is probable or even possible. It is also
inherently difficult to estimate the amount of any loss and there
may be matters for which a loss is probable or reasonably
possible but not currently estimable. Accordingly, actual losses
may be in excess of the established accrual or the range of
reasonably possible loss.
See Note 13 (Legal Actions) to Financial Statements in this
Report for additional information.
Goodwill Impairment
We test goodwill for impairment annually in the fourth quarter or
more frequently as macroeconomic and other business factors
warrant. These factors may include trends in short-term or long -
term interest rates, negative trends from reduced revenue
generating activities or increased costs, adverse actions by
regulators, or company specific factors such as a decline in
market capitalization.
We identify reporting units to be assessed for goodwill
impairment at the reportable operating segment level or one
level below. We calculate reporting unit carrying amounts as
allocated capital plus assigned goodwill and other intangible
assets. We allocate capital to the reporting units under a risk-
sensitive framework driven by our regulatory capital
requirements. We estimate fair value of the reporting units
based on a balanced weighting of fair values estimated using
both an income approach and a market approach which are
intended to reflect Company performance and expectations as
well as external market conditions. The methodologies for
calculating carrying amounts and estimating fair values are
periodically assessed by senior management and revised as
necessary.
The income approach is a discounted cash flow (DCF)
analysis, which estimates the present value of future cash flows
associated with each reporting unit. A DCF analysis requires
significant judgment to model financial forecasts for our
reporting units, which includes future expectations of economic
conditions and balance sheet changes, as well as considerations
related to future business activities. The forecasts are reviewed
by senior management. For periods after our financial forecasts,
we incorporate a terminal value estimate based on an assumed
long-term growth rate. We discount these forecasted cash flows
using a consistent rate derived from the capital asset pricing
model which produces an estimated cost of equity for our
reporting units, which reflects risks and uncertainties in the
financial markets and in our internally generated business
projections.
The market approach utilizes observable market data from
comparable publicly traded companies, such as price-to-earnings
or price-to-tangible book value ratios, to estimate a reporting
unit’s fair value. The results of the market approach include a
control premium to represent our expectation of a hypothetical
acquisition of the reporting unit. Management uses judgment in
the selection of comparable companies and includes those with
the most similar business activities.
The aggregate fair value of our reporting units exceeded our
market capitalization for our fourth quarter 2022 assessment.
Factors that we considered in our assessment and contributed to
this difference included: (i) an overall premium that would be paid
to gain control of the operating and financial decisions of the
Company, (ii) synergies that we believe may not be reflected in
the price of the Company’s common stock, and (iii) risks or
benefits at the Company level that may not be reflected in the
aggregated fair value of the individual reporting units, such as
the impacts of a variety of historical matters, including litigation,
regulatory, and customer remediation matters.
Based on our fourth quarter 2022 assessment, there was no
impairment of goodwill at December 31, 2022. The fair values of
each reporting unit exceeded their carrying amounts by
substantial amounts, with the exception of our Consumer
Lending reporting unit. Although the fair value of our Consumer
Lending reporting unit exceeded its carrying amount by more
than 10%, it was the most sensitive to changes in valuation
assumptions, particularly related to the financial forecasts of
the supporting businesses. The home lending business may
experience uncertainty related to the current mortgage
origination market and the outcome of planned changes to the
business model. The credit card business has forecasted higher
loan balances driven by growth from new products. Adverse
changes to these forecasts may result in an impairment. Using
our fourth quarter 2022 assessment, we would need to
Wells Fargo & Company 64
experience a substantial decrease in forecasted earnings of the
Consumer Lending reporting unit or have a significant increase
in the discount rate used for the DCF analysis to result in an
impairment. The amount of goodwill assigned to the Consumer
Lending reporting unit was $7.1 billion at December 31, 2022.
Declines in our ability to generate revenue, significant
increases in credit losses or other expenses, or adverse actions
from regulators are factors that could result in material goodwill
impairment of any reporting unit in a future period.
For additional information on goodwill and our reportable
operating segments, see Note 1 (Summary of Significant
Accounting Policies), Note 7 (Intangible Assets and Other
Assets), and Note 19 (Operating Segments) to Financial
Statements in this Report.
Current Accounting Developments
Table 52 provides the significant accounting updates applicable
to us that have been issued by the Financial Accounting
Standards Board (FASB) but are not yet effective.
Table 52: Current Accounting Developments – Issued Standards
Description a nd Effective Da te Financial statement impact
Accounting Standards Update (ASU) 2018-12 – Financial Services – Insurance (Topic 944):
Targeted Improvements to the Accounting for Long-Duration Contracts and subsequent related updates
The Update, effective January 1, 2023,
requires market risk benefits (features
of insurance contracts that protect the
policyholder from other-than-nominal
capital market risk and expose the
insurer to that risk) to be measured at
fair value through earnings with changes
in fair value attributable to our own
credit risk recognized in other
comprehensive income. The Update also
requires more frequent updates for
insurance assumptions, mandates the
use of a standardized discount rate for
traditional long-duration contracts, and
simplifies the amortization of deferred
acquisition costs.
We adopted the Update on January 1, 2023, with retroactive application to prior periods. The most
significant impact of adoption relates to reinsurance of variable annuity products for a limited number of
our insurance clients. Our reinsurance business is no longer entering into new contracts. These variable
annuity products contain guaranteed minimum benefits that require us to make benefit payments for
the remainder of the policyholder’s life once the account values are exhausted. These guaranteed
minimum benefits meet the definition of market risk benefits and are measured at fair value.
At adoption, the effect of the difference between fair value and the carrying value of our market risk
benefits, net of income tax adjustments and excluding the impact of our own credit risk, was
approximately $325 million as of January 1, 2023. The adjustment increased our retained earnings and
regulatory capital amounts and ratios. The adjustment for the impact of our own credit risk recorded as
an increase to other comprehensive income was approximately $15 million, net of tax, as of January 1,
2023. We expect future earnings volatility from changes in the fair value of market risk benefits, which
are sensitive to changes in equity and fixed income markets, as well as policyholder behavior and changes
in mortality assumptions. We economically hedge the market volatility, where feasible.
Changes in the accounting for the liability of future policy benefits for traditional long-duration contracts
and deferred acquisition costs did not have a material impact upon adoption.
ASU 2022-01, Derivatives and Hedging (Topic 815): Fair Value Hedging – Portfolio Layer Method
The Update, effective January 1, 2023
(with early adoption permitted),
establishes the portfolio layer method,
which expands an entity’s ability to
achieve fair value hedge accounting for
interest rate risk hedges of closed
portfolios of financial assets. The Update
also provides guidance on the
accounting for hedged item basis
adjustments under the portfolio layer
method.
We adopted the Update on January 1, 2023 on a prospective basis. No cumulative effect adjustment to
the opening balance of stockholders’ equity was required upon adoption, as impacts to us were reflected
prospectively. The Update improves our ability to use derivatives to hedge interest rate risk exposures
associated with portfolios of financial assets, such as fixed-rate available-for-sale debt securities and
loans. The Update allows us to hedge a larger proportion of these portfolios by expanding the number
and type of derivatives permitted as eligible hedges, as well as by increasing the scope of eligible hedged
items to include both prepayable and nonprepayable assets.
Upon adoption, any election to designate portfolio layer method hedges is applied prospectively.
Additionally, the Update permits a one-time reclassification of debt securities from held-to-maturity to
available-for-sale classification as long as the securities are designated in a portfolio layer method hedge
no later than 30 days after the adoption date.
In January 2023, we reclassified fixed-rate debt securities with an aggregate fair value of $23.2 billion
and amortized cost of $23.9 billion from held-to-maturity to available-for-sale and designated interest
rate swaps with notional amounts of $20.1 billion as fair value hedges using the portfolio layer method.
The transfer of debt securities was recorded at fair value and resulted in approximately $566 million of
unrealized losses associated with available-for-sale debt securities being recorded to other
comprehensive income, net of deferred taxes.
(continued on following page)
Wells Fargo & Company 65
Current Accounting Developments (continued)
(continued from previous page)
Description a nd Effective Da te Financial statement impact
ASU 2022-02, Financial Instruments-Credit Losses (Topic 326): Troubled Debt Restructurings and Vintage Disclosures
The Update, effective January 1, 2023
(with early adoption permitted),
eliminates the accounting and reporting
for TDRs by creditors and introduces
new required disclosures for loan
modifications made to borrowers
experiencing financial difficulty. The
Update also amends the guidance for
vintage disclosures to require disclosure
of current period gross charge-offs by
year of origination.
We adopted the Update on January 1, 2023. The Update will impact the measurement of the ACL for
loans and require new enhanced disclosures related to loan modifications and credit quality, specifically
the Update:
• Eliminates the requirement to use a discounted cash flow (DCF) approach to measure the ACL for
TDRs and instead allows for the use of an expected loss approach for all loans. On January 1, 2023,
we removed the interest concession component recognized in the ACL for TDRs using a DCF
approach. The cumulative effect adjustment reflected the difference between the pre-modification
and post-modification effective interest rates, which would have been recognized over the
remaining life of the loans as interest income. The adjustment was a reduction to the ACL for loans
of approximately $430 million, and an increase to retained earnings of approximately $320 million,
after-tax. This adjustment to retained earnings impacts regulatory capital amounts and ratios.
• Eliminates TDR disclosures and requires new disclosures for modifications made to borrowers
experiencing financial difficulty in the form of principal forgiveness, interest rate reduction, other
than insignificant payment delay, term extension, or a combination of these modifications.
• Requires us to provide current period gross charge-offs by origination date (vintage) in our credit
quality disclosures on a prospective basis beginning as of the adoption date.
Other Accounting Developments
The following Updates are applicable to us but are not expected
to have a material impact on our consolidated financial
statements:
• ASU 2021-08 – Business Combinations (Topic 805):
Accounting for Contract Assets and Contract Liabilities from
Contracts with Customers
• ASU 2022-03 – Fair Value Measurement (Topic 820): Fair
Value Measurement of Equity Securities Subject to Contractual
Sale Restrictions
Wells Fargo & Company 66

Forward-Looking Statements
This document contains forward-looking statements. In addition ,
we may make forward-looking statements in our other
documents filed or furnished with the Securities and Exchange
Commission, and our management may make forward-looking
statements orally to analysts, investors, representatives of th e
media and others. Forward-looking statements can be identified
by words such as “anticipates,” “intends,” “plans,” “seeks,”
“believes,” “estimates,” “expects,” “target,” “projects,” “outl ook,”
“forecast,” “will,” “may,” “could,” “should,” “can” and simila r
references to future periods. In particular, forward-looking
statements include, but are not limited to, statements we make
about: (i) the future operating or financial performance of th e
Company, including our outlook for future growth; (ii) our
noninterest expense and efficiency ratio; (iii) future credit q uality
and performance, including our expectations regarding future
loan losses, our allowance for credit losses, and the economic
scenarios considered to develop the allowance; (iv) our
expectations regarding net interest income and net interest
margin; (v) loan growth or the reduction or mitigation of risk in
our loan portfolios; (vi) future capital or liquidity levels, r atios or
targets; (vii) the performance of our mortgage business and an y
related exposures; (viii) the expected outcome and impact of
legal, regulatory and legislative developments, as well as our
expectations regarding compliance therewith; (ix) future
common stock dividends, common share repurchases and other
uses of capital; (x) our targeted range for return on assets, r eturn
on equity, and return on tangible common equity; (xi)
expectations regarding our effective income tax rate; (xii) th e
outcome of contingencies, such as legal proceedings; (xiii)
environmental, social and governance related goals or
commitments; and (xiv) the Company’s plans, objectives and
strategies.
Forward-looking statements are not based on historical
facts but instead represent our current expectations and
assumptions regarding our business, the economy and other
future conditions. Because forward-looking statements relate t o
the future, they are subject to inherent uncertainties, risks a nd
changes in circumstances that are difficult to predict. Our act ual
results may differ materially from those contemplated by the
forward-looking statements. We caution you, therefore, against
relying on any of these forward-looking statements. They are
neither statements of historical fact nor guarantees or
assurances of future performance. While there is no assurance
that any list of risks and uncertainties or risk factors is com plete,
important factors that could cause actual results to differ
materially from those in the forward-looking statements includ e
the following, without limitation:
• current and future economic and market conditions,
including the effects of declines in housing prices, high
unemployment rates, U.S. fiscal debt, budget and tax
matters, geopolitical matters (including the conflict in
Ukraine), and any slowdown in global economic growth;
• the effect of the COVID-19 pandemic, including on our
credit quality and business operations, as well as its impact
on general economic and financial market conditions;
• our capital and liquidity requirements (including under
regulatory capital standards, such as the Basel III capital
standards) and our ability to generate capital internally or
raise capital on favorable terms;
• current, pending or future legislation or regulation that
could have a negative effect on our revenue and businesses,
including rules and regulations relating to bank products and
financial services;
• developments in our mortgage banking business, including
the extent of the success of our mortgage loan modification
efforts, the amount of mortgage loan repurchase demands
that we receive, any negative effects relating to our
mortgage servicing, loan modification or foreclosure
practices, and the effects of regulatory or judicial
requirements or guidance impacting our mortgage banking
business and any changes in industry standards or our
strategic plans for the business;
• our ability to realize any efficiency ratio or expense target a s
part of our expense management initiatives, including as a
result of business and economic cyclicality, seasonality,
changes in our business composition and operating
environment, growth in our businesses and/or acquisitions,
and unexpected expenses relating to, among other things,
litigation and regulatory matters;
• the effect of the current interest rate environment or
changes in interest rates or in the level or composition of ou r
assets or liabilities on our net interest income, net interest
margin and our mortgage originations, mortgage servicing
rights and mortgage loans held for sale;
• significant turbulence or a disruption in the capital or
financial markets, which could result in, among other things,
reduced investor demand for mortgage loans, a reduction in
the availability of funding or increased funding costs, and
declines in asset values and/or recognition of impairments of
securities held in our debt securities and equity securities
portfolios;
• the effect of a fall in stock market prices on our investment
banking business and our fee income from our brokerage
and wealth management businesses;
• negative effects from the retail banking sales practices
matter and from instances where customers may have
experienced financial harm, including on our legal,
operational and compliance costs, our ability to engage in
certain business activities or offer certain products or
services, our ability to keep and attract customers, our
ability to attract and retain qualified employees, and our
reputation;
• resolution of regulatory matters, litigation, or other legal
actions, which may result in, among other things, additional
costs, fines, penalties, restrictions on our business activitie s,
reputational harm, or other adverse consequences;
• a failure in or breach of our operational or security systems
or infrastructure, or those of our third-party vendors or
other service providers, including as a result of cyber attacks ;
• the effect of changes in the level of checking or savings
account deposits on our funding costs and net interest
margin;
• fiscal and monetary policies of the Federal Reserve Board;
• changes to U.S. tax guidance and regulations as well as the
effect of discrete items on our effective income tax rate;
• our ability to develop and execute effective business plans
and strategies; and
• the other risk factors and uncertainties described under
“Risk Factors” in this Report.
Wells Fargo & Company 67

Forward-Looking Statements (continued)
In addition to the above factors, we also caution that the
amount and timing of any future common stock dividends or
repurchases will depend on the earnings, cash requirements and
financial condition of the Company, market conditions, capital
requirements (including under Basel capital standards), common
stock issuance requirements, applicable law and regulations
(including federal securities laws and federal banking
regulations), and other factors deemed relevant by the Company,
and may be subject to regulatory approval or conditions.
For additional information about factors that could cause
actual results to differ materially from our expectations, refe r to
our reports filed with the Securities and Exchange Commission,
including the discussion under “Risk Factors” in this Report, a s
filed with the Securities and Exchange Commission and availabl e
on its website at www.sec.gov.
1
Any forward-looking statement made by us speaks only as
of the date on which it is made. Factors or events that could
cause our actual results to differ may emerge from time to time,
and it is not possible for us to predict all of them. We undertake
no obligation to publicly update any forward-looking statement,
whether as a result of new information, future developments or
otherwise, except as may be required by law.
Forward-looking Non-GAAP Financial Measures . From time to
time management may discuss forward-looking non-GAAP
financial measures, such as forward-looking estimates or target s
for return on average tangible common equity. We are unable to
provide a reconciliation of forward-looking non-GAAP financial
measures to their most directly comparable GAAP financial
measures because we are unable to provide, without
unreasonable effort, a meaningful or accurate calculation or
estimation of amounts that would be necessary for the
reconciliation due to the complexity and inherent difficulty i n
forecasting and quantifying future amounts or when they may
occur. Such unavailable information could be significant to fut ure
results.
1
We do not control this website. Wells Fargo has provided this link for
your convenience, but does not endorse and is not responsible for the
content, links, privacy policy, or security policy of this website.
Wells Fargo & Company 68

Risk Factors
An investment in the Company involves risk, including the
possibility that the value of the investment could fall
substantially and that dividends or other distributions on the
investment could be reduced or eliminated. We discuss below
risk factors that could adversely affect our financial results and
condition, and the value of, and return on, an investment in the
Company.
ECONOMIC, FINANCIAL MARKETS, INTEREST RATES, AND
LIQUIDITY RISKS
Our financial results have been, and will continue to be,
materially affected by general economic conditions, and a
deterioration in economic conditions or in the financial
markets may materially adversely affect our lending and other
businesses and our financial results and condition. We
generate revenue from the interest and fees we charge on the
loans and other products and services we sell, and a substantia l
amount of our revenue and earnings comes from the net interest
income and fee income that we earn from our consumer and
commercial lending and banking businesses. These businesses
have been, and will continue to be, materially affected by the
state of the U.S. economy, particularly unemployment levels an d
home prices. The negative effects and continued uncertainty
stemming from U.S. fiscal, monetary and political matters,
including concerns about deficit and debt levels, inflation, ta xes
and U.S. debt ratings, have impacted and may continue to impac t
the global economy. Moreover, geopolitical matters, including
international political unrest or disturbances, such as the con flict
in Ukraine, as well as continued concerns over commodity prices ,
restrictions on international trade and corresponding retaliato ry
measures, and global economic difficulties, may impact the
stability of financial markets and the global economy. Any
impacts to the global economy could have a similar impact to th e
U.S. economy. A prolonged period of slow growth in the global
economy or any deterioration in general economic conditions
and/or the financial markets resulting from the above matters o r
any other events or factors that may disrupt or weaken the U.S .
or global economy , could materially adversely affect our
financial results and condition.
A weakening in business or economic conditions, including
higher unemployment levels or declines in home prices, as well as
higher interest rates, can also adversely affect our customers’
ability to repay their loans or other obligations, which can
negatively impact our credit performance. If unemployment
levels worsen or if home prices fall we would expect to incur
elevated charge-offs and provision expense from increases in our
allowance for credit losses. These conditions may adversely
affect not only consumer loan performance but also commercial
and CRE loans, especially for those business borrowers that rely
on the health of industries that may experience deteriorating
economic conditions. The ability of these and other borrowers to
repay their loans may deteriorate, causing us, as one of the
largest commercial and CRE lenders in the U.S., to incur
significantly higher credit losses. In addition, weak or
deteriorating economic conditions make it more challenging for
us to increase our consumer and commercial loan portfolios by
making loans to creditworthy borrowers at attractive yields.
Furthermore, weak economic conditions, as well as competition
and/or increases in interest rates, could soften demand for our
loans resulting in our retaining a much higher amount of lower
yielding liquid assets on our consolidated balance sheet. If
economic conditions do not continue to improve or if the
economy worsens and unemployment rises, which also would
likely result in a decrease in consumer and business confidence
and spending, the demand for our products, including our
consumer and commercial loans, may fall, reducing our interest
and noninterest income and our earnings.
A deterioration in business and economic conditions, which
may erode consumer and investor confidence levels, and/or
increased volatility of financial markets, also could adversely
affect financial results for our fee-based businesses, including our
investment advisory, securities brokerage, wealth management,
markets and investment banking businesses. For example,
because investment advisory fees are often based on the value of
assets under management, a fall in the market prices of those
assets could reduce our fee income. Changes in stock market
prices could affect the trading activity of investors, reducing
commissions and other fees we earn from our brokerage
business. In addition, adverse market conditions may negatively
affect the performance of products we have provided to
customers, which may expose us to legal actions or additional
costs. Poor economic conditions and volatile or unstable financial
markets also can negatively affect our debt and equity
underwriting and advisory businesses, as well as our venture
capital business and trading activities, including through
heightened counterparty credit risk. Any deterioration in global
financial markets and economies, including as a result of any
international political unrest or disturbances, may adversely
affect the revenue and earnings of our international operations,
particularly our global financial institution and correspondent
banking services.
For additional information, see the “Risk Management –
Asset/Liability Management” and “– Credit Risk Management”
sections in this Report.
The COVID-19 pandemic has adversely impacted our business
and financial results and any further impact will depend on
future developments, which are highly uncertain and cannot be
predicted. The COVID-19 pandemic has negatively impacted the
global economy; disrupted global supply chains; affected equity
market valuations; and created significant volatility and
disruption in financial markets and unemployment levels. As a
result of the pandemic, the demand for our products and services
has, at times, been significantly impacted, which adversely
affected our revenue. The pandemic also resulted in the
recognition of credit losses in our loan portfolios and increases in
our allowance for credit losses, particularly for industries most
directly and adversely affected by the pandemic, such as travel
and entertainment.
Moreover, the pandemic created additional operational and
compliance risks, including the need to quickly implement and
execute new pandemic-related programs and procedures,
comply with rapidly changing regulatory requirements, address
any increased risk of fraudulent activity, and protect the integrity
and functionality of our systems, networks, and operations while
a larger number of our employees and those of our third-party
service providers may spend more time working remotely than
prior to the pandemic. In response to the pandemic, we
previously suspended certain mortgage foreclosure activities and
provided fee waivers, payment deferrals, and other assistance for
certain consumer and commercial lending customers.
Furthermore, our participation in governmental measures taken
to address the economic impact from the pandemic could
Wells Fargo & Company 69
Risk Factors (continued)
continue to result in litigation and government investigations
and proceedings. In addition, we previously reduced our common
stock dividend and temporarily suspended share repurchases.
The pandemic also increased the likelihood and/or magnitude of
the other risks described herein, including credit, market and
operational related risks.
The extent to which the COVID-19 pandemic further
impacts our business, results of operations, and financial
condition, as well as our regulatory capital and liquidity ratios,
depends on future developments, which are highly uncertain and
cannot be predicted, including the scope and duration of the
pandemic and actions taken by governmental authorities and
other third parties in response to the pandemic. Depending on
future developments, the COVID-19 pandemic or any new
pandemic could result in the occurrence of new, unanticipated
adverse effects on us or the recurrence of adverse effects similar
to those already experienced.
Changes in interest rates and financial market values could
reduce our net interest income and earnings, as well as our
other comprehensive income, including as a result of
recognizing losses on the debt and equity securities that we
hold in our portfolio or trade for our customers. Changes in
either our net interest margin or the amount or mix of earning
assets we hold, including as a result of the asset cap under the
February 2018 consent order with the FRB, could affect our net
interest income and our earnings. Changes in interest rates can
affect our net interest margin. Although the yield we earn on our
assets and our funding costs tend to move in the same direction
in response to changes in interest rates, one can rise or fall faster
than the other, causing our net interest margin to expand or
contract. If our funding costs rise faster than the yield we earn on
our assets or if the yield we earn on our assets falls faster than
our funding costs, our net interest margin could contract.
The amount and type of earning assets we hold can affect
our yield and net interest income. We hold earning assets in the
form of loans and debt and equity securities, among other assets.
As noted above, if the economy worsens we may see lower
demand for loans by creditworthy customers, reducing our yield
and net interest income. In addition, our net interest income and
net interest margin can be negatively affected by a prolonged
period of low interest rates as it may result in us holding lower
yielding loans and securities on our consolidated balance sheet,
particularly if we are unable to replace the maturing higher
yielding assets with similar higher yielding assets. Increases in
interest rates, however, may continue to negatively affect loan
demand and could result in higher credit losses as borrowers may
have more difficulty making higher interest payments. As
described below, changes in interest rates also affect our
mortgage business, including the value of our MSRs. In an effort
to address high inflation, the FRB significantly raised its target
range for the federal funds rate and has indicated it may continue
to raise it in 2023.
Changes in the slope of the yield curve – or the spread
between short-term and long-term interest rates – could also
reduce our net interest income and net interest margin.
Normally, the yield curve is upward sloping, meaning short-term
rates are lower than long-term rates. When the yield curve
flattens or inverts, our net interest income and net interest
margin could decrease if the cost of our short-term funding
increases relative to the yield we can earn on our long-term
assets. Moreover, a negative interest rate environment, in which
interest rates drop below zero, could reduce our net interest
income and net interest margin due to a likely decline in the
interest we could earn on loans and other earning assets, while
also likely requiring us to pay to maintain our deposits with
the FRB.
We assess our interest rate risk by estimating the effect on
our earnings under various scenarios that differ based on
assumptions about the direction, magnitude and speed of
interest rate changes and the slope of the yield curve. We may
hedge some of that interest rate risk with interest rate
derivatives. We also rely on the “natural hedge” that our
mortgage loan originations and servicing rights can provide as
their revenue impact tends to move in opposite directions based
on changes in interest rates.
We generally do not hedge all of our interest rate risk. There
is always the risk that changes in interest rates, credit spreads or
option volatility could reduce our net interest income and
earnings, as well as our other comprehensive income, in material
amounts, especially if actual conditions turn out to be materially
different than what we assumed. For example, if interest rates
rise or fall faster than we assumed or the slope of the yield curve
changes, we may incur significant losses on debt securities we
hold as investments. To reduce our interest rate risk, we may
rebalance our portfolios of debt securities, equity securities and
loans, refinance our debt and take other strategic actions. We
may incur losses when we take such actions. In addition, changes
in interest rates can result in increased basis risk, which could
limit the effectiveness of our hedging activities.
Because of changing economic and market conditions, as
well as credit ratings, affecting issuers and the performance o f
any underlying collateral, we may be required to recognize othe r-
than-temporary impairment (OTTI) in future periods on the
securities we hold. Furthermore, the value of the debt securiti es
we hold can fluctuate due to changes in interest rates, issuer
creditworthiness, and other factors. Our net income also is
exposed to changes in interest rates, credit spreads, foreign
exchange rates, and equity and commodity prices in connection
with our trading activities, which are conducted primarily to
accommodate the investment and risk management activities of
our customers, as well as when we execute economic hedging to
manage certain balance sheet risks. Trading debt securities an d
equity securities held for trading are carried at fair value wi th
realized and unrealized gains and losses recorded in noninteres t
income. As part of our business to support our customers, we
trade public debt and equity securities and other financial
instruments that are subject to market fluctuations with gains
and losses recognized in net income. In addition, although hig h
market volatility can increase our exposure to trading-related
losses, periods of low volatility may have an adverse effect o n our
businesses as a result of reduced customer activity levels.
Although we have processes in place to measure and monitor the
risks associated with our trading activities, including stress
testing and hedging strategies, there can be no assurance that
our processes and strategies will be effective in avoiding loss es
that could have a material adverse effect on our financial resu lts.
The value of our marketable and nonmarketable equity
securities can fluctuate from quarter to quarter. Marketable
equity securities are carried at fair value with unrealized gains and
losses reflected in earnings. Nonmarketable equity securities are
carried under the cost method, equity method, or measurement
alternative, while others are carried at fair value with unrealized
gains and losses reflected in earnings. Earnings from our equity
securities portfolio may be volatile and hard to predict, and may
have a significant effect on our earnings from period to period.
When, and if, we recognize gains may depend on a number of
factors, including general economic and market conditions, the
prospects of the companies in which we invest, when a company
Wells Fargo & Company 70
goes public, the size of our position relative to the public float,
and whether we are subject to any resale restrictions.
Nonmarketable equity securities include our private equity
and venture capital investments that could result in significant
OTTI losses for those investments carried under the
measurement alternative or equity method. If we determine
there is OTTI for an investment, we write-down the carrying
value of the investment, resulting in a charge to earnings, which
could be significant.
For additional information, see the “Risk Management –
Asset/Liability Management – Interest Rate Risk”, “– Mortgage
Banking Interest Rate and Market Risk”, “– Market Risk – Trading
Activities”, and “– Market Risk – Equity Securities” and the
“Balance Sheet Analysis – Available-for-Sale and Held-to-
Maturity Debt Securities” sections in this Report and Note 2
(Trading Activities), Note 3 (Available-for-Sale and Held-to-
Maturity Debt Securities) and Note 4 (Equity Securities) to
Financial Statements in this Report.
The transition away from the London Interbank Offered Rate
(LIBOR) may adversely affect our business, results of
operations, and financial condition. The administrator of LIBOR
ceased publication of LIBOR settings on a representative basis on
December 31, 2021, with the exception of the most commonly
used U.S. dollar (USD) LIBOR settings, which will no longer be
published on a representative basis after June 30, 2023.
Additionally, federal banking regulators issued guidance strongly
encouraging banking organizations to cease using USD LIBOR in
new contracts. We have a significant number of assets and
liabilities, such as legacy commercial loans, adjustable-rate
mortgage loans, derivatives, debt securities, and long-term debt,
referenced to LIBOR and other interbank offered rates. When
any such benchmark rate or other referenced financial metric is
significantly changed, replaced or discontinued, or ceases to be
recognized as an acceptable market benchmark rate or financial
metric, there may be uncertainty or differences in the calculation
of the applicable interest rate or payment amount depending on
the terms of the governing instrument.
This could impact the financial performance of previously
booked transactions, result in losses on financial instruments we
hold, require different hedging strategies or result in ineffective
or increased basis risk on existing hedges, impact the overall
interest rate environment and the availability or cost of floating-
rate funding, affect our capital and liquidity planning and
management, or have other adverse financial consequences.
There can be no assurance that any new benchmark rate, such as
the Secured Overnight Financing Rate (SOFR), or other financial
metric will be an adequate alternative to LIBOR or produce the
economic equivalent of LIBOR. In addition, the transition away
from LIBOR will continue to require changes to existing
transaction data, products, systems, models, operations, and
pricing processes, as well as the modification or renegotiation of
contracts that reference USD LIBOR. It may also continue to
result in significant operational, systems, or other practical
challenges, increased compliance and operational costs, and
heightened expectations and scrutiny from regulators, and could
result in litigation, reputational harm, or other adverse
consequences. Furthermore, the transition away from widely
used benchmark rates like LIBOR could result in customers or
other market participants challenging the determination of their
interest payments, disputing the interpretation or
implementation of fallback provisions and other transition
related changes, or entering into fewer transactions or
postponing their financing needs, which could reduce our
revenue and adversely affect our business. Moreover, to the
extent borrowers with loans referenced to LIBOR, such as
adjustable-rate mortgage loans, experience higher interest
payments as a result of the transition to a new benchmark rate,
our customers’ ability to repay their loans may be adversely
affected, which can negatively impact our credit performance.
For additional information on the discontinuation of LIBOR
and the steps we are taking to address and mitigate the risks we
have identified, see the “Overview – Recent Developments –
LIBOR Transition” section in this Report.
Effective liquidity management is essential for the operation
of our business, and our financial results and condition could be
materially adversely affected if we do not effectively manage
our liquidity. We primarily rely on customer deposits to be a
low-cost and stable source of funding for the loans we make and
the operation of our business. In addition to customer deposits,
our sources of liquidity include certain debt and equity securities,
our ability to sell or securitize loans in secondary markets and to
pledge loans to access secured borrowing facilities through the
FHLB and the FRB, and our ability to raise funds in domestic and
international money through capital markets.
Our liquidity and our ability to fund and run our business
could be materially adversely affected by a variety of conditions
and factors, including financial and credit market disruption and
volatility or a lack of market or customer confidence in financial
markets in general similar to what occurred during the financial
crisis in 2008 and early 2009, which may result in a loss of
customer deposits or outflows of cash or collateral and/or our
inability to access capital markets on favorable terms. Market
disruption and volatility could impact our credit spreads, which
are the amount in excess of the interest rate of U.S. Treasury
securities, or other benchmark securities, of the same maturity
that we need to pay to our funding providers. Increases in
interest rates and our credit spreads could significantly increase
our funding costs. Other conditions and factors that could
materially adversely affect our liquidity and funding include a lack
of market or customer confidence in the Company or negative
news about the Company or the financial services industry
generally which also may result in a loss of deposits and/or
negatively affect our ability to access the capital markets; our
inability to sell or securitize loans or other assets; disruptions or
volatility in the repurchase market which also may increase our
short-term funding costs; regulatory requirements or
restrictions; unexpectedly high or accelerated customer draws on
lines of credit; and, as described below, reductions in one or more
of our credit ratings. Many of the above conditions and factors
may be caused by events over which we have little or no control.
There can be no assurance that significant disruption and
volatility in the financial markets will not occur in the future. For
example, concerns over geopolitical issues, commodity and
currency prices, as well as global economic conditions, may cause
financial market volatility.
In addition, concerns regarding U.S. government debt levels,
including any potential failure to raise the debt limit, and any
associated downgrade of U.S. government debt ratings may
cause uncertainty and volatility as well. A downgrade of the
sovereign debt ratings of the U.S. government or the debt
ratings of related institutions, agencies or instrumentalities, as
well as other fiscal or political events could, in addition to causing
economic and financial market disruptions, materially adversely
affect the market value of the U.S. government securities that
we hold, the availability of those securities as collateral for
borrowing, and our ability to access capital markets on favorable
terms, as well as have other material adverse effects on the
operation of our business and our financial results and condition.
Wells Fargo & Company 71
Risk Factors (continued)
As noted above, we rely heavily on customer deposits for our
funding and liquidity. We compete with banks and other financial
services companies for deposits. If our competitors raise the
rates they pay on deposits our funding costs may increase, either
because we raise our rates to avoid losing deposits or because we
lose deposits and must rely on more expensive sources of
funding. Checking and savings account balances and other forms
of customer deposits may decrease when customers perceive
other investment opportunities, such as stocks, bonds, or money
market mutual funds, as providing a better risk/return tradeoff.
When customers move money out of bank deposits and into
other investments, we may lose a relatively low-cost source of
funds, increasing our funding costs and negatively affecting our
liquidity. In addition, we may continue to reduce certain deposit
balances in order to manage under the asset cap.
If we are unable to continue to fund our assets through
customer deposits or access capital markets on favorable terms
or if we suffer an increase in our borrowing costs or otherwis e fail
to manage our liquidity effectively (including on an intra-day or
intra-affiliate basis), our liquidity, net interest margin, fin ancial
results and condition may be materially adversely affected. As we
did during the financial crisis, we may also need, or be requir ed by
our regulators, to raise additional capital through the issuanc e of
common stock, which could dilute the ownership of existing
stockholders, or reduce or even eliminate our common stock
dividend to preserve capital or to raise additional capital.
For additional information, see the “Risk Management –
Asset/Liability Management” section in this Report.
Adverse changes in our credit ratings could have a material
adverse effect on our liquidity, cash flows, financial results and
condition. Our borrowing costs and ability to obtain funding are
influenced by our credit ratings. Reductions in one or more of our
credit ratings could adversely affect our ability to borrow funds
and raise the costs of our borrowings substantially and could
cause creditors and business counterparties to raise collateral
requirements or take other actions that could adversely affect
our ability to raise funding. Credit ratings and credit ratings
agencies’ outlooks are based on the ratings agencies’ analysis of
many quantitative and qualitative factors, such as our capital
adequacy, liquidity, asset quality, business mix, the level and
quality of our earnings, rating agency assumptions regarding the
probability and extent of federal financial assistance or support,
and other rating agency specific criteria. In addition to credit
ratings, our borrowing costs are affected by various other
external factors, including market volatility and concerns or
perceptions about the financial services industry generally. There
can be no assurance that we will maintain our credit ratings and
outlooks and that credit ratings downgrades in the future would
not materially affect our ability to borrow funds and borrowing
costs. Downgrades in our credit ratings also may trigger
additional collateral or funding obligations which, depending on
the severity of the downgrade, could have a material adverse
effect on our liquidity, including as a result of credit-related
contingent features in certain of our derivative contracts.
For information on our credit ratings, see the “Risk
Management – Asset/Liability Management – Liquidity Risk and
Funding – Credit Ratings” section and for information regarding
additional collateral and funding obligations required of certain
derivative instruments in the event our credit ratings were to fall
below investment grade, see Note 14 (Derivatives) to Financial
Statements in this Report.
We rely on dividends from our subsidiaries for liquidity, and
federal and state law, as well as certain contractual
arrangements, can limit those dividends. Wells Fargo &
Company, the parent holding company (the “Parent”), is a
separate and distinct legal entity from its subsidiaries. It receives
substantially all of its funding and liquidity from dividends and
other distributions from its subsidiaries. We generally use these
dividends and distributions, among other things, to pay dividends
on our common and preferred stock and interest and principal on
our debt. Federal and state laws limit the amount of dividends
and distributions that our bank and some of our nonbank
subsidiaries, including our broker-dealer subsidiaries, may pay to
the Parent. In addition, under a Support Agreement dated
June 28, 2017, as amended and restated on June 26, 2019,
among the Parent, WFC Holdings, LLC, an intermediate holding
company and subsidiary of the Parent (the “IHC”), Wells Fargo
Bank, N.A. (the “Bank”), Wells Fargo Securities, LLC, Wells Fargo
Clearing Services, LLC, and certain other subsidiaries of the
Parent designated from time to time as material entities for
resolution planning purposes or identified from time to time as
related support entities in our resolution plan, the IHC may be
restricted from making dividend payments to the Parent if
certain liquidity and/or capital metrics fall below defined triggers
or if the Parent’s board of directors authorizes it to file a case
under the U.S. Bankruptcy Code. Also, our right to participate in a
distribution of assets upon a subsidiary’s liquidation or
reorganization is subject to the prior claims of the subsidiary’s
creditors.
For additional information, see the “Regulation and
Supervision – Dividend Restrictions” and “– Holding Company
Structure” sections in our 2022 Form 10-K and to Note 25
(Regulatory Capital Requirements and Other Restrictions) to
Financial Statements in this Report.
REGULATORY RISKS
Current and future legislation and/or regulation could require
us to change certain of our business practices, reduce our
revenue and earnings, impose additional costs on us or
otherwise adversely affect our business operations and/or
competitive position. Our parent company, our subsidiary
banks and many of our nonbank subsidiaries such as those
related to our brokerage business, are subject to significant and
extensive regulation under state and federal laws in the U.S., as
well as the applicable laws of the various jurisdictions outside of
the U.S. where they conduct business. These regulations
generally protect depositors, federal deposit insurance funds,
consumers, investors, employees, or the banking and financial
system as a whole, not necessarily our security holders.
Economic, market and political conditions during the past few
years have led to a significant amount of legislation and
regulation in the U.S. and abroad affecting the financial services
industry, as well as heightened expectations and scrutiny of
financial services companies from banking regulators. These laws
and regulations may continue to affect the manner in which we
do business and the products and services that we provide, affect
or restrict our ability to compete in our current businesses or our
ability to enter into or acquire new businesses, reduce or limit our
revenue, affect our compliance and risk management activities,
increase our capital requirements, impose additional fees,
assessments or taxes on us, intensify the regulatory supervision
of us and the financial services industry, and adversely affect our
business operations or have other negative consequences. Our
businesses and revenue in non-U.S. jurisdictions are also subject
to risks from political, economic and social developments in
Wells Fargo & Company 72
those jurisdictions, including sanctions or business restrictions,
asset freezes or confiscation, unfavorable political or diplomatic
developments, or financial or social instability. In addition,
greater government oversight and scrutiny of Wells Fargo, as
well as financial services companies generally, has increased our
operational and compliance costs as we must continue to devote
substantial resources to enhancing our procedures and controls
and meeting heightened regulatory standards and expectations.
Any failure to meet regulatory requirements, standards or
expectations, either in the U.S. or in non-U.S. jurisdictions, could
continue to result in significant fees, penalties, restrictions on our
ability to engage in certain business activities, or other adverse
consequences.
Our consumer businesses, including our mortgage, auto,
credit card and other consumer lending and non-lending
businesses, are subject to numerous and, in many cases, highly
complex consumer protection laws and regulations, as well as
enhanced regulatory scrutiny and more and expanded regulatory
examinations and/or investigations. In particular, the CFPB’s
rules may continue to increase our compliance costs and require
changes in our business practices, which could limit or negatively
affect the products and services that we offer our customers. If
we fail to meet enhanced regulatory requirements and
expectations with respect to our consumer businesses, we may
be subject to increased costs, fines, penalties, restrictions on our
business activities including the products and services we can
provide, and/or harm to our reputation.
In addition, the Dodd-Frank Act established a
comprehensive framework for regulating over-the-counter
derivatives, and the CFTC, SEC, and other federal regulatory
agencies have adopted rules regulating swaps, security-based
swaps, and derivatives activities. These rules may continue to
negatively impact customer demand for over-the-counter
derivatives, impact our ability to offer customers new derivatives
or amendments to existing derivatives, and increase our costs for
engaging in swaps, security-based swaps, and other derivatives
activities.
We are also subject to various rules and regulations related
to the prevention of financial crimes and combating terrorism,
including the USA PATRIOT Act of 2001. These rules and
regulations require us to, among other things, implement policies
and procedures related to anti-money laundering, anti-bribery
and corruption, economic sanctions, suspicious activities,
currency transaction reporting and due diligence on customers.
Although we have policies and procedures designed to comply
with these rules and regulations, to the extent they are not fully
effective or do not meet heightened regulatory standards or
expectations, we may be subject to fines, penalties, restrictions
on certain activities, reputational harm, or other adverse
consequences.
Our businesses are also subject to laws and regulations
enacted by U.S. and non-U.S. regulators and governmental
authorities relating to the privacy of the information of
customers, employees and others. These laws and regulations,
among other things, increase our compliance obligations; have a
significant impact on our businesses’ collection, processing,
sharing, use, and retention of personal data and reporting of data
breaches; and provide for significantly increased penalties for
non-compliance.
In addition, we are subject to a number of consent orders
and other regulatory actions, including a February 2018 consent
order with the FRB regarding the Board’s governance and
oversight of the Company, and the Company’s compliance and
operational risk management program. This consent order limits
the Company’s total consolidated assets as defined under the
consent order to the level as of December 31, 2017, until certain
conditions are met. This limitation could continue to adversely
affect our results of operations or financial condition. We are also
subject to April 2018 consent orders with the CFPB and OCC
regarding the Company’s compliance risk management program
and past practices involving certain automobile collateral
protection insurance policies and certain mortgage interest rate
lock extensions. In addition, we are subject to a September 2021
consent order with the OCC regarding loss mitigation activities in
the Company’s Home Lending business. Similarly, we are subject
to a December 2022 consent order with the CFPB regarding
multiple matters related to automobile lending, consumer
deposit accounts, and mortgage lending.
Under the April 2018 consent order with the OCC, the Bank
remains subject to requirements that were originally imposed in
November 2016 to provide prior written notice to, and obtain
non-objection from, the OCC with respect to changes in directors
and senior executive officers, and remains subject to certain
regulatory limitations on post-termination payments to certain
individuals and employees.
The Company may be subject to further actions, including
the imposition of additional consent orders, regulatory
agreements or civil money penalties, by federal regulators
regarding similar or other issues. Furthermore, issues or delays in
satisfying the requirements of a regulatory action could affect
our progress on others, and failure to satisfy the requirements of
a regulatory action on a timely basis could result in additional
penalties, enforcement actions, and other negative
consequences, which could be significant. For example, in
September 2021, the OCC assessed a $250 million civil money
penalty against the Company related to insufficient progress in
addressing requirements under the OCC’s April 2018 consent
order and loss mitigation activities in the Company’s Home
Lending business. Compliance with the February 2018 FRB
consent order, the April 2018 CFPB and OCC consent orders, the
September 2021 OCC consent order, the December 2022 CFPB
consent order, and any other consent orders or regulatory
actions, as well as the implementation of their requirements, may
continue to increase the Company’s costs, require the Company
to reallocate resources away from growing its existing
businesses, subject the Company to business restrictions,
negatively impact the Company’s capital and liquidity, and
require the Company to undergo significant changes to its
business, operations, products and services, and risk
management practices. For additional information on the
Company’s consent orders, see the “Overview” section in this
Report.
Other future regulatory initiatives that could significantly
affect our business include proposals to reform the housing
finance market in the United States. These proposals, among
other things, consider ending the conservatorships of the GSEs
and reducing or eliminating over time the role of the GSEs in
buying mortgage loans or guaranteeing mortgage-backed
securities (MBS), as well as the implementation of reforms
relating to borrowers, lenders, and investors in the mortgage
market. The extent and timing of any regulatory reform or the
adoption of any legislation regarding the GSEs and/or the home
mortgage market, as well as any effect on the Company’s
business and financial results, are uncertain.
Any other future legislation and/or regulation, if adopted,
also could significantly change our regulatory environment and
increase our cost of doing business, limit the activities we may
pursue or affect the competitive balance among banks, savings
associations, credit unions, and other financial services
Wells Fargo & Company 73
Risk Factors (continued)
companies, and have a material adverse effect on our financial
results and condition.
For additional information on the significant regulations and
regulatory oversight initiatives that have affected or may affect
our business, see the “Regulatory Matters” section in this Report
and the “Regulation and Supervision” section in our 2022 Form
10-K.
We could be subject to more stringent capital, leverage or
liquidity requirements or restrictions on our growth, activities
or operations if regulators determine that our resolution or
recovery plan is deficient. Pursuant to rules adopted by the FRB
and the FDIC, Wells Fargo prepares and periodically submits
resolution plans, also known as “living wills,” designed to facilitate
our rapid and orderly resolution in the event of material financial
distress or failure. There can be no assurance that the FRB or
FDIC will respond favorably to the Company’s resolution plans.
If the FRB and/or FDIC determine that a resolution plan has
deficiencies, they may impose more stringent capital, leverage or
liquidity requirements on us or restrict our growth, activities or
operations until we adequately remedy the deficiencies. If the
FRB and/or FDIC ultimately determine that we have been unable
to remedy any deficiencies, they could require us to divest certain
assets or operations.
In addition to our resolution plans, we must also prepare and
periodically submit to the FRB a recovery plan that identifies a
range of options that we may consider during times of
idiosyncratic or systemic economic stress to remedy any
financial weaknesses and restore market confidence without
extraordinary government support. The Bank must also prepare
and periodically submit to the OCC a recovery plan. If either the
FRB or the OCC determines that our recovery plan is deficient,
they may impose fines, restrictions on our business or ultimately
require us to divest assets.
Our security holders may suffer losses in a resolution of
Wells Fargo even if creditors of our subsidiaries are paid in full.
If Wells Fargo were to fail, it may be resolved in a bankruptcy
proceeding or, if certain conditions are met, under the resolution
regime created by the Dodd-Frank Act known as the “orderly
liquidation authority,” which allows for the appointment of the
FDIC as receiver. The FDIC’s orderly liquidation authority requires
that security holders of a company in receivership bear all losses
before U.S. taxpayers are exposed to any losses. There are
substantial differences in the rights of creditors between the
orderly liquidation authority and the U.S. Bankruptcy Code,
including the right of the FDIC to disregard the strict priority of
creditor claims under the U.S. Bankruptcy Code in certain
circumstances and the use of an administrative claims procedure
instead of a judicial procedure to determine creditors’ claims.
The strategy described in our most recent resolution plan is
a single point of entry strategy, in which the Parent would be the
only material legal entity to enter resolution proceedings.
However, the strategy described in our resolution plan is not
binding in the event of an actual resolution of Wells Fargo.
To facilitate the orderly resolution of the Company, we
entered into the Support Agreement, pursuant to which the
Parent transferred a significant amount of its assets to the IHC
and will continue to transfer assets to the IHC from time to time.
In the event of our material financial distress or failure, the IHC
will be obligated to use the transferred assets to provide capital
and/or liquidity to the Bank and certain other direct and indirect
subsidiaries of the Parent. Under the Support Agreement, the
IHC will provide funding and liquidity to the Parent through
subordinated notes and a committed line of credit. If certain
liquidity and/or capital metrics fall below defined triggers, or if
the Parent’s board of directors authorizes it to file a case under
the U.S. Bankruptcy Code, the subordinated notes would be
forgiven, the committed line of credit would terminate, and the
IHC’s ability to pay dividends to the Parent would be restricted,
any of which could materially and adversely impact the Parent’s
liquidity and its ability to satisfy its debts and other obligations,
and could result in the commencement of bankruptcy
proceedings by the Parent at an earlier time than might have
otherwise occurred if the Support Agreement were not
implemented.
Any resolution of the Company will likely impose losses on
shareholders, unsecured debt holders and other creditors of th e
Parent, while the Parent’s subsidiaries may continue to operate .
Creditors of some or all of our subsidiaries may receive
significant or full recoveries on their claims, while the Paren t’s
security holders could face significant or complete losses. Thi s
outcome may arise whether the Company is resolved under the
U.S. Bankruptcy Code or by the FDIC under the orderly
liquidation authority, and whether the resolution is conducted
using a single point of entry strategy or using a multiple poin t of
entry strategy, in which the Parent and one or more of its
subsidiaries would each undergo separate resolution
proceedings. Furthermore, in a single point of entry or multipl e
point of entry strategy, losses at some or all of our subsidiar ies
could be transferred to the Parent and borne by the Parent’s
security holders. Moreover, if either resolution strategy prove d
to be unsuccessful, our security holders could face greater los ses
than if the strategy had not been implemented.
For additional information, see the “Regulatory Matters –
‘Living Will’ Requirements and Related Matters” section in this
Report.
Bank regulations and rules may require higher capital and
liquidity levels, limiting our ability to pay common stock
dividends, repurchase our common stock, invest in our
business, or provide loans or other products and services to our
customers. The Company and each of our insured depository
institutions are subject to various regulatory capital adequacy
requirements administered by federal banking regulators. In
particular, the Company is subject to rules issued by federal
banking regulators to implement Basel III risk-based capital
requirements for U.S. banking organizations. These capital rules,
among other things, establish required minimum ratios relating
capital to different categories of assets and exposures. Federal
banking regulators have also imposed a leverage ratio and a
supplementary leverage ratio on large BHCs like Wells Fargo and
our insured depository institutions. The FRB has also finalized
rules to address the amount of equity and unsecured long-term
debt a U.S. G-SIB must hold to improve its resolvability and
resiliency, often referred to as total loss absorbing capacity
(TLAC). Similarly, federal banking regulators have issued final
rules that implement a liquidity coverage ratio and a net stable
funding ratio.
In addition, as part of its obligation to impose enhanced
capital and risk-management standards on large financial firms
pursuant to the Dodd-Frank Act, the FRB has issued a capital
plan rule that establishes capital planning and other
requirements that govern capital distributions, including
dividends and share repurchases, by certain BHCs, including
Wells Fargo. The FRB has also finalized a number of regulations
implementing enhanced prudential requirements for large BHCs
like Wells Fargo regarding risk-based capital and leverage, risk
and liquidity management, single counterparty credit limits, and
Wells Fargo & Company 74
imposing debt-to-equity limits on any BHC that regulators
determine poses a grave threat to the financial stability of the
United States. The FRB and OCC have also finalized rules
implementing stress testing requirements for large BHCs and
national banks. In addition, the FRB has proposed a rule to
establish remediation requirements for large BHCs experiencing
financial distress and has proposed additional requirements
regarding effective risk management practices at large BHCs,
including its expectations for boards of directors and senior
management. The OCC, under separate authority, has also
established heightened governance and risk management
standards for large national banks, such as the Bank.
The Basel standards and federal regulatory capital, leverage,
liquidity, TLAC, capital planning, and other requirements may
limit or otherwise restrict how we utilize our capital, including
common stock dividends and stock repurchases, and may require
us to increase our capital and/or liquidity. Any requirement that
we increase our regulatory capital, regulatory capital ratios or
liquidity, including due to changes in regulatory requirements,
such as through the adoption or implementation of new or
revised Basel standards, or as a result of business growth,
acquisitions or a change in our risk profile, could require us to
liquidate assets or otherwise change our business, product
offerings and/or investment plans, which may negatively affect
our financial results. Although not currently anticipated, new
capital requirements and/or our regulators may require us to
raise additional capital in the future. Issuing additional common
stock may dilute the ownership of existing stockholders. In
addition, federal banking regulations may continue to increase
our compliance costs as well as limit our ability to invest in our
business or provide loans or other products and services to our
customers.
For additional information, see the “Capital Management,”
“Risk Management – Asset/Liability Management – Liquidity Risk
and Funding – Liquidity Standards,” and “Regulatory Matters”
sections in this Report and the “Regulation and Supervision”
section in our 2022 Form 10-K.
FRB policies, including policies on interest rates, can
significantly affect business and economic conditions and our
financial results and condition. The FRB regulates the supply of
money in the United States. Its policies determine in large part
our cost of funds for lending and investing and the return we
earn on those loans and investments, both of which affect our
net interest income and net interest margin. The FRB’s interest
rate policies also can materially affect the value of financial
instruments we hold, such as debt securities and MSRs. In
addition, its policies can affect our borrowers, potentially
increasing the risk that they may fail to repay their loans.
Changes in FRB policies, including its target range for the federal
funds rate or actions taken to increase or decrease the size of its
balance sheet, are beyond our control and can be hard to predict.
The FRB significantly raised its target range for the federal funds
rate and has indicated it may continue to raise it in 2023 to
address high inflation. As noted above, changes in the interest
rate environment and yield curve which may result from the
FRB’s actions could negatively affect our net interest income and
net interest margin.
CREDIT RISKS
Increased credit risk, including as a result of a deterioration in
economic conditions or changes in market conditions, could
require us to increase our provision for credit losses and
allowance for credit losses and could have a material adverse
effect on our results of operations and financial condition.
When we loan money or commit to loan money we incur credit
risk, or the risk of losses if our borrowers do not repay their loans.
As one of the largest lenders in the U.S., the credit performance
of our loan portfolios significantly affects our financial results
and condition. We also incur credit risk in connection with trading
and other activities. As noted above, if the current economic
environment were to deteriorate, more of our customers and
counterparties may have difficulty in repaying their loans or
other obligations which could result in a higher level of credit
losses and provision for credit losses. We reserve for credit losses
by establishing an allowance through a charge to earnings. The
amount of this allowance is based on our assessment of credit
losses inherent in our loan portfolio (including unfunded credit
commitments). The process for determining the amount of the
allowance is critical to our financial results and condition. It
requires difficult, subjective and complex judgments about the
future, including forecasts of economic or market conditions that
might impair the ability of our borrowers to repay their loans. We
might increase the allowance because of changing economic
conditions, including falling home prices, higher unemployment
or inflation, significant loan growth, changes in consumer
behavior, or other market conditions that adversely affect
borrowers, or other factors. Additionally, the regulatory
environment or external factors, such as natural disasters,
disease pandemics, political or social matters, or trade policies,
also can influence recognition of credit losses in our loan
portfolios and impact our allowance for credit losses.
Future allowance levels may increase or decrease based on a
variety of factors, including loan balance changes, portfolio credit
quality and mix changes, and changes in general economic
conditions. While we believe that our allowance for credit losses
was appropriate at December 31, 2022, there is no assurance
that it will be sufficient to cover future credit losses. In the event
of significant deterioration in economic conditions or if we
experience significant loan growth, we may be required to build
reserves in future periods, which would reduce our earnings.
For additional information, see the “Risk Management –
Credit Risk Management” and “Critical Accounting Policies –
Allowance for Credit Losses” sections in this Report.
We may have more credit risk and higher credit losses to the
extent our loans are concentrated by loan type, industry
segment, borrower type, or location of the borrower or
collateral. Our credit risk and credit losses can increase if our
loans are concentrated to borrowers engaged in the same or
similar activities or to borrowers who individually or as a group
may be uniquely or disproportionately affected by economic or
market conditions. Similarly, challenging economic or market
conditions, or trade policies, affecting a particular industry or
geography may also impact related or dependent industries or
the ability of borrowers living in such affected areas or working in
such industries to meet their financial obligations. We
experienced the effect of concentration risk in 2009 and 2010
when we incurred greater than expected losses in our residential
real estate loan portfolio due to a housing slowdown and greater
than expected deterioration in residential real estate values in
many markets, including the Central Valley California market and
several Southern California metropolitan statistical areas. As
California is our largest banking state in terms of loans and
deposits, deterioration in real estate values and underlying
economic conditions in those markets or elsewhere in California
could result in materially higher credit losses. In addition, changes
in consumer behavior or other market conditions may adversely
affect borrowers in certain industries or sectors, which may
Wells Fargo & Company 75
Risk Factors (continued)
increase our credit risk and reduce the demand by these
borrowers for our products and services. Moreover, deterioration
in macro-economic conditions generally across the country could
result in materially higher credit losses, including for our
residential real estate loan portfolio, which includes
nonconforming mortgage loans we retain on our balance sheet.
We may experience higher delinquencies and higher loss rates as
our consumer real estate secured lines of credit reach their
contractual end of draw period and begin to amortize.
We are currently one of the largest CRE lenders in the U.S.
A deterioration in economic conditions that negatively affects
the business performance of our CRE borrowers, including
increases in interest rates, declines in commercial property
values, and/or changes in consumer behavior or other market
conditions, such as a continued decrease in the demand for office
space, could result in materially higher credit losses and have a
material adverse effect on our financial results and condition.
Challenges and/or changes in non-U.S. economic conditions
may increase our non-U.S. credit risk. Economic difficulties in
non-U.S. jurisdictions could also indirectly have a material
adverse effect on our credit performance and results of
operations and financial condition to the extent they negatively
affect the U.S. economy and/or our borrowers who have non-U.S.
operations.
Due to regulatory requirements, we must clear certain
derivative transactions through central counterparty
clearinghouses (CCPs), which results in credit exposure to thes e
CCPs. Similarly, because we are a member of various CCPs, we
may be required to pay a portion of any losses incurred by the
CCP in the event that one or more members of the CCP defaults
on its obligations. In addition, we are exposed to the risk of non-
performance by our clients for which we clear transactions
through CCPs to the extent such non-performance is not
sufficiently covered by available collateral.
For additional information regarding credit risk, see the
“Risk Management – Credit Risk Management” section and
Note 5 (Loans and Related Allowance for Credit Losses) to
Financial Statements in this Report.
OPERATIONAL, STRATEGIC AND LEGAL RISKS
A failure in or breach of our operational or security systems,
controls or infrastructure, or those of our third-party vendors
and other service providers, could disrupt our businesses,
damage our reputation, increase our costs and cause losses.
As a large financial institution that serves customers through
numerous physical locations, ATMs, the internet, mobile banking
and other distribution channels across the U.S. and
internationally, we depend on our ability to process, record and
monitor a large number of customer transactions on a
continuous basis. As our customer base and locations have
expanded throughout the U.S. and internationally, as we have
increasingly used the internet and mobile banking to provide
products and services to our customers, as customer, public,
legislative and regulatory expectations regarding operational and
information security have increased, and as cyber and other
information security attacks have become more prevalent and
complex, our operational systems, controls and infrastructure
must continue to be safeguarded and monitored for potential
failures, disruptions and breakdowns. Our business, financial,
accounting, data processing systems or other operating systems
and facilities may stop operating properly, become insufficient
based on our evolving business needs, or become disabled or
damaged as a result of a number of factors including events that
are wholly or partially beyond our control. For example, there
have been and could in the future be sudden increases in
customer transaction volume; electrical or telecommunications
outages; degradation or loss of internet, website or mobile
banking availability; natural disasters such as earthquakes,
tornados, and hurricanes; disease pandemics; events arising from
local or larger scale political or social matters, including terrorist
acts; and, as described below, cyber attacks or other information
security incidents. Furthermore, enhancements and upgrades to
our infrastructure or operating systems may be time-consuming,
entail significant costs, and create risks associated with
implementing new systems and integrating them with existing
ones. Due to the complexity and interconnectedness of our
systems, the process of enhancing our infrastructure and
operating systems, including their security measures and
controls, can itself create a risk of system disruptions and
security issues. Similarly, we may not be able to timely recover
critical business processes or operations that have been
disrupted, which may further increase any associated costs and
consequences of such disruptions. Although we have business
continuity plans and other safeguards in place to help provide
operational resiliency, our business operations may be adversely
affected by significant and widespread disruption to our physical
infrastructure or operating systems that support our businesses
and customers. For example, on February 7, 2019, we
experienced system issues caused by an automatic power
shutdown at one of our main data center facilities. Although
applications and related workloads were systematically re-routed
to back-up data centers throughout the day, certain of our
services, including our online and mobile banking systems,
certain mortgage origination systems, and certain ATM
functions, experienced disruptions that delayed service to our
customers.
As a result of financial institutions and technology systems
becoming more interconnected and complex, any operational
incident at a third party may increase the risk of loss or material
impact to us or the financial industry as a whole. Furthermore,
third parties on which we rely, including those that facilitate our
business activities or to which we outsource operations, such as
exchanges, clearing houses, financial intermediaries or vendors
that provide services or security solutions for our operations,
could continue to be sources of operational risk to us, including
from information breaches or loss, breakdowns, disruptions or
failures of their own systems or infrastructure, or any deficiencies
in the performance of their responsibilities. These risks are
heightened to the extent we rely on a single third party or on
third parties in a single geographic area. We are also exposed to
the risk that a disruption or other operational incident at a
common service provider to our third parties could impede their
ability to provide services or perform their responsibilities for us.
In addition, we must meet regulatory requirements and
expectations regarding our use of third-party service providers,
and any failure by our third-party service providers to meet their
obligations to us or to comply with applicable laws, rules,
regulations, or Wells Fargo policies could result in fines, penalties,
restrictions on our business, or other negative consequences.
Disruptions or failures in the physical infrastructure, controls
or operating systems that support our businesses and
customers, failures of the third parties on which we rely to
adequately or appropriately provide their services or perform
their responsibilities, or our failure to effectively manage or
oversee our third-party relationships, could result in business
disruptions, loss of revenue or customers, legal or regulatory
proceedings, compliance and other costs, violations of applicable
privacy and other laws, reputational damage, or other adverse
Wells Fargo & Company 76
consequences, any of which could materially adversely affect our
results of operations or financial condition.
A cyber attack or other information security incident could
have a material adverse effect on our results of operations,
financial condition, or reputation. Information security risks for
large financial institutions such as Wells Fargo have generally
increased in recent years in part because of the proliferation of
new technologies, the use of the internet, mobile devices, and
cloud technologies to conduct financial transactions, the increase
in remote work arrangements, and the increased sophistication
and activities of organized crime, hackers, terrorists, activists,
and other external parties, including foreign state-sponsored
parties. Those parties also may continue to attempt to
misrepresent personal or financial information to commit fraud,
obtain loans or other financial products from us, or attempt to
fraudulently induce employees, customers, or other users of our
systems to disclose confidential, proprietary, or other
information to gain access to our data or that of our customers.
Geopolitical matters, such as the conflict in Ukraine, may also
elevate the risk of an information security threat, particularly by
foreign state-sponsored parties or their supporters. As noted
above, our operations rely on the secure processing, transmission
and storage of confidential, proprietary, and other information in
our computer systems and networks. Our banking, brokerage,
investment advisory, and capital markets businesses rely on our
digital technologies, computer and email systems, software,
hardware, and networks to conduct their operations. In addition,
to access our products and services, our customers may use
personal smartphones, tablets, and other mobile devices that are
beyond our control systems. Our technologies, systems,
software, networks, and our customers’ devices continue to be
the target of cyber attacks or other information security threats,
which could materially adversely affect us, including as a result of
fraudulent activity, the unauthorized release, gathering,
monitoring, misuse, loss or destruction of Wells Fargo’s or our
customers’ confidential, proprietary and other information, or
the disruption of Wells Fargo’s or our customers’ or other third
parties’ business operations. For example, various retailers have
reported they were victims of cyber attacks in which large
amounts of their customers’ data, including debit and credit card
information, was obtained. In these situations, we generally incur
costs to replace compromised cards and address fraudulent
transaction activity affecting our customers. We are also exposed
to the risk that an employee or other person acting on behalf of
the Company fails to comply with applicable policies and
procedures and inappropriately circumvents information security
controls for personal gain or other improper purposes.
Due to the increasing interconnectedness and complexity of
financial institutions and technology systems, an information
security incident at a third party or a third party’s downstream
service providers may increase the risk of loss or material impact
to us or the financial industry as a whole. In addition, third parties
(including their downstream service providers) on which we rely,
including those that facilitate our business activities or to which
we outsource operations, such as internet, mobile technology,
hardware, software, and cloud service providers, continue to be
sources of information security risk to us. We could suffer
material harm, including business disruptions, losses or
remediation costs, reputational damage, legal or regulatory
proceedings, or other adverse consequences as a result of the
failure of those third parties to adequately or appropriately
safeguard their technologies, systems, networks, hardware, and
software, or as a result of our or our customers’ data being
compromised due to information security incidents affecting
those third parties.
Our risk and exposure to information security threats
remains heightened because of, among other things, the
persistent and evolving nature of these threats, the prominent
size and scale of Wells Fargo and its role in the financial services
industry, our plans to continue to implement our digital and
mobile banking channel strategies and develop additional remote
connectivity solutions to serve our customers when and how
they want to be served, our geographic footprint and
international presence, the outsourcing of some of our business
operations, and the current global economic and political
environment. For example, Wells Fargo and other financial
institutions, as well as our third-party service providers, continue
to be the target of various evolving and adaptive information
security threats, including cyber attacks, malware, ransomware,
other malicious software intended to exploit hardware or
software vulnerabilities, phishing, credential validation, and
distributed denial-of-service, in an effort to disrupt the
operations of financial institutions, test their cybersecurity
capabilities, commit fraud, or obtain confidential, proprietary or
other information. Cyber attacks have also focused on targeting
online applications and services, such as online banking, as well as
cloud-based and other products and services provided by third
parties, and have targeted the infrastructure of the internet,
causing the widespread unavailability of websites and degrading
website performance. As a result, information security and the
continued development and enhancement of our controls,
processes and systems designed to protect our networks,
computers, software and data from attack, damage or
unauthorized access remain a priority for Wells Fargo. We are
also proactively involved in industry cybersecurity efforts and
working with other parties, including our third-party service
providers and governmental agencies, to continue to enhance
defenses and improve resiliency to information security threats.
As these threats continue to evolve, we expect to continue to be
required to expend significant resources to develop and enhance
our protective measures or to investigate and remediate any
information security vulnerabilities or incidents. Because the
investigation of any information security breach is inherently
unpredictable and would require time to complete, we may not
be able to immediately address the consequences of a breach,
which may further increase any associated costs and
consequences. Moreover, to the extent our insurance covers
aspects of information security risk, such insurance may not be
sufficient to cover all liabilities or losses associated with an
information security breach.
Cyber attacks or other information security incidents
affecting us or third parties (including their downstream service
providers) on which we rely, including those that facilitate our
business activities or to which we outsource operations, or
affecting the networks, systems or devices that our customers
use to access our products and services, could result in business
disruptions, loss of revenue or customers, legal or regulatory
proceedings, compliance, remediation and other costs, violations
of applicable privacy and other laws, reputational damage, or
other adverse consequences, any of which could materially
adversely affect our results of operations or financial condition.
Our framework for managing risks may not be fully effective in
mitigating risk and loss to us. Our risk management framework
seeks to mitigate risk and loss to us. We have established
processes and procedures intended to identify, measure,
monitor, report and analyze the types of risk to which we are
subject, including liquidity risk, credit risk, market risk, interest
Wells Fargo & Company 77
Risk Factors (continued)
rate risk, operational risk, legal and compliance risk, and
reputational risk, among others. However, as with any risk
management framework, there are inherent limitations to our
risk management strategies as there may exist, or develop in the
future, risks that we have not appropriately anticipated,
identified or managed. Our risk management framework is also
dependent on ensuring that effective operational controls and a
sound culture exist throughout the Company. The inability to
develop effective operational controls or to foster the
appropriate culture in each of our lines of business, including the
inability to align performance management and compensation to
achieve the desired culture, could adversely impact the
effectiveness of our risk management framework. Similarly, if we
are unable to effectively manage our business or operations, we
may be exposed to increased risks or unexpected losses. We
process a large number of transactions each day and are exposed
to risks or losses if we do not accurately or completely execute a
process or transaction, whether due to human error or otherwise;
if we are unable to detect and prevent fraudulent activity; or if an
employee or third-party service provider fails to comply with
applicable policies and procedures, inappropriately circumvents
controls, or engages in other misconduct.
In certain instances, we rely on models to measure, monitor
and predict risks, such as market, interest rate, liquidity and
credit risks, as well as to help inform business decisions; however,
there is no assurance that these models will appropriately or
sufficiently capture all relevant risks or accurately predict future
events or exposures. Furthermore, certain of our models are
subject to regulatory review and approval, and any failure to
meet regulatory standards or expectations could result in fines,
penalties, restrictions on our ability to engage in certain business
activities, or other adverse consequences, and any required
modifications or changes to these models can impact our capital
ratios and requirements and result in increased operational and
compliance costs. In addition, we rely on data to aggregate and
assess our various risk exposures and business activities, and any
issues with the quality or effectiveness of our data, including our
aggregation, management, and validation procedures, could
result in ineffective risk management practices, business
decisions or customer service, inefficient use of resources, or
inaccurate regulatory or other risk reporting. We also use
artificial intelligence to help further inform or automate our
business decisions and risk management practices, but there is
no assurance that artificial intelligence will appropriately or
sufficiently replicate certain outcomes or human assessment or
accurately predict future events or exposures. Previous financial
and credit crises and resulting regulatory reforms highlighted
both the importance and some of the limitations of managing
unanticipated risks, and our regulators remain focused on
ensuring that financial institutions, and Wells Fargo in particular,
build and maintain robust risk management policies and
practices. If our risk management framework proves ineffective,
we could suffer unexpected losses which could materially
adversely affect our results of operations or financial condition.
We may be exposed to additional legal or regulatory
proceedings, costs, and other adverse consequences related to
retail sales practices and instances where customers may have
experienced financial harm. Various government entities and
offices have undertaken formal or informal inquiries or
investigations arising out of certain retail sales practices of the
Company that were the subject of settlements with the CFPB,
the OCC, and the Office of the Los Angeles City Attorney
announced by the Company on September 8, 2016, and various
non-governmental parties filed lawsuits against us seeking
damages or other remedies related to these retail sales practices.
The Company has entered into various settlements to resolve
these investigations and proceedings, as a result of which we
have incurred monetary penalties, costs, and business
restrictions. If we are unable to meet any ongoing obligations
under these settlements, we may incur additional monetary or
other penalties or be required to make admissions of wrongdoing
and comply with other conditions, which can lead to restrictions
on our ability to engage in certain business activities or offer
certain products or services, limitations on our ability to access
capital markets, limitations on capital distributions, the loss of
customers, and/or other adverse consequences. Any inability to
meet our ongoing obligations under these settlements,
depending on the sanctions and remedy sought and granted,
could materially adversely affect our results of operations and
financial condition. In addition, negative publicity or public
opinion resulting from these matters may increase the risk of
reputational harm to our business, which can impact our ability to
keep and attract customers, affect our ability to attract and
retain qualified employees, result in the loss of revenue, or have
other material adverse effects on our results of operations and
financial condition.
Furthermore, we have identified and may in the future
identify areas or instances where customers may have
experienced financial harm, including as a result of our continuing
efforts to strengthen our risk and control infrastructure. For
example, we have identified certain issues related to past
practices involving certain automobile collateral protection
insurance policies and certain issues related to the unused
portion of guaranteed automobile protection waiver or insurance
agreements. The identification of such areas or instances where
customers may have experienced financial harm could lead to,
and in some cases has already resulted in, additional remediation
costs, loss of revenue or customers, legal or regulatory
proceedings, compliance and other costs, reputational damage,
or other adverse consequences.
For additional information, see the “Overview – Retail Sales
Practices Matters” and “Overview – Customer Remediation
Activities” sections and Note 13 (Legal Actions) to Financial
Statements in this Report.
We may incur fines, penalties and other negative
consequences from regulatory violations or from any failure to
meet regulatory standards or expectations. We maintain
systems and procedures designed to ensure that we comply with
applicable laws and regulations. However, we are subject to
heightened compliance and regulatory oversight and
expectations, particularly due to the evolving and increasingly
complex regulatory landscape we operate in. We are also subject
to consent orders and other regulatory actions that subject us to
various conditions and restrictions. In addition, a single event or
issue may give rise to numerous and overlapping investigations
and proceedings, either by multiple federal and state agencies in
the U.S. or by multiple regulators and other governmental
entities in different jurisdictions. Similarly, regulators may be
more likely to pursue investigations or proceedings against us to
the extent that we are or have previously been subject to other
regulatory actions. Also, the laws and regulations in jurisdictions
in which we operate may be different or even conflict with each
other, such as differences between U.S. federal and state law or
differences between U.S. and non-U.S. laws as to the products
and services we may offer or other business activities we may
engage in, which can lead to compliance difficulties or issues.
Furthermore, many legal and regulatory regimes require us to
report transactions and other information to regulators and
Wells Fargo & Company 78
other governmental authorities, self-regulatory organizations,
exchanges, clearing houses and customers. We may be subject to
fines, penalties, restrictions on our business, or other negative
consequences if we do not timely, completely, or accurately
provide regulatory reports, customer notices or disclosures.
Moreover, some legal/regulatory frameworks provide for the
imposition of fines or penalties for noncompliance even though
the noncompliance was inadvertent or unintentional and even
though there were systems and procedures in place at the time
designed to ensure compliance. For example, we are subject to
regulations issued by the Office of Foreign Assets Control
(OFAC) that prohibit financial institutions from participating in
the transfer of property belonging to the governments of certain
non-U.S. countries and designated nationals of those countries.
OFAC may impose penalties or restrictions on certain activities
for inadvertent or unintentional violations even if reasonable
processes are in place to prevent the violations. Any violation of
these or other applicable laws or regulatory requirements, even if
inadvertent or unintentional, or any failure to meet regulatory
standards or expectations, including any failure to satisfy the
conditions of any consent orders or other regulatory actions,
could result in significant fees, penalties, restrictions on our
ability to engage in certain business activities, reputational harm,
loss of customers, or other negative consequences.
Reputational harm, including as a result of our actual or alleged
conduct or public opinion of the financial services industry
generally, could adversely affect our business, results of
operations, and financial condition. Reputation risk, or the risk
to our business, earnings and capital from negative public
opinion, is inherent in our business and has increased
substantially because of our size and profile in the financial
services industry, sales practices related matters, and instances
where customers may have experienced financial harm. Negative
public opinion about the financial services industry generally or
Wells Fargo specifically could adversely affect our reputation and
our ability to keep and attract customers. Negative public opinion
could result from our actual or alleged conduct in any number of
activities, including sales practices; mortgage, auto or other
consumer lending practices; loan origination or servicing
activities; mortgage foreclosure actions; management of client
accounts or investments; lending, investing or other business
relationships; identification and management of potential
conflicts of interest from transactions, obligations and interests
with and among our customers; environmental, social and
governance practices; regulatory compliance; risk management;
incentive compensation practices; and disclosure, sharing or
inadequate protection or improper use of customer information,
and from actions taken by government regulators and
community or other organizations in response to that conduct.
Although we have policies and procedures in place intended to
detect and prevent conduct by employees and third-party
service providers that could potentially harm customers or our
reputation, there is no assurance that such policies and
procedures will be fully effective in preventing such conduct.
Furthermore, our actual or perceived failure to address or
prevent any such conduct or otherwise to effectively manage our
business or operations could result in significant reputational
harm. In addition, because we conduct most of our businesses
under the “Wells Fargo” brand, negative public opinion about one
business also could affect our other businesses. Moreover,
actions by the financial services industry generally or by certain
members or individuals in the industry also can adversely affect
our reputation. The proliferation of social media websites utilized
by Wells Fargo and other third parties, as well as the personal use
of social media by our employees and others, including personal
blogs and social network profiles, also may increase the risk that
negative, inappropriate or unauthorized information may be
posted or released publicly that could harm our reputation or
have other negative consequences, including as a result of our
employees interacting with our customers in an unauthorized
manner in various social media outlets.
Wells Fargo and other financial institutions have been
targeted from time to time by protests and demonstrations,
which have included disrupting the operation of our retail
banking locations, and have been subject to negative public
commentary, including with respect to the fees charged for
various products and services. Wells Fargo and other financial
institutions have also been subject to negative publicity as a
result of providing or reducing financial services to or making
investments in industries or organizations subject to stakeholder
concerns. There can be no assurance that continued protests or
negative public opinion of the Company specifically or large
financial institutions generally will not harm our reputation and
adversely affect our business, results of operations, and financial
condition.
If we are unable to develop and execute effective business
plans or strategies or manage change effectively, our
competitive standing and results of operations could suffer. In
order to advance our business goals, we may undertake business
plans or strategies related to, among other things, our
organizational structure, our compliance and risk management
framework, our expenses and efficiency, the types of products
and services we offer, the types of businesses we engage in, the
geographies in which we operate, the manner in which we serve
our clients and customers, the third parties with which we do
business, and the methods and distribution channels by which we
offer our products and services. Accomplishing these business
plans or strategies may be complex, time intensive, require
significant financial, technological, management and other
resources, may divert management attention and resources away
from other areas of the Company, and may impact our expenses
and ability to generate revenue. There is no guarantee that any
business plans or strategies, including our current efficiency
initiatives, will ultimately be successful. To the extent we are
unable to develop or execute effective business plans or
strategies or manage change effectively, our competitive
position, reputation, prospects for growth, and results of
operations may be adversely affected.
In addition, from time to time, we may decide to divest
certain businesses or assets. Difficulties in executing a divestiture
may cause us not to realize any expected cost savings or other
benefits from the divestiture, or may result in higher than
expected losses of employees or harm our ability to retain
customers. The divestiture or winding down of certain businesses
or assets may also result in the impairment of goodwill or other
long-lived assets related to those businesses or assets.
Similarly, we may explore opportunities to expand our
products, services, and assets through strategic acquisitions of
companies or businesses in the financial services industry. We
generally must receive federal regulatory approvals before we
can acquire a bank, bank holding company, or certain other
financial services businesses. We cannot be certain when or if, or
on what terms and conditions, any required regulatory approvals
will be granted. We might be required to sell banks, branches
and/or business units or assets or issue additional equity as a
condition to receiving regulatory approval for an acquisition.
When we do announce an acquisition, our stock price may fall
depending on the size of the acquisition, the type of business to
Wells Fargo & Company 79
Risk Factors (continued)
be acquired, the purchase price, and the potential dilution to
existing stockholders or our earnings per share if we issue
common stock in connection with the acquisition. Furthermore,
difficulty in integrating an acquired company or business may
cause us not to realize expected revenue increases, cost savings,
increases in geographic or product presence, and other projected
benefits from the acquisition. The integration could result in
higher than expected deposit attrition, loss of key employees, an
increase in our compliance costs or risk profile, disruption of our
business or the acquired business, or otherwise harm our ability
to retain customers and employees or achieve the anticipated
benefits of the acquisition. Time and resources spent on
integration may also impair our ability to grow our existing
businesses. Many of the foregoing risks may be increased if the
acquired company or business operates internationally or in a
geographic location where we do not already have significant
business operations and/or employees.
Our operations and business could be adversely affected by the
impacts of climate change. The physical effects of climate
change, including the increased prevalence and severity of
extreme weather events and natural disasters, such as
hurricanes, droughts, and wildfires, could damage or interfere
with our operations or those of our third-party service providers,
which could disrupt our business, increase our costs, or cause
losses. Climate change related impacts could also negatively
affect the financial condition of our customers, increase the
credit risk associated with those customers, or result in the
deterioration of the value of the collateral we hold. In addition,
changes in consumer behavior or other market conditions on
account of climate considerations or due to the transition to a
low carbon economy may adversely affect customers in certain
industries, sectors or geographies, which may increase our credit
risk and reduce the demand by these customers for our products
and services. Furthermore, the transition to a low carbon
economy could affect our business practices or result in
additional costs or other adverse consequences to our business
operations. Legislation and/or regulation in connection with
climate change, as well as stakeholder perceptions and
expectations related to climate change and its impacts, could
require us to change certain of our business and/or risk
management practices, impose additional costs on us, or
otherwise adversely affect our operations and business.
Moreover, our reputation may be damaged as a result of our
response to climate change or our strategy for the transition to a
low carbon economy, including if we are unable or perceived to be
unable to achieve our objectives or if our response is disliked,
disfavored, or perceived to be ineffective or insufficient. For
additional information on regulatory developments in response
to climate change, see the “Regulatory Matters” section in this
Report.
We are exposed to potential financial loss or other adverse
consequences from legal actions. Wells Fargo and some of its
subsidiaries are involved in judicial, regulatory, governmental,
arbitration, and other proceedings or investigations concerning
matters arising from the conduct of our business activities, and
many of those proceedings and investigations expose
Wells Fargo to potential financial loss or other adverse
consequences. There can be no assurance as to the ultimate
outcome of any of these legal actions. We establish accruals for
legal actions when potential losses associated with the actions
become probable and the costs can be reasonably estimated. We
may still incur costs for a legal action even if we have not
established an accrual. In addition, the actual cost of resolving a
legal action may be substantially higher than any amounts
accrued for that action. The ultimate resolution of a pending legal
proceeding or investigation, depending on the remedy sought
and granted, could materially adversely affect our results of
operations and financial condition.
As noted above, we are subject to heightened regulatory
oversight and scrutiny, which may lead to regulatory
investigations, proceedings or enforcement actions. In addition
to imposing potentially significant monetary penalties, business
restrictions, and other sanctions, regulatory authorities may
require criminal pleas or other admissions of wrongdoing and
compliance with other conditions in connection with settling
such matters, which can lead to reputational harm, loss of
customers, restrictions on the ability to access capital markets,
limitations on capital distributions, the inability to engage in
certain business activities or offer certain products or services,
and/or other direct and indirect adverse effects.
For additional information, see Note 13 (Legal Actions) to
Financial Statements in this Report.
MORTGAGE BUSINESS RISKS
Our mortgage banking revenue can be volatile from quarter to
quarter, including from the impact of changes in interest rates,
and we rely on the GSEs to purchase our conforming loans to
reduce our credit risk and provide liquidity to fund new
mortgage loans. We earn revenue from fees we receive for
originating mortgage loans and for servicing mortgage loans.
Changes in interest rates can affect these fees, as well as the fair
value of our MSRs. When rates rise, the demand for mortgage
loans usually tends to fall, reducing the revenue we receive from
loan originations. Under the same conditions, revenue from our
MSRs can increase due to a decline in the likelihood of
prepayments, which increases the fair value of our MSRs. When
rates fall, mortgage originations usually tend to increase and the
value of our MSRs usually tends to decline, also with some
offsetting revenue effect. Even though they can act as a “natural
hedge,” the hedge is not perfect, either in amount or timing.
We typically use derivatives and other instruments to hedge
our mortgage banking interest rate risk. We may not hedge all of
our risk, and we may not be successful in hedging any of the risk.
Hedging is not a perfect science, and we could incur significant
losses from our hedging activities.
We rely on the GSEs to purchase mortgage loans that meet
their conforming loan requirements and on government insuring
agencies, such as the Federal Housing Administration (FHA) and
the Department of Veterans Affairs (VA), to insure or guarantee
loans that meet their policy requirements. If the GSEs or
government insuring agencies were to limit or reduce their
purchasing, insuring or guaranteeing of loans, our ability to fund,
and thus originate, new mortgage loans, could be reduced. We
cannot assure that the GSEs or government insuring agencies will
not materially limit their purchases, insuring or guaranteeing of
conforming loans or change their criteria for what constitutes a
conforming loan (e.g., maximum loan amount or borrower
eligibility). As noted above, there are various proposals to reform
the housing finance market in the U.S., including the role of the
GSEs in the housing finance market. The impact of any such
regulatory reform regarding the housing finance market and the
GSEs, as well as any effect on the Company’s business and
financial results, are uncertain. In addition, to meet customer
needs, we also originate loans that do not conform to either the
GSEs’ or government insuring agencies’ standards, which are
generally retained on our balance sheet and therefore do not
generate sale proceeds that could be used to originate new loans.
Wells Fargo & Company 80
For additional information, see the “Risk Management –
Asset/Liability Management – Mortgage Banking Interest Rate
and Market Risk,” “Critical Accounting Policies – Valuation of
Residential Mortgage Servicing Rights (MSRs)” and “Critical
Accounting Policies – Fair Value of Financial Instruments”
sections in this Report.
We may suffer losses, penalties, or other adverse
consequences if we fail to satisfy our obligations with respect
to the residential mortgage loans we originate or service. For
residential mortgage loans that we originate, we could become
subject to monetary damages and other civil penalties, including
the loss of certain contractual payments or the inability to
exercise certain remedies under the loans such as foreclosure
proceedings, if it is alleged or determined that the loans were not
originated in accordance with applicable laws or regulations.
Additionally, for residential mortgage loans that we
originate and sell, we may be required to repurchase the loans or
indemnify or reimburse the securitization trust, investor or
insurer for credit losses incurred on loans in the event of a breach
of contractual representations or warranties in the agreements
under which we sell the loans or in the insurance or guaranty
agreements that we enter into with the FHA and VA. We
establish a mortgage repurchase liability that reflects
management’s estimate of losses for loans for which we have a
repurchase obligation. Because the level of the liability depends
on economic factors and other external conditions, the level of
the liability is difficult to estimate, requires considerable
management judgment, and is subject to change. If economic
conditions or the housing market worsen, we could have
increased repurchase obligations and increased loss severity on
repurchases, requiring significant additions to the repurchase
liability.
Furthermore, if we fail to satisfy our servicing obligations for
the mortgage loans we service, we may be terminated as servicer
or master servicer, required to indemnify the securitization
trustee against losses, and/or contractually obligated to
repurchase a mortgage loan or reimburse investors for credit
losses, any of which could significantly reduce our net servicing
income.
We may also incur costs, liabilities to borrowers and/or
securitization investors, legal proceedings, or other adverse
consequences if we fail to meet our servicing obligations,
including with respect to mortgage foreclosure actions or if we
experience delays in the foreclosure process. Our net servicing
income and the fair value of our MSRs may be negatively
affected to the extent our servicing costs increase because of
higher foreclosure or other servicing related costs. In addition, we
may continue to be subject to fines, business restrictions, and
other sanctions imposed by federal or state regulators as a result
of actual or perceived deficiencies in our mortgage servicing
practices, including with respect to our foreclosure practices, our
loss mitigation activities such as loan modifications or
forbearances, or our servicing of flood zone properties. Any of
these actions may harm our reputation, negatively affect our
residential mortgage origination or servicing business, or result in
material fines, penalties, equitable remedies, or other
enforcement actions. We may also face risks, including
regulatory, compliance, and market risks, as we pursue our
previously announced plans to reduce the amount of residential
mortgage loans we service.
For additional information, see the “Overview,” “Risk
Management – Credit Risk Management – Mortgage Banking
Activities,” and “Critical Accounting Policies – Valuation of
Residential Mortgage Servicing Rights” sections and Note 13
(Legal Actions) and Note 18 (Pledged Assets and Collateral) to
Financial Statements in this Report.
COMPETITIVE RISKS
We face significant and increasing competition in the rapidly
evolving financial services industry. We compete with other
financial institutions in a highly competitive industry that is
undergoing significant changes as a result of financial regulatory
reform, technological advances, increased public scrutiny, and
current economic conditions. Our success depends on, among
other things, our ability to develop and maintain deep and
enduring relationships with our customers based on the quality
of our customer service, the wide variety of products and
services that we can offer our customers and the ability of those
products and services to satisfy our customers’ needs and
preferences, the pricing of our products and services, the
extensive distribution channels available for our customers, our
innovation, and our reputation. Continued or increased
competition in any one or all of these areas may negatively affect
our customer relationships, market share and results of
operations and/or cause us to increase our capital investment in
our businesses in order to remain competitive. In addition, our
ability to reposition or reprice our products and services from
time to time may be limited and could be influenced significantly
by the current economic, regulatory and political environment for
large financial institutions as well as by the actions of our
competitors. Furthermore, any changes in the types of products
and services that we offer our customers and/or the pricing for
those products and services could result in a loss of customer
relationships and market share and could materially adversely
affect our results of operations.
Continued technological advances and the growth of
e-commerce have made it possible for non-depository
institutions to offer products and services that traditionally were
banking products, and for financial institutions and other
companies to provide electronic and internet-based financial
solutions, including electronic securities trading, lending and
payment solutions. In addition, technological advances, including
digital currencies and alternative payment methods, may
diminish the importance of depository institutions and other
financial intermediaries in the transfer of funds between parties.
We may not respond effectively to these and other competitive
threats from existing and new competitors and may be forced to
sell products at lower prices, increase our investment in our
business to modify or adapt our existing products and services,
and/or develop new products and services to respond to our
customers’ needs and preferences. To the extent we are not
successful in developing and introducing new products and
services or responding or adapting to the competitive landscape
or to changes in customer preferences, we may lose customer
relationships and our revenue growth and results of operations
may be materially adversely affected.
Our ability to attract and retain qualified employees is critical
to the success of our business and failure to do so could
adversely affect our business performance, competitive
position and future prospects. The success of Wells Fargo is
heavily dependent on the talents and efforts of our employees,
including our senior leaders, and in many areas of our business,
including commercial banking, brokerage, investment advisory,
capital markets, risk management and technology, the
competition for highly qualified personnel is intense. We also
seek to retain a pipeline of employees to provide continuity of
succession for our senior leadership positions. In order to attract
Wells Fargo & Company 81
Risk Factors (continued)
and retain highly qualified employees, we must provide
competitive compensation, benefits and work arrangements,
effectively manage employee performance and development,
and foster a diverse and inclusive environment. As a large
financial institution and additionally to the extent we remain
subject to consent orders we may be subject to limitations on
compensation by our regulators that may adversely affect our
ability to attract and retain these qualified employees, especially
if some of our competitors may not be subject to these same
compensation limitations. If we are unable to continue to attract
and retain qualified employees, including successors for senior
leadership positions, our business performance, competitive
position and future prospects may be adversely affected.
FINANCIAL REPORTING RISKS
Changes in accounting standards, and changes in how
accounting standards are interpreted or applied, could
materially affect our financial results and condition. From time
to time the FASB and the SEC update the financial accounting
and reporting standards that govern the preparation of our
external financial statements. In addition, accounting standard
setters and those who interpret the accounting standards (such
as the FASB, SEC, and banking regulators) may update their
previous interpretations or positions on how these standards
should be applied. Changes in financial accounting and reporting
standards and changes in current interpretations may be beyond
our control, can be hard to predict, and could materially affect
our financial results and condition, including requiring a
retrospective restatement of prior period financial statements.
Similarly, any change in our accounting policies could also
materially affect our financial statements. For additional
information, see the “Current Accounting Developments” section
in this Report.
Our financial statements require certain assumptions and
estimates and rely on the effectiveness of our internal control
over financial reporting. Pursuant to U.S. GAAP, we are required
to use certain assumptions and estimates in preparing our
financial statements, including, among other items, in
determining the allowance for credit losses, the liability for
contingent litigation losses, and the fair value of certain assets
and liabilities such as debt securities, loans held for sale, MSRs,
derivative assets and liabilities, and equity securities. Several of
our accounting policies are critical because they require
management to make difficult, subjective and complex
judgments about matters that are inherently uncertain and
because it is likely that materially different amounts would be
reported under different conditions or using different
assumptions. If the assumptions or estimates underlying our
financial results are incorrect or different from actual results, we
could experience unexpected losses or other adverse impacts,
some of which could be significant. For a description of our
critical accounting policies, see the “Critical Accounting Policies”
section in this Report.
The Sarbanes-Oxley Act of 2002 (Sarbanes-Oxley) requires
our management to evaluate the Company’s disclosure controls
and procedures and its internal control over financial reporting
and requires our auditors to issue a report on our internal control
over financial reporting. We are required to disclose, in our annual
report on Form 10-K, the existence of any “material weaknesses”
in our internal controls. We cannot assure that we will not
identify one or more material weaknesses as of the end of any
given quarter or year, nor can we predict the effect on our
reputation or stock price of disclosure of a material weakness.
We could also be required to devote significant resources to
remediate any material weakness. In addition, our customers may
rely on the effectiveness of certain of our operational and
internal controls as a service provider, and any deficiency in those
controls could affect our customers and damage our reputation
or business. Sarbanes-Oxley also limits the types of non-audit
services our outside auditors may provide to us in order to
preserve their independence from us. If our auditors were found
not to be independent of us, we could be required to engage new
auditors and re-file financial statements and audit reports with
the SEC. We could be out of compliance with SEC rules until new
financial statements and audit reports were filed, limiting our
ability to raise capital and resulting in other adverse
consequences.
* * *
Any factor described in this Report or in any of our other SEC
filings could by itself, or together with other factors, adversely
affect our financial results and condition. Refer to our quarterly
reports on Form 10-Q filed with the SEC in 2023 for material
changes to the above discussion of risk factors. There are factors
not discussed above or elsewhere in this Report that could
adversely affect our financial results and condition.
Wells Fargo & Company 82

Controls and Procedures
Disclosure Controls and Procedures
The Company’s management evaluated the effectiveness, as of December 31, 2022, of the Company’s disclosure controls and
procedures. The Company’s chief executive officer and chief financial officer participated in the evaluation. Based on this evaluation, the
Company’s chief executive officer and chief financial officer concluded that the Company’s disclosure controls and procedures were
effective as of December 31, 2022.
Internal Control Over Financial Reporting
Internal control over financial reporting is defined in Rule 13a-15(f) promulgated under the Securities Exchange Act of 1934 as a process
designed by, or under the supervision of, the Company’s principal executive and principal financial officers and effected by the
Company’s Board, management and other personnel, to provide reasonable assurance regarding the reliability of financial reporting and
the preparation of financial statements for external purposes in accordance with U.S. generally accepted accounting principles (GAAP)
and includes those policies and procedures that:
• pertain to the maintenance of records that in reasonable detail accurately and fairly reflect the transactions and dispositions of
assets of the Company;
• provide reasonable assurance that transactions are recorded as necessary to permit preparation of financial statements in
accordance with GAAP, and that receipts and expenditures of the Company are being made only in accordance with authorizations
of management and directors of the Company; and
• provide reasonable assurance regarding prevention or timely detection of unauthorized acquisition, use or disposition of the
Company’s assets that could have a material effect on the financial statements.
Because of its inherent limitations, internal control over financial reporting may not prevent or detect misstatements. Projections
of any evaluation of effectiveness to future periods are subject to the risk that controls may become inadequate because of changes in
conditions, or that the degree of compliance with the policies or procedures may deteriorate. No change occurred during fourth quarter
2022 that has materially affected, or is reasonably likely to materially affect, the Company’s internal control over financial reporting.
Management’s report on internal control over financial reporting is set forth below and should be read with these limitations
in mind.
Management’s Report on Internal Control Over Financial Reporting
The Company’s management is responsible for establishing and maintaining adequate internal control over financial reporting for the
Company. Management assessed the effectiveness of the Company’s internal control over financial reporting as of December 31, 2022,
using the criteria set forth by the Committee of Sponsoring Organizations of the Treadway Commission (COSO) in Internal Control –
Integrated Framework (2013). Based on this assessment, management concluded that as of December 31, 2022, the Company’s internal
control over financial reporting was effective.
KPMG LLP, the independent registered public accounting firm that audited the Company’s financial statements included in this
Annual Report, issued an audit report on the Company’s internal control over financial reporting. KPMG’s audit report appears on the
following page.
Wells Fargo & Company 83

FF
Report of Independent Registered Public Accounting Firm
T
o
the
S
toc
kh
o
ld
er
s
a
n
d
Boa
r
d
o
f
D
ir
e
ctor
s
W
ells
F
ar
g
o
&
C
ompan
y:
Op
i
n
i
o
n
on
In
te
rn
al
Contro
l
O
ve
r
F
i
na
n
ci
a
l
Re
port
i
ng
W
e
h
a
v
e
aud
i
ted
W
e
ll
s
Fa
r
go
&
C
om
pa
n
y
a
n
d
subs
i
d
i
a
r
ies
(
t
he
C
ompan
y
)
i
n
t
e
rn
a
l
co
n
t
r
o
l
ov
er
f
i
n
a
n
c
i
a
lre
p
or
t
in
g
as
of
D
ece
m
ber
3
1
,
2022,
based
on
c
ri
te
ri
a
esta
b
li
s
h
e
d
i
n In
te
rn
al
C
ontro
l
–
I
nte
g
rated Fr
a
m
e
w
o
rk
(
2013
)
i
ssued
b
y
t
h
e
C
o
m
m
ittee
of
S
ponsorin
g
O
r
g
anization
s
of
t
h
e
Tr
ea
d
w
a
y
C
ommissio
n
.
I
n
our
o
p
inion
,
t
h
e
C
ompan
y
m
a
in
t
ained
,
i
n
a
ll m
at
e
ri
a
l res
p
ec
t
s
,
ef
f
ect
i
v
e
in
te
rn
al
co
n
t
r
o
l
o
v
er
f
in
a
n
c
i
al
reportin
g
a
s
of
Dece
mbe
r
3
1
,
2022
,
ba
se
d
o
n
c
ri
t
e
ri
a
est
ab
li
s
h
ed
i
n
I
n
te
rn
al
C
ontro
l
–
Inte
g
rate
d
F
r
a
m
e
w
o
rk
(
2013)
issued
by
t
h
e
C
omm
i
tte
e
of
Sponsor
i
n
g
O
r
g
an
i
z
a
tion
s
of
t
h
e
Treadwa
y
C
o
mm
issio
n
.
W
e
also
ha
v
e
a
u
d
ite
d,
i
n
a
cco
r
da
n
ce
w
i
th
the
sta
n
da
r
ds
of
t
he
P
u
bl
i
c
C
ompany
Accou
n
t
i
n
g
O
versi
gh
t
B
oa
r
d
(
U
ni
t
ed
St
at
es
)
(PCAOB)
,
the
co
n
soli
dated
bala
n
ce
sheet
of
the
C
omp
a
n
y
a
s
of
Dece
m
ber
3
1
,
2022
a
n
d
202
1
,
t
he
r
elat
ed
co
n
sol
i
dat
ed
st
at
e
m
e
n
t
of
i
ncome
,
compre
h
ensiv
e
i
n
c
ome
,
cha
nges
in
e
qu
i
t
y
,
a
n
d
ca
sh
f
l
o
w
s
fo
r
each
of
t
he
y
ea
r
s
in
t
he
t
h
ree-
y
ear
perio
d
e
n
ded
D
ece
m
ber
3
1
,
2022
,
a
n
d
the
r
elated
n
otes
(
collective
l
y,
the
con
sol
i
da
te
d
f
in
a
n
c
i
al
st
at
e
m
e
n
t
s
)
,
a
n
d
our
repor
t
dat
ed
F
e
b
ruary
2
1
,
2023
ex
presse
d
an
unquali
f
ie
d
o
pi
n
i
on
on
those
co
n
sol
i
dated
f
in
a
n
cia
l
sta
te
me
n
ts.
Bas
is
f
o
r
O
p
i
n
i
o
n
Th
e
C
ompan
y’
s mana
g
e
m
e
n
t
i
s
r
e
sp
o
n
s
i
b
l
e
fo
rm
a
i
n
ta
inin
g
effect
i
v
e
i
n
t
e
rn
al
co
n
t
r
ol
ov
er
f
i
n
a
n
c
i
a
l
r
e
p
or
t
i
n
g
a
n
d
f
or
i
t
s
ass
es
s
m
e
n
t
o
f
t
h
e
effect
iv
e
n
e
ss
of
i
n
te
rn
a
l
co
n
tr
o
l
ov
e
r
f
in
a
n
c
i
a
l
r
e
por
t
in
g,
in
c
l
uded
i
n
t
he
a
ccompan
y
i
n
g
M
ana
g
emen
t
’
s
R
epor
t
on
I
n
t
e
rn
a
l
C
ontro
l
o
v
er
Fin
a
n
c
i
a
l Report
i
n
g.
O
ur respo
n
s
ibility
is
to
e
xp
r
e
ss
an
op
i
n
i
o
n
on
t
h
e
C
ompany
’
s
i
n
t
e
rn
al
co
n
t
r
ol
ov
er
f
i
n
a
n
c
i
a
l report
i
n
g
bas
e
d
o
n
o
ur
aud
i
t.
W
e
a
r
e
a
publi
c
a
ccou
n
tin
g
f
ir
m
r
e
gi
st
e
r
e
d
w
ith
t
h
e
PC
A
O
B
a
n
d
a
r
e
r
equired
t
o
be
i
ndependen
t
w
it
h
respec
t
t
o
t
h
e
C
ompan
y
in
acco
r
da
n
ce
wi
th
the
U
.
S
.
feder
a
l
se
cu
ri
t
i
e
s
la
w
s
a
n
d
the
a
pp
l
ica
bl
er
ules
a
n
d
re
g
u
l
at
io
n
s
of
t
he
S
ecuri
t
i
es
a
n
d
Exc
h
an
g
e
C
ommi
s
s
i
o
n
a
nd
the
P
C
A
O
B
.
W
e
co
n
ducted
our
aud
it
i
n
a
cco
r
d
a
n
ce
w
ith
the
sta
n
da
r
ds
of
t
he
P
C
AO
B
.
T
hose
st
a
n
da
r
ds
requ
i
r
e
t
hat
we
p
l
a
n
a
n
d
per
f
o
r
m
the
au
d
i
t
to
o
bta
i
n
r
easo
n
able
ass
u
r
a
nce
a
bout
w
he
the
r
e
ffe
ctiv
e
i
n
t
e
rn
al
co
n
t
r
ol
ov
er
f
i
n
a
n
c
i
al
r
epor
t
i
ng
was
m
ai
n
t
a
in
ed
i
n
all
m
at
e
ri
al
r
es
pec
ts
.
O
u
r
au
d
i
t
o
f
i
nterna
l
co
ntro
l
o
v
er
f
in
a
n
c
i
a
l
r
e
po
r
ti
n
g
i
nc
l
u
d
e
d
o
b
taining
an
un
d
erstan
d
in
g
of
i
n
t
erna
l
con
t
ro
l
ov
er
f
i
nancia
l
report
i
ng
,
assess
i
ng
the
ris
k
t
h
at
a
ma
t
er
i
a
l
w
e
a
kn
e
ss
e
xi
sts,
a
n
d
t
es
t
i
ng
a
n
d
e
va
l
uat
i
ng
t
he
d
esign an
d
opera
t
i
ng e
f
f
ec
t
iv
eness
o
f
i
nterna
l
co
nt
ro
l
b
ased
on
t
h
e
assessed
r
i
s
k.
O
ur
a
ud
i
t
a
lso
in
c
l
ude
d
pe
r
formin
g
su
ch
ot
h
er
p
rocedure
s
as
we
co
n
s
i
de
r
ed
necessar
y
in
t
he
c
ir
cu
m
s
ta
n
ce
s
.
W
e
be
li
e
v
e
t
h
at
our
aud
i
t
p
rovides
a
r
e
a
so
n
a
b
l
e
ba
s
i
s
f
o
r
ou
r
o
p
inion
.
Definition and Limitations of Internal Control Over Financial Reporting
A company
’s
i
n
te
r
n
al
co
n
t
r
ol
o
v
e
r
f
in
a
n
cia
l
r
e
por
ti
n
g
is
a
p
r
ocess
d
esigne
d
t
o
p
r
ov
ide
r
easo
n
able
assu
r
ance
regar
d
in
g
t
he
re
l
ia
b
i
l
ity
o
f
f
in
a
n
c
i
al
report
in
g
a
n
d
the
p
r
epar
a
tion
of
f
i
n
a
n
cia
l
sta
te
m
e
n
t
s
for
ex
t
e
rn
al
p
ur
poses
i
n
acco
r
da
n
ce
w
it
h
genera
ll
y accep
t
ed
account
i
n
g
princip
l
es.
A
company
’
s
i
nter
na
l
c
on
t
ro
l
ov
e
r
f
i
n
a
n
c
i
a
l
r
epor
t
i
ng
i
nc
l
u
d
es
t
h
os
e
po
l
icie
s
a
n
d
p
roce
d
ure
s
t
h
at
(
1
)
per
t
ai
n
t
o
t
he
ma
i
nten
an
ce
o
f
recor
d
s
tha
t,
in
re
a
son
a
ble
de
ta
il,
a
cc
u
r
a
t
e
ly
a
n
d
f
air
l
yre
f
l
ec
t
t
h
e
t
ransac
t
i
ons
a
n
d
d
isposit
i
on
s
o
f
t
h
e asse
t
so
f
the
compan
y;
(
2
)
p
rov
i
de
r
ea
sona
ble
a
ss
u
r
a
n
ce
t
ha
t
t
r
a
n
sa
c
t
i
on
s
a
r
e
recor
d
e
d
as
necessa
r
y
t
o
p
erm
it
prepara
t
i
on o
f
f
inancia
l
s
t
a
t
emen
t
s
i
n
a
ccor
d
anc
e
wi
th
gene
r
a
ll
y
a
ccep
t
e
d
a
cco
u
n
t
i
n
g
p
r
in
cip
l
es
,
an
d
t
h
at rece
i
p
t
s
an
d
ex
p
en
d
i
t
u
r
es
o
f
t
h
e
compan
y
a
r
e
b
eing
m
a
d
e
o
n
l
y
i
n
acco
r
da
n
c
e
wi
th
aut
ho
riz
a
t
i
o
n
s
o
f
ma
n
a
ge
m
e
n
t
a
n
d
d
ir
ect
o
r
s
o
f
t
h
e
compan
y
;
a
n
d
(
3
)
p
rovi
de
r
easo
n
ab
l
e
assu
r
a
n
ce
r
e
g
ardin
g
p
reventio
n
or
timel
y
detect
i
on
o
f
u
n
a
ut
h
or
i
z
e
d
a
c
q
uisition,
u
s
e
,
or
dis
p
osi
t
io
n
o
f
t
h
e
compan
y
’
s
asset
s
t
hat
cou
l
d
hav
e
a
mate
ri
a
l
e
f
f
e
ct
o
n
t
h
e
fin
a
n
c
i
a
l
stat
e
m
e
n
ts.
B
ecause
of
i
ts
inh
e
r
e
n
t
l
imi
ta
t
i
on
s
,
i
n
te
r
n
a
l
con
t
r
ol
o
v
e
r
fin
a
n
c
i
al
re
p
or
t
in
g
ma
y
n
ot
p
re
v
e
n
t
or
det
ect
mi
sst
at
e
m
e
n
t
s
. Also
,
p
ro
j
ect
i
o
n
s
o
fan
y
e
v
a
l
uat
i
on
o
f
e
ff
ect
iv
e
n
ess
to
f
utu
r
e
pe
r
iods
a
r
e
su
bj
ec
t
t
o
t
he
ri
sk
t
hat
co
n
t
r
o
l
s
ma
y
beco
m
e
inade
q
ua
t
e
because
o
f chan
g
e
s
in
c
o
n
d
i
t
i
on
s
,
o
r
t
h
at
t
h
e
de
gr
ee
of
com
p
li
a
n
ce
w
ith
t
h
e
p
olicie
s
o
r
p
rocedure
s
ma
y
det
e
ri
o
r
at
e
.
C
h
ar
l
otte
,
N
o
r
th
C
aro
l
i
n
a
Fe
b
ruar
y
2
1
,
2023
Wells Fargo & Company
84
2,968
Financial Statements
Wells Fargo & Company and Subsidiaries
Consolidated Statement of Income
Year ended December 31,
(in millions, except per share amounts) 2022 2021 2020
Interest income
Debt securities $ 11,781 9,253 11,234
Loans held for sale 513 865 947
Loans 37,715 28,634 34,230
Equity securities 707 608 554
Other interest income 3,308 334 954
Total interest income 54,024 39,694 47,919
Interest expense
Deposits 2,349 388 2,804
Short-term borrowings 582 (41) 250
Long-term debt 5,505 3,173 4,471
Other interest expense 638 395 438
Total interest expense 9,074 3,915 7,963
Net interest income 44,950 35,779 39,956
Noninterest income
Deposit and lending-related fees 6,713 6,920 6,602
Investment advisory and other asset-based fees 9,004 11,011 9,863
Commissions and brokerage services fees 2,242 2,299 2,384
Investment banking fees 1,439 2,354 1,865
Card fees 4,355 4,175 3,544
Mortgage banking 1,383 4,956 3,493
Net gains from trading and securities 1,461 7,264 2,710
Other 2,238 3,734 3,847
Total noninterest income 28,835 42,713 34,308
Total revenue 73,785 78,492 74,264
Provision for credit losses 1,534 (4,155) 14,129
Noninterest expense
Personnel 34,340 35,541 34,811
Technology, telecommunications and equipment 3,375 3,227 3,099
Occupancy 2,881 3,263
Operating losses 6,984 1,568 3,523
Professional and outside services 5,188 5,723 6,706
Advertising and promotion 505 600 600
Restructuring charges 5 76 1,499
Other 4,004 4,128 4,129
Total noninterest expense 57,282 53,831 57,630
Income before income tax expense 14,969 28,816 2,505
Income tax expense (benefit) 2,087 5,578 (1,157)
Net income before noncontrolling interests 12,882 23,238 3,662
Less: Net income (loss) from noncontrolling interests (300) 1,690 285
Wells Fargo net income $ 13,182 21,548 3,377
Less: Preferred stock dividends and other 1,115 1,292 1,591
Wells Fargo net income applicable to common stock $ 12,067 20,256 1,786
Per share information
Earnings per common share $
3.17
4.99
0.43
Diluted earnings per common
share 3.14 4.95
0.43
Average common shares outstanding 3,805.2 4,061.9
4,118.0
Diluted average common shares outstanding 3,837.0 4,096.2
4,134.2
The accompanying notes are an integral part of these statements.
Wells Fargo & Company 85
Wells Fargo & Company and Subsidiaries
Consolidated Statement of Comprehensive Income
Year ended December 31,
(in millions) 2022 2021 2020
Net income before noncontrolling interests $ 12,882 23,238 3,662
Other comprehensive income (loss), after tax:
Net change in debt securities (10,500) (2,375) 1,487
Net change in derivatives and hedging activities (1,090) 159 149
Defined benefit plans adjustments 154 349 (181)
Other (241) (30) 50
Other comprehensive income (loss), after tax (11,677) (1,897) 1,505
Total comprehensive income before noncontrolling interests 1,205 21,341 5,167
Less: Other comprehensive income (loss) from noncontrolling interests 2 (1) —
Less: Net income (loss) from noncontrolling interests (300) 1,690 285
Wells Fargo comprehensive income $ 1,503 19,652 4,882
The accompanying notes are an integral part of these statements.
Wells Fargo & Company 86
Wells Fargo & Company and Subsidiaries
Consolidated Balance Sheet
(in millions, except shares)
Dec 31,
2022
Dec 31,
2021
Assets
Cash and due from banks $ 34,596 24,616
Interest-earning deposits with banks 124,561 209,614
Total cash, cash equivalents, and restricted cash 159,157 234,230
Federal funds sold and securities purchased under resale agreements 68,036 66,223
Debt securities:
Trading, at fair value (includes assets pledged as collateral of $26,932 and $13,304) 86,155 88,265
Available-for-sale, at fair value (amortized cost of $121,725 and $175,463, net of allowance for credit losses) 113,594 177,244
Held-to-maturity, at amortized cost, net of allowance for credit losses (fair value $255,521 and $272,386) 297,059 272,022
Loans held for sale (includes $4,220 and $15,895 carried at fair value) 7,104 23,617
Loans 955,871 895,394
Allowance for loan losses (12,985) (12,490)
Net loans 942,886 882,904
Mortgage servicing rights (includes $9,310 and $6,920 carried at fair value) 10,480 8,189
Premises and equipment, net 8,350 8,571
Goodwill 25,173 25,180
Derivative assets 22,774 21,478
Equity securities (includes $28,383 and $39,098 carried at fair value; and assets pledged as collateral of $747 and $984) 64,414 72,886
Other assets 75,834 67,259
Total assets (1) $ 1,881,016 1,948,068
Liabilities
Noninterest-bearing deposits $
458,010
527,748
Interest-bearing deposits 925,975 954,731
Total deposits 1,383,985 1,482,479
Short-term borrowings (includes $181 and $0 carried at fair value) 51,145 34,409
Derivative liabilities 20,085 9,424
Accrued expenses and other liabilities (includes $20,123 and $20,685 carried at fair value) 69,056 70,957
Long-term debt (includes $1,346 and $0 carried at fair value) 174,870 160,689
Total liabilities (2) 1,699,141 1,757,958
Equity
Wells Fargo stockholders’ equity:
Preferred stock – aggregate liquidation preference of $20,216 and $20,825 19,448 20,057
Common stock – $1-2/3 par value, authorized 9,000,000,000 shares; issued 5,481,811,474 shares 9,136 9,136
Additional paid-in capital 60,319 60,196
Retained earnings 187,649 180,322
Accumulated other comprehensive loss (13,381) (1,702)
Treasury stock, at cost – 1,648,007,022 shares and 1,596,009,977 shares (82,853) (79,757)
Unearned ESOP shares (429) (646)
Total Wells Fargo stockholders’ equity 179,889 187,606
Noncontrolling interests 1,986 2,504
Total equity 181,875 190,110
Total liabilities and equity $
1,881,016
1,948,068
(1) Our consolidated assets at December 31, 2022 and 2021, include the following assets of certain variable interest entities (VIEs) that can only be used to settle the liabilities of those VIEs: Debt
securities, $71 million and $71 million; Loans, $4.8 billion and $4.5 billion; All other assets, $191 million and $234 million; and Total assets, $5.1 billion and $4.8 billion, respectively.
(2) Our consolidated liabilities at December 31, 2022 and 2021, include the following VIE liabilities for which the VIE creditors do not have recourse to Wells Fargo: Long-term debt, $0 million and
$149 million; All other liabilities, $201 million and $259 million; and Total liabilities, $201 million and $408 million, respectively.
The accompanying notes are an integral part of these statements.
Wells Fargo & Company 87
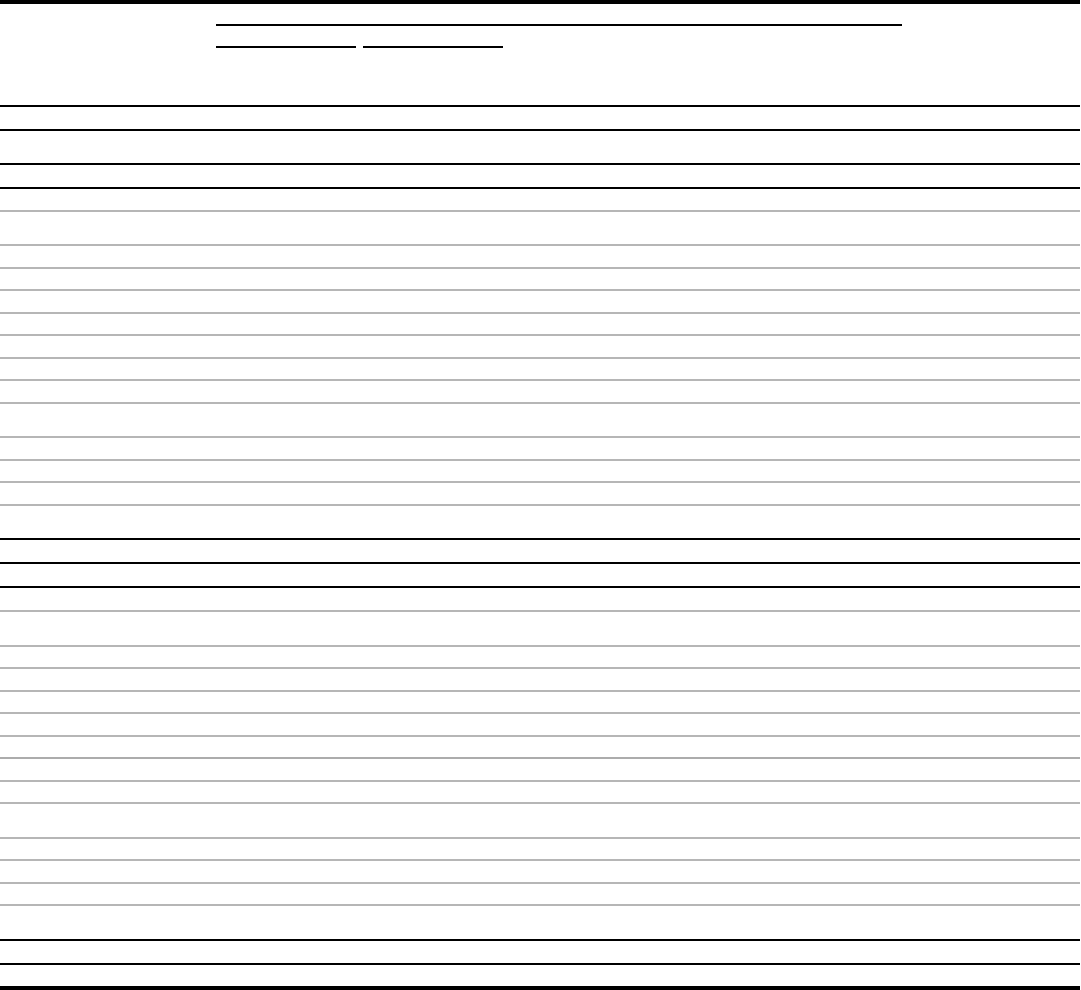
Wells Fargo & Company and Subsidiaries
Consolidated Statement of Changes in Equity
Wells Fargo stockholders’ equity
Preferred stock Common stock
Accumulated
other
comprehensive
income (loss)
Additional
paid-in
capital
Unearned
ESOP
shares ($ and shares in millions) Shares Amount Shares Amount
Retained
earnings
Treasury
stock
Noncontrolling
interests
Total
equity
Balance December 31, 2019 7.5 $ 21,549 4,134.4 $ 9,136 61,049 166,415 (1,311) (68,831) (1,143) 838 187,702
Cumulative effect from change in
accounting policies (1) 990 990
Balance January 1, 2020 7.5 21,549 4,134.4 9,136 61,049 167,405 (1,311) (68,831) (1,143) 838 188,692
Net income 3,377 285 3,662
Other comprehensive income,
net of tax 1,505 — 1,505
Noncontrolling interests (91) (91)
Common stock issued 75.6 207 (1,449) 3,961 2,719
Common stock repurchased (75.7) (3,415) (3,415)
Preferred stock issued 0.1 3,183 (67) 3,116
Preferred stock redeemed (2) (1.9) (3,347) 46 (301) — (3,602)
Preferred stock issued to ESOP — — — — —
Preferred stock released by ESOP (19) 268 249
Preferred stock converted to
common sh ares (0.2) (249) 9.7 (243) 492 —
Common stock dividends 44 (5,059) (5,015)
Preferred stock dividends (1,290) (1,290)
Stock-based compensation 643 643
Net change in deferred compensation
and related plans (1,463) 2 (1,461)
Net change (2.0) (413) 9.6 — (852) (4,722) 1,505 1,040 268 194 (2,980)
Balance December 31, 2020 5.5 $ 21,136 4,144.0 $ 9,136 60,197 162,683 194 (67,791) (875) 1,032 185,712
Net income 21,548 1,690 23,238
Other comprehensive loss,
net of tax (1,896) (1) (1,897)
Noncontrolling interests (217) (217)
Common stock issued 43.8 (8) (162) 2,265 2,095
Common stock repurchased (306.4) (14,464) (14,464)
Preferred stock issued 0.2 5,810 (54) 5,756
Preferred stock redeemed (3) (0.2) (6,676) 87 (87) — (6,676)
Preferred stock issued to ESOP — — — — —
Preferred stock released by ESOP (16) 229 213
Preferred stock converted to
common sh ares (0.2) (213) 4.4 (8) 221 —
Common stock dividends 29 (2,455) (2,426)
Preferred stock dividends (1,205) (1,205)
Stock-based compensation 1,043 1,043
Net change in deferred compensation
and related plans (1,074) 12 (1,062)
Net change (0.2) (1,079) (258.2) — (1) 17,639 (1,896) (11,966) 229 1,472 4,398
Balance December 31, 2021 5.3 $ 20,057 3,885.8 $ 9,136 60,196 180,322 (1,702) (79,757) (646) 2,504 190,110
(1) Effective Ja nuary 1, 2020, we a dopted ASU 2016-13 – F inancial Inst ruments – C redit Losses (Top ic 326): Measurement of Credit Losses on Financial Instruments (CECL). For additional infor mation, see
Note 1 (Summary of S ignificant Accounting Policies) in ou r Annual Rep ort on F orm 10-K for the y ear ended December 31, 2020.
(2) Represents t he im pact of t he r edemption of t he r emaining preferred stock, Series K , in fir st quarter 2020, and Series T a nd Series V in fou rth quarter 2020.
(3) Represents t he im pact of t he r edemption of Pr eferred Stock, Series I, Series P a nd Series W, in fir st quarter 2021; Preferred Stock, Series N, in second quarter 2021; and Preferred Stock, Series O a nd
Series X , in t hird quarter 2021.
The accompanying notes are an integral part of these statements.
Wells Fargo & Company 88
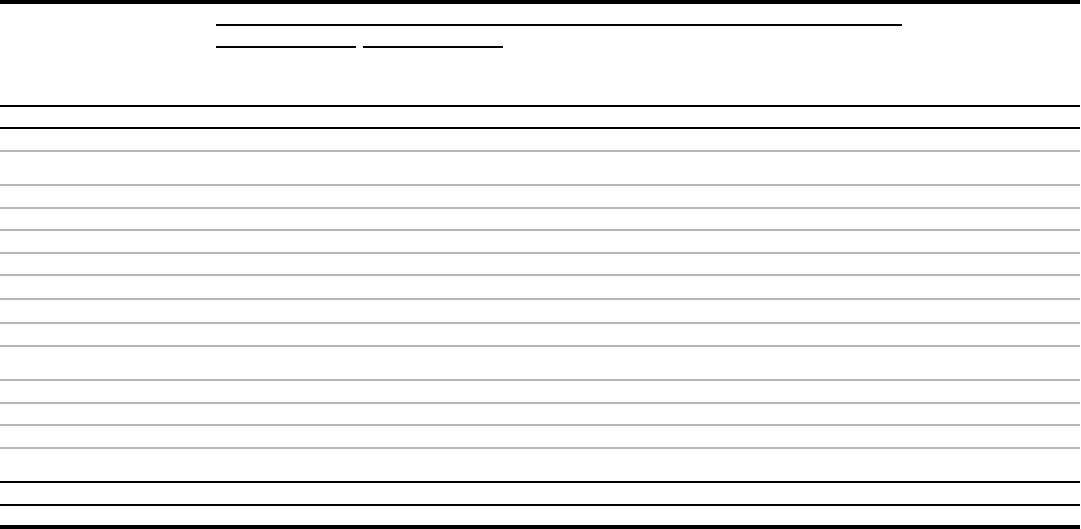
Wells Fargo & Company and Subsidiaries
Consolidated Statement of Changes in Equity
Wells Fargo stockholders’ equity
Preferred stock Common stock
Accumulated
other
comprehensive
income (loss)
Additional
paid-in
capital
Unearned
ESOP
shares ($ and shares in millions) Shares Amount Shares Amount
Retained
earnings
Treasury
stock
Noncontrolling
interests
Total
equity
Balance December 31, 2021 5.3 $ 20,057 3,885.8 $ 9,136 60,196 180,322 (1,702) (79,757) (646) 2,504 190,110
Net income (loss) 13,182 (300) 12,882
Other comprehensive income (loss),
net of tax (11,679) 2 (11,677)
Noncontrolling interests (220) (220)
Common stock issued 43.5 129 (497) 2,181 1,813
Common stock repurchased (110.4) (6,033) (6,033)
Preferred stock issued — — — —
Preferred stock redeemed (1) (0.6) (609) (37) — 646 —
Common stock issued to ESOP (1) 14.9 (129) 747 (618) —
Common stock released by ESOP (2) (1) 189 188
Preferred stock converted to
common shares — — — — — —
Common stock dividends 59 (4,243) (4,184)
Preferred stock dividends (1,115) (1,115)
Stock-based compensation 1,002 1,002
Net change in deferred
compensation and related plans (900) 9 (891)
Net change (0.6) (609) (52.0) — 123 7,327 (11,679) (3,096) 217 (518) (8,235)
Balance December 31, 2022 4.7 $ 19,448 3,833.8 $ 9,136 60,319 187,649 (13,381) (82,853) (429) 1,986 181,875
(1) See Note 11 (Preferred Stock) for additional information.
(2) For additional information on our ESOP Plan, see the “Employee Stock Ownership Plan” section of Note 12 (Common Stock and Stock Plans).
The accompanying notes are an integral part of these statements.
Wells Fargo & Company 89
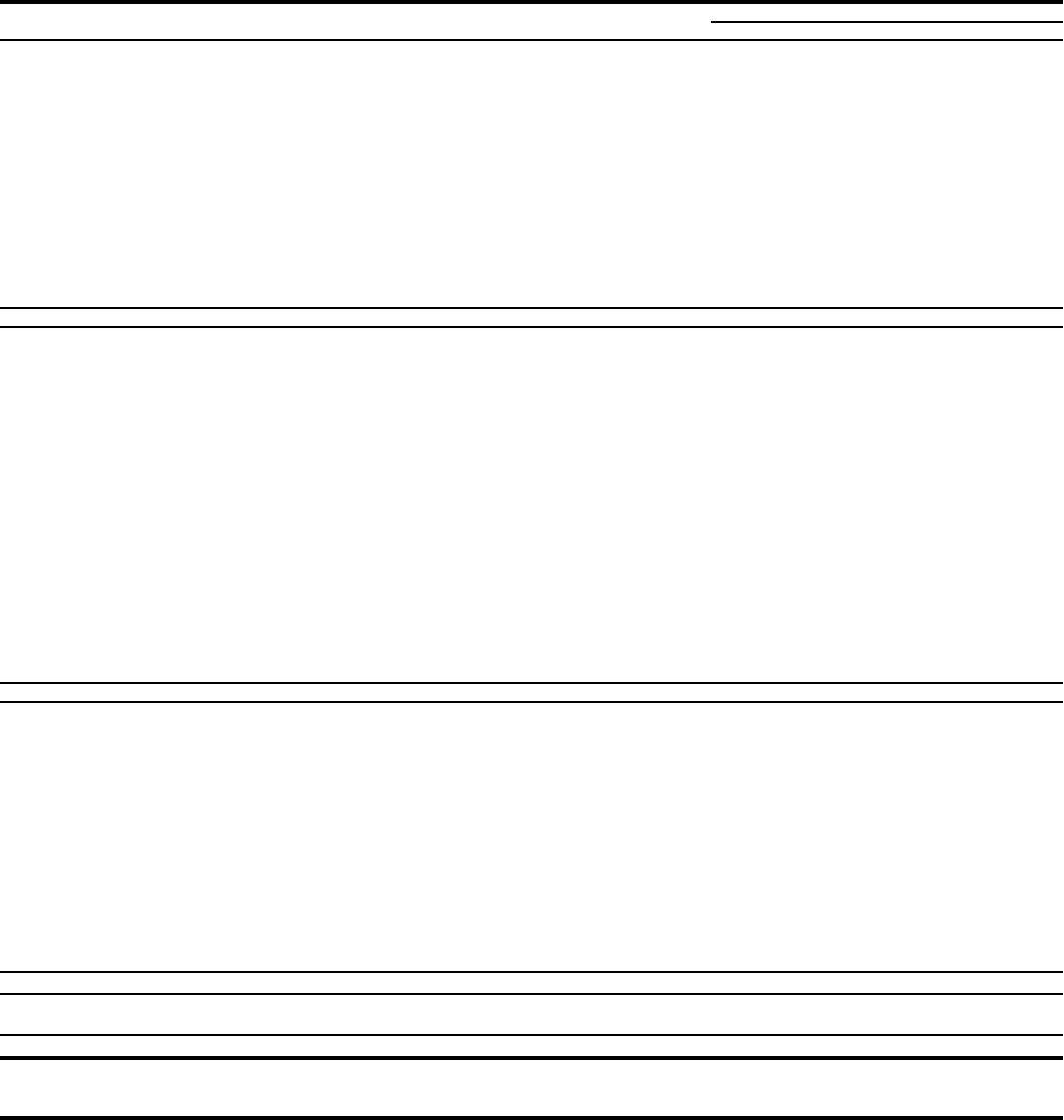
Cash flows from financing activities:
Net change in:
Deposits (98,494) 78,582 81,755
Short-term borrowings 16,564 (24,590) (45,513)
Long-term debt:
Proceeds from issuance 53,737 1,275 38,136
Repayment (19,587) (47,134) (65,347)
Preferred stock:
Proceeds from issuance — 5,756 3,116
Redeemed — (6,675) (3,602)
Cash dividends paid (1,115) (1,205) (1,290)
Common stock:
Repurchased (6,033) (14,464) (3,415)
Cash dividends paid (4,178) (2,422) (4,852)
Other, net (539) (361) (231)
Net cash used by financing activities (59,645) (11,238) (1,243)
Net change in cash, cash equivalents, and restricted cash (75,073) (30,382) 123,362
Cash, cash equivalents, and restricted cash at beginning of period 234,230 264,612 141,250
Cash, cash equivalents, and restricted cash at end of period $ 159,157 234,230 264,612
Supplemental cash flow disclosures:
Cash paid for interest $ 8,289 4,384 8,414
Cash paid for income taxes, net 3,376 3,166 1,175
Wells Fargo & Company and Subsidiaries
Consolidated Statement of Cash Flows
Year ended December 31,
(in millions) 2022 2021 2020
Cash flows from operating activities:
Net income before noncontrolling interests $ 12,882 23,238 3,662
Adjustments to reconcile net income to net cash provided by operating activities:
Provision for credit losses 1,534 (4,155) 14,129
Changes in fair value of MSRs and LHFS carried at fair value (1,326) (1,188) 4,321
Depreciation, amortization and accretion 6,832 7,890 8,219
Deferred income tax expense (benefit) 1,075 (1,292) (3,289)
Other, net (14,524) (12,194) 7,024
Originations and purchases of loans held for sale (74,910) (158,923) (181,961)
Proceeds from sales of and paydowns on loans originally classified as held for sale 65,418 101,293 122,592
Net change in:
Debt and equity securities, held for trading 31,579 19,334 43,214
Derivative assets and liabilities 7,856 (2,472) (5,492)
Other assets (9,137) 15,477 (12,304)
Other accrued expenses and liabilities (231) 1,467 1,936
Net cash provided (used) by operating activities 27,048 (11,525) 2,051
Cash flows from investing activities:
Net change in:
Federal funds sold and securities purchased under resale agreements (704) (551) 36,468
Available-for-sale debt securities:
Proceeds from sales 16,895 17,958 48,638
Paydowns and maturities 19,791 75,701 78,174
Purchases (40,104) (110,431) (91,545)
Held-to-maturity debt securities:
Paydowns and maturities 27,666 79,517 36,641
Purchases (2,360) (71,245) (46,755)
Equity securities, not held for trading:
Proceeds from sales and capital returns 4,326 4,933 12,187
Purchases (6,984) (7,680) (8,677)
Loans:
Loans originated by banking subsidiaries, net of principal collected (74,861) (28,809) 53,718
Proceeds from sales of loans originally classified as held for investment 12,446 31,847 9,359
Purchases of loans (741) (389) (1,313)
Principal collected on nonbank entities’ loans 5,173 8,985 7,927
Loans originated by nonbank entities (3,824) (11,237) (13,052)
Other, net 805 3,782 784
Net cash provided (used) by investing activities (42,476) (7,619) 122,554
The accompanying notes are an integral part of these statements. See Note 1 (Summary of Significant Accounting Policies) for noncash activities.
Wells Fargo & Company 90

Notes to Financial Statements
-See the “Glossary of Acronyms“ at the end of this Report for terms used throughout the Financial Statements and related Notes.
Note 1: Summary of Significant Accounting Policies
Wells Fargo & Company is a diversified financial services
company. We provide banking, investment and mortgage
products and services, as well as consumer and commercial
finance, through banking locations and offices, the internet and
other distribution channels to individuals, businesses and
institutions in all 50 states, the District of Columbia, and in
countries outside the U.S. When we refer to “Wells Fargo,” “the
Company,” “we,” “our” or “us,” we mean Wells Fargo & Company
and Subsidiaries (consolidated). Wells Fargo & Company (the
Parent) is a financial holding company and a bank holding
company. We also hold a majority interest in a real estate
investment trust, which has publicly traded preferred stock
outstanding.
Our accounting and reporting policies conform with U.S.
generally accepted accounting principles (GAAP) and practices in
the financial services industry. To prepare the financial
statements in conformity with GAAP, management must make
estimates based on assumptions about future economic and
market conditions (for example, unemployment, market liquidity,
real estate prices, etc.) that affect the reported amounts of
assets and liabilities at the date of the financial statements,
income and expenses during the reporting period and the related
disclosures. Although our estimates contemplate current
conditions and how we expect them to change in the future, it is
reasonably possible that actual conditions could be worse than
anticipated in those estimates, which could materially affect our
results of operations and financial condition. Management has
made significant estimates in several areas, including:
• allowance for credit losses (Note 5 (Loans and Related
Allowance for Credit Losses));
• valuations of residential mortgage servicing rights (MSRs)
(Note 6 (Mortgage Banking Activities) and Note 16
(Securitizations and Variable Interest Entities));
• valuations of financial instruments (Note 15 (Fair Values of
Assets and Liabilities));
• liabilities for contingent litigation losses (Note 13 (Legal
Actions));
• income taxes (Note 22 (Income Taxes)); and
• goodwill impairment (Note 7 (Intangible Assets and Other
Assets)).
Actual results could differ from those estimates.
Accounting Standards Adopted in 2022
In 2022, we adopted the following new accounting guidance:
• Accounting Standards Update (ASU or Update) 2020-06 –
Debt – Debt with Conversion and Other Options (Subtopic
470-20) and Derivatives and Hedging – Contracts in Entity’s
Own Equity (Subtopic 815-40): Accounting for Convertible
Instruments and Contracts in an Entity’s Own Equity
• ASU 2021-05 – Leases (Topic 842): Lessors – Certain Leases
with Variable Lease Payments
• ASU 2021-10 – Government Assistance (Topic 832):
Disclosures by Business Entities about Government Assistance
• ASU 2022-06 – Reference Rate Reform (Topic 848): Deferral
of the Sunset Date of Topic 848
ASU 2020-06 simplifies the accounting for convertible financial
instruments that embody characteristics of debt and equity by
(1) eliminating accounting models for convertible financial
instruments with cash conversion and beneficial conversion
features within Accounting Standards Codification (ASC)
Subtopic 470-20, (2) removing three equity classification
requirements for a contract in an entity’s own equity to qualif y
for the derivative scope exception in ASC Subtopic 815-40, and
(3) prescribing the method used for computing earnings per
share. We adopted this Update prospectively in first quarter
2022. This Update did not have a material impact to our
consolidated financial statements.
ASU 2021-05 amends ASC Topic 842 – Leases and provides
specific guidance for lessors whose leases include variable lease
payments that are not dependent on a reference index or rate
and otherwise would have resulted in the recognition of a loss at
lease commencement (a day 1 loss). Prior to ASU 2016-02,
variable lease payments were excluded from the definition of
lease payments for lessors measuring their net investment loss in
a sales-type lease or direct financing lease. This often resulted in
a day 1 loss, even if the lessor expected the arrangement to be
profitable overall. We adopted this Update prospectively in first
quarter 2022. This Update did not have a material impact to our
consolidated financial statements.
ASU 2021-1 0 created a new topic in the codification, ASC Topic
832. The ASU requires annual disclosures for a business entity
that has received government assistance and uses a grant or
contribution accounting model by analogy to other accounting
guidance. We adopted this Update in fourth quarter 2022 on a
prospective basis. This Update did not have a material impact t o
our consolidated financial statements.
ASU 2022-06 defers the sunset date of ASC Topic 848 –
Reference Rate Reform from December 31, 2022, to
December 31, 2024, to extend the ability to apply the guidance
in Topic 848, which provides temporary optional guidance to
ease the burden in accounting for reference rate reform on
financial reporting. We adopted this Update prospectively in
fourth quarter 2022. This Update did not have a material impact
to our consolidated financial statements.
Consolidation
Our consolidated financial statements include the accounts of
the Parent and our subsidiaries in which we have a controlling
financial interest. When our consolidated subsidiaries follow
specialized industry accounting, that accounting is retained in
consolidation.
We are also a variable interest holder in certain entities in
which equity investors do not have the characteristics of a
controlling financial interest or where the entity does not have
enough equity at risk to finance its activities without additional
subordinated financial support from other parties (collectively
referred to as variable interest entities (VIEs)). Our variable
interest arises from contractual, ownership or other monetary
interests in the entity, which change with fluctuations in the fair
value of the entity’s net assets. We consolidate a VIE if we are the
primary beneficiary, which is when we have both the power to
direct the activities that most significantly impact the VIE and a
variable interest that could potentially be significant to the VIE.
To determine whether or not a variable interest we hold could
potentially be significant to the VIE, we consider both qualitative
and quantitative factors regarding the nature, size and form of
Wells Fargo & Company 91
Note 1: Summary of Significant Accounting Policies (continued)
our involvement with the VIE. We assess whether or not we are
the primary beneficiary of a VIE on an ongoing basis.
Significant intercompany accounts and transactions are
eliminated in consolidation. When we have significant influence
over operating and financing decisions for a company but do not
own a majority of the voting equity interests, we account for the
investment using the equity method of accounting, which
requires us to recognize our proportionate share of the
company’s earnings. If we do not have significant influence, we
account for the equity security under the fair value method, cost
method or measurement alternative.
Noncontrolling interests represent the portion of net
income and equity attributable to third-party owners of
consolidated subsidiaries that are not wholly-owned by
Wells Fargo. Substantially all of our noncontrolling interests
relate to our affiliated venture capital and private equity
businesses.
Cash, Cash Equivalents, and Restricted Cash
Cash, cash equivalents and restricted cash are recorded at
amortized cost and include cash on hand, cash items in transit,
and amounts due from or held with other depository institutions.
See Note 25 (Regulatory Capital Requirements and Other
Restrictions) for additional information on the restrictions on
cash and cash equivalents.
Trading Activities
We engage in trading activities to accommodate the investment
and risk management activities of our customers. These
activities predominantly occur in our Corporate and Investment
Banking reportable operating segment. Trading assets and
liabilities include debt securities, equity securities, loans held
for sale, derivatives and short sales, which are reported within
our consolidated balance sheet based on the accounting
classification of the instrument. In addition, debt securities that
are held for investment purposes that we have elected to
account for under the fair value method, are classified as trading.
Our trading assets and liabilities are carried on our
consolidated balance sheet at fair value with changes in fair
value recognized in net gains from trading and securities within
noninterest income. Interest income and interest expense are
recognized in net interest income.
Customer accommodation trading activities include our
actions as an intermediary to buy and sell financial instruments
and market-making activities. We also take positions to manage
our exposure to customer accommodation activities. We hold
financial instruments for trading in long positions, as well as short
positions, to facilitate our trading activities. As an intermediary,
we interact with market buyers and sellers to facilitate the
purchase and sale of financial instruments to meet the
anticipated or current needs of our customers. For example, we
may purchase or sell a derivative to a customer who wants to
manage interest rate risk exposure. We typically enter into an
offsetting derivative or security position to manage our exposure
to the customer transaction. We earn income based on the
transaction price difference between the customer transaction
and the offsetting position, which is reflected in earnings where
the fair value changes and related interest income and expense of
the positions are recorded.
Our market-making activities include taking long and short
trading positions to facilitate customer order flow. These
activities are typically executed on a short-term basis. As a
market-maker we earn income due to: (1) the difference
between the price paid or received for the purchase and sale of
the security (bid-ask spread), (2) the net interest income of the
positions, and (3) the changes in fair value of the trading
positions held on our consolidated balance sheet. Additionally, we
may enter into separate derivative or security positions to
manage our exposure related to our long and short trading
positions taken in our market-making activities. Income earned
on these market-making activities are reflected in earnings
where the fair value changes and related interest income and
expense of the positions are recorded.
Available-for-Sale and Held-to-Maturity Debt Securities
Our investments in debt securities that are not held for tradin g
purposes are classified as either available-for-sale (AFS) or held -
to-maturity (HTM).
Investments in debt securities for which the Company does
not have the positive intent and ability to hold to maturity are
classified as AFS. AFS debt securities are measured at fair value,
with unrealized gains and losses reported in accumulated other
comprehensive income (AOCI). The amount reported in other
comprehensive income (OCI) is net of the allowance for credit
losses (ACL) and applicable income taxes. Investments in debt
securities for which the Company has the positive intent and
ability to hold to maturity are classified as HTM. HTM debt
securities are measured at amortized cost, net of ACL. See Note
3 (Available-for-Sale and Held-to-Maturity Debt Securities) for
additional information.
INTEREST INCOME AND GAIN/LOSS RECOGNITION Unamortized
premiums and discounts are recognized in interest income over
the contractual life of the security using the effective interest
method, except for purchased callable debt securities carried at a
premium. For purchased callable debt securities carried at a
premium, the premium is amortized into interest income to the
next call date using the effective interest method. As principal
repayments are received on securities (e.g., mortgage-backed
securities (MBS)), a proportionate amount of the related
premium or discount is recognized in income so that the
effective interest rate on the remaining portion of the security
continues unchanged.
We recognize realized gains and losses on the sale of debt
securities in net gains from trading and securities within
noninterest income using the specific identification method.
IMPAIRMENT AND CREDIT LOSSES Unrealized losses on AFS debt
securities are driven by a number of factors, including changes in
interest rates and credit spreads which impact most types of
debt securities, and prepayment rates which impact MBS and
collateralized loan obligations (CLO). Additional considerations
for certain types of AFS debt securities include:
• Debt securities of U.S. Treasury and federal agencies,
including federal agency MBS, are not impacted by credit
movements given the explicit or implicit guarantees
provided by the U.S. government.
• Debt securities of U.S. states and political subdivisions are
most impacted by changes in the relationship between
municipal and term funding credit curves rather than by
changes in the credit quality of the underlying securities.
• Structured securities, such as MBS and CLO, are also
impacted by changes in projected collateral losses of assets
underlying the security.
For AFS debt securities where fair value is less than
amortized cost basis, we recognize impairment in earnings if we
have the intent to sell the security or if it is more likely than not
that we will be required to sell the security before recovery of its
amortized cost basis. Impairment is recognized in net gains on
Wells Fargo & Company 92
trading and securities within noninterest income equal to the
difference between the amortized cost basis, net of ACL, and the
fair value of the AFS debt security. Following the recognition of
this impairment, the AFS debt security’s new amortized cost
basis is fair value.
For AFS debt securities where fair value is less than
amortized cost basis where we did not recognize impairment in
earnings, we record an ACL as of the balance sheet date to the
extent unrealized loss is due to credit losses. See the “Allowance
for Credit Losses” section in this Note for our accounting policies
relating to the ACL for debt securities, which also includes debt
securities classified as HTM.
TRANSFERS BETWEEN C ATEGORIES OF DEBT S ECURITIES Transfers
of debt securities from the AFS to HTM classification are
recorded at fair value, and accordingly the amortized cost of t he
security transferred to HTM is adjusted to fair value . Unrealized
gains or losses reported in AOCI at the transfer date are
amortized into earnings over the same period as the unamortize d
premiums and discounts using the effective interest method.
Any ACL previously recorded under the AFS debt security model
is reversed and an ACL under the HTM debt security model is re -
established. The reversal and re-establishment of the ACL are
recorded in provision for credit losses.
Transfers of debt securities from the HTM to AFS
classification are recorded at fair value. The HTM amortized co st
(excluding any ACL previously recorded under the HTM debt
security model) becomes the AFS amortized cost, and the debt
security is remeasured at fair value with the unrealized gains and
losses reported in OCI. Any ACL previously recorded under the
HTM debt security model is reversed and an ACL under the AFS
debt security model is re-established. The reversal and re -
establishment of the ACL are recorded in provision expense .
Transfers from HTM to AFS are only expected to occur under
limited circumstances.
NONACCRUAL AND PAST DUE, AND CHARGE-OFF POLICIES We
generally place debt securities on nonaccrual status using factors
similar to those described for loans. When we place a debt
security on nonaccrual status, we reverse the accrued unpaid
interest receivable against interest income and suspend the
amortization of premiums and accretion of discounts. If the
ultimate collectability of the principal is in doubt on a nonaccrual
debt security, any cash collected is first applied to reduce the
security’s amortized cost basis to zero, followed by recovery of
amounts previously charged off, and subsequently to interest
income. Generally, we return a debt security to accrual status
when all delinquent interest and principal become current under
the contractual terms of the security and collectability of
remaining principal and interest is no longer doubtful.
Our debt securities are considered past due when
contractually required principal or interest payments have not
been made on the due dates.
Our charge-off policy for debt securities are similar to those
described for loans. Subsequent to charge-off, the debt security
will be designated as nonaccrual and follow the process described
above for any cash received.
Securities and Other Collateralized Financing
Agreements
Resale and repurchase agreements, as well as securities
borrowing and lending agreements, are accounted for as
collateralized financing transactions and are recorded at the
acquisition or sale price plus accrued interest. We monitor the
fair value of securities or other assets purchased and sold as well
as the collateral pledged and received. Additional collateral is
pledged or returned to maintain the appropriate collateral
position for the transactions. These financing transactions do not
create material credit risk given the collateral provided and the
related monitoring process.
We include securities purchased under securities financing
agreements in federal funds sold and securities purchased under
resale agreements on our consolidated balance sheet. We include
collateral other than securities purchased under resale
agreements in Loans on our consolidated balance sheet. We
include securities sold under securities financing agreements in
short-term borrowings on our consolidated balance sheet. At
December 31, 2022 and 2021, short-term borrowings were
primarily comprised of federal funds purchased and securities
sold under agreements to repurchase.
Assets and liabilities arising from securities and other
collateralized financing transactions with a single counterparty
are presented net on the balance sheet provided they meet
certain criteria that permit balance sheet netting. See Note 18
(Pledged Assets and Collateral) for additional information on our
offsetting policy.
Loans Held for Sale
Loans held for sale (LHFS) generally includes commercial and
residential mortgage loans originated or purchased for sale in the
securitization or whole loan market. We have elected the fair
value option for a majority of residential LHFS (see Note 15 (Fair
Values of Assets and Liabilities)). The remaining residential LHFS
are held at the lower of cost or fair value (LOCOM) and are
measured on a pool level basis.
Commercial LHFS are generally held at LOCOM and are
measured on an individual loan basis. We have elected the fair
value option for certain commercial loans included in LHFS that
are used in market-making activities for our trading business.
Gains and losses on residential and commercial mortgage
LHFS are generally recorded in mortgage banking noninterest
income. Gains and losses on trading LHFS are recognized in net
gains from trading activities. Gains and losses on other LHFS are
recognized in other noninterest income. Direct loan origination
costs and fees for LHFS under the fair value option are
recognized in earnings at origination. For LHFS recorded at
LOCOM, direct loan origination costs and fees are deferred at
origination and are recognized in earnings at time of sale.
Interest income on LHFS is calculated based upon the note rate
of the loan and is recorded in interest income.
Commitments to originate mortgage LHFS are accounted
for as derivatives and are measured at fair value. When a
determination is made at the time of commitment to originate
loans as held for investment, it is our intent to hold these loans to
maturity or for the foreseeable future, subject to periodic review
under our management evaluation processes, including
corporate asset/liability management. If subsequent changes
occur, including changes in interest rates, our business strategy,
or other market conditions, we may change our
intent to hold these loans. When management makes this
determination, we immediately transfer these loans to the LHFS
portfolio at LOCOM.
Loans
Loans are reported at their outstanding principal balances net of
any unearned income, cumulative charge-offs, unamortized
deferred fees and costs on originated loans and unamortized
premiums or discounts on purchased loans.
Unearned income, deferred fees and costs, and discounts
and premiums are amortized to interest income generally over
Wells Fargo & Company 93
Note 1: Summary of Significant Accounting Policies (continued)
the contractual life of the loan using the effective interest
method. Loan commitment fees collected at closing are deferred
and amortized to noninterest income on a straight-line basis
over the commitment period if loan funding is unlikely. Upon
funding, deferred loan commitment fees are amortized to
interest income over the contractual life of the loan.
Loans also include financing leases where we are the lessor
(see the “Leasing Activity” section in this Note for our accounting
policy for leases) and resale agreements involving collateral other
than securities (see “Securities and Other Collateralized
Financing Agreements” section in this Note for our accounting
policy for other collateralized financing agreements).
See Note 5 (Loans and Related Allowance for Credit Losses)
for additional information regarding our accounting for loans.
NONACCRUAL AND PAST DUE LOANS We generally place loans on
nonaccrual status when:
• the full and timely collection of interest or principal becomes
uncertain (generally based on an assessment of the
borrower’s financial condition and the adequacy of collateral,
if any), such as in bankruptcy or other circumstances;
• they are 90 days (120 days with respect to residential
mortgage loans) past due for interest or principal, unless the
loan is both well-secured and in the process of collection;
• part of the principal balance has been charged off; or
• for junior lien mortgage loans, we have evidence that the
related first lien mortgage may be 120 days past due or in
the process of foreclosure regardless of the junior lien
delinquency status.
Credit card loans are not placed on nonaccrual status, but are
generally fully charged off when the loan reaches 180 days past
due.
When we place a loan on nonaccrual status, we reverse the
accrued unpaid interest receivable against interest income and
suspend amortization of any net deferred fees. If the ultimate
collectability of the recorded loan balance is in doubt on a
nonaccrual loan, the cost recovery method is used and cash
collected is applied to first reduce the carrying value of the loan
to zero and then as a recovery of prior charge-offs. Otherwise,
interest income may be recognized to the extent cash is received.
Generally, we return a loan to accrual status when all delinquent
interest and principal become current under the terms of the
loan agreement and collectability of remaining principal and
interest is no longer doubtful.
We may re-underwrite modified loans at the time of a
restructuring to determine if there is sufficient evidence of
sustained repayment capacity based on the borrower’s financial
strength, including documented income, debt to income ratios
and other factors. If the borrower has demonstrated
performance under the previous terms and the underwriting
process shows the capacity to continue to perform under the
restructured terms, the loan will generally remain in accruing
status. When a loan classified as a troubled debt restructuring
(TDR) performs in accordance with its modified terms, the loan
either continues to accrue interest (for performing loans) or will
return to accrual status after the borrower demonstrates a
sustained period of performance (generally six consecutive
months of payments, or equivalent, inclusive of consecutive
payments made prior to the modification). Loans will be placed
on nonaccrual status and a corresponding charge-off is recorded
if the re-underwriting did not include an evaluation of the
borrower’s ability to repay or we believe it is probable that
principal and interest contractually due under the modified terms
of the agreement will not be collectible.
Our loans are considered past due when contractually
required principal or interest payments have not been made on
the due dates.
LOAN CHARGE-OFF POLICIES For commercial loans, we generally
fully charge off or charge down to net realizable value (fair value
of collateral, less estimated costs to sell) for loans secured by
collateral when:
• management judges the loan to be uncollectible;
• repayment is deemed to be protracted beyond reasonable
time frames;
• the loan has been classified as a loss by either our internal
loan review process or our banking regulatory agencies;
• the customer has filed bankruptcy and the loss becomes
evident owing to a lack of assets;
• the loan is 180 days past due unless both well-secured and in
the process of collection; or
• the loan is probable of foreclosure, and we have received an
appraisal of less than the recorded loan balance.
For consumer loans, we fully charge off or charge down to
net realizable value when deemed uncollectible due to
bankruptcy or other factors, or no later than reaching a defined
number of days past due, as follows:
• Residential mortgage loans – We generally charge down to
net realizable value when the loan is 180 days past due and
fully charge-off when the loan exceeds extended
delinquency dates.
• Auto loans – We generally fully charge off when the loan is
120 days past due.
• Credit card loans – We generally fully charge off when the
loan is 180 days past due.
• Unsecured loans – We generally fully charge off when the
loan is 120 days past due.
• Unsecured lines – We generally fully charge off when the
loan is 180 days past due.
• Other secured loans – We generally fully or partially charge
down to net realizable value when the loan is 120 days past
due.
TROUBLED DEBT RESTRUCTURINGS In situations where, for
economic or legal reasons related to a borrower’s financial
difficulties, we grant a concession for other than an insignificant
period of time to the borrower that we would not otherwise
consider, the related loan is classified as a troubled debt
restructuring (TDR). These modified terms may include interest
rate reductions, principal forgiveness, term extensions, payment
forbearance and other actions intended to minimize our
economic loss and to avoid foreclosure or repossession of the
collateral, if applicable. For modifications where we forgive
principal, the entire amount of such principal forgiveness is
immediately charged off. If the underwriting for a TDR
modification did not include an evaluation of the borrower’s
ability to repay, the loan is deemed collateral dependent. Other
than resolutions such as foreclosures, sales and transfers to held-
for-sale, we may remove loans held for investment from TDR
classification, but only if they have been refinanced or
restructured at market terms and qualify as a new loan.
TROUBLED DEBT RESTRUCTURINGS AND OTHER RELIEF RELATED
TO COVID-19 The Coronavirus, Aid, Relief, and Economic Security
Act (the CARES Act) and the Interagency Statement on Loan
Modifications and Reporting for Financial Institutions Working with
Customers Affected by the Coronavirus (Revised) issued by federal
regulators in April 2020 (the Interagency Statement) provide
Wells Fargo & Company 94
optional, temporary relief from accounting for certain loan
modifications as TDRs. Based on guidance in the CARES Act and
Interagency Statement, modifications related to the adverse
effects of Coronavirus Disease 2019 (COVID-19) that meet
certain criteria are exempt from TDR classification. We ceased
applying TDR relief provided by the CARES Act upon the
expiration of the CARES Act on January 1, 2022. During 2022, we
continued to apply the TDR relief provided by the Interagency
Statement for eligible COVID-related residential mortgage loan
modifications.
For COVID-19-related modifications in the form of payment
deferrals or payment forbearance, delinquency status will not
advance and loans that were accruing at the time the relief is
provided will generally not be placed on nonaccrual status during
the deferral period. Interest accrued during payment deferrals or
payment forbearance may be included in the principal balance of
the loans and charge-offs will generally be based on delinquency
status after the loan exits the deferral or forbearance period.
Loans that exit COVID-related deferrals or payment forbearance
are placed on nonaccrual status if there is no evidence that the
borrower can resume making payments or if the borrower
requests additional modifications.
FORECLOSED ASSETS Foreclosed assets obtained through our
lending activities primarily include real estate. Generally, loans
have been written down to their net realizable value prior to
foreclosure. Any further reduction to their net realizable value is
recorded with a charge to the ACL at foreclosure. We allow up to
90 days after foreclosure to finalize determination of net
realizable value. Thereafter, changes in net realizable value are
recorded to noninterest expense. The net realizable value of
these assets is reviewed and updated periodically depending on
the type of property. Certain government-guaranteed mortgage
loans upon foreclosure are included in accounts receivable, not
foreclosed assets. These receivables were loans insured by the
Federal Housing Administration (FHA) or guaranteed by the
Department of Veterans Affairs (VA) and are measured based on
the balance expected to be recovered from the FHA or VA.
Allowance for Credit Losses
The ACL is management’s estimate of the current expected life -
time credit losses in the loan portfolio and unfunded credit
commitments, at the balance sheet date, excluding loans and
unfunded credit commitments carried at fair value or held for
sale. Additionally, we maintain an ACL for AFS and HTM debt
securities, other financing receivables measured at amortized
cost, and other off-balance sheet credit exposures. While we
attribute portions of the allowance to specific financial asse t
classes (loan and debt security portfolios), loan portfolio
segments (commercial and consumer) or major security type, the
entire ACL is available to absorb credit losses of the Company .
Our ACL process involves procedures to appropriately
consider the unique risk characteristics of our financial asset
classes, portfolio segments, and major security types. For each
loan portfolio segment and each major HTM debt security type,
losses are estimated collectively for groups of loans or securities
with similar risk characteristics. For loans and securities that do
not share similar risk characteristics with other financial assets,
the losses are estimated individually, which generally includes our
nonperforming large commercial loans and non-accruing HTM
debt securities. For AFS debt securities, losses are estimated at
the individual security level.
Our ACL amounts are influenced by a variety of factors,
including changes in loan and debt security volumes, portfolio
credit quality, and general economic conditions. General
economic conditions are forecasted using economic variables
which will create volatility as those variables change over time.
See Table 1.1 for key economic variables used for our loan
portfolios.
Table 1.1: Key Economic Variables
Loan Portfolio Key economic variables
Total commercial • Gross domestic product
• Commercial real estate asset prices, where applicable
• Unemployment rate
Residential mortgage • Home price index
• Unemployment rate
Other consumer (including credit card, auto, and other consumer) • Unemployment rate
Our approach for estimating expected life-time credit losses
for loans and debt securities includes the following key
components:
• An initial loss forecast period of two years for all portfolio
segments and classes of financing receivables and off-
balance-sheet credit exposures. This period reflects
management’s expectation of losses based on forward-
looking economic scenarios over that time. We forecast
multiple economic scenarios that generally include a base
scenario with an optimistic (upside) and one or more
pessimistic (downside) scenarios, which are weighted by
management to estimate future credit losses.
• Long-term average loss expectations estimated by reverting
to the long-term average, on a linear basis, for each of the
economic variables forecasted during the initial loss forecast
period. These long-term averages are based on observations
over multiple economic cycles. The reversion period, which
may be up to two years, is assessed on a quarterly basis.
• The remaining contractual term of a loan is adjusted for
expected prepayments and certain expected extensions,
renewals, or modifications. We extend the contractual term
when we are not able to unconditionally cancel contractual
renewals or extension options. We also incorporate any
scenarios where we reasonably expect to provide an
extension through a TDR. Credit card loans have
indeterminate maturities, which requires that we determine
a contractual life by estimating the application of future
payments to the outstanding loan amount.
• Utilization of discounted cash flow (DCF) methods to
measure credit impairment for loans modified in a troubled
debt restructuring, unless they are collateral dependent and
measured at the fair value of the collateral. The DCF
methods obtain estimated life-time credit losses using the
initial and historical mean loss forecast periods described
above.
• For AFS debt securities and certain beneficial interests
classified as HTM, we utilize DCF methods to measure the
Wells Fargo & Company 95
Note 1: Summary of Significant Accounting Policies (continued)
ACL, which incorporate expected credit losses using the
conceptual components described above. For most HTM
debt securities, the ACL is measured using an expected loss
model, similar to the methodology used for loans.
The ACL for financial assets held at amortized cost is a
valuation account that is deducted from, or added to, the
amortized cost basis of the financial assets to present the net
amount expected to be collected. When credit expectations
change, the valuation account is adjusted with changes reported
in provision for credit losses. If amounts previously charged off
are subsequently expected to be collected, we may recognize a
negative allowance, which is limited to the amount that was
previously charged off. For financial assets with an ACL
estimated using DCF methods, changes in the ACL due to the
passage of time are recorded in interest income. The ACL for AFS
debt securities reflects the amount of unrealized loss related to
expected credit losses, limited by the amount that fair value is
less than the amortized cost basis (fair value floor) and cannot
have an associated negative allowance.
For certain financial assets, such as residential real estate
loans guaranteed by the Government National Mortgage
Association (GNMA), an agency of the federal government, U. S.
Treasury and Agency mortgage-backed debt securities and
certain sovereign debt securities, the Company has not
recognized an ACL as our expectation of loss is zero, based on
historical losses and consideration of current and forecasted
conditions.
For financial assets that are collateral-dependent, we will
measure the ACL based on the fair value of the collateral. If we
intend to sell the underlying collateral, we will measure the ACL
based on the collateral’s net realizable value. In most situations,
based on our charge-off policies, we will immediately write-down
the financial asset to the fair value of the collateral or net
realizable value. For consumer loans, collateral-dependent
financial assets may have collateral in the form of residential real
estate, autos or other personal assets. For commercial loans,
collateral-dependent financial assets may have collateral in the
form of commercial real estate or other business assets.
We do not generally record an ACL for accrued interest
receivables because uncollectible accrued interest is reversed
through interest income in a timely manner in line with our non-
accrual and past due policies for loans and debt securities. For
consumer credit card and certain consumer lines of credit, we
include an ACL for accrued interest and fees since these loans are
neither placed on nonaccrual status nor written off until the loan
is 180 days past due. Accrued interest receivables are included in
other assets, except for certain revolving loans, such as credit
card loans.
COMMERCIAL LOAN PORTFOLIO S EGMENT AC L METHODOLOGY
Generally, commercial loans, which include net investments in
lease financing, are assessed for estimated losses by grading each
loan using various risk factors as identified through periodic
reviews. Our estimation approach for the commercial portfolio
reflects the estimated probability of default in accordance with
the borrower’s financial strength and the severity of loss in the
event of default, considering the quality of any underlying
collateral. Probability of default, loss severity at the time of
default, and exposure at default are statistically derived through
historical observations of default and losses after default within
each credit risk rating. These estimates are adjusted as
appropriate for risks identified from current and forecasted
economic conditions and credit quality trends. Unfunded credit
commitments are evaluated based on a conversion factor to
derive a funded loan equivalent amount. The estimated
probability of default and loss severity at the time of default are
applied to the funded loan equivalent amount to estimate losses
for unfunded credit commitments.
CONSUMER LOAN PORTFOLIO SEGMENT ACL METHODOLOGY For
consumer loans, we determine the allowance using a pooled
approach based on the individual risk characteristics of the loans
within those pools. Quantitative modeling methodologies that
estimate probability of default, loss severity at the time of
default and exposure at default are typically leveraged to
estimate expected loss. These methodologies pool loans,
generally by product types with similar risk characteristics, such
as residential real estate mortgages, auto loans and credit cards.
As appropriate and to achieve greater accuracy, we may further
stratify selected portfolios by sub-product, risk pool, loss type,
geographic location and other predictive characteristics. We use
attributes such as delinquency status, Fair Isaac Corporation
(FICO) scores, and loan-to-value ratios (where applicable) in the
development of our consumer loan models, in addition to home
price trends, unemployment trends, and other economic
variables that may influence the frequency and severity of losses
in the consumer portfolio.
OTHER QUALITATIVE FACTORS The ACL includes amounts for
qualitative factors which may not be adequately reflected in our
loss models. These amounts represent management’s judgment
of risks in the processes and assumptions used in establishing the
ACL. Generally, these amounts are established at a granular level
below our loan portfolio segments. We also consider economic
environmental factors, modeling assumptions and performance,
process risk, and other subjective factors, including industry
trends and emerging risk assessments.
OFF-BALANCE SHEET CREDIT EXPOSURES Our off-balance sheet
credit exposures include unfunded loan commitments (generally
in the form of revolving lines of credit), financial guarantees not
accounted for as insurance contracts or derivatives, including
standby letters of credit, and other similar instruments. For off-
balance sheet credit exposures, we recognize an ACL associated
with the unfunded amounts. We do not recognize an ACL for
commitments that are unconditionally cancelable at our
discretion. Additionally, we recognize an ACL for financial
guarantees that create off-balance sheet credit exposure, such as
loans sold with credit recourse and factoring guarantees. ACL for
off-balance sheet credit exposures are reported as a liability in
accrued expenses and other liabilities on our consolidated
balance sheet.
OTHER FINANCIAL ASSETS Other financial assets are evaluated
for expected credit losses. These other financial assets include
accounts receivable for fees, receivables from government-
sponsored entities, such as Federal National Mortgage
Association (FNMA) and Federal Home Loan Mortgage
Corporation (FHLMC), and GNMA, and other accounts
receivables from high-credit quality counterparties, such as
central clearing counterparties. Many of these financial assets are
generally not expected to have an ACL as there is a zero loss
expectation (e.g., government guarantee) based on no historical
credit losses and consideration of current and forecasted
conditions. Some financial assets, such as loans to employees,
maintain an ACL that is presented on a net basis with the related
amortized cost amounts in other assets on our consolidated
balance sheet. A provision for credit losses is not recognized
Wells Fargo & Company 96
separately from the regular income or expense associated with
these financial assets.
Securities purchased under resale agreements are generally
over-collateralized by securities or cash and are generally short-
term in nature. We have elected the practical expedient for these
financial assets given collateral maintenance provisions. These
provisions require that we monitor the collateral value and
customers are required to replenish collateral, if needed.
Accordingly, we generally do not maintain an ACL for these
financial assets.
See Note 5 (Loans and Related Allowance for Credit Losses)
for additional information.
Purchased Credit Deteriorated Financial Assets
Financial assets acquired that are of poor credit quality and with
more than an insignificant evidence of credit deterioration since
their origination or issuance are purchased credit deteriorated
(PCD) assets. PCD assets include HTM and AFS debt securities
and loans. PCD assets are recorded at their purchase price plus an
ACL estimated at the time of acquisition. Under this approach,
there is no provision for credit losses recognized at acquisition;
rather, there is a gross-up of the purchase price of the financial
asset for the estimate of expected credit losses and a
corresponding ACL recorded. Changes in estimates of expected
credit losses after acquisition are recognized as provision for
credit losses in subsequent periods. In general, interest income
recognition for PCD financial assets is consistent with interest
income recognition for the similar non-PCD financial asset.
Leasing Activity
AS LESSOR We lease equipment to our customers under
financing or operating leases. Financing leases, which includes
both direct financing and sales-type leases, are presented in
loans and are recorded at the discounted amounts of lease
payments receivable plus the estimated residual value of the
leased asset. Leveraged leases, which are a form of financing
leases, are reduced by related non-recourse debt from third-
party investors. Lease payments receivable reflect contractual
lease payments adjusted for renewal or termination options that
we believe the customer is reasonably certain to exercise. The
residual value reflects our best estimate of the expected sales
price for the equipment at lease termination based on sales
history adjusted for recent trends in the expected exit markets.
Many of our leases allow the customer to extend the lease at
prevailing market terms or purchase the asset for fair value at
lease termination.
Our allowance for loan losses for financing leases considers
both the collectability of the lease payments receivable as well as
the estimated residual value of the leased asset. We typically
purchase residual value insurance on our financing leases to
reduce the risk of loss at lease termination.
In connection with a lease, we may finance the customer’s
purchase of other products or services from the equipment
vendor and allocate the contract consideration between the use
of the asset and the purchase of those products or services.
Amounts allocated are reported in loans as commercial and
industrial loans, rather than as lease financing.
Our primary income from financing leases is interest income
recognized using the effective interest method. Variable lease
revenue, such as reimbursement for property taxes, are included
in lease income within noninterest income.
Operating lease assets are presented in other assets, net of
accumulated depreciation. Periodic depreciation expense is
recorded on a straight-line basis over the estimated useful life of
the leased asset and are included in other noninterest expense.
Operating lease assets are reviewed periodically for impairment
and an impairment loss is recognized if the carrying amount of
operating lease assets exceeds fair value and is not recoverable.
Recoverability is evaluated by comparing the carrying amount of
the leased assets to undiscounted cash flows expected through
the operation or sale of the asset. Impairment charges for
operating lease assets are included in other noninterest income.
Operating lease rental income for leased assets is recognized
in lease income within noninterest income on a straight-line basis
over the lease term. Variable revenue on operating leases include
reimbursements of costs, including property taxes, which
fluctuate over time, as well as rental revenue based on usage. For
leases of railcars, revenue for maintenance services provided
under the lease is recognized in lease income.
We elected to exclude from revenue and expenses any sales
tax incurred on lease payments which are reimbursed by the
lessee. Substantially all of our leased assets are protected against
casualty loss through third-party insurance.
AS LESSEE We enter into lease agreements to obtain the right to
use assets for our business operations, substantially all of which
are real estate. Lease liabilities and right-of-use (ROU) assets are
recognized when we enter into operating or financing leases and
represent our obligations and rights to use these assets over the
period of the leases and may be re-measured for certain
modifications.
Operating lease liabilities include fixed and in-substance
fixed payments for the contractual duration of the lease,
adjusted for renewals or terminations which were considered
probable of exercise when measured. The lease payments are
discounted using a rate that approximates a collateralized
borrowing rate for the estimated duration of the lease as the
implicit discount rate is typically not known. The discount rate is
updated when re-measurement events occur. The related
operating lease ROU assets may differ from operating lease
liabilities due to initial direct costs, deferred or prepaid lease
payments and lease incentives.
We present operating lease liabilities in accrued expenses
and other liabilities and the related operating lease ROU assets in
other assets. The amortization of operating lease ROU assets
and the accretion of operating lease liabilities are reported
together as fixed lease expense and are included in occupancy
expense within noninterest expense. The fixed lease expense is
recognized on a straight-line basis over the life of the lease.
Some operating leases include variable lease payments and
are recognized as incurred in net occupancy expense within
noninterest expense.
For substantially all of our leased assets, we account for
consideration paid under the contract for maintenance or other
services as lease payments. We exclude certain asset classes, with
original terms of less than one year from the operating lease
ROU assets and lease liabilities. The related short-term lease
expense is included in net occupancy expense.
Finance lease liabilities are presented in long-term debt and
the associated finance ROU assets are presented in premises and
equipment.
See Note 8 (Leasing Activity) for additional information.
Deposits, Short-term Borrowings and Long-term Debt
Customer deposits, short-term borrowings, and long-term debt
are recorded at amortized cost, unless we have elected the fair
value option for these items. For example, we may elect the fair
value option for certain structured notes. We generally report
borrowings with original maturities of one year or less as short-
term borrowings and borrowings with original maturities of
Wells Fargo & Company 97
Note 1: Summary of Significant Accounting Policies (continued)
greater than one year as long-term debt on our consolidated
balance sheet. We do not reclassify long-term debt to short-
term borrowings within a year of maturity.
Refer to Note 9 (Deposits) for further information on
deposits, Note 10 (Long-Term Debt) for further information on
long-term debt, and Note 15 (Fair Values of Assets and
Liabilities) for additional information on fair value, including fair
value option elections.
Securitizations and Beneficial Interests
Securitizations are transactions in which financial assets are sold
to a Special Purpose Entity (SPE), which then issues beneficial
interests collateralized by the transferred financial assets.
Beneficial interests are generally issued in the form of senior and
subordinated interests, and in some cases, we may obtain
beneficial interests issued by the SPE. Additionally, from time to
time, we may re-securitize certain financial assets in a new
securitization transaction. See Note 16 (Securitizations and
Variable Interest Entities) for additional information about our
involvement with SPEs.
The assets and liabilities transferred to a SPE are excluded
from our consolidated balance sheet if the transfer qualifies
as a sale and we are not required to consolidate the SPE.
For transfers of financial assets recorded as sales, we
recognize and initially measure at fair value all assets obtained
(including beneficial interests or mortgage servicing rights) and
all liabilities incurred. We record a gain or loss in noninterest
income for the difference between assets obtained (net of
liabilities incurred) and the carrying amount of the assets sold.
Beneficial interests obtained from, and liabilities incurred in,
securitizations with off-balance sheet entities may include debt
and equity securities, loans, MSRs, derivative assets and
liabilities, other assets, and other obligations such as liabilities
for mortgage repurchase losses or long-term debt and are
accounted for as described within this Note.
Mortgage Servicing Rights
We recognize MSRs resulting from a sale or securitization of
mortgage loans that we originate (asset transfers) or through a
direct purchase of such rights. We initially record all of our MSRs
at fair value. Subsequently, residential loan MSRs are carried at
fair value. Commercial MSRs are subsequently measured at
LOCOM. The valuation and sensitivity of MSRs is discussed
further in Note 6 (Mortgage Banking Activities), Note 15 (Fair
Values of Assets and Liabilities) and Note 16 (Securitizations and
Variable Interest Entities).
For MSRs carried at fair value, changes in fair value are
reported in mortgage banking noninterest income in the period
in which the change occurs. MSRs subsequently measured at
LOCOM are amortized in proportion to, and over the period of,
estimated net servicing income. The amortization of MSRs is
reported in mortgage banking noninterest income, analyzed
monthly and adjusted to reflect changes in prepayment rates, as
well as other factors.
MSRs accounted for at LOCOM are periodically evaluated
for impairment based on the fair value of those assets. For
purposes of impairment evaluation and measurement, we
stratify MSRs based on the predominant risk characteristics of
the underlying loans, including investor and product type. If, by
individual stratum, the carrying amount of these MSRs exceeds
fair value, a valuation allowance is established. The valuation
allowance is adjusted as the fair value changes.
Premises and Equipment
Premises and equipment are carried at cost less accumulated
depreciation and amortization. We use the straight-line method
of depreciation and amortization. Depreciation and amortization
expense for premises and equipment was $1.2 billion in 2022 and
$1.4 billion in both 2021 and 2020. Estimated useful lives range
up to 40 years for buildings and improvements, up to 10 years
for furniture and equipment, and the shorter of the estimated
useful life (up to 8 years) or the lease term for leasehold
improvements.
Goodwill and Identifiable Intangible Assets
Goodwill is recorded for business combinations when the
purchase price is higher than the fair value of the acquired net
assets, including identifiable intangible assets.
We assess goodwill for impairment at a reporting unit level
on an annual basis or more frequently in certain circumstances.
We have determined that our reporting units are at the
reportable operating segment level or one level below. We
identify the reporting units based on how the segments and
reporting units are managed, taking into consideration the
economic characteristics, nature of the products and services,
and customers of the segments and reporting units. We allocate
goodwill to applicable reporting units based on their relative fair
value at the time we acquire a business and when we have a
significant business reorganization. If we sell a business, a portion
of goodwill is included with the carrying amount of the divested
business.
We have the option of performing a qualitative assessment
of goodwill. We may also elect to bypass the qualitative test and
proceed directly to a quantitative test. If we perform a qualitative
assessment of goodwill to test for impairment and conclude it is
more likely than not that a reporting unit’s fair value is greater
than its carrying amount, quantitative tests are not required.
However, if we determine it is more likely than not that a
reporting unit’s fair value is less than its carrying amount, we
complete a quantitative assessment to determine if there is
goodwill impairment. We apply various quantitative valuation
methodologies, including discounted cash flow and earnings
multiple approaches, to determine the estimated fair value,
which is compared with the carrying value of each reporting unit.
A goodwill impairment loss is recognized if the fair value is less
than the carrying amount, including goodwill. The goodwill
impairment loss is limited to the amount of goodwill allocated to
the reporting unit. We recognize impairment losses as a charge
to other noninterest expense and a reduction to the carrying
value of goodwill. Subsequent reversals of goodwill impairment
are prohibited.
We amortize customer relationship intangible assets on an
accelerated basis over useful lives not exceeding 10 years. We
review intangible assets for impairment whenever events or
changes in circumstances indicate that their carrying amounts
may not be recoverable. Impairment is indicated if the sum of
undiscounted estimated future net cash flows is less than the
carrying value of the asset. Impairment is permanently
recognized by writing down the asset to the extent that the
carrying value exceeds the estimated fair value.
Derivatives and Hedging Activities
DERIVATIVES We recognize all derivatives on our consolidated
balance sheet at fair value. On the date we enter into a derivative
contract, we categorize the derivative as either an accounting
hedge, economic hedge or part of our customer accommodation
trading and other portfolio.
Wells Fargo & Company 98
Accounting hedges are either fair value or cash flow hedges.
Fair value hedges represent the hedge of the fair value of a
recognized asset or liability or an unrecognized firm
commitment, including hedges of foreign currency exposure.
Cash flow hedges represent the hedge of a forecasted
transaction or the variability of cash flows to be paid or received
related to a recognized asset or liability.
Economic hedges and customer accommodation trading and
other derivatives do not qualify for, or we have elected not to
apply, hedge accounting. Economic hedges are derivatives we
use to manage interest rate, foreign currency and certain other
risks associated with our non-trading activities. Customer
accommodation trading and other derivatives predominantly
represents derivatives related to our trading business activities.
We report changes in the fair values of these derivatives in
noninterest income or noninterest expense.
FAIR VALUE HEDGES We record changes in the fair value of the
derivative in income, except for certain derivatives in which a
portion is recorded to OCI. We record basis adjustments to the
amortized cost of the hedged asset or liability due to the changes
in fair value related to the hedged risk with the offset recorded in
earnings. We present derivative gains or losses in the same
income statement category as the hedged asset or liability, as
follows:
• For fair value hedges of interest rate risk, amounts are
reflected in net interest income;
• For hedges of foreign currency risk, amounts representing
the fair value changes less the accrual for periodic cash flow
settlements are reflected in noninterest income. The
periodic cash flow settlements are reflected in net interest
income;
• For hedges of both interest rate risk and foreign currency
risk, amounts representing the fair value change less the
accrual for periodic cash flow settlements is attributed to
both net interest income and noninterest income. The
periodic cash flow settlements are reflected in net interest
income.
The entire derivative gain or loss is included in the
assessment of hedge effectiveness for all fair value hedge
relationships, except for hedges of foreign-currency
denominated AFS debt securities and long-term debt liabilities
hedged with cross-currency swaps. The change in fair value of
these swaps attributable to cross-currency basis spread changes
is excluded from the assessment of hedge effectiveness. The
initial fair value of the excluded component is amortized to net
interest income and the difference between changes in fair value
of the excluded component and the amount recorded in earnings
is recorded in OCI.
CASH FLOW HEDGES We record changes in the fair value of the
derivative in OCI. We subsequently reclassify gains and losses
from these changes in fair value from OCI to earnings in the same
period(s) that the hedged transaction affects earnings and in the
same income statement category as the hedged item. The entire
gain or loss on these derivatives is included in the assessment of
hedge effectiveness.
DOCUMENTATION AND EFFECTIVENESS ASSESSMENT FOR
ACCOUNTING HEDGES For fair value and cash flow hedges
qualifying for hedge accounting, we formally document at
inception the relationship between hedging instruments and
hedged items, our risk management objective, strategy and our
evaluation of effectiveness for our hedge transactions. This
process includes linking all derivatives designated as fair value or
cash flow hedges to specific assets and liabilities on our
consolidated balance sheet or to specific forecasted transactions.
We assess hedge effectiveness using regression analysis, both at
inception of the hedging relationship and on an ongoing basis.
For fair value hedges, the regression analysis involves regressing
the periodic change in fair value of the hedging instrument
against the periodic changes in fair value of the asset or liability
being hedged due to changes in the hedged risk(s). For cash flow
hedges, the regression analysis involves regressing the periodic
changes in fair value of the hedging instrument against the
periodic changes in fair value of a hypothetical derivative. The
hypothetical derivative has terms that identically match and
offset the cash flows of the forecasted transaction being hedged
due to changes in the hedged risk(s). The initial assessment for
fair value and cash flow hedges includes an evaluation of the
quantitative measures of the regression results used to validate
the conclusion of high effectiveness. Periodically, as required, we
also formally assess whether the derivative we designated in
each hedging relationship is expected to be and has been highly
effective in offsetting changes in fair values or cash flows of the
hedged item using the regression analysis method.
DISCONTINUING HEDGE ACCOUNTING We discontinue hedge
accounting prospectively when (1) a derivative is no longer highly
effective in offsetting changes in the fair value or cash flows of a
hedged item, (2) a derivative expires or is sold, terminated or
exercised, (3) we elect to discontinue hedge accounting, or (4)
when the forecasted transaction is no longer probable of
occurring in a cash flow hedge.
When we discontinue fair value hedge accounting, we no
longer adjust the previously hedged asset or liability for changes
in fair value. The remaining cumulative adjustments to the
hedged item and accumulated amounts reported in OCI are
accounted for in the same manner as other components of the
carrying amount of the asset or liability. For example, for financial
debt instruments such as AFS debt securities, loans or long-term
debt, these amounts are amortized into net interest income over
the remaining life of the asset or liability similar to other
amortized cost basis adjustments. If the hedged item is
derecognized, the accumulated amounts reported in OCI are
immediately reclassified to net interest income. If the derivative
continues to be held after fair value hedge accounting ceases, we
carry the derivative on the consolidated balance sheet at its fair
value with changes in fair value included in noninterest income.
When we discontinue cash flow hedge accounting and it is
probable that the forecasted transaction will occur, the
accumulated amount reported in OCI at the de-designation date
continues to be reported in OCI until the forecasted transaction
affects earnings at which point the related OCI amount is
reclassified to net interest income. If cash flow hedge accounting
is discontinued and it is probable the forecasted transaction will
no longer occur, the accumulated gains and losses reported in
OCI at the de-designation date is immediately reclassified to
noninterest income. If the derivative continues to be held after
cash flow hedge accounting ceases, we carry the derivative on our
consolidated balance sheet at its fair value with changes in fair
value included in noninterest income.
EMBEDDED DERIVATIVES We may purchase or originate financial
instruments that contain an embedded derivative. At inception
of the financial instrument, we assess (1) if the economic
characteristics of the embedded derivative are not clearly and
closely related to the economic characteristics of the host
contract, (2) if the financial instrument that embodies both the
Wells Fargo & Company 99
Note 1: Summary of Significant Accounting Policies (continued)
embedded derivative and the host contract is not measured at
fair value with changes in fair value reported in earnings, and (3) if
a separate instrument with the same terms as the embedded
instrument would meet the definition of a derivative. If the
embedded derivative meets all of these conditions, we separate
it from the hybrid contract by recording the bifurcated derivative
at fair value and the remaining host contract at the difference
between the basis of the hybrid instrument and the fair value of
the bifurcated derivative. The bifurcated derivative is carried at
fair value with changes recorded in noninterest income and
reported on our consolidated balance sheet as a derivative asset
or liability. The accounting for the remaining host contract is the
same as other assets and liabilities of a similar type and reported
on our consolidated balance sheet based upon the accounting
classification of the instrument.
COUNTERPARTY CREDIT RISK AND NETTING By using derivatives,
we are exposed to counterparty credit risk, which is the risk that
counterparties to the derivative contracts do not perform as
expected. If a counterparty fails to perform, our counterparty
credit risk is equal to the amount reported as a derivative asset
on our consolidated balance sheet. The amounts reported as a
derivative asset are derivative contracts in a gain position, and to
the extent subject to legally enforceable master netting
arrangements, net of derivatives in a loss position with the same
counterparty and cash collateral received. We minimize
counterparty credit risk through credit approvals, limits,
monitoring procedures, executing master netting arrangements
and obtaining collateral, where appropriate. Counterparty credit
risk related to derivatives is considered in determining fair value
and our assessment of hedge effectiveness. To the extent
derivatives subject to master netting arrangements meet the
applicable requirements, including determining the legal
enforceability of the arrangement, it is our policy to present
derivative balances and related cash collateral amounts net on
our consolidated balance sheet. We incorporate adjustments to
reflect counterparty credit risk (credit valuation adjustments
(CVA)) in determining the fair value of our derivatives. CVA,
which considers the effects of enforceable master netting
agreements and collateral arrangements, reflects market-based
views of the credit quality of each counterparty. We estimate
CVA based on observed credit spreads in the credit default swap
market and indices indicative of the credit quality of the
counterparties to our derivatives.
Cash collateral exchanged related to our interest rate
derivatives, and certain commodity and equity derivatives, with
centrally cleared counterparties is recorded as a reduction of the
derivative fair value asset and liability balances, as opposed to
separate non-derivative receivables or payables. This cash
collateral, also referred to as variation margin, is exchanged
based upon derivative fair value changes, typically on a one-day
lag. For additional information on our derivatives and hedging
activities, see Note 14 (Derivatives).
Equity Securities
Equity securities exclude investments that represent a
controlling interest in the investee. Marketable equity securities
have readily determinable fair values and are predominantly used
in our trading activities. Marketable equity securities are
recorded at fair value with realized and unrealized gains and
losses recognized in net gains from trading and securities in
noninterest income. Dividend income from marketable equity
securities is recognized in interest income.
Nonmarketable equity securities do not have readily
determinable fair values. These securities are accounted for
under one of the following accounting methods:
• Fair value through net income: This method is an election.
The securities are recorded at fair value with unrealized gains
or losses recognized in net gains from trading and securities
in noninterest income;
• Equity method: This method is applied when we have the
ability to exert significant influence over the investee. The
securities are recorded at cost and adjusted for our share of
the investee’s earnings or losses, less any dividends received
and/or impairments. Equity method adjustments for our
share of the investee’s earnings or losses are recognized in
other noninterest income and dividends are recognized as a
reduction of the investment carrying value;
• Proportional amortization method: This method is applied to
certain low-income housing tax credit (LIHTC) investments.
The investments are initially recorded at cost and amortized
in proportion to the tax credits received. The amortization of
the investments and the related tax impacts are recognized
in income tax expense;
• Cost method: This method is required for specific securities,
such as Federal Reserve Bank stock and Federal Home Loan
Bank stock. These securities are held at cost less any
impairments;
• Measurement alternative: This method is followed by all
remaining nonmarketable equity securities. These securities
are initially recorded at cost and are remeasured to fair value
as of the date of an orderly observable transaction of the
same or similar security of the same issuer. These securities
are also adjusted for impairments.
All realized and unrealized gains and losses, including
impairment losses, from nonmarketable equity securities are
recognized in net gains from trading and securities in noninterest
income. Dividend income from all nonmarketable equity
securities, other than equity method securities, is recognized in
interest income.
Our review for impairment for nonmarketable equity
securities not carried at fair value includes an analysis of the facts
and circumstances of each security, the intent or requirement to
sell the security, the expectations of cash flows, capital needs and
the viability of its business model. When the fair value of an
equity method or cost method investment is less than its
carrying value, we write-down the asset to fair value when we
consider declines in value to be other than temporary. When
the fair value of an investment accounted for using the
measurement alternative is less than its carrying value, we write-
down the asset to fair value, without the consideration of
anticipated recovery.
See Note 4 (Equity Securities) for additional information.
Pension Accounting
We sponsor a frozen noncontributory qualified defined benefit
retirement plan, the Wells Fargo & Company Cash Balance Plan
(Cash Balance Plan), which covers eligible employees of
WellsFargo. We also sponsor nonqualified defined benefit plans
that provide supplemental defined benefit pension benefits to
certain eligible employees. We account for our defined benefit
pension plans using an actuarial model. Principal assumptions
used in determining the net periodic pension cost and the
pension obligation include the discount rate, the expected long-
term rate of return on plan assets and projected mortality rates.
A single weighted-average discount rate is used to estimate
the present value of our future pension benefit obligations. We
Wells Fargo & Company 100
determine the discount rate using a yield curve derived from a
broad-based population of high-quality corporate bonds with
maturity dates that closely match the estimated timing of the
expected benefit payments.
On December 31, 2021, we changed the method used to
estimate the interest cost component of pension expense for our
principal defined benefit and postretirement plans to the full
yield curve approach. The full yield curve approach aligns specific
spot rates along the yield curve to the projected benefit payment
cash flows. This change does not affect the measurement of our
pension obligation as the change in interest cost is offset in the
actuarial gain (loss). We accounted for this change prospectively
as a change in estimate to our pension expense. Previously, we
estimated the interest cost component utilizing a single
weighted-average discount rate. We made this change to
improve the correlation between the yield curve and the
projected benefit payment cash flows.
The determination of our expected long-term rate of return
on plan assets is highly quantitative by nature. We evaluate the
current asset allocations and expected returns using forward-
looking capital market assumptions. We use the resulting
projections to derive a baseline expected rate of return for the
Cash Balance Plan’s prescribed asset mix.
Mortality rate assumptions are based on mortality tables
published by the Society of Actuaries adjusted to reflect our
specific experience.
At year end, we re-measure our defined benefit plan
liabilities and related plan assets and recognize any resulting
actuarial gain or loss in OCI. We generally amortize net actuarial
gain or loss in excess of a 5% corridor from AOCI into net periodic
pension cost over the estimated average remaining participation
period, which at December31, 2022, is 18 years. See Note 21
(Employee Benefits) for additional information on our pension
accounting.
Income Taxes
We file income tax returns in the jurisdictions in which we
operate and evaluate income tax expense in two components:
current and deferred income tax expense. Current income tax
expense represents our estimated taxes to be paid or refunded
for the current period and includes income tax expense related to
uncertain tax positions. Uncertain tax positions that meet the
more likely than not recognition threshold are measured to
determine the amount of benefit to recognize.An uncertain tax
position is measured at the largest amount of benefit that
management believes has a greater than 50% likelihood of
realization upon settlement.Tax benefits not meeting our
realization criteria represent unrecognized tax benefits.
Deferred income taxes are based on the balance sheet
method and deferred income tax expense results from changes
in deferred tax assets and liabilities between periods. Under the
balance sheet method, the net deferred tax asset or liability is
based on the tax effects of the differences between the book and
tax basis of assets and liabilities, and enacted changes in tax rates
and laws are recognized in the period in which they occur.
Deferred tax assets are recognized subject to management’s
judgment that realization is more likely than not. A valuation
allowance reduces deferred tax assets to the realizable amount.
See Note 22 (Income Taxes) to Financial Statements in this
Report for a further description of our provision for income taxes
and related income tax assets and liabilities.
Stock-Based Compensation
Our long-term incentive plans provide awards for employee
services in various forms, such as restricted share rights (RSRs)
and performance share awards (PSAs).
Stock-based awards are measured at fair value on the grant
date. The cost is recognized in personnel expense, net of actual
forfeitures, in our consolidated statement of income normally
over the vesting period of the award; awards with graded vesting
are expensed on a straight-line method. Awards to employees
who are retirement eligible at the grant date are subject to
immediate expensing upon grant. Awards to employees who
become retirement eligible before the final vesting date are
expensed between the grant date and the date the employee
becomes retirement eligible. Except for retirement and other
limited circumstances, RSRs are canceled when employment
ends.
PSAs and certain RSRs granted in 2020 included
discretionary conditions that can result in forfeiture and are
measured at fair value initially and subsequently until the
discretionary conditions end. For these awards, the associated
compensation expense fluctuates with changes in our stock
price. Awards granted in 2022 and 2021 no longer included these
discretionary conditions and are not adjusted for subsequent
changes in stock price. For PSAs, compensation expense also
fluctuates based on the estimated outcome of meeting the
performance conditions.The total expense that will be
recognized on these awards is finalized upon the completion of
the performance period.
For additional information on our stock-based employee
compensation plans, see Note 12 (Common Stock and Stock
Plans).
Earnings Per Common Share
We compute earnings per common share by dividing net income
applicable to common stock (net income less dividends on
preferred stock and the excess of consideration transferred over
carrying value of preferred stock redeemed, if any) by the
average number of common shares outstanding during the
period. We compute diluted earnings per common share using
net income applicable to common stock and adding the effect of
common stock equivalents (e.g., restricted share rights) that are
dilutive to the average number of common shares outstanding
during the period.
Fair Value of Assets and Liabilities
Fair value represents the price that would be received to sell an
asset or paid to transfer a liability in an orderly transaction
between market participants at the measurement date. Fair
value is based on an exit price notion that maximizes the use of
observable inputs and minimizes the use of unobservable inputs.
We measure our assets and liabilities at fair value when we
are required to record them at fair value, when we have elected
the fair value option, and to fulfill fair value disclosure
requirements. Assets and liabilities are recorded at fair value on a
recurring or nonrecurring basis. Assets and liabilities that are
recorded at fair value on a recurring basis require a fair value
measurement at each reporting period. Assets and liabilities that
are recorded at fair value on a nonrecurring basis are adjusted to
fair value only as required through the application of an
accounting method such as LOCOM, write-downs of individual
assets, or application of the measurement alternative for certain
nonmarketable equity securities.
Wells Fargo & Company 101
Note 1: Summary of Significant Accounting Policies (continued)
We classify our assets and liabilities measured at fair value
based upon a three-level hierarchy that assigns the highest
priority to unadjusted quoted prices in active markets and the
lowest priority to unobservable inputs. The three levels are as
follows:
• Level 1 – Valuation is based upon quoted prices for identical
instruments traded in active markets.
• Level 2 – Valuation is based upon quoted prices for similar
instruments in active markets, quoted prices for identical or
similar instruments in markets that are not active, and
model-based valuation techniques for which all significant
assumptions are observable in the market.
• Level 3 – Valuation is generated from techniques that use
significant assumptions that are not observable in the
market. These unobservable assumptions reflect our
estimates of assumptions that market participants would
use in pricing the asset or liability. Valuation techniques
include use of discounted cash flow models, market
comparable pricing, option pricing models, and similar
techniques.
We monitor the availability of observable market data to
assess the appropriate classification of financial instruments
within the fair value hierarchy and transfers between Level 1,
Level 2, and Level 3 accordingly. Observable market data includes
but is not limited to quoted prices and market transactions.
Changes in economic conditions or market liquidity generally will
drive changes in availability of observable market data. Changes
in availability of observable market data, which also may result in
changing the valuation technique used, are generally the cause of
transfers between Level 1, Level 2, and Level 3. The amounts
reported as transfers represent the fair value as of the beginning
of the quarter in which the transfer occurred.
See Note 15 (Fair Values of Assets and Liabilities) for a more
detailed discussion of the valuation methodologies that we apply
to our assets and liabilities.
Supplemental Cash Flow Information
Significant noncash activities are presented in Table 1.2.
Table 1.2: Supplemental Cash Flow Information
Year ended December 31,
(in millions) 2022 2021 2020
Available-for-sale debt securities purchased from securitization of LHFS (1)
$ 1,506
3,096
21,768
Held-to-maturity debt securities purchased from securitization of LHFS (1)
745
20,265
9,912
Transfers from loans to LHFS
6,586
19,297
19,975
Transfers from available-for-sale debt securities to held-to-maturity debt securities
50,132
55,993
31,815
(1) Predominantly represents agency mortgage-backed securities purchased upon settlement of the sale and securitization of our conforming residential mortgage loans. See Note 16 (Securitizations
and Variable Interest Entities) for additional information.
Subsequent Events
We have evaluated the effects of events that have occurred
subsequent to December31, 2022 as follows:
In January 2023, we reclassified fixed-rate debt securities with an
aggregate fair value of $23.2 billion and amortized cost of
$23.9billion from held-to-maturity to available-for-sale and
designated $20.1 billion in notional amounts of interest rate
swaps as fair value hedges using the portfolio layer method, in
connection with the adoption of ASU 2022-01, Derivatives and
Hedging (Topic 815): Fair Value Hedging – Portfolio Layer Method.
The transfer of debt securities was recorded at fair value and
resulted in $566 million of unrealized losses associated with
available-for-sale debt securities being recorded to other
comprehensive income, net of deferred taxes.
Except as discussed above, there have been no material events
that would require recognition in our 2022 consolidated financial
statements or disclosure in the Notes to the consolidated
financial statements.
Wells Fargo & Company 102
Note 2: Trading Activities
Table 2.1 presents a summary of our trading assets and liabilities
measured at fair value through earnings.
Table 2.1: Trading Assets and Liabilities
(in millions)
Dec 31,
2022
Dec 31,
2021
Trading assets:
Debt securities $ 86,155 88,265
Equity securities (1) 26,910 27,476
Loans held for sale 1,466 3,242
Gross trading derivative assets (1) 77,148 48,325
Netting (2) (54,922) (28,146)
Total trading derivative assets 22,226 20,179
Total trading assets 136,757 139,162
Trading liabilities:
Short sale and other liabilities 20,304 20,685
Long-term debt 1,346 —
Gross trading derivative liabilities (1) 77,698 42,449
Netting (2) (59,232) (33,978)
Total trading derivative liabilities 18,466 8,471
Total trading liabilities $ 40,116 29,156
(1) In first quarter 2022, we prospectively reclassified certain equity securities and related economic hedge derivatives from “not held for trading activities” to “held for trading activities” to better
reflect the business activity of those financial instruments. For additional information on Trading Activities, see Note 1 (Summary of Significant Accounting Policies).
(2) Represents balance sheet netting for trading derivative asset and liability balances, and trading portfolio level counterparty valuation adjustments.
Table 2.2 provides a summary of the net interest income
earned from trading securities, and net gains and losses due to
the realized and unrealized gains and losses from trading
activities.
Net interest income also includes dividend income on
trading securities and dividend expense on trading securities we
have sold, but not yet purchased.
Table 2.2: Net Interest Income and Net Gains (Losses) from Trading Activities
Year ended December 31,
(in millions) 2022 2021 2020
Interest income:
Debt securities $ 2,466 2,086 2,530
Equity securities (1) 497 441 366
Loans held for sale 48 40 30
Total interest income 3,011 2,567 2,926
Less: Interest expense 592 405 442
Net interest income 2,419 2,162 2,484
Net gains (losses) from trading activities (2):
Debt securities (10,053) (1,796) 2,697
Equity securities (1) (3,823) 4,491 (630)
Loans held for sale 6 54 28
Long-term debt 52 — —
Derivatives (1)(3) 15,934 (2,465) (923)
Total net gains from trading activities 2,116 284 1,172
Total trading-related net interest and noninterest income $ 4,535 2,446 3,656
(1) In first quarter 2022, we prospectively reclassified certain equity securities and related economic hedge derivatives from “not held for trading activities” to “held for trading activities” to better
reflect the business activity of those financial instruments. For additional information on Trading Activities, see Note 1 (Summary of Significant Accounting Policies).
(2) Represents realized gains (losses) from our trading activities and unrealized gains (losses) due to changes in fair value of our trading positions.
(3) Excludes economic hedging of mortgage banking and asset/liability management activities, for which hedge results (realized and unrealized) are reported with the respective hedged activities.
Wells Fargo & Company 103
Note 3: Available-for-Sale and Held-to-Maturity Debt Securities
Table 3.1 provides the amortized cost, net of the allowance for
credit losses (ACL) for debt securities, and fair value by major
categories of available-for-sale (AFS) debt securities, which are
carried at fair value, and held-to-maturity (HTM) debt securities,
which are carried at amortized cost, net of the ACL. The net
unrealized gains (losses) for AFS debt securities are reported as a
component of accumulated other comprehensive income (AOCI),
net of the ACL and applicable income taxes. Information on debt
securities held for trading is included in Note 2 (Trading
Activities).
Outstanding balances exclude accrued interest receivable on
AFS and HTM debt securities, which are included in other assets.
See Note 7 (Intangible Assets and Other Assets) for additional
information on accrued interest receivable. Amounts considered
to be uncollectible are reversed through interest income. The
interest income reversed for the years ended 2022 and 2021 was
insignificant.
Table 3.1: Available-for-Sale and Held-to-Maturity Debt Securities Outstanding
(in millions)
Amortized
cost, net (1)
Gross
unrealized gains
Gross
unrealized losses Fair value
December 31, 2022
Available-for-sale debt securities:
Securities of U.S. Treasury and federal agencies $ 47,536 9 (2,260) 45,285
Non-U.S. government securities 162 — — 162
Securities of U.S. states and political subdivisions (2) 10,958 20 (533) 10,445
Federal agency mortgage-backed securities 53,302 2 (5,167) 48,137
Non-agency mortgage-backed securities (3) 3,423 1 (140) 3,284
Collateralized loan obligations 4,071 — (90) 3,981
Other debt securities 2,273 75 (48) 2,300
Total available-for-sale debt securities 121,725 107 (8,238) 113,594
Held-to-maturity debt securities:
Securities of U.S. Treasury and federal agencies 16,202 — (1,917) 14,285
Securities of U.S. states and political subdivisions 30,985 8 (4,385) 26,608
Federal agency mortgage-backed securities 216,966 30 (34,252) 182,744
Non-agency mortgage-backed securities (3) 1,253 — (147) 1,106
Collateralized loan obligations 29,926 1 (727) 29,200
Other debt securities 1,727 — (149) 1,578
Total held-to-maturity debt securities 297,059 39 (41,577) 255,521
Total $ 418,784 146 (49,815) 369,115
December 31, 2021
Available-for-sale debt securities:
Securities of U.S. Treasury and federal agencies $ 39,668 185 (192) 39,661
Non-U.S. government securities 71 — — 71
Securities of U.S. states and political subdivisions (2) 16,618 350 (51) 16,917
Federal agency mortgage-backed securities 104,661 1,807 (582) 105,886
Non-agency mortgage-backed securities (3) 4,515 32 (15) 4,532
Collateralized loan obligations 5,713 2 (7) 5,708
Other debt securities 4,217 259 (7) 4,469
Total available-for-sale debt securities 175,463 2,635 (854) 177,244
Held-to-maturity debt securities:
Securities of U.S. Treasury
and federal agencies 16,544 599 (318) 16,825
Securities of U.S. states and political subdivisions 32,689 847 (61) 33,475
Federal agency mortgage-backed securities 188,909 1,882 (2,807) 187,984
Non-agency mortgage-backed securities (3) 1,082 31 (18) 1,095
Collateralized loan obligations 31,067 194 (2) 31,259
Other debt securities 1,731 17 — 1,748
Total held-to-maturity debt securities 272,022 3,570 (3,206) 272,386
Total $ 447,485 6,205 (4,060) 449,630
(1) Represents amortized cost of the securities, net of the ACL of $6 million and $8million related to AFS debt securities and $85 million and $96 million related to HTM debt securities at December31,
2022 and 2021, respectively.
(2) Includes investments in tax-exempt preferred debt securities issued by investment funds or trusts that predominantly invest in tax-exempt municipal securities. The amortized cost, net of the ACL,
and fair value of these types of securities, was $5.1 billion at December31, 2022, and $5.2 billion at December31, 2021.
(3) Predominantly consists of commercial mortgage-backed securities at both December31, 2022 and 2021.
Wells Fargo & Company 104
Table 3.2 details the breakout of purchases of and transfers
to HTM debt securities by major category of security.
Table 3.2: Held-to-Maturity Debt Securities Purchases and Transfers
Year ended December 31,
(in millions) 2022 2021 2020
Purchases of held-to-maturity debt securities (1):
Securities of U.S. Treasury and federal agencies $ — — 3,016
Securities of U.S. states and political subdivisions 843 5,198 1,906
Federal agency mortgage-backed securities 2,051 76,010 51,320
Non-agency mortgage-backed securities 211 235 126
Collateralized loan obligations — 9,379 688
Total purchases of held-to-maturity debt securities 3,105 90,822 57,056
Transfers from available-for-sale debt securities to held-to-maturity debt securities (2):
Securities of U.S. states and political subdivisions — 2,954 10,721
Federal agency mortgage-backed securities 50,132 41,298 5,522
Collateralized loan obligations — 10,003 15,572
Other debt securities — 1,738 —
Total transfers from available-for-sale debt securities to held-to-maturity debt securities $ 50,132 55,993 31,815
(1) Inclusive of securities purchased but not yet settled and noncash purchases from securitization of loans held for sale (LHFS).
(2) Represents fair value as of the date of the transfers. Debt securities transferred from available-for-sale to held-to-maturity had pre-tax unrealized losses recorded in AOCI of $4.5 billion for the year
ended 2022 and $529 million for the year ended 2021, respectively, at the time of the transfers.
Table 3.3 shows the composition of interest income,
provision for credit losses, and gross realized gains and losses
from sales and impairment write-downs included in earnings
related to AFS and HTM debt securities (pre-tax).
Table 3.3: Income Statement Impacts for Available-for-Sale and Held-to-Maturity Debt Securities
Year ended December 31,
(in millions) 2022 2021 2020
Interest income (1):
Available-for-sale $ 3,095 2,808 4,992
Held-to-maturity 6,220 4,359 3,712
Total interest income 9,315 7,167 8,704
Provision for credit losses:
Available-for-sale 1 (2) 89
Held-to-maturity (11) 54 35
Total provision for credit losses (10) 52 124
Realized gains and losses (2):
Gross realized gains 276 571 931
Gross realized losses (125) (10) (43)
Impairment write-downs — (8) (15)
Net realized gains $ 151 553 873
(1) Excludes interest income from trading debt securities, which is disclosed in Note 2 (Trading Activities).
(2) Realized gains and losses relate to AFS debt securities. There were no realized gains or losses from HTM debt securities in all periods presented.
Credit Quality
We monitor credit quality of debt securities by evaluating various
attributes and utilize such information in our evaluation of the
appropriateness of the ACL for debt securities. The credit quality
indicators that we most closely monitor include credit ratings
and delinquency status and are based on information as of our
financial statement date.
CREDIT RATINGS Credit ratings express opinions about the credit
quality of a debt security. We determine the credit rating of a
security according to the lowest credit rating made available by
national recognized statistical rating organizations (NRSROs).
Debt securities rated investment grade, that is those with ratings
similar to BBB-/Baa3 or above, as defined by NRSROs, are
generally considered by the rating agencies and market
participants to be low credit risk. Conversely, debt securities
rated below investment grade, labeled as “speculative grade” by
the rating agencies, are considered to be distinctively higher
credit risk than investment grade debt securities. For debt
securities not rated by NRSROs, we determine an internal credit
grade of the debt securities (used for credit risk management
purposes) equivalent to the credit ratings assigned by major
credit agencies. Substantially all of our debt securities were rated
by NRSROs at December 31, 2022 and 2021.
Table 3.4 shows the percentage of fair value of AFS debt
securities and amortized cost of HTM debt securities determined
to be rated investment grade, inclusive of securities rated based
on internal credit grades.
Wells Fargo & Company 105
Table 3.4: Investment Grade Debt Securities
Available-for-Sale Held-to-Maturity
($ in millions)
Fair
value
% investment grade
Amortized cost % investment grade
December 31, 2022
Total portfolio (1)
$
113,594 99% $
297,144
99%
Breakdown by category:
Securities of U.S. Treasury and federal agencies (2) $
93,422
100% $
233,169
100%
Securities of U.S. states and political subdivisions
10,445
99
31,000
100
Collateralized loan obligations (3)
3,981
100
29,972
100
All other debt securities (4)
5,746
89
3,003
63
December 31, 2021
Total portfolio (1) $
177,244
99% $
272,118
99%
Breakdown by category:
Securities of U.S. Treasury and federal agencies
(2) $
145,547
100% $
205,453
100%
Securities of U.S. states and political subdivisions
16,917
99
32,704
100
Collateralized loan obligations
(3)
5,708
100
31,128
100
All other debt securities
(4)
9,072
88
2,833
64
Note 3: Available-for-Sale and Held-to-Maturity Debt Securities (continued)
(1) 99% and 98% were rated AA- and above at December 31, 2022 and 2021, respectively.
(2) Includes federal agency mortgage-backed securities.
(3) 100% were rated AA- and above at both December 31, 2022 and 2021.
(4) Includes non-U.S. government, non-agency mortgage-backed, and all other debt securities.
DELINQUENCY S TATUS AND NONAC CRUAL DEBT S ECURITIES Debt
security issuers that are delinquent in payment of amounts due
under contractual debt agreements have a higher probability of
recognition of credit losses. As such, as part of our monitorin g of
the credit quality of the debt security portfolio, we consider
whether debt securities we own are past due in payment of
principal or interest payments and whether any securities have
been placed into nonaccrual status.
Debt securities that are past due and still accruing or in
nonaccrual status were insignificant at both December 31, 2022
and 2021. Charge-offs on debt securities were insignificant for
the years ended December 31, 2022 and 2021.
Purchased debt securities with credit deterioration (PCD)
are not considered to be in nonaccrual status, as payments fro m
issuers of these securities remain current. PCD securities wer e
insignificant for the years ended December 31, 2022 and 2021.
Wells Fargo & Company 106
Unrealized Losses of Available-for-Sale Debt Securities
Table 3.5 shows the gross unrealized losses and fair value of AFS
debt securities by length of time those individual securities in
each category have been in a continuous loss position. Debt
securities on which we have recorded credit impairment are
categorized as being “less than 12 months” or “12 months or
more” in a continuous loss position based on the point in time
that the fair value declined to below the amortized cost basis , net
of allowance for credit losses.
Table 3.5: Gross Unrealized Losses and Fair Value – Available-for-Sale Debt Securities
Less than 12 months 12 months or more Total
(in millions)
Gross
unrealized
losses Fair value
Gross
unrealized
losses Fair value
Gross
unrealized
losses Fair value
December 31, 2022
Available-for-sale debt securities:
Securities of U.S. Treasury and federal agencies $ (291) 9,870 (1,969) 27,899 (2,260) 37,769
Securities of U.S. states and political subdivisions (72) 2,154 (461) 2,382 (533) 4,536
Federal agency mortgage-backed securities (3,580) 39,563 (1,587) 8,481 (5,167) 48,044
Non-agency mortgage-backed securities (43) 1,194 (97) 2,068 (140) 3,262
Collateralized loan obligations (65) 3,195 (25) 786 (90) 3,981
Other debt securities (31) 1,591 (17) 471 (48) 2,062
Total available-for-sale debt securities $ (4,082) 57,567 (4,156) 42,087 (8,238) 99,654
December 31, 2021
Available-for-sale debt securities:
Securities of U.S. Treasury and federal agencies $ (192) 24,418 — — (192) 24,418
Securities of U.S. states and political subdivisions (36) 2,308 (15) 532 (51) 2,840
Federal agency mortgage-backed securities (334) 40,695 (248) 9,464 (582) 50,159
Non-agency mortgage-backed securities (4) 1,966 (11) 543 (15) 2,509
Collateralized loan obligations (3) 1,619 (4) 1,242 (7) 2,861
Other debt securities — — (7) 624 (7) 624
Total available-for-sale debt securities $ (569) 71,006 (285) 12,405 (854) 83,411
We have assessed each debt security with gross unrealized
losses included in the previous table for credit impairment. A s
part of that assessment we evaluated and concluded that we do
not intend to sell any of the debt securities, and that it is m ore
likely than not that we will not be required to sell, prior to
recovery of the amortized cost basis. We evaluate, where
necessary, whether credit impairment exists by comparing the
present value of the expected cash flows to the debt securities ’
amortized cost basis. Credit impairment is recorded as an ACL f or
debt securities.
For descriptions of the factors we consider when analyzing
debt securities for impairment as well as methodology and
significant inputs used to measure credit losses, see Note 1
(Summary of Significant Accounting Policies ) in this Report .
Wells Fargo & Company 107
Contractual Maturities
Table 3.6 and Table 3.7 show the remaining contractual
maturities, amortized cost, net of the ACL, fair value and
weighted average effective yields of AFS and HTM debt
securities, respectively. The remaining contractual principal
maturities for mortgage-backed securities (MBS) do not
consider prepayments. Remaining expected maturities will diffe r
from contractual maturities because borrowers may have the
right to prepay obligations before the underlying mortgages
mature.
Table 3.6: Contractual Maturities – Available-for-Sale Debt Securities
By remaining contractual maturity ($ in millions) Total
Within
one year
After
one year
through
five years
After
five years
through
ten years
After
ten years
December 31, 2022
Available-for-sale debt securities (1):
Securities of U.S. Treasury and federal agencies
Amortized cost, net $ 47,536 4,046 21,094 20,884 1,512
Fair value 45,285 3,945 20,576 19,326 1,438
Weighted average yield 1.09% 1.19 0.55 1.59 1.44
Non-U.S. government securities
Amortized cost, net $ 162 1 137 24 —
Fair value 162 1 137 24 —
Weighted average yield 3.49% 5.10 3.62 2.71 —
Securities of U.S. states and political subdivisions
Amortized cost, net $ 10,958 1,139 2,471 4,866 2,482
Fair value 10,445 1,138 2,455 4,513 2,339
Weighted average yield 3.46% 4.06 3.43 3.16 3.80
Federal agency mortgage-backed securities
Amortized cost, net $ 53,302 1 277 856 52,168
Fair value 48,137 1 264 799 47,073
Weighted average yield 3.26% 3.33 1.90 2.48 3.28
Non-agency mortgage-backed securities
Amortized cost, net $ 3,423 — — 71 3,352
Fair value 3,284 — — 65 3,219
Weighted average yield 4.58% — — 3.31 4.61
Collateralized loan obligations
Amortized cost, net $ 4,071 — — 3,668 403
Fair value 3,981 — — 3,592 389
Weighted average yield 5.53% — — 5.53 5.54
Other debt securities
Amortized cost, net $ 2,273 81 203 866 1,123
Fair value 2,300 79 199 866 1,156
Weighted average yield 5.13% 5.16 5.73 4.47 5.52
Total available-for-sale debt securities
Amortized cost, net $ 121,725 5,268 24,182 31,235 61,040
Fair value 113,594 5,164 23,631 29,185 55,614
Weighted average yield 2.57% 1.87 0.90 2.41 3.38
Note 3: Available-for-Sale and Held-to-Maturity Debt Securities (continued)
(1) Weighted average yields displayed by maturity bucket are weighted based on amortized cost without effect for any related hedging derivatives and are shown pre-tax.
Wells Fargo & Company 108
Table 3.7: Contractual Maturities – Held-to-Maturity Debt Securities
By remaining contractual maturity ($ in millions) Total
Within
one year
After
one year
through
five years
After
five years
through
ten years
After
ten years
December 31, 2022
Held-to-maturity debt securities (1):
Securities of U.S. Treasury and federal agencies
Amortized cost, net $ 16,202 — 12,415 — 3,787
Fair value 14,285 — 11,972 — 2,313
Weighted average yield 2.18% — 2.37 — 1.58
Securities of U.S. states and political subdivisions
Amortized cost, net $ 30,985 1,677 1,959 2,052 25,297
Fair value 26,608 1,664 1,912 2,018 21,014
Weighted average yield 2.12% 1.26 1.58 2.28 2.20
Federal agency mortgage-backed securities
Amortized cost, net $ 216,966 — — — 216,966
Fair value 182,744 — — — 182,744
Weighted average yield 2.27% — — — 2.27
Non-agency mortgage-backed securities
Amortized cost, net $ 1,253 — 18 65 1,170
Fair value 1,106 — 17 61 1,028
Weighted average yield 3.11% — 2.93 3.88 3.07
Collateralized loan obligations
Amortized cost, net $ 29,926 — — 13,264 16,662
Fair value 29,200 — — 13,085 16,115
Weighted average yield 5.62% — — 5.71 5.55
Other debt securities
Amortized cost, net $ 1,727 — 758 969 —
Fair value 1,578 — 713 865 —
Weighted average yield 4.47% — 4.10 4.75 —
Total held-to-maturity debt securities
Amortized cost, net $ 297,059 1,677 15,150 16,350 263,882
Fair value 255,521 1,664 14,614 16,029 223,214
Weighted average yield 2.61% 1.26 2.35 5.21 2.47
(1) Weighted average yields displayed by maturity bucket are weighted based on amortized cost, excluding unamortized basis adjustments related to the transfer of certain debt securities from AFS to
HTM, and are shown pre-tax.
Wells Fargo & Company 109
Note 4 : Equity Securities
Table 4.1 provides a summary of our equity securities by business
purpose and accounting method.
Table 4.1: Equity Securities
(in millions)
Dec 31,
2022
Dec 31,
2021
Held for trading at fair value:
Marketable equity securities (1) $ 17,180 27,476
Nonmarketable equity securities (2)(3) 9,730 —
Total equity securities held for trading 26,910 27,476
Not held for trading:
Fair value:
Marketable equity securities 1,436 2,578
Nonmarketable equity securities (2) 37 9,044
Total equity securities not held for trading at fair value 1,473 11,622
Equity method:
Private equity 2,836 3,077
Tax-advantaged renewable energy (4) 6,535 4,740
New market tax credit and other 298 379
Total equity method 9,669 8,196
Other methods:
Low-income housing tax credit investments (LIHTC) (4) 12,186 12,314
Private equity (5) 9,276 9,694
Federal Reserve Bank stock and other at cost (6) 4,900 3,584
Total equity securities not held for trading 37,504 45,410
Total equity securities $ 64,414 72,886
(1) Represents securities held as part of our customer accommodation trading activities. For additional information on these activities, see Note 2 (Trading Activities).
(2) In first quarter 2022, we prospectively reclassified certain equity securities and related economic hedge derivatives from “not held for trading activities” to “held for trading activities” to better
reflect the business activity of those financial instruments. For additional information on Trading Activities, see Note 1 (Summary of Significant Accounting Policies).
(3) Represents securities economically hedged with equity derivatives.
(4) See Note 16 (Securitizations and Variable Interest Entities) for information about tax credit investments.
(5) Represents nonmarketable equity securities accounted for under the measurement alternative, which were predominantly securities associated with our affiliated venture capital business.
(6) Includes $3.5 billion of investments in Federal Reserve Bank stock at both December 31, 2022 and 2021, and $1.4 billion and $39 million of investments in Federal Home Loan Bank stock at
December 31, 2022 and 2021, respectively.
Net Gains and Losses Not Held for Trading
Table 4.2 provides a summary of the net gains and losses from
equity securities not held for trading, which excludes equity
method adjustments for our share of the investee’s earnings or
losses that are recognized in other noninterest income. Gains a nd
losses for securities hel d for trading are reported in net gains
from trading and securities.
Table 4.2: Net Ga ins (Lo sses) fro m Equity S ecurities No t Held for Tra ding
Year ended December 31,
(in millions) 2022 2021 2020
Net gains (losses) from equity securities carried at fair value:
Marketable equity securities $ (225) (202) 63
Nonmarketable equity securities (1) (82) (188) 1,414
Total equity securities carried at fair value (307) (390) 1,477
Net gains (losses) from nonmarketable equity securities not carried at fair value (2):
Impairment write-downs (2,452) (121) (1,655)
Net unrealized gains (3)(4) 1,101 4,862 1,651
Net realized gains from sale (4) 852 1,581 359
Total nonmarketable equity securities not carried at fair value (499) 6,322 355
Net gains (losses) from economic hedge derivatives (1) — 495 (1,167)
Total net gains (losses) from equity securities not held for trading $ (806) 6,427 665
(1) In first quarter 2022, we prospectively reclassified certain equity securities and related economic hedge derivatives from “not held for trading activities” to “held for trading activities” to better
reflect the business activity of those financial instruments. For additional information on Trading Activities, see Note 1 (Summary of Significant Accounting Policies).
(2) Includes amounts related to private equity and venture capital investments in consolidated portfolio companies, which are not reported in equity securities on our consolidated balance sheet.
(3) Includes unrealized gains (losses) due to observable price changes from equity securities accounted for under the measurement alternative.
(4) During the year ended December 31, 2021, we recognized $442 million of gains (including $293 million of unrealized gains) related to the partial sale of a nonmarketable equity investment to an
unrelated third-party that resulted in the deconsolidation of a consolidated portfolio company. Our retained investment in nonmarketable equity securities of the formerly consolidated portfolio
company was remeasured to fair value.
Wells Fargo & Company 110
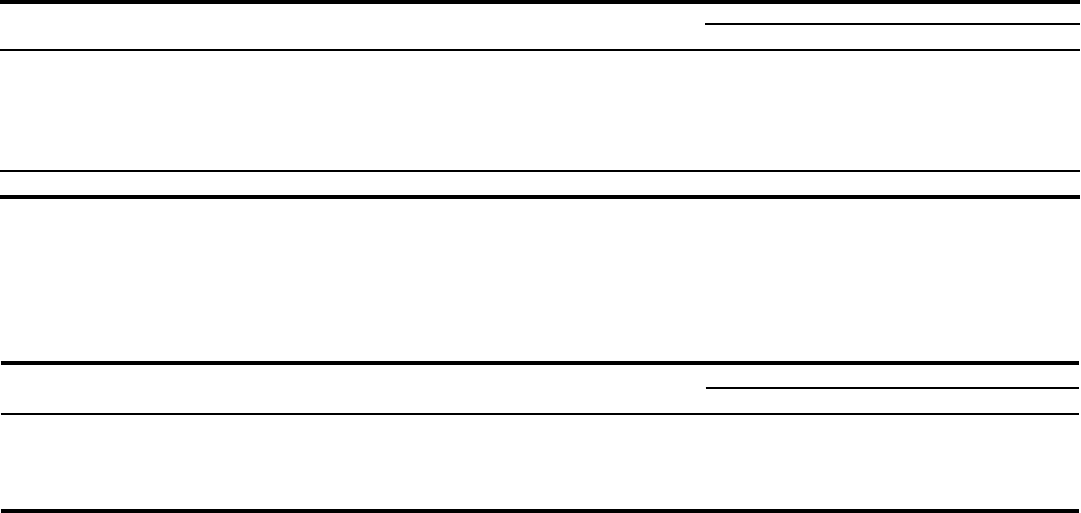
Measurement Alternative
Table 4.3 provides additional information about the impairment
write-downs and observable price changes from nonmarketable
equity securities accounted for under the measurement
alternative. Gains and losses related to these adjustments are
also included in Table 4.2 .
Table 4.3: Net Gains (Losses) from Measurement Alternative Equity Securities
Year ended December 31,
(in millions) 2022 2021 2020
Net gains (losses) recognized in earnings during the period:
Gross unrealized gains from observable price changes
$
1,115
4,569
1,651
Gross unrealized losses from observable price changes
(14)
—
—
Impairment write-downs
(2,263)
(109)
(954)
Net realized gains from sale
98
456
38
Total
net
gains
(losses)
recognized
during
the
period $
(1,064)
4,916
735
Table 4.4 presents cumulative carrying value adjustments to
nonmarketable equity securities accounted for under the
measurement alternative that were still held at the end of eac h
reporting period presented.
Table 4.4: Measurement Alterna tive C umulative Ga ins (Lo sses)
Year ended December 31,
(in millions) 2022 2021 2020
Cumulative gains (losses):
Gross unrealized gains from observable price changes
$
7,141
6,278
2,356
Gross unrealized losses from observable price changes
(14)
(3)
(25)
Impairment write-downs
(2,896)
(821)
(969)
Wells Fargo & Company 111
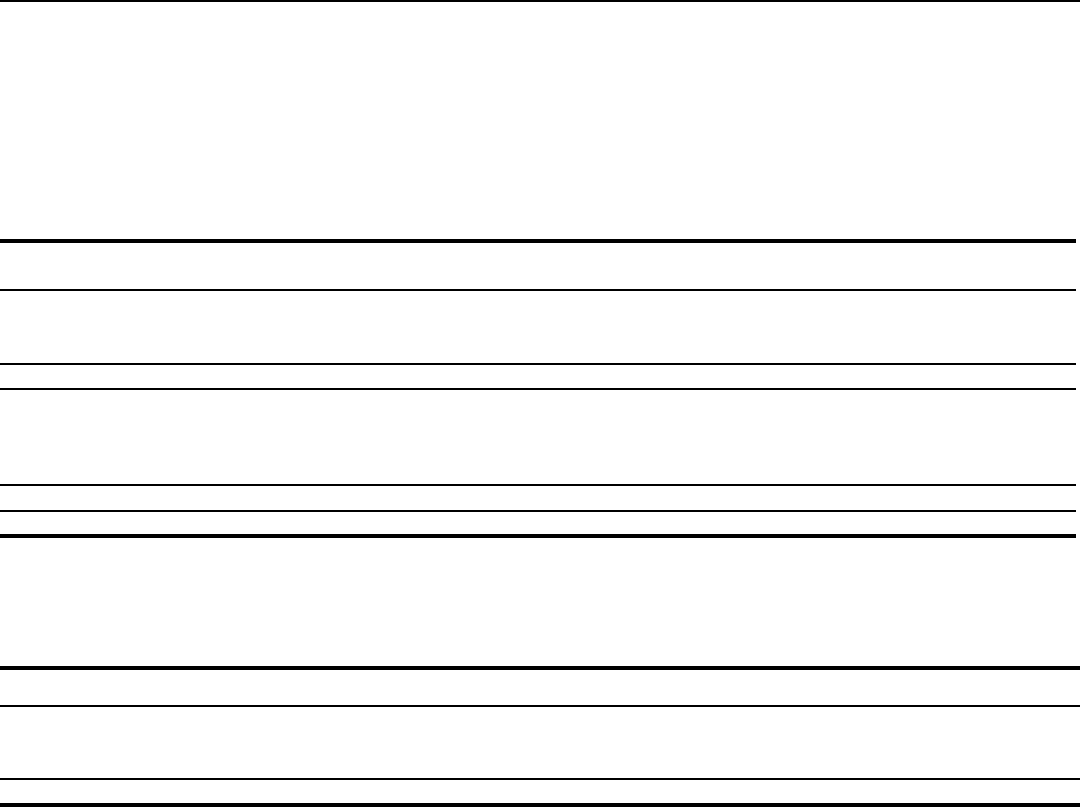
Note 5 : Loans and Related Allowance for Credit Losses
Table 5.1 presents total loans outstanding by portfolio segment
and class of financing receivable. Outstanding balances include
unearned income, net deferred loan fees or costs, and
unamortized discounts and premiums. These amounts were less
than 1% of our total loans outstanding at December 31, 2022
and 2021.
Outstanding balances exclude accrued interest receivable on
loans, except for certain revolving loans, such as credit card loans.
See Note 7 (Intangible Assets and Other Assets ) for additional
information on accrued interest receivable. Amounts considered
to be uncollectible are reversed through interest income. Durin g
2022, we reversed accrued interest receivable of $29 million for
our commercial portfolio segment and $143 million for our
consumer portfolio segment, compared with $44 million and
$175 million , respectively, for 2021.
Table 5.1: Loans Outsta nding
(in millions)
Dec 31,
2022
Dec 31,
2021
Commercial and industrial $ 386,806 350,436
Commercial real estate 155,802 147,825
Lease financing 14,908 14,859
Total commercial 557,516 513,120
Residential mortgage 269,117 258,888
Credit card 46,293 38,453
Auto 53,669 56,659
Other consumer 29,276 28,274
Total consumer 398,355 382,274
Total loans $ 955,871 895,394
Our non-U.S. loan s are reported by respective class of
financing receivable in the table above. Substantially all of our
non-U.S. loan portfolio is commercial loans. Table 5.2 presents
total non-U.S. commercial loans outstanding by class of financi ng
receivable.
Table 5.2: Non-U.S. C ommercial Lo ans Outsta nding
(in millions)
Dec 31,
2022
Dec 31,
2021
Commercial and industrial $ 78,981 77,365
Commercial real estate 7,619 8,652
Lease financing 670
680
Total non-U.S. commercial loans $ 87,270 86,697
Loan Concentrations
Loan concentrations may exist when there are amounts loaned to
borrowers engaged in similar activities or similar types of loans
extended to a diverse group of borrowers that would cause them
to be similarly impacted by economic or other conditions.
Commercial and industrial loans and lease financing to borrowers
in the financials except banks industry represented 15% and 16%
of total loans at December 31, 2022 and
2021, respectively. At
December 31, 2022 and 2021, we did not have concentrations
representing 10% or more of our total loan portfolio in the
commercial real estate (CRE) portfolios (real estate mortgage
and real estate construction) by state or property type.
Residential mortgage loans to borrowers in the state of
California represented 12% of total loans at both December 31,
2022 and 2021. These California loans are generally diversified
among the larger metropolitan areas in California, with no single
area consisting of more than 4% of total loans at both
December 31, 2022 and 2021. We continuously monitor changes
in real estate values and underlying economic or market
conditions for all geographic areas of our residential mortgage
portfolio as part of our credit risk management process.
Some of our residential mortgage loans include an interest-
only feature as part of the loan terms. These interest-only loans
were approximately 2% and 3% of total loans at December 31,
2022 and 2021, respectively. Substantially all of these interest-
only loans at origination were considered to be prime or near
prime. We do not offer option adjustable-rate mortgage (ARM)
products, nor do we offer variable-rate mortgage products with
fixed payment amounts, commonly referred to within the
financial services industry as negative amortizing mortgage
loans.
Wells Fargo & Company 112
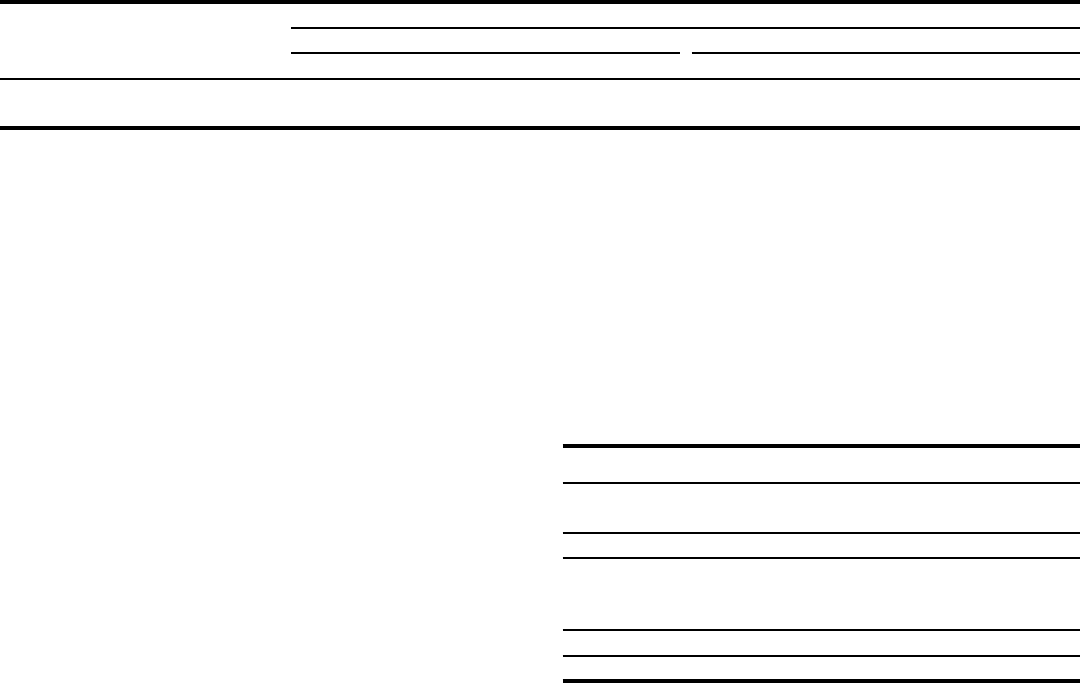
Loan Purchases, Sales, and Transfers
Table 5.3 presents the proceeds paid or received for purchases
and sales of loans and transfers from loans held for investmen t
to mortgages/loans held for sale. The table excludes loans for
which we have elected the fair value option and government
insured/guaranteed residential mortgage – first lien loans
because their loan activity normally does not impact the ACL.
Table 5.3: Loan Purchases, Sales, and Transfers
Year ended December 31,
2022 2021
(in
millions) Commercial
Consumer Total Commercial Consumer Total
Purchases $
740
5
745
380
6
386
Sales
and
net
transfers
(to)/from
LHFS (3,182)
(1,135)
(4,317)
(4,084)
(243)
(4,327)
Unfunded Credit Commitments
Unfunded credit commitments are legally binding agreements to
lend to customers with terms covering usage of funds,
contractual interest rates, expiration dates, and any required
collateral. Our commercial lending commitments include, but are
not limited to, (i) commitments for working capital and general
corporate purposes, (ii) financing to customers who warehouse
financial assets secured by real estate, consumer, or corporate
loans, (iii) financing that is expected to be syndicated or replaced
with other forms of long-term financing, and (iv) commercial real
estate lending. We also originate multipurpose lending
commitments under which commercial customers have the
option to draw on the facility in one of several forms, including
the issuance of letters of credit, which reduces the unfunded
commitment amounts of the facility.
The maximum credit risk for these commitments will
generally be lower than the contractual amount because these
commitments may expire without being used or may be
cancelled at the customer’s request. We may reduce or cancel
lines of credit in accordance with the contracts and applicable
law. Certain commitments either provide us with funding
discretion or are subject to loan agreements with covenants
regarding the financial performance of the customer or
borrowing base formulas that must be met before we are
required to fund the commitment. Our credit risk monitoring
activities include managing the amount of commitments, both to
individual customers and in total, and the size and maturity
structure of these commitments. We do not recognize an ACL
for commitments that are unconditionally cancellable at our
discretion.
We issue commercial letters of credit to assist customers in
purchasing goods or services, typically for international trade. At
December 31, 2022 and 2021, we had $1.8 billion and
$1.5 billion, respectively, of outstanding issued commercial
letters of credit. See Note 17 (Guarantees and Other
Commitments) for additional information on issued standby
letters of credit.
We may be a fronting bank, whereby we act as a
representative for other lenders, and advance funds or provide
for the issuance of letters of credit under syndicated loan or
letter of credit agreements. Any advances are generally repaid in
less than a week and would normally require default of both the
customer and another lender to expose us to loss.
The contractual amount of our unfunded credit
commitments, including unissued letters of credit, is summarized
in Table 5.4. The table excludes issued letters of credit and is
presented net of commitments syndicated to others, including
the fronting arrangements described above.
Table 5.4: Unfunded Credit C ommitments
(in millions)
Dec 31,
2022
Dec 31,
2021
Commercial and industrial $ 457,473 388,162
Commercial real estate 29,518 31,458
Total commercial 486,991 419,620
Residential mortgage (1) 39,155 60,439
Credit card 145,526 130,743
Other consumer (2) 69,244 75,919
Total consumer 253,925 267,101
Total unfunded credit commitments $ 740,916 686,721
(1) Includes lines of credit totaling $35.5 billion and $45.6 billion as of December 31, 2022 and
2021, respectively.
(2) Primarily includes securities-based lines of credit.
Wells Fargo & Company 113
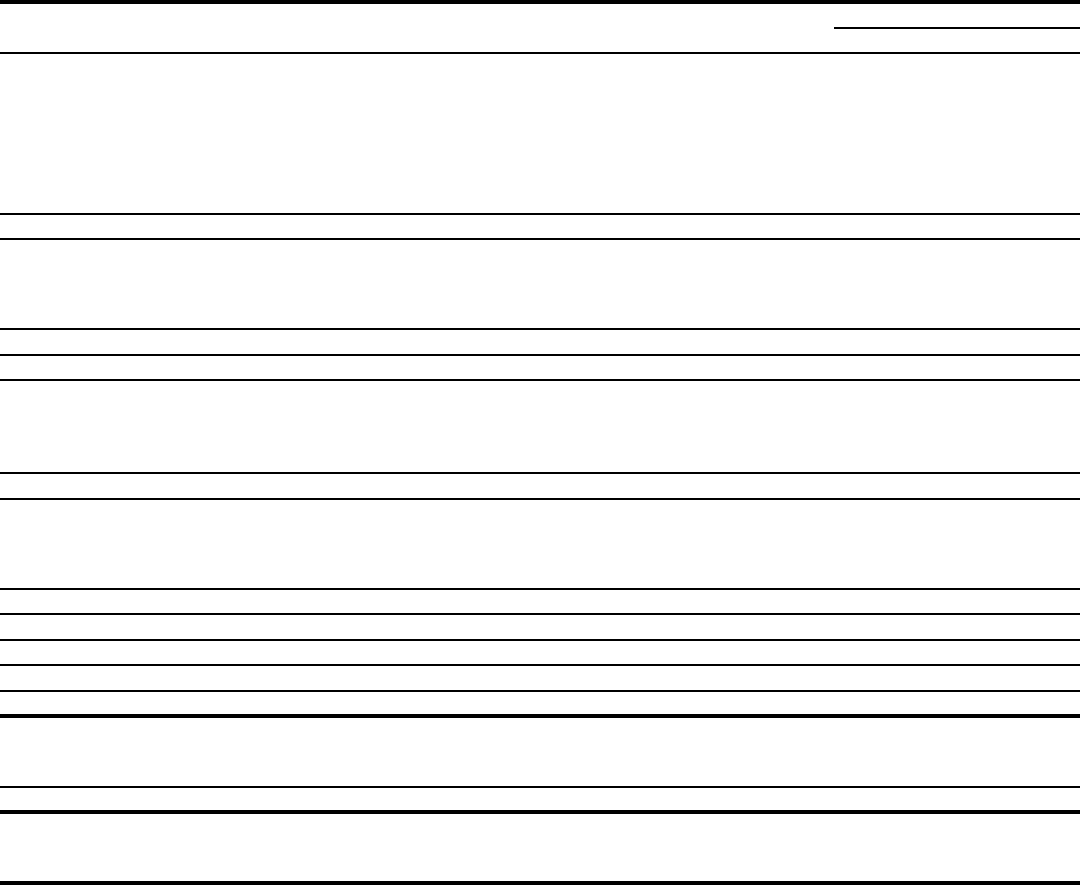
Note 5: Loans and Related Allowance for Credit Losses (continued)
Allowance for Credit Losses
Table 5.5 presents the allowance for credit losses (ACL) for loans,
which consists of the allowance for loan losses and the allowan ce
for unfunded credit commitments. The ACL for loans decreased
$179 million from December 31, 2021 , reflecting reduced
uncertainty around the economic impact of the COVID-19
pandemic on our loan portfolio. This decrease was partially off set
by loan growth and a less favorable economic environment.
Table 5.5: Allowance fo r C redit Lo sses fo r Lo ans
Year ended December 31,
($ in millions) 2022 2021
Balance, beginning of period $ 13,788 19,713
Provision for credit losses 1,544 (4,207)
Interest income on certain loans (1) (108) (145)
Loan charge-offs:
Commercial and industrial (307) (517)
Commercial real estate (21) (99)
Lease financing (27) (46)
Total commercial (355) (662)
Residential mortgage (175) (260)
Credit card (1,195) (1,189)
Auto (734) (497)
Other consumer (407) (423)
Total consumer (2,511) (2,369)
Total loan charge-offs (2,866) (3,031)
Loan recoveries:
Commercial and industrial 224 299
Commercial real estate 32 46
Lease financing 20 22
Total commercial 276
367
Residential mortgage 238 277
Credit card 344 389
Auto 312 316
Other consumer 88 108
Total consumer 982 1,090
Total loan recoveries 1,258 1,457
Net loan charge-offs (1,608) (1,574)
Other (7)
1
Balance, end of period $ 13,609 13,788
Components:
Allowance
for
loan
losses $
12,985
12,490
Allowance
for
unfunded
credit
commitments 624
1,298
Allowance
for
credit
losses $
13,609
13,788
Net
loan
charge-offs
as
a
percentage
of
average
total
loans
0.17
% 0.18
Allowance
for
loan
losses
as
a
percentage
of
total
loans
1.36
1.39
Allowance
for
credit
losses
for
loans
as
a
percentage
of
total
loans
1.42
1.54
(1) Loans with an allowance measured by discounting expected cash flows using the loan’s effective interest rate over the remaining life of the loan recognize changes in allowance attributable to the
passage of time as interest income.
Wells Fargo & Company
114
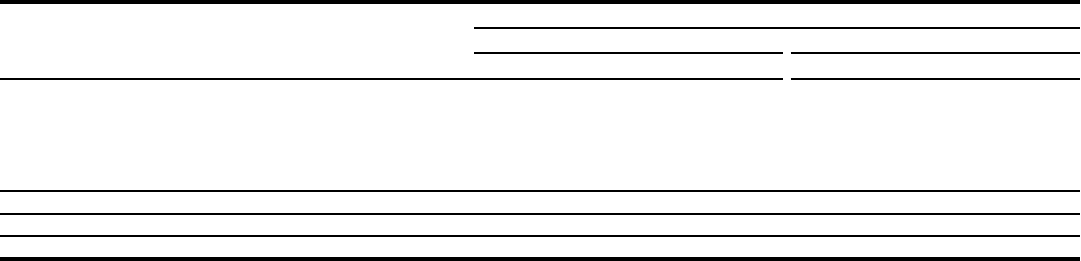
Table 5.6 summarizes the activity in the ACL by our
commercial and consumer portfolio segments.
Table 5.6: Allowance fo r C redit Lo sses fo r Lo ans Activity by Po rtfolio Segment
Year ended December 31,
2022 2021
(in millions)
Commercial
Consumer
Total
Commercial
Consumer
Total
Balance, beginning of period
$
7,791
5,997
13,788
11,516
8,197
19,713
Provision for credit losses
(721)
2,265
1,544
(3,373)
(834)
(4,207)
Interest
income
on
certain
loans
(1)
(29)
(79)
(108)
(58)
(87)
(145)
Loan charge-offs
(355)
(2,511)
(2,866)
(662)
(2,369)
(3,031)
Loan recoveries
276
982
1,258
367
1,090
1,457
Net loan charge-offs
(79)
(1,529)
(1,608)
(295)
(1,279)
(1,574)
Other
(6)
(1)
(7)
1
—
1
Balance, end of period $
6,956
6,653
13,609
7,791
5,997
13,788
(1) Loans with an allowance measured by discounting expected cash flows using the loan’s effective interest rate over the remaining life of the loan recognize changes in allowance attributable to the
passage of time as interest income.
Credit Quality
We monitor credit quality by evaluating various attributes and
utilize such information in our evaluation of the appropriateness
of the ACL for loans. The following sections provide the credit
quality indicators we most closely monitor. The credit quality
indicators are generally based on information as of our financial
statement date.
COMMERCIAL CREDIT QUALITY INDICATORS We manage a
consistent process for assessing commercial loan credit quality.
Commercial loans are generally subject to individual risk
assessment using our internal borrower and collateral quality
ratings, which is our primary credit quality indicator. Our ratings
are aligned to regulatory definitions of pass and criticized
categories with the criticized segmented among special mention,
substandard, doubtful and loss categories.
Table 5.7 provides the outstanding balances of our
commercial loan portfolio by risk category and credit quality
information by origination year for term loans. Revolving loans
may convert to term loans as a result of a contractual provision in
the original loan agreement or if modified in a troubled
debt restructuring (TDR). At December 31, 2022, we had
$532.4 billion and $25.1 billion of pass and criticized commercial
loans, respectively.
Wells Fargo & Company 115
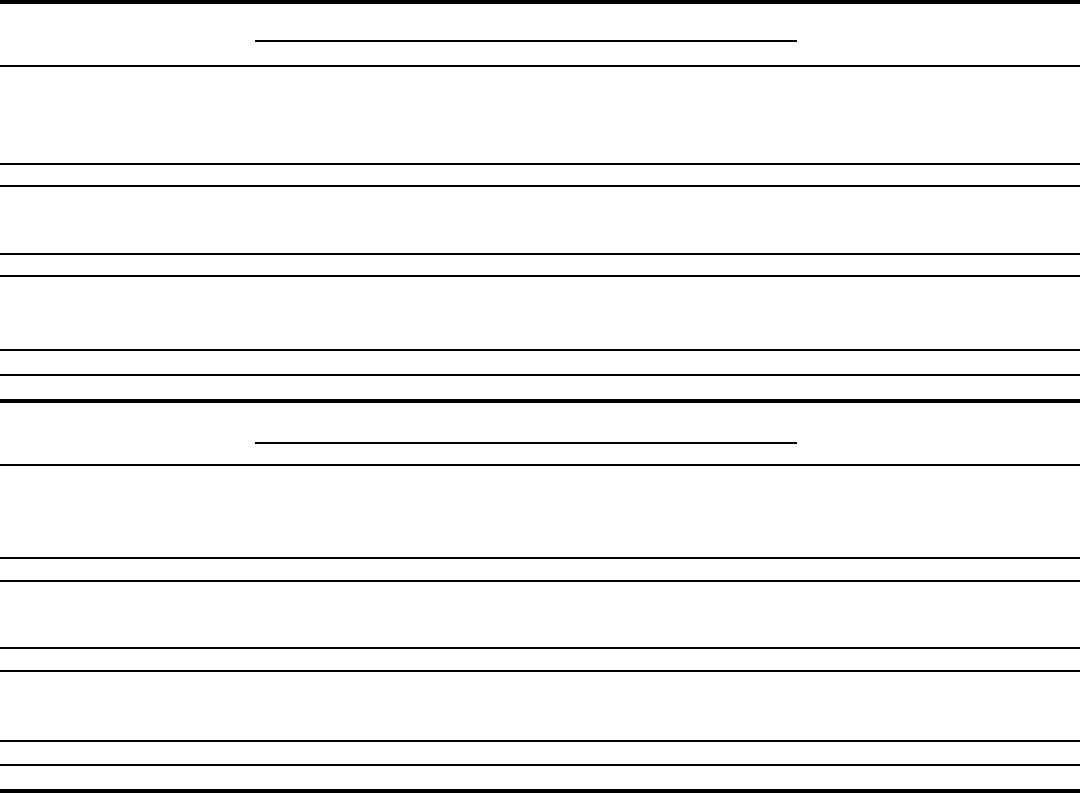
Note 5: Loans and Related Allowance for Credit Losses (continued)
Table 5.7: Commercial Lo an C ategories by Risk C ategories a nd Vintage
(in millions)
Term loans by origination year
Revolving
loans
Revolving
loans
converted to
term loans Total 2022 2021 2020 2019 2018 Prior
December 31, 2022
Commercial and industrial
Pass $ 61,646 31,376 11,128 13,656 3,285 5,739 247,594 842 375,266
Criticized 872 1,244 478 505 665 532 7,244 — 11,540
Total commercial and industrial 62,518 32,620 11,606 14,161 3,950 6,271 254,838 842 386,806
Commercial real estate
Pass 38,022 38,709 16,564 16,409 10,587 16,159 6,765 150 143,365
Criticized 2,785 2,794 965 2,958 1,088 1,688 159 — 12,437
Total commercial real estate 40,807 41,503 17,529 19,367 11,675 17,847 6,924 150 155,802
Lease financing
Pass 4,543 3,336 1,990 1,427 765 1,752 — — 13,813
Criticized 330 275 190 169 94 37 — — 1,095
Total lease financing 4,873 3,611 2,180 1,596 859 1,789 — — 14,908
Total commercial loans $ 108,198 77,734 31,315 35,124 16,484 25,907 261,762 992 557,516
Term loans by origination year
Revolving
loans
Revolving
loans
converted to
term loans Total 2021 2020 2019 2018 2017 Prior
December 31, 2021
Commercial and industrial
Pass $ 65,562 15,193 20,553 7,400 3,797 13,985 211,452 679
338,621
Criticized 1,657 884 1,237 1,256 685 551 5,528 17 11,815
Total commercial and industrial 67,219 16,077 21,790 8,656 4,482 14,536 216,980 696 350,436
Commercial
real estate
Pass 44,091 19,987 23,562 14,785 7,830 16,355 6,453 5 133,068
Criticized 3,972 1,385 3,561 2,068 943 2,428 400 — 14,757
Total commercial real estate 48,063 21,372 27,123 16,853 8,773 18,783 6,853 5 147,825
Lease financing
Pass 4,100 3,012 2,547 1,373 838 1,805 — — 13,675
Criticized 284 246 282 184 86 102 — — 1,184
Total lease financing 4,384 3,258 2,829 1,557 924 1,907 — — 14,859
Total commercial loans $
119,666
40,707 51,742 27,066 14,179 35,226 223,833 701 513,120
Wells Fargo & Company 116
Table 5.8 provides days past due (DPD) information for
commercial loans, which we monitor as part of our credit risk
management practices; however, delinquency is not a primary
credit quality indicator for commercial loans.
Table 5.8: Commercial Loan Categories by Delinquency Status
(in millions)
Still accruing
Nonaccrual loans
Total
commercial loans Current-29 DPD 30-89 DPD 90+ DPD
December 31, 2022
Commercial and industrial $ 384,164 1,313 583 746 386,806
Commercial real estate 153,877 833 134 958 155,802
Lease financing 14,623 166 — 119 14,908
Total commercial loans $ 552,664 2,312 717 1,823 557,516
December 31, 2021
Commercial and industrial $ 348,033 1,217 206 980 350,436
Commercial real estate 146,084 464 29 1,248 147,825
Lease financing 14,568 143 — 148 14,859
Total commercial loans $ 508,685 1,824 235 2,376 513,120
CONSUMER C REDIT QUALITY INDIC ATORS We have various classes
of consumer loans that present unique credit risks. Loan
delinquency, Fair Isaac Corporation (FICO) credit scores and lo an-
to-value (LTV) for residential mortgage loans are the primary
credit quality indicators that we monitor and utilize in our
evaluation of the appropriateness of the ACL for the consumer
loan portfolio segment.
Many of our loss estimation techniques used for the ACL for
loans rely on delinquency-based models; therefore, delinquency
is an important indicator of credit quality in the establishmen t of
our ACL for consumer loans. Credit quality information is
provided with the year of origination for term loans. Revolvin g
loans may convert to term loans as a result of a contractual
provision in the original loan agreement or if modified in a TD R.
We obtain FICO scores at loan origination and the scores
are generally updated at least quarterly, except in limited
circumstances, including compliance with the Fair Credit
Reporting Act (FCRA). FICO scores are not available for certai n
loan types or may not be required if we deem it unnecessary du e
to strong collateral and other borrower attributes.
Table 5.9 provides the outstanding balances of our
residential mortgage loans by our primary credit quality
indicators.
Payment deferral activities in the residential mortgage
portfolio instituted in response to the COVID-19 pandemic coul d
continue to delay the recognition of delinquencies for resident ial
mortgage customers who otherwise would have moved into
past due status. For additional information on customer
accommodations in response to the COVID-19 pandemic, see
Note 1 (Summary of Significant Accounting Policies ) to Financial
Statements in this Report.
LTV refers to the ratio comparing the loan’s outstanding
balance to the property’s collateral value. Combined LTV (CLTV)
refers to the combination of first lien mortgage and junior lien
mortgage (including unused line amounts for credit line
products) ratios. We obtain LTVs and CLTVs using a cascade
approach which first uses values provided by automated
valuation models (AVMs) for the property. If an AVM is not
available, then the value is estimated using the original appraised
value adjusted by the change in Home Price Index (HPI) for the
property location. If an HPI is not available, the original appraised
value is used. The HPI value is normally the only method
considered for high value properties, generally with an original
value of $1 million or more, as the AVM values have proven less
accurate for these properties. Generally, we obtain available LTVs
and CLTVs on a quarterly basis. Certain loans do not have an LTV
or CLTV due to a lack of industry data availability and portfolios
acquired from or serviced by other institutions.
Wells Fargo & Company 117
Note 5: Loans and Related Allowance for Credit Losses (continued)
Table 5.9: Credit Qua lity Ind icators fo r Resid ential Mo rtgage Lo ans by Vinta ge
(in millions)
Term loans by origination year
Revolving
loans
Revolving
loans
converted
to term
loans Total 2022 2021 2020 2019 2018 Prior
December 31, 2022
By delinquency status:
Current-29 DPD $ 48,581 65,705 37,289 20,851 6,190 61,680 11,031 6,913 258,240
30-89 DPD 65 66 32 33 21 683 58 159 1,117
90+ DPD 6 17 15 25 15 530 32 260 900
Government insured/guaranteed loans (1) 9 59 133 148 200 8,311 — — 8,860
Total residential mortgage $ 48,661 65,847 37,469 21,057 6,426 71,204 11,121 7,332 269,117
By FICO:
740+ $ 43,976 61,450 35,221 19,437 5,610 51,551 8,664 4,139 230,048
700-739 3,245 2,999 1,419 941 314 4,740 1,159 1,021 15,838
660-699 1,060 851 438 306 169 2,388 567 656 6,435
620-659 211 248 106 82 50 1,225 223 349 2,494
<620 59 81 44 46 28 1,323 227 466 2,274
No FICO available 101 159 108 97 55 1,666 281 701 3,168
Government insured/guaranteed loans (1) 9 59 133 148 200 8,311 — —
8,860
Total residential mortgage $
48,661
65,847 37,469 21,057 6,426 71,204 11,121 7,332 269,117
By LTV/CLTV
:
0-80% $
40,869
64,613 37,145 20,744 6,155 62,593 10,923 7,188 250,230
80.01-100% 7,670 1,058 112 97 30 107 109 97 9,280
>100% (2)
48 20 13 6 3 23 28 16 157
No LTV available 65 97 66 62 38 170 61 31 590
Government insured/guaranteed loans (1)
9 59 133 148 200 8,311 — — 8,860
Total residential mortgage $
48,661
65,847 37,469 21,057 6,426 71,204 11,121 7,332 269,117
(in millions)
Term
loans
by
origination
year
Revolving
loans
Revolving
loans
converted
to term
loans 2021 2020 2019 2018 2017 Prior
December 31, 2021
By delinquency status:
Current-29 DPD $
70,022
41,547 24,917 7,686 13,755 62,276 16,131 6,099 242,433
30-89 DPD 139 34 32 12 28 558 60 111 974
90+ DPD 1 79 76 75 98 1,458 114 422 2,323
Government insured/guaranteed loans
(1) 14 134 209 349 364 12,088 — — 13,158
Total residential mortgage $
70,176
41,794 25,234 8,122 14,245 76,380 16,305
6,632 258,888
By FICO:
740+ $
64,616
39,168 23,259 7,009 12,584 51,881 12,448 3,568 214,533
700-739 4,129 1,671 1,127 399 766 5,007 1,684 972 15,755
660-699 980 489 358 193 301 2,720 853 653 6,547
620-659 187 122 93 50 55 1,420 352 370 2,649
<620 61 28 40 30 58 1,597 391 467 2,672
No FICO available 189 182 148 92 117 1,667 577 602 3,574
Government insured/guaranteed loans
(1) 14 134 209 349 364 12,088 — — 13,158
Total
residential mortgage $
70,176
41,794 25,234 8,122 14,245 76,380 16,305 6,632 258,888
By LTV/CLTV:
0-80% $
69,511
41,070 24,419 7,544 13,677 63,544 15,300 6,243 241,308
80.01-100% 486 437 474 147 134 394 711 283 3,066
>100%
(2) 15 41 34 15 10 99 186 66 466
No LTV available 150 112 98 67 60 255 108 40 890
Government insured/guaranteed loans (1) 14 134 209 349 364 12,088
— — 13,158
Total residential mortgage $
70,176
41,794 25,234 8,122 14,245 76,380 16,305 6,632 258,888
(1) Government insured or guaranteed loans represent loans whose repayments are predominantly insured by the Federal Housing Administration (FHA) or guaranteed by the Department of Veterans
Affairs (VA). Loans insured/guaranteed by the FHA/VA and 90+ DPD totaled $3.2 billion and $5.7 billion at December 31, 2022 and 2021, respectively.
(2) Reflects total loan balances with LTV/CLTV amounts in excess of 100%. In the event of default, the loss content would generally be limited to only the amount in excess of 100% LTV/CLTV.
Wells Fargo & Company 118
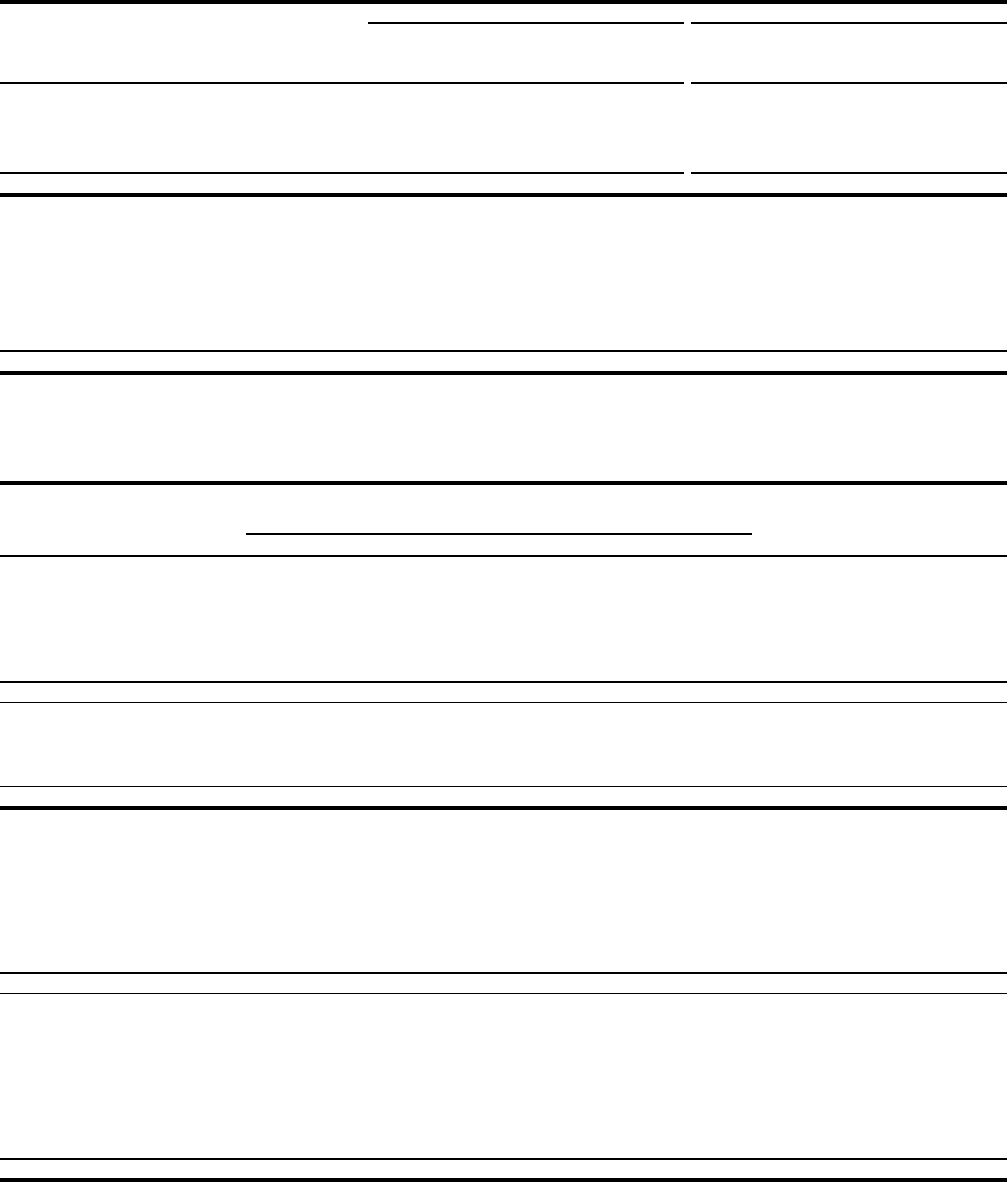
Table 5.10 provides the outstanding balances of our credit
card loan portfolio by primary credit quality indicators.
The revolving loans converted to term loans in the credit
card loan category represent credit card loans with modified
terms that require payment over a specific term.
Table 5.10: Credit Quality Indicators for Credit Card
(in millions)
December 31, 2022 December 31, 2021
Revolving
loans
Revolving
loans
converted to
term loans Total Revolving loans
Revolving loans
converted to
term loans Total
By delinquency status:
Current-29 DPD $ 45,131 223 45,354 37,686 192 37,878
30-89 DPD 457 27 484 294 12 306
90+ DPD 441 14 455 263 6 269
Total credit cards $ 46,029 264 46,293 38,243 210 38,453
By FICO:
740+ $ 16,681 19 16,700 14,240 19 14,259
700-739 10,640 37 10,677 9,254 39 9,293
660-699 9,573 55 9,628 7,934 52 7,986
620-659 4,885 45 4,930 3,753 38 3,791
<620 4,071 107 4,178 2,945 61 3,006
No FICO available 179 1 180 117 1
118
Total credit cards $ 46,029 264 46,293 38,243 210 38,453
Wells Fargo & Company 119
Table 5.11 provides the outstanding balances of our Auto
and Other consumer loan portfolios by primary credit quality
indicators.
Table 5.11: Credit Quality Indicators for Auto and Other Consumer by Vintage
(in millions)
Term loans by origination year
Revolving
loans
Revolving
loans
converted
to term
loans Total 2022 2021 2020 2019 2018 Prior
December 31, 2022
By delinquency status:
Auto
Current-29 DPD $ 19,101 19,126 7,507 4,610 1,445 421 — — 52,210
30-89 DPD 218 585 253 167 69 45 — — 1,337
90+ DPD 23 56 22 13 4 4 — — 122
Total auto $ 19,342 19,767 7,782 4,790 1,518 470 — — 53,669
Other consumer
Current-29 DPD $ 3,718 1,184 341 240 63 83 23,431 117 29,177
30-89 DPD 17 12 2 3 1 2 14 8 59
90+ DPD 5 5 1 1 — 1 13 14 40
Total other consumer $ 3,740 1,201 344 244 64 86 23,458 139 29,276
By FICO:
Auto
740+ $ 9,361 8,233 3,193 2,146 664 166 — — 23,763
700-739 3,090 3,033 1,287 788 238 64 — — 8,500
660-699 2,789 2,926 1,163 641 192
58 — — 7,769
620-659 2,021 2,156 796 421 130 47 — — 5,571
<620 2,062 3,389 1,316 756 263 126 — — 7,912
No FICO available 19 30 27 38 31 9 — — 154
Total auto $
19,342
19,767 7,782 4,790 1,518 470 — — 53,669
Other consu
mer
740+ $
1,908
546 174 112 21 50 1,660 43 4,514
700-739 726 216 62 44 10 13 568 18 1,657
660-699 527 177 34 33 9 8 449 19 1,256
620-659 204 81 13 14 4 5 181 11 513
<620 89 64 14 16 5 5 154 18 365
No FICO available 286 117 47 25 15 5 920 30 1,445
FICO not required
(1) — — — — — — 19,526 — 19,526
Total other consumer $
3,740
1,201 344 244 64 86 23,458 139 29,276
(continued on following page)
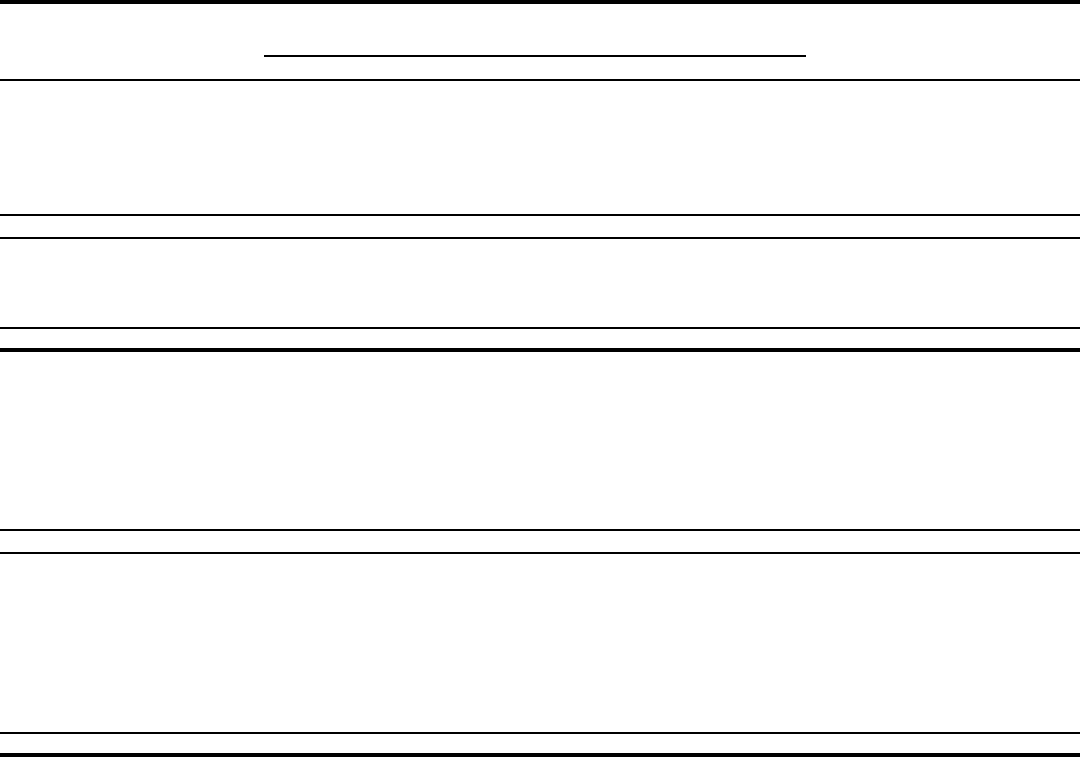
Note 5: Loans and Related Allowance for Credit Losses (continued)
(continued from prev ious pa ge)
(in millions)
Term loans by origination year
Revolving
loans
Revolving
loans
converted
to term
loans Total 2021 2020 2019 2018
2017
Prior
December 31, 2021
By delinquency status:
Auto
Current-29 DPD $ 29,246 12,412 8,476 3,271 1,424 714 — — 55,543
30-89 DPD 289 260 218 106 60 78 — — 1,011
90+ DPD 31 28 23 9 6 8 — — 105
Total auto $ 29,566 12,700 8,717 3,386 1,490 800 — — 56,659
Other consumer
Current-29 DPD $ 2,221 716 703 203 107 125 23,988 143 28,206
30-89 DPD 5 3 5 2 — 3 15 5 38
90+ DPD 1 1 2 1 — 1 13 11 30
Total other consumer $ 2,227 720 710 206 107 129 24,016 159 28,274
By FICO:
Auto
740+ $ 12,029 5,127 4,009 1,566 672 245 — — 23,648
700-739 4,899 2,233 1,519 572 237 112 — — 9,572
660-699 4,953 2,137 1,251 451 190 106 — — 9,088
620-659 3,991 1,453 800 298 135 95
— — 6,772
<620 3,678 1,716 1,126 486 247 232 — — 7,485
No FICO available 16 34 12 13 9 10 — — 94
Total auto $ 29,566 12,700 8,717 3,386 1,490 800 — — 56,659
Other consumer
740+ $ 1,197 382 303 85 19 77 2,509 49 4,621
700-739 412 116 110 39 9 18 713 25 1,442
660-699 261 68 79 31 8 12 490 20 969
620-659 91 24 34 14 4 5 193 13 378
<620 31 17 29 14 5 7 160 16 279
No FICO available 235 113 155 23 62 10 1,236 36 1,870
FICO not required
(1) — — — — — — 18,715 — 18,715
Total other consumer $ 2,227 720 710 206 107 129 24,016 159 28,274
(1) Substantially all loans not requiring a FICO score are securities-based loans originated by the Wealth and Investment Management operating segment.
Wells Fargo & Company 120
NONACCRUAL LOANS Table 5.12 provides loans on nonaccrual
status. Nonaccrual loans may have an ACL or a negative
allowance for credit losses from expected recoveries of amount s
previously written off. Customer payment deferral activities i n
the residential mortgage portfolio instituted in response to th e
COVID-19 pandemic could continue to delay the recognition of
nonaccrual loans for those residential mortgage customers who
would have otherwise moved into nonaccrual status.
Table 5.12: Nonaccrual Lo ans
Amortized cost Recognized interest income
Nonaccrual loans
Nonaccrual loans without related
allowance for credit losses (1) Year ended December 31,
(in millions)
Dec 31,
2022
Dec 31,
2021
Dec 31,
2022
Dec 31,
2021 2022 2021
Commercial and industrial $ 746 980 174 190 63 97
Commercial real estate
958 1,248 134 71 54 69
Lease financing 119 148 5 9 — —
Total commercial
1,823
2,376
313
270
117
166
Residential mortgage
3,611
4,604
2,316
3,219
211
175
Auto
153
198
—
—
26
34
Other consumer 39 34 — — 4 3
Total consumer 3,803 4,836 2,316 3,219 241 212
Total nonaccrual loans $ 5,626 7,212 2,629 3,489 358 378
(1) Nonaccrual loa ns m ay not have a n a llowance for credit losses if t he loss exp ectations a re zer o g iven t he r elated collateral v alue.
LOANS IN PROCESS OF FORECLOSURE Our recorded investment in
consumer mortgage loans collateralized by residential real estate
property that are in process of foreclosure was $1.0 billion and
$694 million at December 31, 2022 and 2021, respectively,
which included $771 million and $583 million, respectively, of
loans that are government insured/guaranteed. Under the
Consumer Financial Protection Bureau guidelines, we do not
commence the foreclosure process on residential mortgage loans
until after the loan is 120 days delinquent. Foreclosure
procedures and timelines vary depending on whether the
property address resides in a judicial or non-judicial state. Judicial
states require the foreclosure to be processed through the
state’s courts while non-judicial states are processed without
court intervention. Foreclosure timelines vary according to
state law.
Wells Fargo & Company 121
LOANS 90 DAYS OR MORE PAST DUE AND STILL ACCRUING Certain
loans 90 days or more past due are still accruing, because they
are (1) well-secured and in the process of collection or (2)
residential mortgage or consumer loans exempt under regulatory
rules from being classified as nonaccrual until later delinquency,
usually 120 days past due.
Table 5.13 shows loans 90 days or more past due and still
accruing by class for loans not government insured/guaranteed.
Table 5.13: Loans 90 Days or More Past Due and Still Accruing
($ in millions)
Dec 31,
2022
Dec 31,
2021
Total: $ 4,340 5,358
Less: FHA insured/VA guaranteed (1) 3,005 4,699
Total, not government insured/guaranteed $ 1,335 659
By segment and class, not government insured/
guaranteed:
Commercial and industrial $ 583 206
Commercial real estate 134 29
Total commercial 717 235
Residential mortgage 28 49
Credit card 455 269
Auto 111 88
Other consumer 24 18
Total consumer 618 424
Total, not government insured/guaranteed $ 1,335 659
Note 5: Loans and Related Allowance for Credit Losses (continued)
(1) Represents loans whose repayments are predominantly insured by the FHA or guaranteed
by the VA.
TROUBLED DEBT RES TRUCTURINGS (TDRs) When, for economic or
legal reasons related to a borrower’s financial difficulties, w e
grant a concession for other than an insignificant period of ti me
to a borrower that we would not otherwise consider, the related
loan is classified as a TDR, the balance of which totaled
$9.2 billion and $10.2 billion at December 31, 2022 and 2021,
respectively. We do not consider loan resolutions such as
foreclosure or short sale to be a TDR. In addition, COVID-19 -
related modifications are generally not classified as TDRs due to
the relief under the CARES Act and the Interagency Statement.
For additional information on the TDR relief, see Note 1
(Summary of Significant Accounting Policies) in this Report .
We may require some consumer borrowers experiencing
financial difficulty to make trial payments generally for a period
of three to four months, according to the terms of a planned
permanent modification, to determine if they can perform
according to those terms. These arrangements represent trial
modifications, which we classify and account for as TDRs. While
loans are in trial payment programs, their original terms are not
considered modified and they continue to advance through
delinquency status and accrue interest according to their original
terms.
Commitments to lend additional funds on loans whose
terms have been modified in a TDR amounted to $434 million
and $431 million at December 31, 2022 and 2021, respectively.
Table 5.14 summarizes our TDR modifications for the
periods presented by primary modification type and includes the
financial effects of these modifications. For those loans that
modify more than once, the table reflects each modification that
occurred during the period. Loans that both modify and are paid
off or written-off within the period, as well as changes in
recorded investment during the period for loans modified in prior
periods, are not included in the table.
Wells Fargo & Company 122
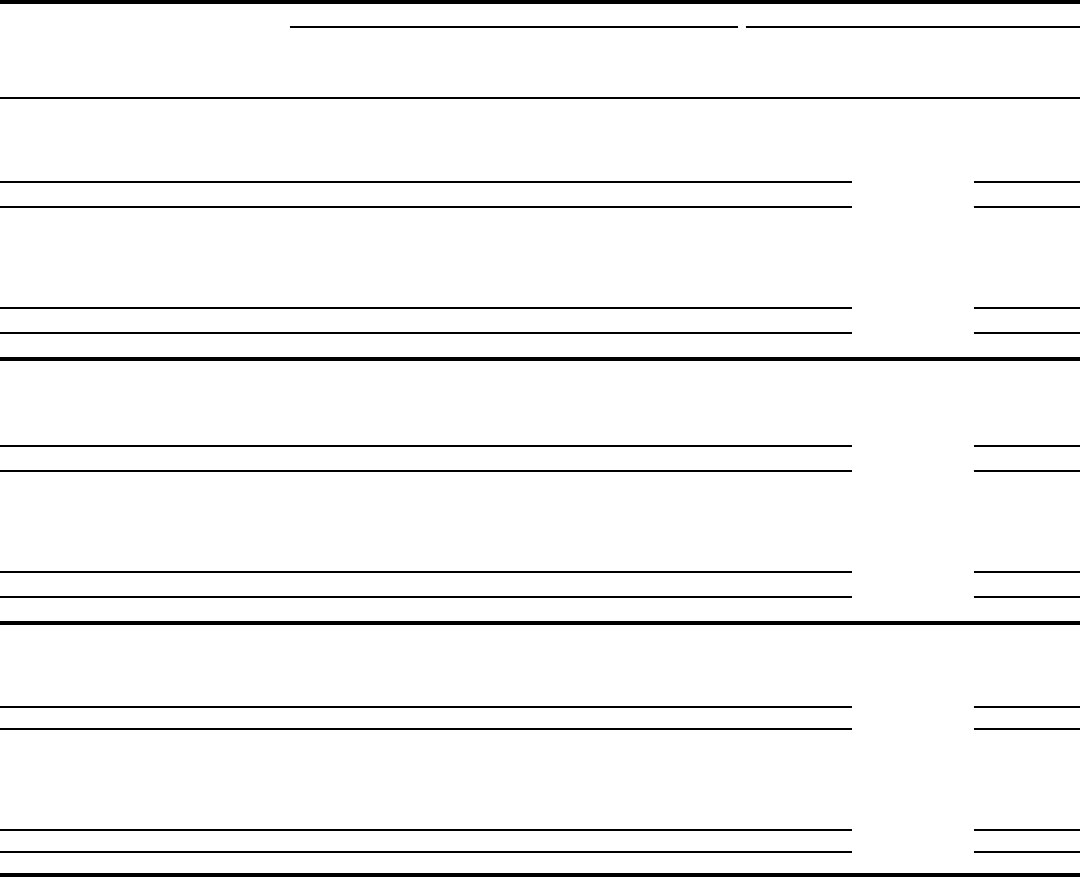
Table 5.14: TDR Modifications
Primary modification type (1) Financial effects of modifications
($ in millions)
Principal
forgiveness
Interest
rate
reduction
Other
concessions (2) Total
Charge-
offs (3)
Weighted
average
interest
rate
reduction
Recorded
investment
related to
interest rate
reduction (4)
Year Ended December 31, 2022
Commercial and industrial $ 24 24 349 397 — 10.69% $ 24
Commercial real estate — 12 112 124 — 0.92 12
Lease financing — — 2 2 — — —
Total commercial 24 36 463 523 — 7.51 36
Residential mortgage 1 369 1,357 1,727 6 1.61 369
Credit card — 311 — 311 — 20.33 311
Auto 2 7 63 72 16 4.33 7
Other consumer — 19 3 22 1 11.48 19
Trial modifications (5) — — 228 228 — — —
Total consumer 3 706 1,651 2,360 23 10.14 706
Total $ 27 742 2,114 2,883 23 10.02% $ 742
Year Ended December 31, 2021
Commercial and industrial $ 2 9 879 890 20 0.81% $ 9
Commercial real estate 41 15 259 315 — 1.28 14
Lease financing — — 7 7 — — —
Total commercial 43 24 1,145 1,212 20 1.11 23
Residential mortgage — 70 1,324 1,394 3 1.80 70
Credit card — 106 — 106 — 19.12 106
Auto 1 4 131 136 54 3.82 4
Other consumer — 18 1 19 — 11.83 18
Trial modifications (5) — — (3) (3) — — —
Total consumer 1 198 1,453 1,652 57 12.01 198
Total $ 44 222 2,598 2,864 77 10.84% $ 221
Year Ended December 31, 2020
Commercial and industrial $ 24 47 2,971 3,042 162 0.74% $ 48
Commercial real estate 10 35 684 729 5 1.11 35
Lease financing — — 1 1 — — —
Total commercial 34 82 3,656 3,772 167 0.90 83
Residential mortgage — 25 4,277 4,302 7 1.93 51
Credit card — 272 — 272 — 14.12 272
Auto 4 6 166 176 93 4.65 6
Other consumer — 23 34 57 1 8.28 23
Trial modifications (5) — — 3 3 — — —
Total consumer 4 326 4,480 4,810 101 11.80 352
Total $ 38 408 8,136 8,582 268 9.73% $ 435
(1) Amounts r epresent the r ecorded investment in loa ns a fter recognizing the effect s of t he TD R, if a ny. TDRs m ay have m ultiple t ypes of concessions, but are p resented only once in t he fir st
modification t ype b ased on t he or der presented in t he t able a bove. The r eported amounts inclu de loa ns r emodified of $445 m illion, $737 m illion, and $1.5 b illion for the y ears end ed December 31,
2022, 2021 a nd 2020, respectively.
(2) Other concessions inclu de loa ns wit h payment (principal a nd/or interest) d eferral, loans d ischarged in b ankruptcy, loan r enewals, term extensions a nd other interest and noninterest adjustments, but
exclude m odifications t hat also for give p rincipal a nd/or reduce t he cont ractual int erest rate. The r eported amounts inclu de loa ns t hat are new TD Rs t hat may have C OVID-19-related payment
deferrals a nd exclude C OVID-19-related payment deferrals on loa ns p reviously reported as TD Rs g iven lim ited current financial effect s ot her than p ayment deferral.
(3) Charge-offs inclu de wr ite-downs of t he inv estment in t he loa n in t he p eriod it is cont ractually modified. The a mount of ch arge-off will d iffer from the m odification t erms if t he loa n h as b een ch arged
down p rior to t he m odification b ased on ou r policies. In a ddition, there m ay be ca ses wh ere we h ave a charge-off/down wit h no leg al p rincipal m odification.
(4) Recorded investment related to int erest rate r eduction r eflects t he effect of r educed interest rates on loa ns wit h an int erest rate concession a s one of t heir concession t ypes, which includes loa ns
reported as a principal p rimary modification t ype t hat also h ave a n int erest rate concession.
(5) Trial m odifications a re g ranted a delay in p ayments d ue u nder the or iginal t erms d uring the t rial p ayment period. However, these loa ns cont inue t o a dvance t hrough delinquency status a nd accrue
interest according to t heir original t erms. Any subsequent permanent modification g enerally includes int erest rate r elated concessions; however, the exa ct concession t ype a nd resulting financial
effect are u sually not known u ntil t he loa n is p ermanently modified. Trial m odifications for the p eriod are p resented net of p reviously reported trial m odifications t hat became p ermanent in t he
current period.
Wells Fargo & Company 123
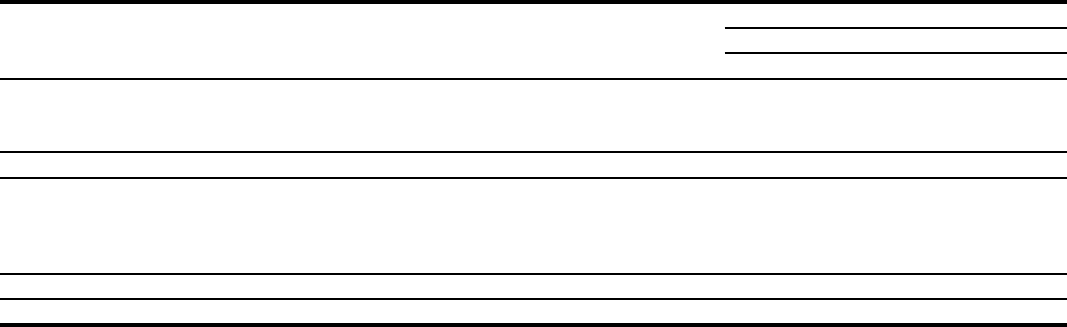
Note 5: Loans and Related Allowance for Credit Losses (continued)
Table 5.15 summarizes permanent modification TDRs that
have defaulted in the current period within 12 months of their
permanent modification date. We are reporting these defaulted
TDRs based on a payment default definition of 90 days past due
for the commercial portfolio segment and 60 days past due for
the consumer portfolio segment.
Table 5.15: Defaulted TDRs
Recorded investment of defaults
Year ended December 31,
(in millions) 2022 2021 2020
Commercial and industrial $ 55 132 677
Commercial real estate 14 34 128
Lease financing — 1 1
Total commercial 69 167 806
Residential mortgage 142 13 46
Credit card 43 25 72
Auto 21 43 32
Other consumer 2 3 5
Total consumer 208 84 155
Total $ 277 251 961
Wells Fargo & Company 124
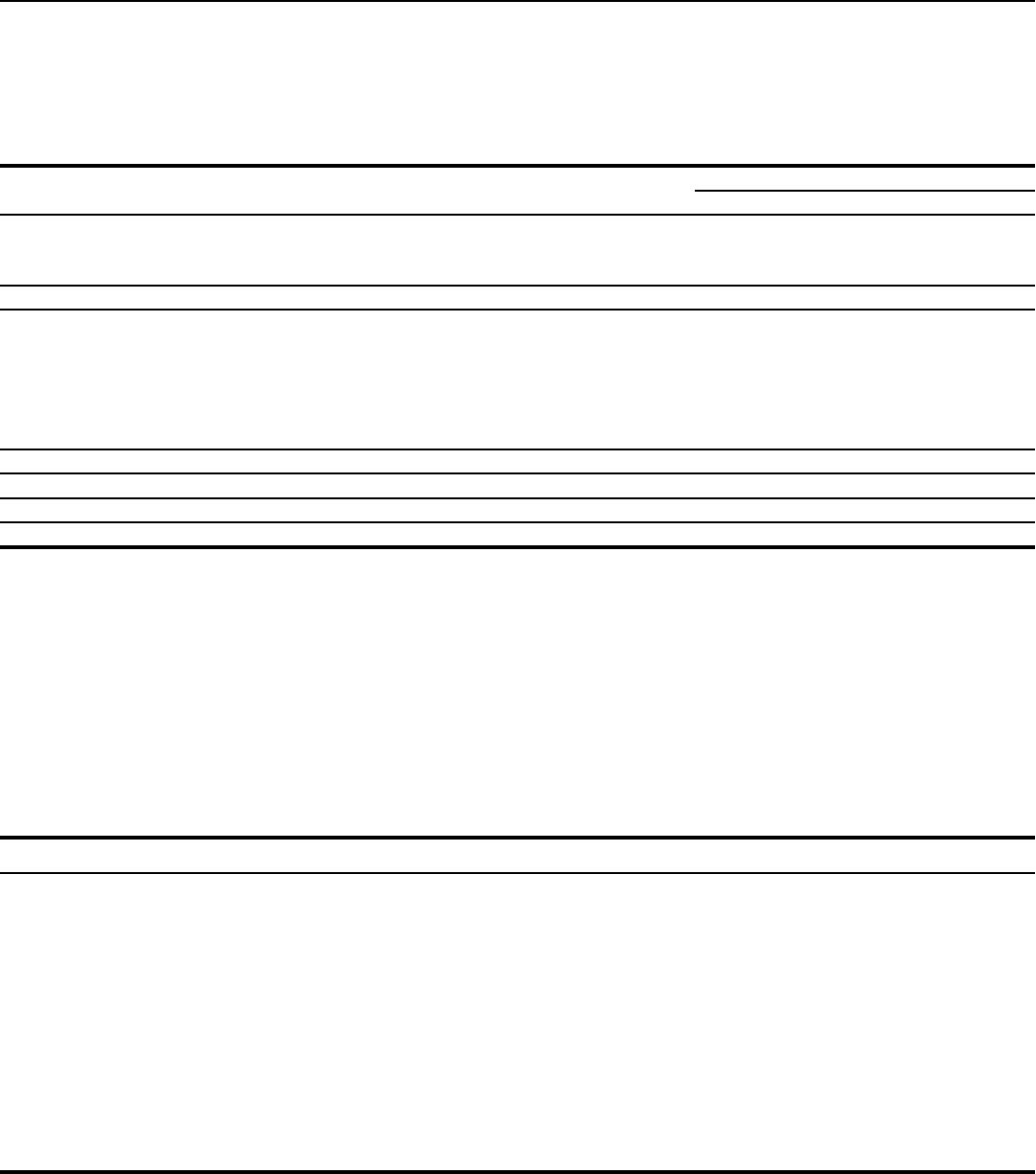
Note 6: Mortgage Banking Activities
Mortgage banking activities consist of residential and
commercial mortgage originations, sales and servicing.
We apply the amortization method to commercial MSRs and
apply the fair value method to residential MSRs. The amortized
cost of commercial MSRs was $1.2 billion, $1.3 billion and
$1.3 billion, with an estimated fair value of $2.1 billion,
$1.5 billion, and $1.4 billion, at December 31, 2022, 2021 and
2020, respectively. Table 6.1 presents the changes in MSRs
measured using the fair value method.
Table 6.1: Analysis of Changes in Fair Value MSRs
Year ended December 31,
(in millions) 2022 2021 2020
Fair value, beginning of period $ 6,920 6,125 11,517
Servicing from securitizations or asset transfers (1) 1,003 1,645 1,708
Sales and other (2) (614) (8) (32)
Net additions 389 1,637 1,676
Changes in fair value:
Due to valuation inputs or assumptions:
Mortgage interest rates (3) 3,417 1,625 (3,946)
Servicing and foreclosure costs (4) (17) (9) (175)
Discount rates (5) 42 (56) 27
Prepayment estimates and other (6) (188) (390) (599)
Net changes in valuation inputs or assumptions 3,254 1,170 (4,693)
Changes due to collection/realization of expected cash flows (7) (1,253) (2,012) (2,375)
Total changes in fair value 2,001 (842) (7,068)
Fair value, end of period $ 9,310 6,920 6,125
(1) Includes impacts associated with exercising cleanup calls on securitizations and our right to repurchase delinquent loans from GNMA loan securitization pools. MSRs may increase upon repurchase
due to servicing liabilities associated with these delinquent GNMA loans.
(2) Includes sales and transfers of MSRs, which can result in an increase in MSRs if related to portfolios with servicing liabilities. For the year ended December 31, 2022, MSRs decreased $611 million due
to the sale of interest-only strips related to excess servicing cash flows from agency residential mortgage-backed securitizations.
(3) Includes prepayment rate changes as well as other valuation changes due to changes in mortgage interest rates. To reduce exposure to changes in interest rates, MSRs are economically hedged with
derivative instruments.
(4) Includes costs to service and unreimbursed foreclosure costs.
(5) In 2022, we enhanced our approach for estimating the discount rates to a more dynamic methodology for market curves and volatility, which had a nominal impact.
(6) Represents other changes in valuation model inputs or assumptions including prepayment rate estimation changes that are independent of mortgage interest rate changes.
(7) Represents the reduction in the MSR fair value for the cash flows expected to be collected during the period, net of income accreted due to the passage of time.
Table 6.2 provides key weighted-average assumptions used
in the valuation of residential MSRs and sensitivity of the cur rent
fair value of residential MSRs to immediate adverse changes in
those assumptions. Amounts for residential MSRs include
purchased servicing rights as well as servicing rights resulting
from the transfer of loans. See Note 15 (Fair Values of Assets
and Liabilities) for additional information on key assumptions for
residential MSRs.
Table 6.2: Assumptions and Sensitivity of Residential MSRs
($ in millions, except cost to service amounts)
Dec 31,
2022
Dec 31,
2021
Fair value of interests held $ 9,310 6,920
Expected weighted-average life (in years) 6.3 4.7
Key assumptions:
Prepayment rate assumption (1) 9.4 % 14.7
Impact on fair value from 10% adverse change $ 288 356
Impact on fair value from 25% adverse change 688 834
Discount rate assumption 9.1 % 6.4
Impact on fair value from 100 basis point increase $ 368 276
Impact on fair value from 200 basis point increase 707 529
Cost to service assumption ($ per loan) 102 106
Impact on fair value from 10% adverse change 171 165
Impact on fair value from 25% adverse change 427 411
(1) Includes a blend of prepayment speeds and expected defaults. Prepayment speeds are influenced by mortgage interest rates as well as our estimation of drivers of borrower behavior.
The sensitivities in the preceding table are hypothetical and
caution should be exercised when relying on this data. Changes in
value based on variations in assumptions generally cannot be
extrapolated because the relationship of the change in the
assumption to the change in value may not be linear. Also, the
effect of a variation in a particular assumption on the value of the
other interests held is calculated independently without changing
any other assumptions. In reality, changes in one factor may
result in changes in others, which might magnify or counteract
the sensitivities.
Wells Fargo & Company 125
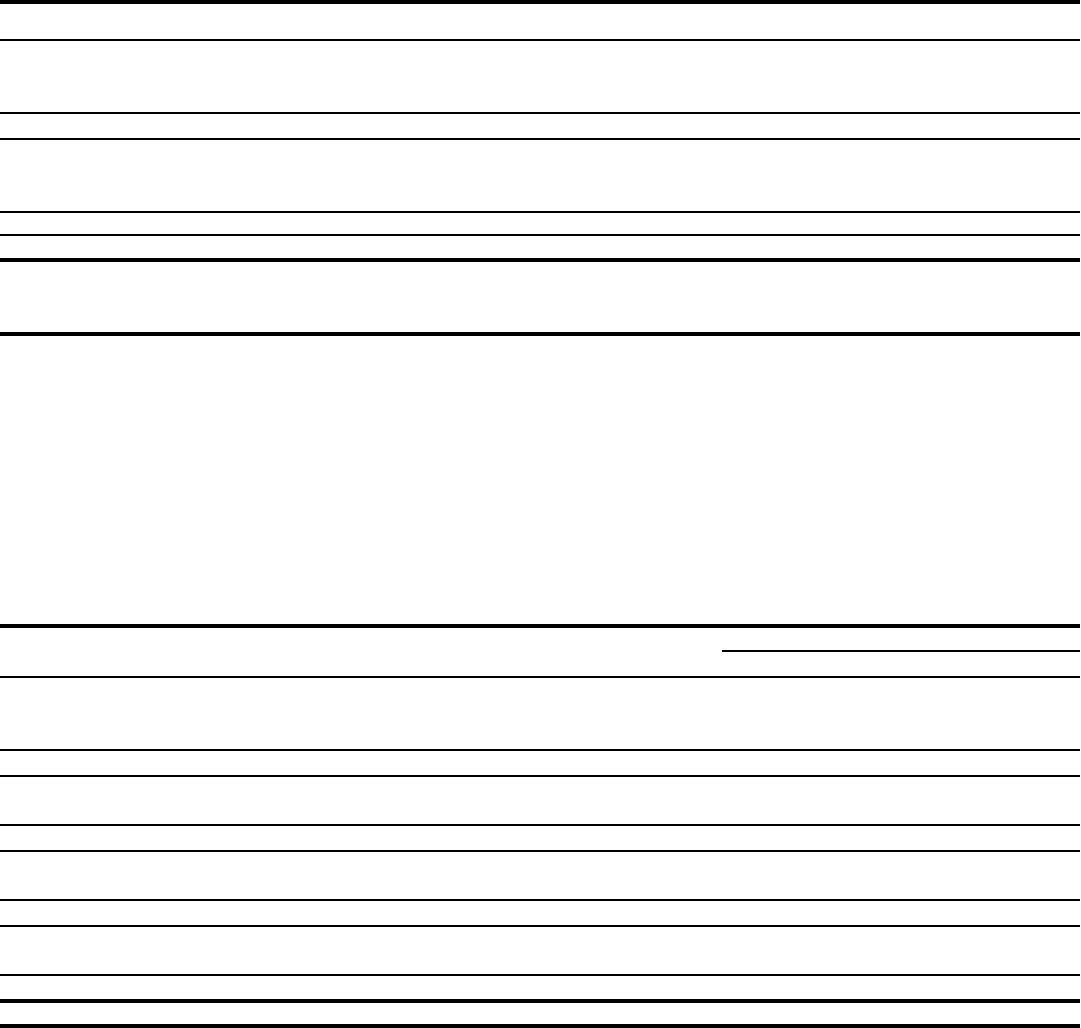
Note 6: Mortgage Banking Activities (continued)
We present the components of our managed servicing
portfolio in Table 6.3 at unpaid principal balance for loans
serviced and subserviced for others and at carrying value for
owned loans serviced.
Table 6.3: Managed Servicing Portfolio
(in billions)
Dec 31,
2022
Dec 31,
2021
Residential mortgage servicing:
Serviced and subserviced for others $ 681 718
Owned loans serviced 273 276
Total residential servicing 954 994
Commercial mortgage servicing:
Serviced and subserviced for others 577 597
Owned loans serviced 133 130
Total commercial servicing 710 727
Total managed servicing portfolio $ 1,664 1,721
Total serviced for others, excluding subserviced for others $ 1,246 1,304
MSRs as a percentage of loans serviced for others
0.84 % 0.63
Weighted average note rate (mortgage loans serviced for others)
4.30 3.82
At December 31, 2022 and 2021, we had servicer advances,
net of an allowance for uncollectible amounts, of $2.5 billion and
$3.2 billion, respectively. As the servicer of loans for others, we
advance certain payments of principal, interest, taxes, insurance,
and default-related expenses which are generally reimbursed
within a short timeframe from cash flows from the trust,
government-sponsored entities (GSEs), insurer or borrower.
The credit risk related to these advances is limited since the
reimbursement is generally senior to cash payments to investors.
We also advance payments of taxes and insurance for our owned
loans which are collectible from the borrower. We maintain an
allowance for uncollectible amounts for advances on loans
serviced for others that may not be reimbursed if the payments
were not made in accordance with applicable servicing
agreements or if the insurance or servicing agreements contain
limitations on reimbursements. Servicing advances on owned
loans are charged-off when deemed uncollectible.
Table 6.4 presents the components of mortgage banking
noninterest income.
Table 6.4: Mortgage Banking Noninterest Income
Year ended December 31,
(in millions) 2022 2021 2020
Servicing fees:
Contractually specified servicing fees, late charges and ancillary fees $ 2,475 2,801 3,250
Unreimbursed direct servicing costs (1) (189) (332) (620)
Servicing fees 2,286 2,469 2,630
Amortization (2) (247) (225) (308)
Changes due to collection/realization of expected cash flows (3) (A) (1,253) (2,012) (2,375)
Net servicing fees 786 232 (53)
Changes in fair value of MSRs due to valuation inputs or assumptions (4) (B) 3,254 1,170 (4,693)
Net derivative gains (losses) from economic hedges (5) (3,507) (1,208) 4,607
Market-related valuation changes to MSRs, net of hedge results (253) (38) (86)
Total net servicing income 533 194 (139)
Net gains on mortgage loan originations/sales (6) 850 4,762 3,632
Total mortgage banking noninterest income $ 1,383 4,956 3,493
Total changes in fair value of MSRs carried at fair value (A)+(B) $ 2,001 (842) (7,068)
(1) Includes costs associated with foreclosures, unreimbursed interest advances to investors, and other interest costs.
(2) Includes a $4 million and $41 million reversal of impairment on the commercial amortized MSRs in 2022 and 2021, respectively, and a $37 million impairment on the commercial amortized MSRs in
2020.
(3) Represents the reduction in the MSR fair value for the cash flows expected to be collected during the period, net of income accreted due to the passage of time.
(4) Refer to the analysis of changes in fair value MSRs presented in Table 6.1 in this Note for more detail.
(5) See Note 14 (Derivatives) for additional discussion and detail on economic hedges.
(6) Includes net gains (losses) of $2.5 billion, $1.2 billion and $(1.8) billion at December 31, 2022, 2021 and 2020, respectively, related to derivatives used as economic hedges of mortgage loans held for
sale and derivative loan commitments.
Wells Fargo & Company 126
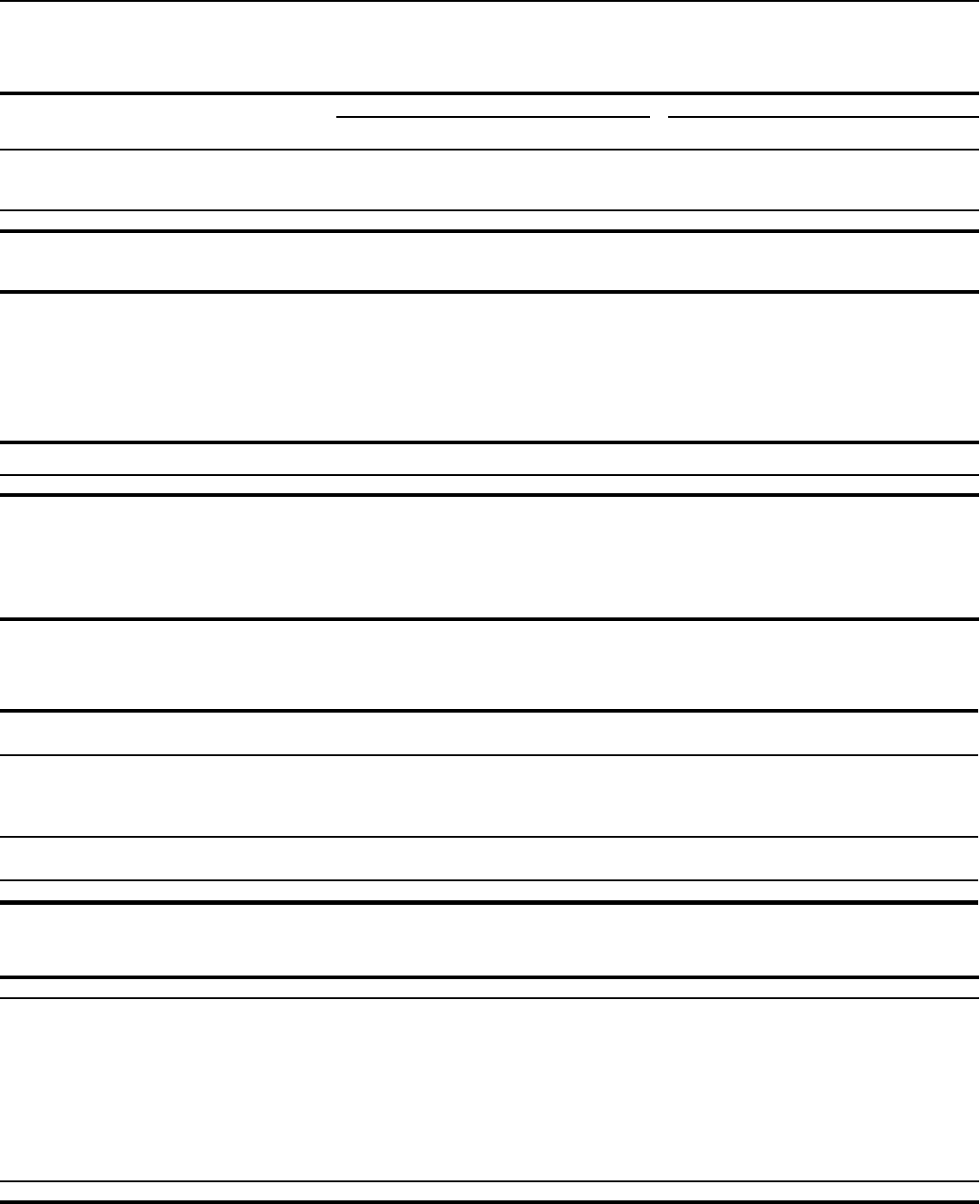
Note 7: Intangible Assets and Other Assets
Table 7.1 presents the gross carrying value of intangible assets
and accumulated amortization.
Table 7.1: Intangible Assets
December 31, 2022 December 31, 2021
(in millions)
Gross carrying
value
Accumulated
amortization
Net carrying
value
Gross carrying
value
Accumulated
amortization
Net carrying
value
Amortized intangible assets (1):
MSRs (2) $ 4,942 (3,772) 1,170 4,794 (3,525) 1,269
Customer relationship and other intangibles 754 (602) 152 842 (631) 211
Total amortized intangible assets $ 5,696 (4,374) 1,322 5,636 (4,156) 1,480
Unamortized intangible assets:
MSRs (carried at fair value) $ 9,310 6,920
Goodwill 25,173 25,180
(1) Balances are excluded commencing in the period following full amortization.
(2) There was no valuation allowance recorded for amortized MSRs at December 31, 2022, and a $4 million valuation allowance recorded at December 31, 2021. See Note 6 (Mortgage Banking
Activities) for additional information on MSRs.
Table 7.2 provides the current year and estimated future
amortization expense for amortized intangible assets. We based
our projections of amortization expense shown below on existin g
asset balances at December 31, 2022. Future amortization
expense may vary from these projections.
Table 7.2: Amortization Expense for Intangible Assets
(in millions) Amortized MSRs
Customer relationship
and other intangibles Total
Year ended December 31, 2022 (actual) $ 247 59 306
Estimate for year ended December 31,
2023 $ 238 51 289
2024 201 41 242
2025 176 33 209
2026 141 27 168
2027
111 — 111
Table 7.3 shows the allocation of goodwill to our reportable
operating segments.
Table 7.3: Goodwill
(in millions)
Consumer
Banking and
Lending
Commercial
Banking
Corporate and
Investment
Banking
Wealth and
Investment
Management Corporate
Consolidated
Company
December 31, 2020 $ 16,418 3,018 5,375 1,276 305 26,392
Foreign currency translation — — — — — —
Transfers of goodwill — (80) — (932) 1,012 —
Divestitures — — — — (1,212) (1,212)
December 31, 2021 $ 16,418 2,938 5,375 344 105 25,180
Foreign currency translation — (7) — — — (7)
December 31, 2022 $ 16,418
2,931 5,375 344 105 25,173
Table 7.4 presents the components of other assets.
Table 7.4: Other Assets
(in millions) Dec 31, 2022 Dec 31, 2021
Corporate/bank-owned life insurance (1) $ 20,807 20,619
Accounts receivable (2) 23,646 20,831
Interest receivable:
AFS and HTM debt securities 1,572 1,360
Loans 3,470 1,950
Trading and other 767 305
Operating lease assets (lessor) 5,790 6,182
Operating lease ROU assets (lessee) 3,837 3,805
Other (3) 15,945 12,207
Total other assets $ 75,834 67,259
(1) Corporate/bank-owned life insurance is recorded at cash surrender value.
(2) Primarily includes derivatives clearinghouse receivables, trade date receivables, and servicer advances, which are recorded at amortized cost.
(3) Primarily includes income tax receivables, prepaid expenses, foreclosed assets, and private equity and venture capital investments in consolidated portfolio companies.
Wells Fargo & Company 127
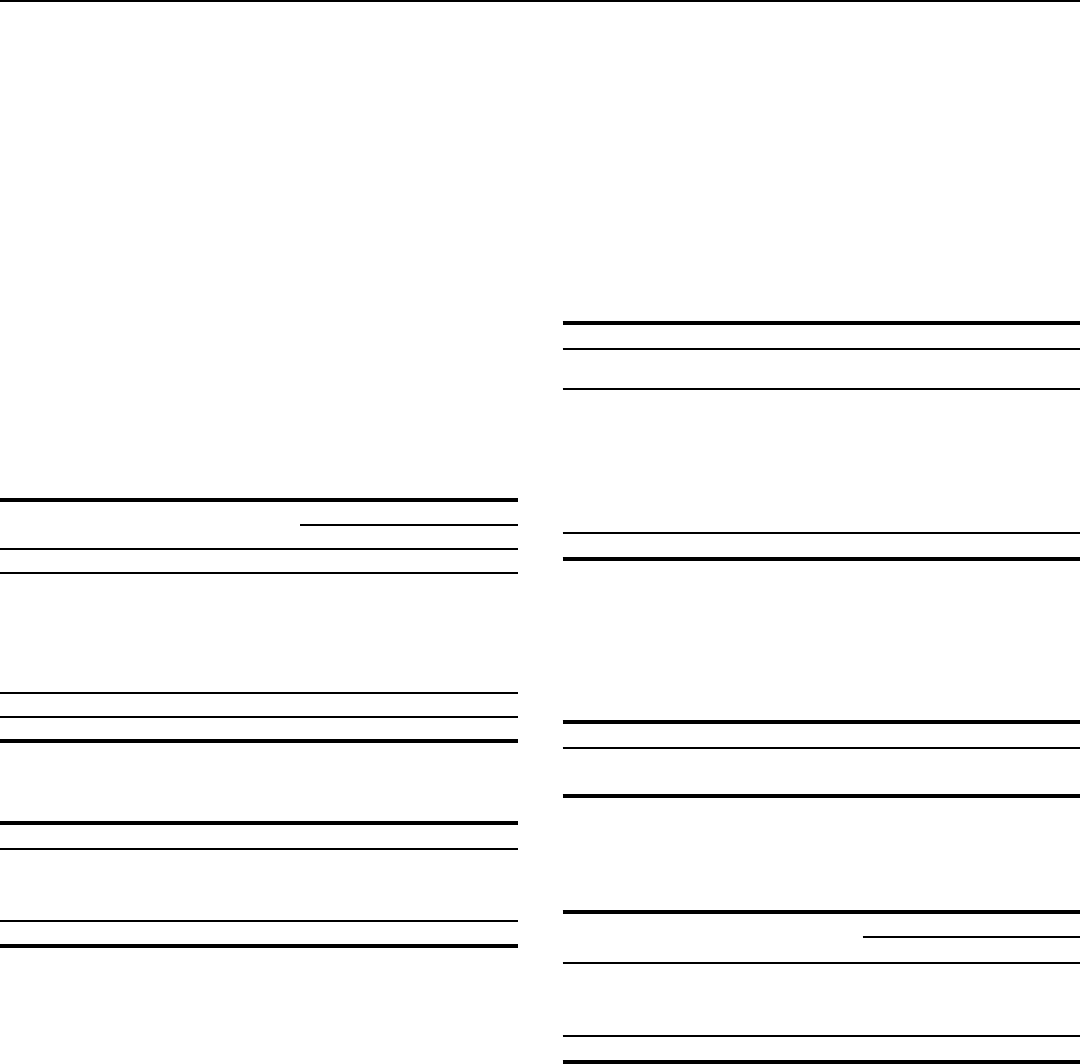
Note 8: Leasing Activity
The information below provides a summary of our leasing
activities as a lessor and lessee.
As a Lessor
Table 8.1 presents the composition of our leasing revenue and
Table 8.2 provides the components of our investment in lease
financing. Noninterest income on leases, included in Table 8.1 is
included in other noninterest income on our consolidated
statement of income. Lease expense, included in other
noninterest expense on our consolidated statement of income,
was $750 million, $867 million, and $1.0 billion for the years
ended December 31, 2022, 2021 and 2020, respectively.
In 2021, we recognized an impairment charge of
$268 million due to weakening demand for certain rail cars used
for transportation of coal products. There were no impairments
of rail cars as of December 31, 2022. Our rail car leasing business
is in Corporate for our operating segment disclosures. For
additional information on the accounting for impairment of
operating lease assets, see Note 1 (Summary of Significant
Accounting Policies).
Table 8.1: Leasing Revenue
Year ended December 31,
(in millions) 2022 2021 2020
Interest income on lease financing $ 600 683 853
Other lease revenue:
Variable revenue on lease financing 114 101 107
Fixed revenue on operating leases 972 995 1,169
Variable revenue on operating leases 58 64 47
Other lease-related revenue (1) 125 (164) (78)
Noninterest income on leases 1,269 996 1,245
Total leasing revenue $ 1,869 1,679 2,098
(1) Includes net gains (losses) on disposition of assets leased under operating leases or lease
financings, and impairment charges.
Table 8.2: Investment in Lease Financing
(in millions) Dec 31, 2022 Dec 31, 2021
Lease receivables $ 13,139 12,756
Residual asset values 3,554 3,721
Unearned income (1,785) (1,618)
Lease financing $
14,908
14,859
Our net investment in financing and sales-type leases
included $789 million and $1.0 billion of leveraged leases at
December 31, 2022 and 2021, respectively.
As shown in Table 7.4, included in Note 7 (Intangible Assets
and Other Assets), we had $5.8 billion and $6.2 billion in
operating lease assets at December 31, 2022 and 2021,
respectively, which was net of $3.1 billion of accumulated
depreciation for both periods. Depreciation expense for the
operating lease assets was $477 million, $604 million and
$755 million in 2022, 2021 and 2020, respectively.
Table 8.3 presents future lease payments owed by our
lessees.
Table 8.3: Maturities of Lease Receivables
December 31, 2022
(in millions)
Direct financing and
sales- type leases Operating leases
2023 $ 4,260 571
2024 3,265 437
2025 2,221 320
2026 1,260 193
2027 649 120
Thereafter 1,484 164
Total lease receivables $ 13,139 1,805
As a Lessee
Substantially all of our leases are operating leases. Table 8.4
presents balances for our operating leases.
Table 8.4: Operating Lease Right-of-Use (ROU) Assets and Lease
Liabilities
(in millions) Dec 31, 2022 Dec 31, 2021
ROU assets $ 3,837 3,805
Lease liabilities 4,465 4,476
Table 8.5 provides the composition of our lease costs, which
are predominantly included in net occupancy expense.
Table 8.5: Lease Costs
Year ended December 31,
(in millions) 2022 2021 2020
Fixed lease expense – operating leases
$
1,022
1,048
1,149
Variable lease expense
277
289
299
Other
(1)
(37)
(93)
(77)
Total lease costs
$
1,262
1,244
1,371
(1) Predominantly includes gains recognized from sale leaseback transactions and sublease
rental income.
Wells Fargo & Company 128
Table 8.6 provides the future lease payments under
operating leases as well as information on the remaining average
lease term and discount rate as of December 31, 2022.
Table 8.6: Lease Payments on Operating Leases
(in millions, except for weighted averages) Dec 31, 2022
2023 $ 883
2024 947
2025 772
2026 633
2027 488
Thereafter 1,142
Total lease payments 4,865
Less: imputed interest 400
Total operating lease liabilities $ 4,465
Weighted average remaining lease term (in years) 6.5
Weighted average discount rate 2.6 %
Our operating leases predominantly expire within the next
15 years, with the longest lease expiring in 2105. We do not
include renewal or termination options in the establishment of
the lease term when we are not reasonably certain that we will
exercise them. As of December 31, 2022, we had additional
operating leases commitments of $654 million, predominantly
for real estate, which leases had not yet commenced. These
leases are expected to commence during 2024 and have lease
terms of 3 years to 20 years.
Wells Fargo & Company 129

Note 9: Deposits
Table 9.1 presents a summary of both time certificates of
deposit (CDs) and other time deposits issued by domestic and
non-U.S. offices.
Table 9.1: Time Deposits
December 31,
(in millions) 2022 2021
Total domestic and Non-U.S. $ 66,887 30,012
Time deposits in excess of $250,000 9,133 5,527
The contractual maturities of time deposits are presented in
Table 9.2.
Table 9.2: Contractual Maturities of Time Deposits
(in millions) December 31, 2022
2023
$
52,445
2024
12,654
2025
693
2026 255
2027 474
Thereafter 366
Total $
66,887
Demand deposit overdrafts of $339 million and $153 million
were included as loan balances at December 31, 2022 and 2021,
respectively.
Wells Fargo & Company 130
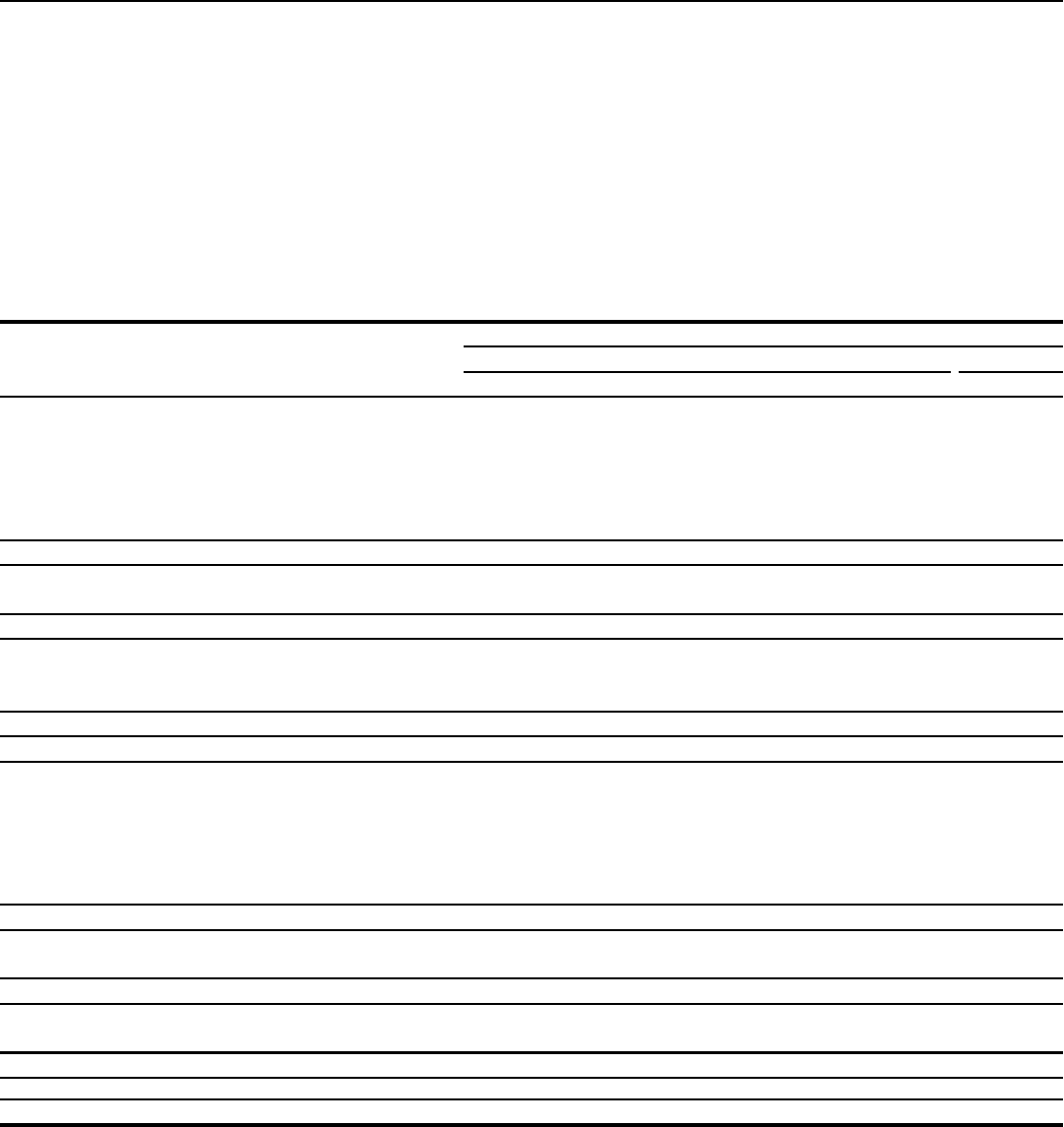
Note 10: Long-Term Debt
We issue long-term debt denominated in multiple currencies,
predominantly in U.S. dollars. Our issuances , which are generally
unsecured, have both fixed and floating interest rates. Princip al is
repaid upon contractual maturity, unless redeemed at our optio n
at an earlier date. Interest is paid primarily on either a semi -
annual or annual basis.
As a part of our overall interest rate risk management
strategy, we often use derivatives to manage our exposure to
interest rate risk. We also use derivatives to manage our
exposure to foreign currency risk. As a result, a majority of the
long-term debt presented below is hedged in a fair value or cash
flow hedge relationship.
Table 10.1 presents a summary of our long-term debt
carrying values, reflecting unamortized debt discounts and
premiums, and hedge basis adjustments; unless we have elected
the fair value option. See Note 14 (Derivatives) for additional
information on qualifying hedge contracts and Note 15 (Fair
Values of Assets and Liabilities) for additional information on fair
value option elections. The interest rates displayed represent the
range of contractual rates in effect at December 31, 2022. These
interest rates do not include the effects of any associated
derivatives designated in a hedge accounting relationship.
Table 10.1: Long-Term Debt
December 31,
2022 2021
(in
millions)
Maturity
date(s)
Stated
interest
rate(s)
Wells Fargo & Company (Parent only)
Senior
Fixed-rate notes
2023-2045
0.50-6.75%
$
43,749
62,525
Floating-rate notes
2026-2048
3.49-4.74%
1,046
5,535
FixFloat notes
2024-2053
0.81-5.01%
60,752
43,010
Structured notes
(1)
6,305
5,874
Total senior debt – Parent
111,852
116,944
Subordinated
Fixed-rate notes
(2)
2023-2046
3.45-7.57%
21,379
27,970
Total subordinated debt – Parent
21,379
27,970
Junior subordinated
Fixed-rate notes
2029-2036
5.95-7.95%
827
1,041
Floating-rate notes
2027
4.58-5.08%
343
331
Total
junior
subordinated
debt
–
Parent
(3)
1,170
1,372
Total long-term debt – Parent
(2)
134,401
146,286
Wells Fargo Bank
, N.A., and other bank
entities (Bank
)
Senior
Floating-rate notes
2038-2053
4.21-4.54%
117
116
Floating-rate advances – Federal Home Loan Bank (FHLB)
(4)
2023-2024
3.71-4.93%
27,000
—
Structured notes
(1)
262
307
Finance leases
2023-2029
1.13-17.78%
22
26
Total senior debt – Bank
27,401
449
Subordinated
Fixed-rate notes
2023-2038
5.25-7.74%
4,305
5,387
Total subordinated debt – Bank
4,305
5,387
Junior subordinated
Floating-rate notes
2027
4.73-5.18%
401
388
Total junior subordinated debt – Bank
(3)
401
388
Other bank debt
(5)
2023-2062
0.24-9.50%
7,082
6,634
Total long-term debt – Bank
$
39,189
12,858
(continued on following page)
Wells Fargo & Company 131
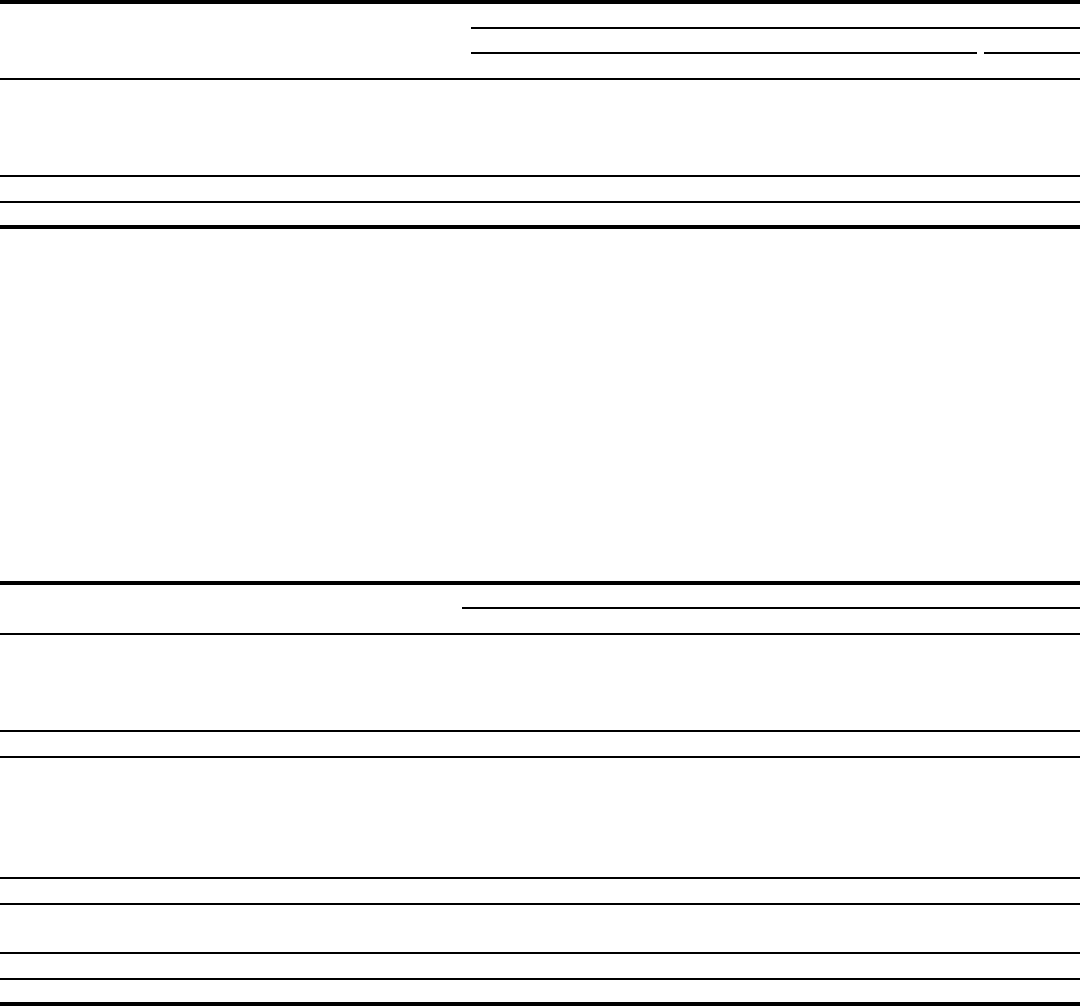
Note 10: Long-Term Debt (continued)
(continued from previous page)
December 31,
2022 2021
(in millions) Maturity date(s) Stated interest rate(s)
Other consolidated su bsidiaries
Senior
Fixed-rate
notes 2023 3.46% $
369
398
Structured
notes
(1) 911
1,147
Total
long-term
debt
–
Other
consolidated
subsidiaries 1,280
1,545
Total
long-term
debt
(6) $
174,870
160,689
(1) Includes certain structured notes that have coupon or repayment terms linked to the performance of debt or equity securities, an embedded equity, commodity, or currency index, or basket of
indices, for which the maturity may be accelerated based on the value of a referenced index or security. In addition, a major portion consists of zero coupon notes where interest is paid as part of the
final redemption amount.
(2) Includes fixed-rate subordinated notes issued by the Parent at a discount of $121 million and $123 million at December 31, 2022 and 2021, respectively, and debt issuance costs of $2 million at both
December 31, 2022 and 2021, to effect a modification of Wells Fargo Bank, N.A., notes. These subordinated notes are carried at their par amount on the consolidated balance sheet of the Parent
presented in Note 26 (Parent-Only Financial Statements). In addition, Parent long-term debt presented in Note 26 also includes affiliate related issuance costs of $365 million and $329 million at
December 31, 2022 and 2021, respectively.
(3) Includes $401 million and $388 million of junior subordinated debentures held by unconsolidated wholly-owned trust preferred security VIEs at December 31, 2022 and 2021, respectively. In 2021,
we liquidated certain of our trust preferred security VIEs. As part of these liquidations, junior subordinated debentures that were held by the trusts with a total carrying value of $332 million, were
distributed to third-party investors. See Note 16 (Securitizations and Variable Interest Entities) for additional information about trust preferred security VIEs.
(4) We pledge certain assets as collateral to secure advances from the FHLB. For additional information, see Note 18 (Pledged Assets and Collateral).
(5) Primarily relates to unfunded commitments for LIHTC investments. For additional information, see Note 16 (Securitizations and Variable Interest Entities).
(6) A major portion of long-term debt is redeemable at our option at one or more dates prior to contractual maturity.
The aggregate carrying value of long-term debt that
matures (based on contractual payment dates) as of
December 31, 2022, in each of the following five years and
thereafter is presented in Table 10.2.
Table 10.2: Maturity of Long-Term Debt
December 31, 2022
(in millions) 2023 2024 2025 2026 2027 Thereafter Total
Wells Fargo & Company (Parent Only)
Senior debt $ 3,712 11,116 14,030 23,189 7,392 52,413 111,852
Subordinated debt 2,620 702 951 2,631 2,343 12,132 21,379
Junior subordinated debt — — — — 343 827 1,170
Total long-term debt – Parent 6,332 11,818 14,981 25,820 10,078 65,372 134,401
Wells Fargo Bank, N.A., and other bank entities (Bank)
Senior debt 10,003 17,003 176 82 3 134 27,401
Subordinated debt 894 — 149 — 27 3,235 4,305
Junior subordinated debt — — — — 401 — 401
Other bank debt 2,815 1,613 488 163 54 1,949 7,082
Total long-term debt – Bank 13,712 18,616 813 245 485 5,318 39,189
Other consolidated subsidiaries
Senior debt 463 86 413 222 — 96 1,280
Total long-term debt – Other consolidated subsidiaries 463 86 413 222 — 96 1,280
Total long-term debt $ 20,507 30,520 16,207 26,287 10,563 70,786 174,870
As part of our long-term and short-term borrowing
arrangements, we are subject to various financial and operational
covenants. Some of the agreements under which debt has been
issued have provisions that may limit the merger or sale of
certain subsidiary banks and the issuance of capital stock or
convertible securities by certain subsidiary banks. At
December 31, 2022, we were in compliance with all the
covenants.
Wells Fargo & Company 132
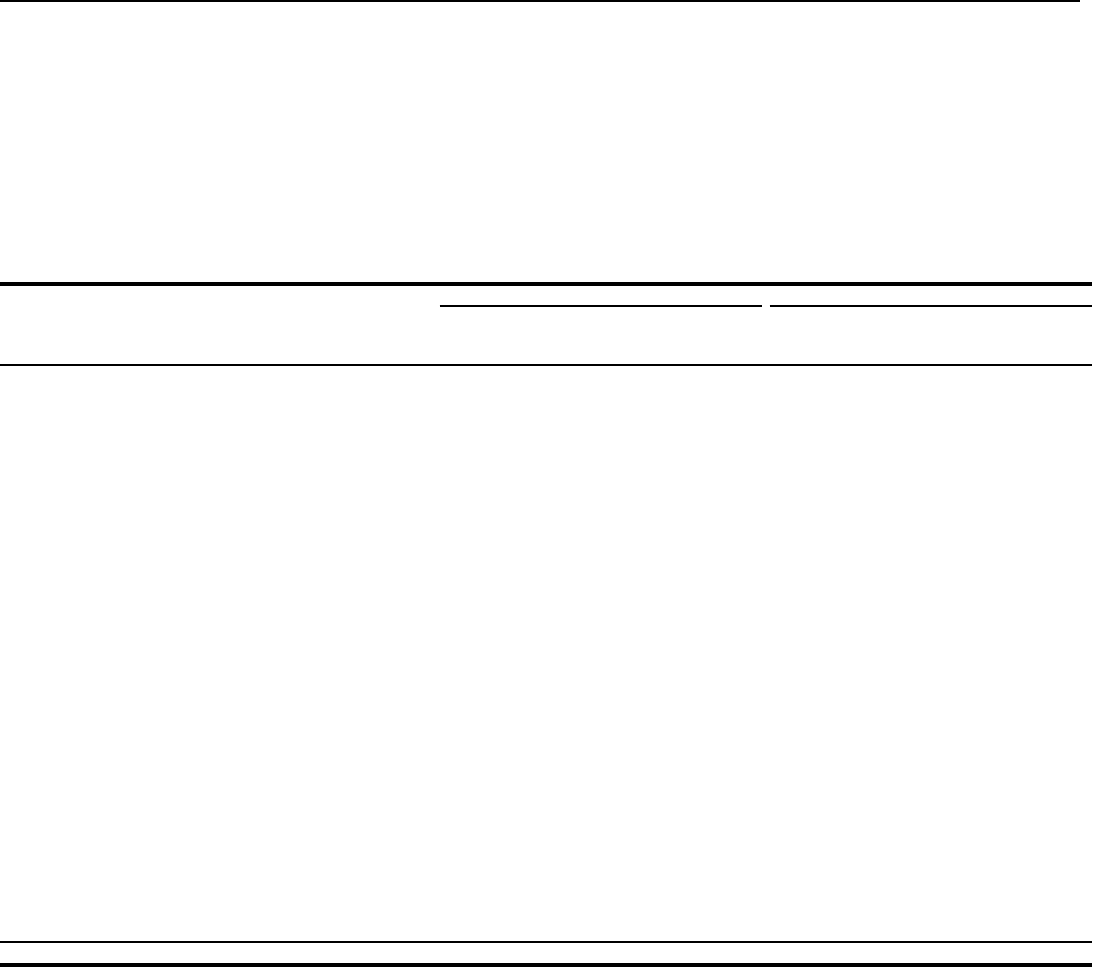
Note 11: Preferred Stock
We are authorized to issue 20 million shares of preferred stock,
without par value. Outstanding preferred shares rank senior to
common shares both as to the payment of dividends and
liquidation preferences but have no general voting rights. All
outstanding preferred stock with a liquidation preference value,
except for Series L Preferred Stock, may be redeemed for the
liquidation preference value, plus any accrued but unpaid
dividends, on any dividend payment date on or after the earliest
redemption date for that series. Additionally, these same series
of preferred stock may be redeemed following a “regulatory
capital treatment event”, as described in the terms of each series.
Capital actions, including redemptions of our preferred stock,
may be subject to regulatory approval or conditions.
In addition, we are authorized to issue 4 million shares of
preference stock, without par value. We have not issued any
preference shares under this authorization. If issued, preference
shares would be limited to one vote per share.
Table 11.1 summarizes information about our preferred
stock.
Table 11.1: Preferred Stock
December 31, 2022 December 31, 2021
(in m illions, except shares)
Earliest
redemption
date
Shares
authorized
and
designated
Shares
issued and
outstanding
Liquidation
preference
value
Carrying
value
Shares
authorized
and
designated
Shares
issued and
outstanding
Liquidation
preference
value
Carrying
value
DEP Shares
Dividend Equalization Preferred Shares (DEP) Currently
redeemable
97,000 96,546 $ — — 97,000 96,546 $ — —
Preferred Stock:
Series L (1)
7.50% Non-Cumulative Per petual C onvertible C lass A — 4,025,000
3,967,986
3,968 3,200 4,025,000
3,967,995 3,968 3,200
Series Q
5.85% Fixed-to-Floating Non-Cumulative Per petual C lass A 9/15/2023 69,000 69,000 1,725 1,725 69,000 69,000 1,725 1,725
Series R
6.625% Fixed-to-Floating Non-Cumulative Per petual C lass A 3/15/2024 34,500 33,600 840 840 34,500 33,600 840 840
Series S
5.90% Fixed-to-Floating Non-Cumulative Perpetual Class A 6/15/2024 80,000 80,000 2,000 2,000 80,000 80,000 2,000 2,000
Series U
5.875% Fixed-to-Floating Non-Cumulative Per petual C lass A 6/15/2025 80,000 80,000 2,000 2,000 80,000 80,000 2,000 2,000
Series Y
5.625% Non-Cumulative Perpetual Class A Currently
redeemable
27,600 27,600 690 690 27,600 27,600 690 690
Series Z
4.75% Non-Cumulative Perpetual Class A 3/15/2025 80,500 80,500 2,013 2,013 80,500 80,500 2,013 2,013
Series AA
4.70% Non-Cumulative Perpetual Class A 12/15/2025 46,800 46,800 1,170 1,170 46,800 46,800 1,170 1,170
Series BB
3.90% Fixed-Reset Non-Cumulative Perpetual Class A 3/15/2026 140,400 140,400 3,510 3,510 140,400 140,400 3,510 3,510
Series CC
4.375% Non-Cumulative Perpetual Class A 3/15/2026 46,000 42,000 1,050 1,050 46,000 42,000 1,050 1,050
Series DD
4.25% Non-Cumulative Perpetual Class A 9/15/2026 50,000 50,000 1,250 1,250 50,000 50,000 1,250 1,250
ESOP (2)
Cumulative Convertible — — — — 609,434 609,434 609 609
Total 4,776,800 4,714,432 $ 20,216 19,448 5,386,234 5,323,875 $ 20,825 20,057
(1) At the option of the holder, each share of Series L Preferred Stock may be converted at any time into 6.3814 shares of common stock, plus cash in lieu of fractional shares, subject to anti-dilution
adjustments. If converted within 30 days of certain liquidation or change of control events, the holder may receive up to 16.5916 additional shares, or, at our option, receive an equivalent amount of
cash in lieu of common stock. We may convert some or all of the Series L Preferred Stock into shares of common stock if the closing price of our common stock exceeds 130 percent of the
conversion price of the Series L Preferred Stock for 20 trading days during any period of 30 consecutive trading days. We declared dividends of $298 million on Series L Preferred Stock in each of the
years 2022, 2021 and 2020.
(2) See the “ESOP Cumulative Convertible Preferred Stock” section in this Note for additional information.
Wells Fargo & Company 133
Note 11: Preferred Stock (continued)
ESOP C UMULATIVE C ONVERTIBLE PREFERRED S TOCK All shares
of our ESOP Cumulative Convertible Preferred Stock (ESOP
Preferred Stock) were issued to a trustee acting on behalf of
the Wells Fargo & Company 401(k) Plan (the 401(k) Plan). In
October 2022, we redeemed all outstanding shares of our ESOP
Preferred Stock in exchange for shares of the Company’s
common stock. The redemption price was based on a fair market
value of $618 million .
Dividends on the ESOP Preferred Stock were cumulative
from the date of initial issuance and were payable quarterly a t
annual rates based upon the year of issuance. Each share of ESO P
Preferred Stock released from the unallocated reserve of the
401(k) Plan was converted into shares of our common stock
based on the stated value of the ESOP Preferred Stock and the
then current market price of our common stock. The ESOP
Preferred Stock was also convertible at the option of the holde r
at any time, unless previously redeemed. We had the option to
redeem the ESOP Preferred Stock at any time, in whole or in
part, at a redemption price per share equal to the higher of (a )
$1,000 per share plus accrued and unpaid dividends or (b) the fair
market value, as defined in the Certificates of Designation fo r the
ESOP Preferred Stock.
Table 11.2: ESOP Preferred Stock
Shares issued and outstanding Carrying value Adjustable dividend rate
(in millions, except shares)
Dec 31,
2022
Dec 31,
2021
Dec 31,
2022
Dec 31,
2021 Minimum Maximum
ESOP Preferred Stock
$1,000 liqu idation preference per share
2018 — 189,225 $ — 189 7.00 % 8.00 %
2017 — 135,135 — 135 7.00 8.00
2016 — 128,380 — 128 9.30 10.30
2015 — 68,106 — 68 8.90 9.90
2014 — 62,420 — 63 8.70 9.70
2013 — 26,168 — 26 8.50 9.50
Total ESOP Preferred Stock (1) — 609,434 $ — 609
Unearned ESOP shares (2) $ — (646)
(1) At December 31, 2021, additional paid-in capital included $37 million related to ESOP Preferred Stock.
(2) We recorded a corresponding charge to unearned ESOP shares in connection with the issuance of the ESOP Preferred Stock. See Note 12 (Common Stock and Stock Plans) for additional information.
Wells Fargo & Company 134

Note 12: Common Stock and Stock Plans
Common Stock
Table 12.1 presents our reserved, issued and authorized shares of
common stock at December 31, 2022.
Table 12.1: Common Stock Shares
Number of shares
Shares reserved (1) 303,203,184
Shares issued 5,481,811,474
Shares not reserved or issued 3,214,985,342
Total shares authorized 9,000,000,000
(1) Shares reserved for employee stock plans (employee restricted share rights, performance
share awards, 401(k), and deferred compensation plans), convertible securities, dividend
reinvestment and common stock purchase plans, and director plans.
We repurchase shares to meet common stock issuance
requirements for our benefit plans, share awards, conversion of
our convertible securities, acquisitions and other corporate
purposes. Various factors determine the amount and timing of
our share repurchases, including our capital requirements, the
number of shares we expect to issue for acquisitions and
employee benefit plans, market conditions (including the trading
price of our stock), and regulatory and legal considerations.
These factors can change at any time, and there can be no
assurance as to the number of shares we will repurchase or when
we will repurchase them.
Dividend Reinvestment and Common Stock
Purchase Plans
Participants in our dividend reinvestment and common stock
direct purchase plans may purchase shares of our common stock
at fair market value by reinvesting dividends and/or making
optional cash payments under the plan’s terms.
Employee Stock Plans
We offer stock-based employee compensation plans as
described below. For additional information on our accounting
for stock-based compensation plans, see Note 1 (Summary of
Significant Accounting Policies).
LONG-TERM INCENTIVE PLANS We have granted restricted share
rights (RSRs) and performance share awards (PSAs) as our
primary long-term incentive awards.
Holders of RSRs and PSAs may be entitled to receive
additional RSRs and PSAs (dividend equivalents) or cash
payments equal to the cash dividends that would have been paid
had the RSRs or PSAs been issued and outstanding shares of
common stock. RSRs and PSAs granted as dividend equivalents
are subject to the same vesting schedule and conditions as the
underlying award.
Table 12.2 summarizes the major components of stock
compensation expense and the related recognized tax benefit.
Table 12.2: Stock Compensation Expense
Year ended December 31,
(in millions)
2022
2021 2020
RSRs $ 947 931 732
Performance shares (1) 31 74 (110)
Total stock compensation expense $ 978 1,005 622
Related recognized tax benefit
$ 242 248 154
(1) Compensation expense fluctuates with the estimated outcome of satisfying performance
conditions and, for certain awards, changes in our stock price.
The total number of shares of common stock available for
grant under the plans at December 31, 2022, was 129 million.
Restricted Share Rights
Holders of RSRs are entitled to the related shares of common
stock at no cost generally vesting over three to five years after
the RSRs are granted. A summary of the status of our RSRs at
December 31, 2022, and changes during 2022 is presented in
Table 12.3.
Table 12.3: Restricted Share Rights
Number
Weighted-
average
grant-date
fair value
Nonvested at January 1, 2022 51,604,179 $ 37.98
Granted 24,793,104 51.80
Vested (20,380,394) 42.30
Canceled or forfeited (2,779,746) 44.18
Nonvested at December 31, 2022 53,237,143 42.44
The weighted-average grant date fair value of RSRs granted
during 2021 and 2020 was $32.99 and $42.53, respectively.
At December 31, 2022, there was $986 million of total
unrecognized compensation cost related to nonvested RSRs. The
cost is expected to be recognized over a weighted-average
period of 2.4 years. The total fair value of RSRs that vested
during 2022, 2021 and 2020 was $1.0 billion, $902 million and
$981 million, respectively.
Performance Share Awards
Holders of PSAs are entitled to the related shares of common
stock at no cost subject to the Company’s achievement of
specified performance criteria over a three-year period. PSAs
are granted at a target number based on the Company’s
performance. The number of awards that vest can be adjusted
downward to zero and upward to a maximum of either 125% or
150% of target. The awards vest in the quarter after the end of
the performance period. For PSAs whose performance period
ended December 31, 2022, the determination of the number of
performance shares that will vest will occur in first quarter 2023
after review of the Company’s performance by the Human
Resources Committee of the Board.
Wells Fargo & Company 135
Note 12: Common Stock and Stock Plans (continued)
A summary of the status of our PSAs at December 31, 2022,
and changes during 2022 is in Table 12.4, based on the
performance adjustments recognized as of December 2022.
Table 12.4: Performance Share Awards
Number
Weighted-average
grant-date fair value (1)
Nonvested at January 1, 2022 4,682,969 $ 36.63
Granted 1,011,080 $ 52.80
Vested (392,241) $ 50.50
Canceled or forfeited (793,471) $ 49.36
Nonvested at December 31, 2022 4,508,337 $ 36.81
(1) Reflects approval date fair value for grants subject to variable accounting.
The weighted-average grant date fair value of performance
awards granted during 2021 and 2020 was $32.76 and $40.39,
respectively.
At December 31, 2022, there was $33 million of total
unrecognized compensation cost related to nonvested
performance awards. The cost is expected to be recognized over
a weighted-average period of 1.9 years. The total fair value of
PSAs that vested during 2022, 2021 and 2020 was $19 million,
$31 million and $35 million, respectively.
Stock Options
Stock options have not been issued in the last three years and no
stock options were outstanding at December 31, 2022, 2021 and
2020.
Director Awards
We granted common stock awards to non-employee directors
elected or re-elected at the annual meeting of stockholders on
April 26, 2022. These stock awards vest immediately.
Employee Stock Ownership Plan
The Wells Fargo & Company 401(k) Plan (401(k) Plan) is a
defined contribution plan with an Employee Stock Ownership
Plan (ESOP) feature. We have previously loaned money to the
401(k) Plan to purchase ESOP Preferred Stock that was
convertible into common stock over time as the loans were
repaid. The Company’s annual contribution to the 401(k) Plan, as
well as dividends received on unreleased shares, are used to make
payments on the loans. As the loans are repaid, shares are
released from the unallocated reserve of the 401(k) Plan.
In October 2022, we redeemed all outstanding shares of our
ESOP Preferred Stock in exchange for shares of the Company’s
common stock. For additional information see Note 11
(Preferred Stock).
Shares that are not yet released are reflected on our
consolidated balance sheet as unearned ESOP shares. Released
common stock is allocated to the 401(k) Plan participants and
invested in the Wells Fargo ESOP Fund within the 401(k) Plan.
Dividends on the allocated common shares reduce retained
earnings, and the shares are considered outstanding for
computing earnings per share. Dividends on the unreleased
common stock or ESOP Preferred Stock do not reduce retained
earnings, and the unreleased shares are not considered to be
common stock equivalents for computing earnings per share.
Table 12.5 presents the information related to the
Wells Fargo ESOP Fund and the dividends paid to the 401(k)
Plan.
Table 12.5: Wells Fargo ESOP Fund
December 31,
(in millions, except shares)
2022
2021 2020
Allocated shares outstanding (common) 152,438,152 149,638,081 155,810,091
Unreleased shares outstanding (common) 10,329,650 — —
Fair value of unreleased shares outstanding (common)
$ 427 — —
Unreleased shares outstanding (preferred) — 609,434 822,242
Conversion value of unreleased ESOP preferred shares
$ — 609 822
Fair value of unreleased ESOP preferred shares based on redemption
— 700 990
Year ended December 31,
Dividends paid on (in millions):
2022
2021 2020
Allocated shares (common) $ 134 74 155
Unreleased shares (common)
4 — —
Unreleased shares (preferred)
36 66 77
Wells Fargo & Company 136

Note 13: Legal Actions
Wells Fargo and certain of our subsidiaries are involved in a
number of judicial, regulatory, governmental, arbitration, and
other proceedings or investigations concerning matters arising
from the conduct of our business activities, and many of those
proceedings and investigations expose Wells Fargo to potential
financial loss or other adverse consequences. These proceedings
and investigations include actions brought against Wells Fargo
and/or our subsidiaries with respect to corporate-related
matters and transactions in which Wells Fargo and/or our
subsidiaries were involved. In addition, Wells Fargo and our
subsidiaries may be requested to provide information to or
otherwise cooperate with government authorities in the conduct
of investigations of other persons or industry groups. We
establish accruals for legal actions when potential losses
associated with the actions become probable and the costs can
be reasonably estimated. For such accruals, we record the
amount we consider to be the best estimate within a range of
potential losses that are both probable and estimable; however, if
we cannot determine a best estimate, then we record the low
end of the range of those potential losses. There can be no
assurance as to the ultimate outcome of legal actions, including
the matters described below, and the actual costs of resolving
legal actions may be substantially higher or lower than the
amounts accrued for those actions.
AUTOMOBILE LENDING MATTERS On April 20, 2018, the Company
entered into consent orders with the Office of the Comptroller of
the Currency (OCC) and the Consumer Financial Protection
Bureau (CFPB) to resolve, among other things, investigations by
the agencies into the Company’s compliance risk management
program and its past practices involving certain automobile
collateral protection insurance (CPI) policies and certain
mortgage interest rate lock extensions. The consent orders
require remediation to customers and the payment of a total of
$1.0 billion in civil money penalties to the agencies. In July 2017,
the Company announced a plan to remediate customers who
may have been financially harmed due to issues related to
automobile CPI policies purchased through a third-party vendor
on their behalf. Multiple putative class actions alleging, among
other things, unfair and deceptive practices relating to these CPI
policies, were filed against the Company and consolidated into
one multi-district litigation in the United States District Court
for the Central District of California. As previously disclosed, the
Company entered into a settlement to resolve the multi-district
litigation. Shareholders also filed a putative securities fraud class
action against the Company and its executive officers alleging
material misstatements and omissions of CPI-related
information in the Company’s public disclosures. In January 2020,
the court dismissed this action as to all defendants except the
Company and a former executive officer and limited the action to
two alleged misstatements. Subject to court approval, the
parties have entered into an agreement pursuant to which the
Company will pay $300 million to resolve this action. In addition,
the Company was subject to a class action in the United States
District Court for the Central District of California alleging that
customers were entitled to refunds related to the unused portion
of guaranteed automobile protection (GAP) waiver or insurance
agreements between the customer and dealer and, by
assignment, the lender. As previously disclosed, the Company
entered into a settlement to resolve the class action. Allegations
related to the CPI and GAP programs were among the subjects of
a shareholder derivative lawsuit in the United States District
Court for the Northern District of California, which has been
dismissed. In addition, federal and state government agencies,
including the CFPB, have undertaken formal or informal inquiries,
investigations, or examinations regarding these and other issues
related to the origination, servicing, and collection of consumer
auto loans, including related insurance products. On
December 20, 2022, the Company entered into a consent order
with the CFPB to resolve the CFPB’s investigations related to
automobile lending, consumer deposit accounts, and mortgage
lending. The consent order requires, among other things,
remediation to customers and the payment of a $1.7 billion civil
penalty to the CFPB. As previously disclosed, the Company
entered into an agreement to resolve investigations by state
attorneys general.
COMMERCIAL LENDING SHAREHOLDER LITIGATION In October and
November 2020, plaintiffs filed two putative securities fraud
class actions, which were consolidated into one lawsuit pending in
the United States District Court for the Northern District of
California alleging that the Company and certain of its current
and former officers made false and misleading statements or
omissions regarding, among other things, the Company’s
commercial lending underwriting practices, the credit quality of
its commercial credit portfolios, and the value of its commercial
loans, collateralized loan obligations and commercial mortgage-
backed securities. In May 2022, the district court granted
defendants’ motion to dismiss the lawsuit, which was appealed to
the United States Court of Appeals for the Ninth Circuit. In
January 2023, the parties voluntarily dismissed the appeal.
COMPANY 401(K) PLAN MATTERS Federal government agencies,
including the United States Department of Labor (Department
of Labor), have undertaken reviews of certain transactions
associated with the Employee Stock Ownership Plan feature of
the Company’s 401(k) plan, including the manner in which the
401(k) plan purchased certain securities used in connection with
the Company’s contributions to the 401(k) plan. As previously
disclosed, the Company entered into an agreement to resolve
the Department of Labor’s review. On September 26, 2022,
participants in the Company’s 401(k) plan filed a putative class
action in the United States District Court for the District of
Minnesota alleging that the Company violated the Employee
Retirement Income Security Act of 1974 in connection with
certain of these transactions.
CONSENT ORDER DISCLOSURE LITIGATION Wells Fargo
shareholders have brought a putative securities fraud class action
in the United States District Court for the Southern District of
New York alleging that the Company and certain of its current
and former executive officers and directors made false or
misleading statements regarding the Company’s efforts to
comply with the February 2018 consent order with the Federal
Reserve Board and the April 2018 consent orders with the CFPB
and OCC. Allegations related to the Company’s efforts to comply
with these three consent orders are also among the subjects of a
shareholder derivative lawsuit filed in California state court.
CONSUMER DEPOSIT ACCOUNT RELATED REGULATORY
INVESTIGATIONS The CFPB has undertaken an investigation into
whether customers were unduly harmed by the Company’s
historical practices associated with the freezing (and, in many
cases, closing) of consumer deposit accounts after the Company
Wells Fargo & Company 137
Note 13: Legal Actions (continued)
detected suspected fraudulent activity (by third parties or
account holders) that affected those accounts. The CFPB has also
undertaken an investigation into certain of the Company’s past
disclosures to customers regarding the minimum qualifying debit
card usage required for customers to receive a waiver of monthly
service fees on certain consumer deposit accounts. As described
above, on December 20, 2022, the Company entered into a
consent order with the CFPB to resolve the CFPB’s investigations
related to automobile lending, consumer deposit accounts, and
mortgage lending.
HIRING PRACTICES MATTERS Government agencies, including the
United States Department of Justice and the United States
Securities and Exchange Commission, have undertaken formal or
informal inquiries or investigations regarding the Company’s
hiring practices related to diversity. A putative securities fraud
class action has also been filed in the United States District Court
for the Northern District of California alleging that the Company
and certain of its executive officers made false or misleading
statements about the Company’s hiring practices related to
diversity. Allegations related to the Company’s hiring practices
related to diversity are also among the subjects of shareholder
derivative lawsuits filed in the United States District Court for
the Northern District of California.
INTERCHANGE LITIGATION Plaintiffs representing a class of
merchants have filed putative class actions, and individual
merchants have filed individual actions, against Wells Fargo Bank,
N.A., Wells Fargo & Company, Wachovia Bank, N.A., and
Wachovia Corporation regarding the interchange fees associated
with Visa and MasterCard payment card transactions. Visa,
MasterCard, and several other banks and bank holding
companies are also named as defendants in these actions. These
actions have been consolidated in the United States District
Court for the Eastern District of New York. The amended and
consolidated complaint asserts claims against defendants based
on alleged violations of federal and state antitrust laws and seeks
damages as well as injunctive relief. Plaintiff merchants allege
that Visa, MasterCard, and payment card issuing banks unlawfully
colluded to set interchange rates. Plaintiffs also allege that
enforcement of certain Visa and MasterCard rules and alleged
tying and bundling of services offered to merchants are
anticompetitive. Wells Fargo and Wachovia, along with other
defendants and entities, are parties to Loss and Judgment
Sharing Agreements, which provide that they, along with other
entities, will share, based on a formula, in any losses from the
Interchange Litigation. On July 13, 2012, Visa, MasterCard, and
the financial institution defendants, including Wells Fargo, signed
a memorandum of understanding with plaintiff merchants to
resolve the consolidated class action and reached a separate
settlement in principle of the consolidated individual actions. The
settlement payments to be made by all defendants in the
consolidated class and individual actions totaled approximately
$6.6 billion before reductions applicable to certain merchants
opting out of the settlement. The class settlement also provided
for the distribution to class merchants of 10 basis points of
default interchange across all credit rate categories for a period
of eight consecutive months. The district court granted final
approval of the settlement, which was appealed to the United
States Court of Appeals for the Second Circuit by settlement
objector merchants. Other merchants opted out of the
settlement and are pursuing several individual actions. On
June 30, 2016, the Second Circuit vacated the settlement
agreement and reversed and remanded the consolidated action
to the United States District Court for the Eastern District of
New York for further proceedings. On November 23, 2016, prior
class counsel filed a petition to the United States Supreme Court,
seeking review of the reversal of the settlement by the Second
Circuit, and the Supreme Court denied the petition on March 27,
2017. On November 30, 2016, the district court appointed lead
class counsel for a damages class and an equitable relief class.
The parties have entered into a settlement agreement to resolve
the money damages class claims pursuant to which defendants
will pay a total of approximately $6.2 billion, which includes
approximately $5.3 billion of funds remaining from the 2012
settlement and $900 million in additional funding. The
Company’s allocated responsibility for the additional funding is
approximately $94.5 million. The court granted final approval of
the settlement on December 13, 2019, which was appealed to
the United States Court of Appeals for the Second Circuit by
settlement objector merchants. On September 27, 2021, the
district court granted the plaintiffs’ motion for class certification
in the equitable relief case. Several of the opt-out and direct
action litigations have been settled while others remain pending.
MORTGAGE LENDING MATTERS Plaintiffs representing a class of
mortgage borrowers filed separate putative class actions alleging
that Wells Fargo improperly denied mortgage loan modifications
or repayment plans to customers in the foreclosure process due
to the overstatement of foreclosure attorneys’ fees that were
included for purposes of determining whether a customer in the
foreclosure process qualified for a mortgage loan modification or
repayment plan. As previously disclosed, the Company entered
into settlements to resolve the class actions, while the others
were voluntarily dismissed. In addition, federal and state
government agencies, including the CFPB, have undertaken
formal or informal inquiries or investigations regarding these and
other mortgage servicing matters. On September 9, 2021, the
OCC assessed a $250 million civil money penalty against the
Company regarding loss mitigation activities in the Company’s
Home Lending business and insufficient progress in addressing
requirements under the OCC’s April 2018 consent order. In
addition, on September 9, 2021, the Company entered into a
consent order with the OCC requiring the Company to improve
the execution, risk management, and oversight of loss mitigation
activities in its Home Lending business. As described above, on
December 20, 2022, the Company entered into a consent order
with the CFPB to resolve the CFPB’s investigations related to
automobile lending, consumer deposit accounts, and mortgage
lending.
NOMURA/NATIXIS MORTGAGE-RELATED LITIGATION In August
2014 and August 2015, Nomura Credit & Capital Inc. (Nomura)
and Natixis Real Estate Holdings, LLC (Natixis) filed a total of
seven third-party complaints against Wells Fargo Bank, N.A., in
New York state court. In the underlying first-party actions,
Nomura and Natixis have been sued for alleged breaches of
representations and warranties made in connection with
residential mortgage-backed securities sponsored by them. In
the third-party actions, Nomura and Natixis allege that
Wells Fargo, as master servicer, primary servicer or securities
administrator, failed to notify Nomura and Natixis of their own
breaches, failed to properly oversee the primary servicers, and
failed to adhere to accepted servicing practices. Natixis
additionally alleges that Wells Fargo failed to perform default
oversight duties. In March 2022, Wells Fargo entered into an
agreement to settle the six actions filed by Nomura, and the
actions have been voluntarily dismissed. In the remaining action
filed by Natixis, Wells Fargo has asserted counterclaims alleging
that Natixis failed to provide Wells Fargo notice of its
Wells Fargo & Company 138
representation and warranty breaches. In January 2023, Natixis
and Wells Fargo reached an agreement in principle to settle their
respective claims.
OFAC RELATED INVESTIGATION The Company has self-identified
an issue whereby certain foreign banks utilized a Wells Fargo
software-based solution to conduct import/export trade-related
financing transactions with countries and entities prohibited by
the Office of Foreign Assets Control (OFAC) of the United States
Department of the Treasury. We do not believe any funds related
to these transactions flowed through accounts at Wells Fargo as
a result of the aforementioned conduct. The Company has made
voluntary self-disclosures to OFAC and has been cooperating
with investigations or inquiries arising out of this matter by
federal government agencies. The Company is in resolution
discussions with certain of these agencies, although there can be
no assurance as to the outcome of these discussions.
RECORD-KEEPING INVESTIGATIONS The United States Securities
and Exchange Commission and the United States Commodity
Futures Trading Commission have undertaken investigations
regarding the Company’s compliance with records retention
requirements relating to business communications sent over
unapproved electronic messaging channels.
RETAIL SALES PRACTICES MATTERS Federal and state government
agencies, including the United States Department of Justice
(Department of Justice) and the United States Securities and
Exchange Commission (SEC), have undertaken formal or informal
inquiries or investigations arising out of certain retail sales
practices of the Company that were the subject of settlements
with the CFPB, the OCC, and the Office of the Los Angeles City
Attorney announced by the Company on September 8, 2016. On
February 21, 2020, the Company entered into an agreement with
the Department of Justice to resolve the Department of Justice’s
criminal investigation into the Company’s retail sales practices as
well as a separate agreement to resolve the Department of
Justice’s civil investigation. As part of the Department of Justice
criminal settlement, no charges will be filed against the Company
provided the Company abides by all the terms of the agreement.
The Department of Justice criminal settlement also includes the
Company’s agreement that the facts set forth in the settlement
document constitute sufficient facts for the finding of criminal
violations of statutes regarding bank records and personal
information. On February 21, 2020, the Company also entered
into an order to resolve the SEC’s investigation arising out of the
Company’s retail sales practices. The SEC order contains a
finding, to which the Company consented, that the facts set
forth include violations of Section 10(b) of the Securities
Exchange Act of 1934 and Rule 10b-5 thereunder. As part of the
resolution of the Department of Justice and SEC investigations,
the Company made payments totaling $3.0 billion. The Company
has also entered into agreements to resolve other government
agency investigations, including investigations by the state
attorneys general. In addition, a number of lawsuits were filed by
non-governmental parties seeking damages or other remedies
related to these retail sales practices. As previously disclosed, the
Company entered into various settlements to resolve these
lawsuits.
RMBS TRUSTEE LITIGATION In December 2014, Phoenix Light SF
Limited (Phoenix Light) and certain related entities filed a
complaint in the United States District Court for the Southern
District of New York alleging claims against Wells Fargo Bank,
N.A., in its capacity as trustee for a number of residential
mortgage-backed securities (RMBS) trusts. Complaints raising
similar allegations have been filed by Commerzbank AG in the
Southern District of New York and by IKB International and IKB
Deutsche Industriebank in New York state court. In each case, the
plaintiffs allege that Wells Fargo Bank, N.A., as trustee, caused
losses to investors, and plaintiffs assert causes of action based
upon, among other things, the trustee’s alleged failure to notify
and enforce repurchase obligations of mortgage loan sellers for
purported breaches of representations and warranties, notify
investors of alleged events of default, and abide by appropriate
standards of care following alleged events of default. In
July 2022, the district court dismissed Phoenix Light’s claims and
certain of the claims asserted by Commerzbank AG, and
subsequently entered judgment in each case in favor of Wells
Fargo Bank, N.A. In August 2022, Phoenix Light and
Commerzbank AG appealed the district court’s decision to the
United States Court of Appeals for the Second Circuit. The
Company previously settled two class actions filed by
institutional investors and an action filed by the National Credit
Union Administration with similar allegations. In addition, Park
Royal I LLC and Park Royal II LLC have filed substantially similar
lawsuits in New York state court alleging Wells Fargo Bank, N.A.,
as trustee, failed to take appropriate actions upon learning of
defective mortgage loan documentation.
SEMINOLE TRIBE TRUSTEE LITIGATION The Seminole Tribe of
Florida filed a complaint in Florida state court alleging that
Wells Fargo, as trustee, charged excess fees in connection with
the administration of a minor’s trust and failed to invest the
assets of the trust prudently. The complaint was later amended
to include three individual current and former beneficiaries as
plaintiffs and to remove the Tribe as a party to the case.
Wells Fargo filed a petition to remove the case to federal court,
but the case was remanded back to state court.
OUTLOOK As described above, the Company establishes accruals
for legal actions when potential losses associated with the
actions become probable and the costs can be reasonably
estimated. The high end of the range of reasonably possible
losses in excess of the Company’s accrual for probable and
estimable losses was approximately $1.4 billion as of
December 31, 2022. The outcomes of legal actions are
unpredictable and subject to significant uncertainties, and it is
inherently difficult to determine whether any loss is probable or
even possible. It is also inherently difficult to estimate the
amount of any loss and there may be matters for which a loss is
probable or reasonably possible but not currently estimable.
Accordingly, actual losses may be in excess of the established
accrual or the range of reasonably possible loss. Based on
information currently available, advice of counsel, available
insurance coverage, and established reserves, Wells Fargo
believes that the eventual outcome of the actions against Wells
Fargo and/or its subsidiaries will not, individually or in the
aggregate, have a material adverse effect on Wells Fargo’s
consolidated financial condition. However, it is possible that the
ultimate resolution of a matter, if unfavorable, may be material
to Wells Fargo’s results of operations for any particular period.
Wells Fargo & Company 139

Note 14: Derivatives
We use derivatives to manage exposure to market risk, including
interest rate risk, credit risk and foreign currency risk, and to
assist customers with their risk management objectives. We
designate certain derivatives as hedging instruments in
qualifying hedge accounting relationships (fair value or cash flow
hedges). Our remaining derivatives consist of economic hedges
that do not qualify for hedge accounting and derivatives held for
customer accommodation trading or other purposes.
Risk Management Derivatives
Our asset/liability management approach to interest rate,
foreign currency and certain other risks includes the use of
derivatives, which are typically designated as fair value or cash
flow hedges, or economic hedges. We use derivatives to help
minimize significant, unplanned fluctuations in earnings, fair
values of assets and liabilities, and cash flows caused by interest
rate, foreign currency and other market risk volatility. This
approach involves modifying the repricing characteristics of
certain assets and liabilities so that changes in interest rates,
foreign currency and other exposures, which may cause the
hedged assets and liabilities to gain or lose fair value, do not have
a significant adverse effect on the net interest margin, cash flows
and earnings. In a fair value or economic hedge, the effect of
change in fair value will generally be offset by the unrealized gain
or loss on the derivatives linked to the hedged assets and
liabilities. In a cash flow hedge, where we manage the variability
of cash payments due to interest rate or foreign currency
fluctuations by the effective use of derivatives linked to hedged
assets and liabilities, the hedged asset or liability is not adjusted
and the unrealized gain or loss on the derivative is recorded in
other comprehensive income.
Customer Accommodation Trading
We also use various derivatives, including interest rate,
commodity, equity, credit and foreign exchange contracts,
as an accommodation to our customers as part of our trading
businesses. These derivative transactions, which involve
engaging in market-making activities or acting as an
intermediary, are conducted in an effort to help customers
manage their market risks. We usually offset our exposure from
such derivatives by entering into other financial contracts, such
as separate derivative or security transactions. These customer
accommodations and any offsetting derivatives are treated as
customer accommodation trading and other derivatives in our
disclosures. Additionally, embedded derivatives that are required
to be accounted for separately from their host contracts are
included in the customer accommodation trading and other
derivatives disclosures, as applicable.
Wells Fargo & Company 140
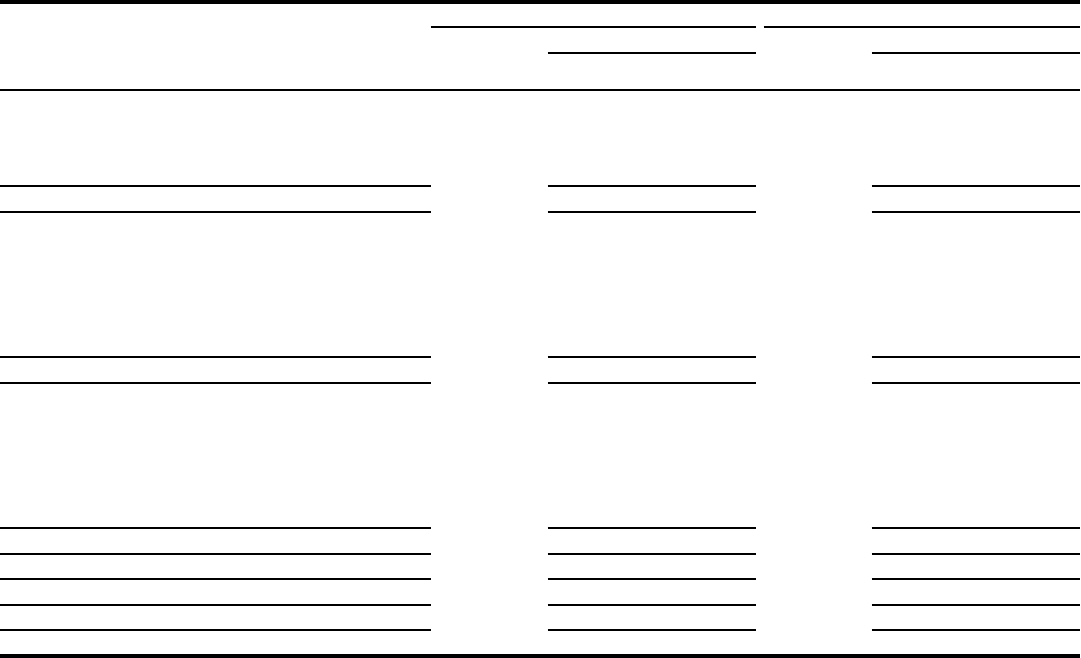
Table 14.1 presents the total notional or contractual
amounts and fair values for our derivatives. Derivative
transactions can be measured in terms of the notional amount,
but this amount is not recorded on our consolidated balance
sheet and is not, when viewed in isolation, a meaningful measur e
of the risk profile of the instruments. The notional amount is
generally not exchanged, but is used only as the basis on whic h
derivative cash flows are determined.
Table 14.1: Notional or Contractual Amounts and Fair Values of Derivatives
December 31, 2022 December 31, 2021
(in millions)
Notional
or contractu al
amount
Fair valu e
Notional
or contractual
amount
Fair value
Derivative
assets
Derivative
liabilities
Derivative
assets
Derivative
liabilities
Derivatives designated as hedging instru ments
Interest rate contracts $ 263,876 670 579 153,993 2,212 327
Commodity contracts 1,681 9 25 1,739 26 3
Foreign exchange contracts 15,544 161 1,015 24,949 281 669
Total derivatives designated as qualifying hedging instruments 840 1,619 2,519 999
Derivatives not designated as hedging instru ments
Economic hedges:
Interest rate contracts 65,727 410 253 142,234 40 41
Equity contracts (1) 3,884 — 260 26,263 1,493 1,194
Foreign exchange contracts 38,139 490 968 28,192 395 88
Credit contracts 290 14 — 290 7 —
Subtotal 914 1,481 1,935 1,323
Customer accommodation trading and other derivatives:
Interest rate contracts 10,156,300 40,006 42,641 7,976,534 20,286 17,435
Commodity contracts 96,001 5,991 3,420 74,903 5,939 2,414
Equity contracts (1) 390,427 9,573 8,012 321,863 16,278 17,827
Foreign exchange contracts 1,475,224 21,562 24,703 560,049 5,912 5,915
Credit contracts 45,359 52 36 38,318 39 43
Subtotal 77,184 78,812 48,454 43,634
Total derivatives not designated as hedging instruments 78,098 80,293 50,389 44,957
Total derivatives before netting 78,938 81,912 52,908 45,956
Netting (56,164) (61,827) (31,430) (36,532)
Total $ 22,774 20,085 21,478 9,424
(1) In first quarter 2022, we prospectively reclassified certain equity securities and related economic hedge derivatives from “not held for trading activities” to “held for trading activities” to better
reflect the business activity of those financial instruments. For additional information on Trading Activities, see Note 1 (Summary of Significant Accounting Policies).
Balance Sheet Offsetting
We execute substantially all of our derivative transactions under
master netting arrangements. Where legally enforceable, these
master netting arrangements give the ability, in the event of
default by the counterparty, to liquidate securities held as
collateral and to offset receivables and payables with the same
counterparty. We reflect all derivative balances and related cash
collateral subject to enforceable master netting arrangements on
a net basis on our consolidated balance sheet. We do not net
non-cash collateral that we receive or pledge against derivative
balances on our consolidated balance sheet.
For disclosure purposes, we present “Total Derivatives, net”
which represents the aggregate of our net exposure to each
counterparty after considering the balance sheet netting
adjustments and any non-cash collateral. We manage derivative
exposure by monitoring the credit risk associated with each
counterparty using counterparty-specific credit risk limits, using
master netting arrangements and obtaining collateral.
Table 14.2 provides information on the fair values of
derivative assets and liabilities subject to enforceable master
netting arrangements, the balance sheet netting adjustments
and the resulting net fair value amount recorded on our
consolidated balance sheet, as well as the non-cash collateral
associated with such arrangements. In addition to the netting
amounts included in the table, we also have balance sheet netting
related to resale and repurchase agreements that are disclosed
within Note 18 (Pledged Assets and Collateral).
Wells Fargo & Company 141
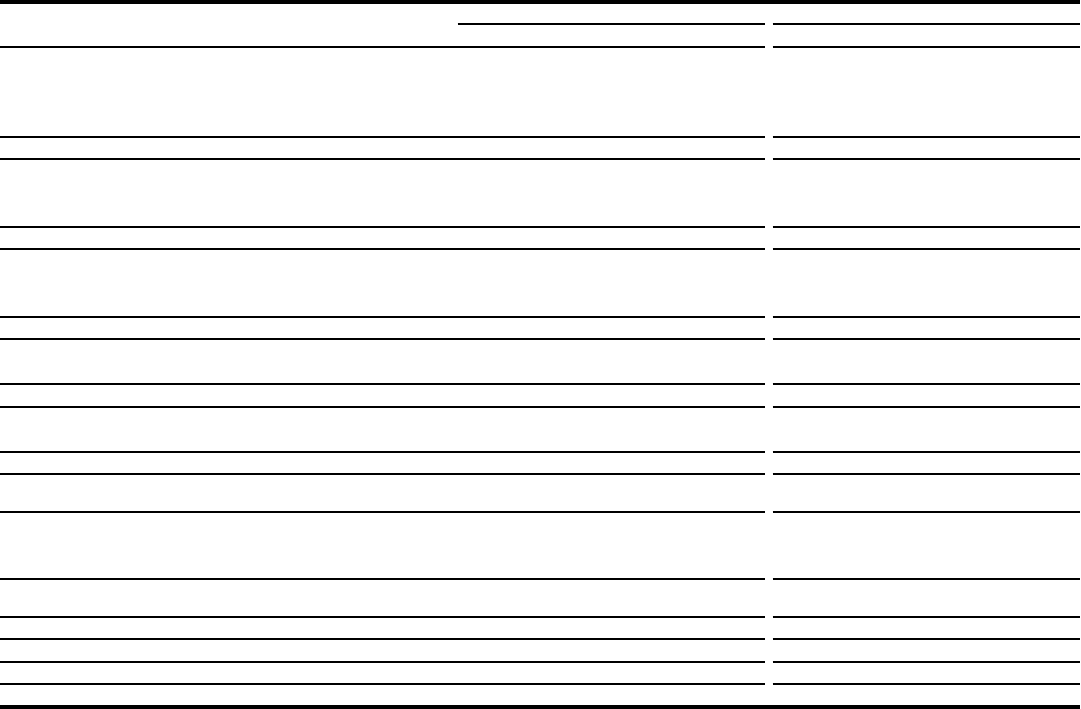
Table 14.2: Fair Values of Derivative Assets and Liabilities
December 31, 2022 December 31, 2021
(in millions) Derivative Assets Derivative Liabilities Derivative Assets Derivative Liabilities
Interest rate contracts
Over-the-counter (OTC) $ 37,000 37,598 20,067 16,654
OTC cleared 649 845 168 192
Exchange traded 262 193 52 28
Total interest rate contracts 37,911 38,636 20,287 16,874
Commodity contracts
OTC 4,833 2,010 5,040 1,249
Exchange traded 876 1,134 557 1,047
Total commodity contracts 5,709 3,144 5,597 2,296
Equity contracts
OTC 4,269 4,475 6,132 9,730
Exchange traded 3,742 2,409 7,493 6,086
Total equity contracts 8,011 6,884 13,625 15,816
Foreign exchange contracts
OTC 21,537 26,127 6,335 6,221
Total foreign exchange contracts 21,537 26,127 6,335 6,221
Credit contracts
OTC 39 22 32 31
Total credit contracts 39 22 32 31
Total derivatives subject to enforceable master netting arrangements,
gross 73,207 74,813 45,876 41,238
Less: Gross amounts offset
Counterparty netting (1) (49,115) (49,073) (27,172) (27,046)
Cash collateral netting (7,049) (12,754) (4,258) (9,486)
Total derivatives subject to enforceable master netting arrangements,
net 17,043 12,986 14,446 4,706
Derivatives not subject to enforceable master netting arrangements 5,731 7,099 7,032 4,718
Total derivatives recognized in consolidated balance sheet, net 22,774 20,085 21,478 9,424
Non-cash collateral (3,517) (582) (1,432) (412)
Total Derivatives, net $ 19,257 19,503 20,046 9,012
Note 14: Derivatives (continued)
(1) Represents amounts with counterparties subject to enforceable master netting arrangements that have been offset in our consolidated balance sheet, including portfolio level counterparty valuation
adjustments related to customer accommodation and other trading derivatives. Counterparty valuation adjustments related to derivative assets were $372 million and $284 million and debit
valuation adjustments related to derivative liabilities were $331 million and $158 million as of December 31, 2022 and 2021, respectively, and were primarily related to interest rate contracts.
Fair Value and Cash Flow Hedges
For fair value hedges, we use interest rate swaps to convert
certain of our fixed-rate long-term debt and time certificates of
deposit to floating rates to hedge our exposure to interest rate
risk. We also enter into cross-currency swaps, cross-currency
interest rate swaps and forward contracts to hedge our exposure
to foreign currency risk and interest rate risk associated with the
issuance of non-U.S. dollar denominated long-term debt. We also
enter into futures contracts, forward contracts, and swap
contracts to hedge our exposure to the price risk of physical
commodities included in Other Assets. In addition, we use
interest rate swaps, cross-currency swaps, cross-currency
interest rate swaps and forward contracts to hedge against
changes in fair value of certain investments in available-for-sale
debt securities due to changes in interest rates, foreign currency
rates, or both. For certain fair value hedges of foreign currency
risk, changes in fair value of cross-currency swaps attributable to
changes in cross-currency basis spreads are excluded from the
assessment of hedge effectiveness and recorded in other
comprehensive income (OCI). See Note 24 (Other
Comprehensive Income) for the amounts recognized in other
comprehensive income.
For cash flow hedges, we use interest rate swaps to hedge
the variability in interest payments received on certain interest-
earning deposits with banks and certain floating-rate commercial
loans, and interest paid on certain floating-rate debt due to
changes in the contractually specified interest rate. We also use
cross-currency swaps to hedge variability in interest payments
on fixed-rate foreign currency-denominated long-term debt due
to changes in foreign exchange rates.
We estimate $695 million pre-tax of deferred net losses
related to cash flow hedges in OCI at December 31, 2022, will be
reclassified into net interest income during the next twelve
months. For cash flow hedges as of December 31, 2022, we are
hedging our interest rate and foreign currency exposure to the
variability of future cash flows for all forecasted transactions for
a maximum of 10 years. For additional information on our
accounting hedges, see Note 1 (Summary of Significant
Accounting Policies).
Wells Fargo & Company 142
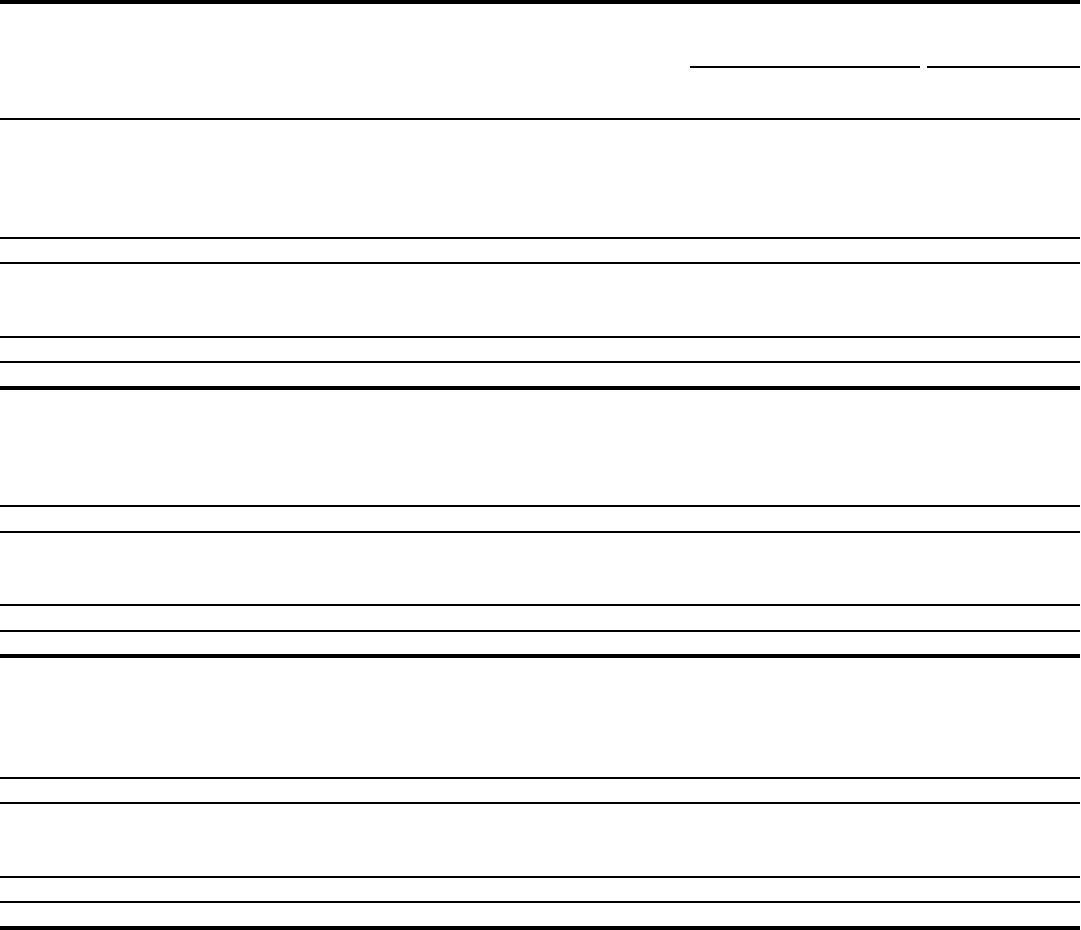
Table 14.3 and Table 14.4 show the net gains (losses) related
to derivatives in cash flow and fair value hedging relationships,
respectively.
Table 14.3: Gains (Losses) Recognized on Cash Flow Hedging Relationships
Net interest income
Total
recorded
in net
income
Total
recorded
in OCI
(in millions) Loans
Other
interest
income
Long-
term debt
Derivative
gains
(losses)
Derivative
gains
(losses)
Year Ended December 31, 2022
Total amounts presented in the consolidated statement of income and other comprehensive income $ 37,715 3,308 (5,505) N/A (1,448)
Interest rate contracts:
Realized gains (losses) (pre-tax) reclassified from OCI into net income (20) 24 — 4 (4)
Net unrealized gains (losses) (pre-tax) recognized in OCI N/A N/A N/A N/A (1,524)
Total gains (losses) (pre-tax) on interest rate contracts (20) 24 — 4 (1,528)
Foreign exchange contracts:
Realized gains (losses) (pre-tax) reclassified from OCI into net income — — (10) (10) 10
Net unrealized gains (losses) (pre-tax) recognized in OCI N/A N/A N/A N/A (17)
Total gains (losses) (pre-tax) on foreign exchange contracts — — (10) (10) (7)
Total gains (losses) (pre-tax) recognized on cash flow hedges $ (20) 24 (10) (6) (1,535)
Year Ended December 31, 2021
Total amounts presented in the consolidated statement of income and other comprehensive income $ 28,634 334 (3,173) N/A 212
Interest rate contracts:
Realized gains (losses) (pre-tax) reclassified from OCI into net income (137) — — (137) 137
Net unrealized gains (losses) (pre-tax) recognized in OCI N/A N/A N/A N/A 7
Total gains (losses) (pre-tax) on interest rate contracts (137) — — (137) 144
Foreign exchange contracts:
Realized gains (losses) (pre-tax) reclassified from OCI into net income — — (6) (6) 6
Net unrealized gains (losses) (pre-tax) recognized in OCI N/A N/A N/A N/A (19)
Total gains (losses) (pre-tax) on foreign exchange contracts — — (6) (6) (13)
Total gains (losses) (pre-tax) recognized on cash flow hedges $ (137) — (6) (143) 131
Year ended December 31, 2020
Total amounts presented in the consolidated statement of income and other comprehensive income $ 34,230 954 (4,471) N/A
198
Interest rate contracts:
Realized
gains (losses) (pre-tax) reclassified from OCI into net income (215) — 4 (211) 211
Net unrealized gains (losses) (pre-tax) recognized in OCI N/A N/A N/A N/A —
Total gains (losses) (pre-tax) on interest rate contracts (215) — 4 (211) 211
Foreign exchange contracts:
Realized gains (losses) (pre-tax) reclassified from OCI into net income — — (8) (8) 8
Net unrealized gains (losses) (pre-tax) recognized in OCI N/A N/A N/A N/A 10
Total gains (losses) (pre-tax) on foreign exchange contracts — — (8) (8) 18
Total gains (losses) (pre-tax) recognized on cash flow hedges $
(215) — (4) (219) 229
Wells Fargo & Company 143
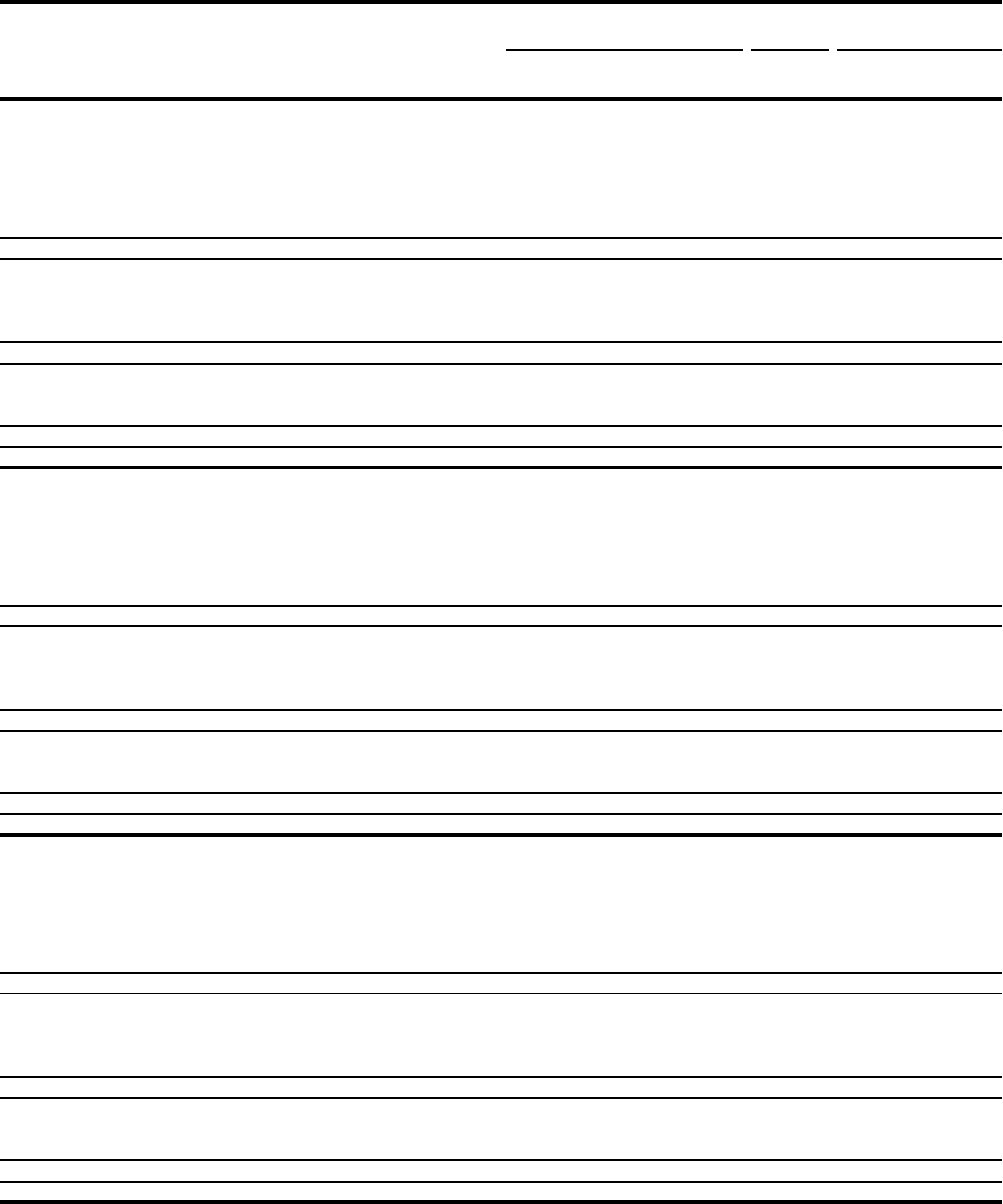
Note 14: Derivatives (continued)
Table 14.4: Gains (Losses) Recognized on Fair Value Hedging Relationships
Net interest income
Noninterest
income
Total
recorded in
net income
Total
recorded in
OCI
(in millions)
Debt
securities Deposits
Long-term
debt Other
Derivative
gains
(losses)
Derivative
gains
(losses)
Year Ended December 31, 2022
Total amounts presented in the consolidated statement of income and other
comprehensive income $ 11,781 (2,349) (5,505) 2,238 N/A (1,448)
Interest contracts
Amounts related to cash flows on derivatives 143 65 313 — 521 N/A
Recognized on derivatives 3,616 (345) (18,056) — (14,785) —
Recognized on hedged items (3,576) 350 17,919 — 14,693 N/A
Total gains (losses) (pre-tax) on interest rate contracts 183 70 176 — 429 —
Foreign exchange contracts
Amounts related to cash flows on derivatives — — (189) — (189) N/A
Recognized on derivatives — — (1,120) (1,021) (2,141) 87
Recognized on hedged items — — 1,097 1,005 2,102 N/A
Total gains (losses) (pre-tax) on foreign exchange contracts — — (212) (16) (228) 87
Commodity contracts
Recognized on derivatives — — — 57 57 —
Recognized on hedged items — — — (43) (43) N/A
Total gains (losses) (pre-tax) on commodity contracts — — — 14 14 —
Total gains (losses) (pre-tax) recognized on fair value hedges $ 183 70 (36) (2) 215 87
Year Ended December 31, 2021
Total amounts presented in the consolidated statement of income and other
comprehensive income $ 9,253 (388) (3,173) 3,734 N/A 212
Interest contracts
Amounts related to cash flows on derivatives (253) 289 2,136 — 2,172 N/A
Recognized on derivatives 1,129 (336) (6,351) — (5,558) —
Recognized on hedged items (1,117) 333 6,288 — 5,504 N/A
Total gains (losses) (pre-tax) on interest rate contracts (241) 286 2,073 — 2,118 —
Foreign exchange contracts
Amounts related to cash flows on derivatives 57 — 10 — 67 N/A
Recognized on derivatives 4 — (516) (99) (611)
81
Recognized on hedged items (3) — 438 82 517 N/A
Total gains (losses) (pre-tax) on foreign exchange contracts 58 — (68) (17) (27) 81
Commodity contracts
Recognized on derivatives
—
— —
113 113
—
Recognized on hedged items
—
—
— (124)
(124) N/A
Total gains (losses) (pre-tax) on commodity contracts — — — (11) (11) —
Total gains (losses) (pre-tax) recognized on fair value hedges $
(183) 286 2,005 (28) 2,080 81
Year
ended
December
31,
2020
Total amounts presented in the consolidated statement of income and other
comprehensive income $
11,234
(2,804) (4,471) 3,847 N/A 198
Interest contracts
Amounts related to cash flows on derivatives (338) 503 1,704 — 1,869 N/A
Recognized on derivatives (1,261) 161 6,691 — 5,591 —
Recognized on hedged items 1,317 (151) (6,543) — (5,377) N/A
Total gains (losses) (pre-tax) on interest rate contracts (282) 513 1,852 — 2,083 —
Foreign exchange contracts
Amounts related to cash flows on derivatives
52 —
(139)
—
(87) N/A
Recognized on derivatives
(1) —
261
1,591
1,851
(31)
Recognized on hedged items
2 —
(201)
(1,575)
(1,774) N/A
Total gains (losses) (pre-tax) on foreign exchange contracts
53 —
(79)
16
(10)
(31)
Commodity contracts
Recognized on derivatives
— —
—
(11)
(11)
—
Recognized on hedged items
—
—
—
27
27 N/A
Total gains (losses) (pre-tax) on commodity contracts
—
—
—
16
16
—
Total gains (losses) (pre-tax) recognized on fair value hedges $
(229)
513
1,773
32
2,089
(31)
Wells Fargo & Company 144
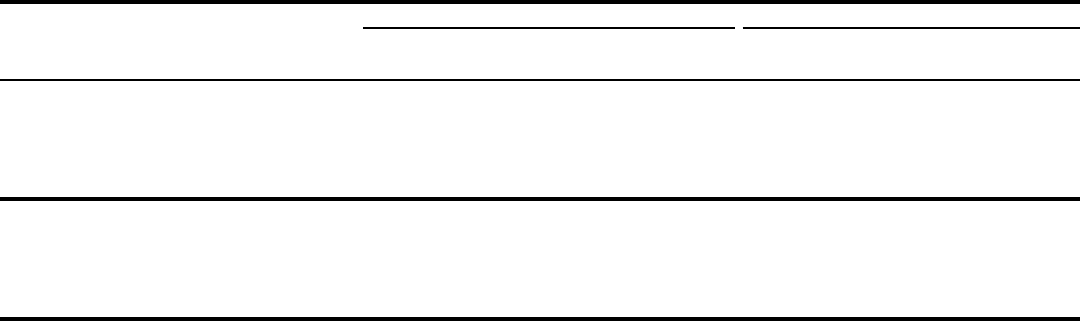
Table 14.5 shows the carrying amount and associated
cumulative basis adjustment related to the application of hedge
accounting that is included in the carrying amount of hedged
assets and liabilities in fair value hedging relationships.
Table 14.5: Hedged Items in Fair Value Hedging Relationships
Hedged items currently designated Hedged items no longer designated
(in millions)
Carrying amount of assets/
(liabilities) (1)(2)
Hedge accounting
basis adjustment
assets/(liabilities) (3)
Carrying amount of assets/
(liabilities) (2)
Hedge accounting basis
adjustment
assets/(liabilities)
December 31, 2022
Available-for-sale debt securities (4) $ 39,423 (3,859) 16,100 722
Other assets 1,663 38 — —
Deposits (41,687) 205 (10) —
Long-term debt (130,997) 13,862 (5) —
December 31, 2021
Available-for-sale debt securities (4) $ 24,144 (559) 17,962 965
Other assets 1,156 (58) — —
Deposits (10,187) (144) — —
Long-term debt (138,801) (5,192) — —
(1) Does not include t he ca rrying amount of h edged items wh ere only foreign cu rrency risk is t he d esignated hedged risk. The ca rrying amount excluded for debt securities is $739 m illion and for long-
term debt is $0 m illion as of December 31, 2022, and $873 m illion for debt securities a nd $(2.7) b illion for long-term debt as of December 31, 2021.
(2) Represents the full carrying amount of the hedged asset or liability item as of the balance sheet date, except for circumstances in which only a portion of the asset or liability was designated as the
hedged item in which case only the portion designated is presented.
(3) The b alance inclu des $39 m illion and $334 m illion of d ebt securities a nd long-term debt cumulative b asis a djustments a s of December 31, 2022, respectively, and $136 m illion and $188 m illion of
debt securities a nd long-term debt cumulative b asis a djustments a s of December 31, 2021, respectively, on t erminated hedges wh ereby the h edged items h ave su bsequently been r e-designated
into exist ing hedges.
(4) Carrying amount represents the amortized cost.
Derivatives Not Designated as Hedging Instruments
Derivatives not designated as hedging instruments include
economic hedges and derivatives entered into for customer
accommodation trading purposes.
We use economic hedge derivatives to manage our exposure
to interest rate risk, equity price risk, foreign currency risk, and
credit risk. We also use economic hedge derivatives to mitigate
the periodic earnings volatility caused by mismatches between
the changes in fair value of the hedged item and hedging
instrument recognized on our fair value accounting hedges.
Changes in the fair values of derivatives used to economically
hedge the deferred compensation plan are reported in personnel
expense.
Mortgage Banking Activities
We use economic hedge derivatives in our mortgage banking
business to hedge the risk of changes in the fair value of
(1) certain residential MSRs measured at fair value, (2) residentia l
mortgage LHFS, (3) derivative loan commitments, and (4) other
interests held. The types of derivatives used include swaps,
swaptions, constant maturity mortgages, forwards, Eurodollar
and Treasury futures and options contracts. Loan commitments
for mortgage loans that we intend to sell are considered
derivatives. Residential MSRs, derivative loan commitments,
certain residential mortgage LHFS, and our economic hedge
derivatives are carried at fair value with changes in fair valu e
included in mortgage banking noninterest income. See Note 6
(Mortgage Banking Activities ) for additional information on this
economic hedging activity and mortgage banking income.
Customer Accommodation Trading and Other
For customer accommodation trading purposes, we use swaps,
futures, forwards, spots and options to assist our customers in
managing their own risks, including interest rate, commodity,
equity, foreign exchange, and credit contracts. These derivatives
are not linked to specific assets and liabilities on our consolidated
balance sheet or to forecasted transactions in an accounting
hedge relationship and, therefore, do not qualify for hedge
accounting. We also enter into derivatives for risk management
that do not otherwise qualify for hedge accounting. They are
carried at fair value with changes in fair value recorded in
noninterest income.
Customer accommodation trading and other derivatives also
include embedded derivatives that are required to be accounted
for separately from their host contract. We periodically issue
hybrid long-term notes and certificates of deposit (CDs) where
the performance of the hybrid instrument note is linked to an
equity, commodity or currency index, or basket of such indices.
These notes contain explicit terms that affect some or all of the
cash flows or the value of the note in a manner similar to a
derivative instrument and therefore are considered to contain an
“embedded” derivative instrument. The indices on which the
performance of the hybrid instrument is calculated are not
clearly and closely related to the host debt instrument. The
“embedded” derivative is separated from the host contract and
accounted for as a derivative. Additionally, we may invest in
hybrid instruments that contain embedded derivatives, such as
credit derivatives, that are not clearly and closely related to the
host contract. In such instances, we either elect fair value option
for the hybrid instrument or separate the embedded derivative
from the host contract and account for the host contract and
derivative separately.
Wells Fargo & Company 145
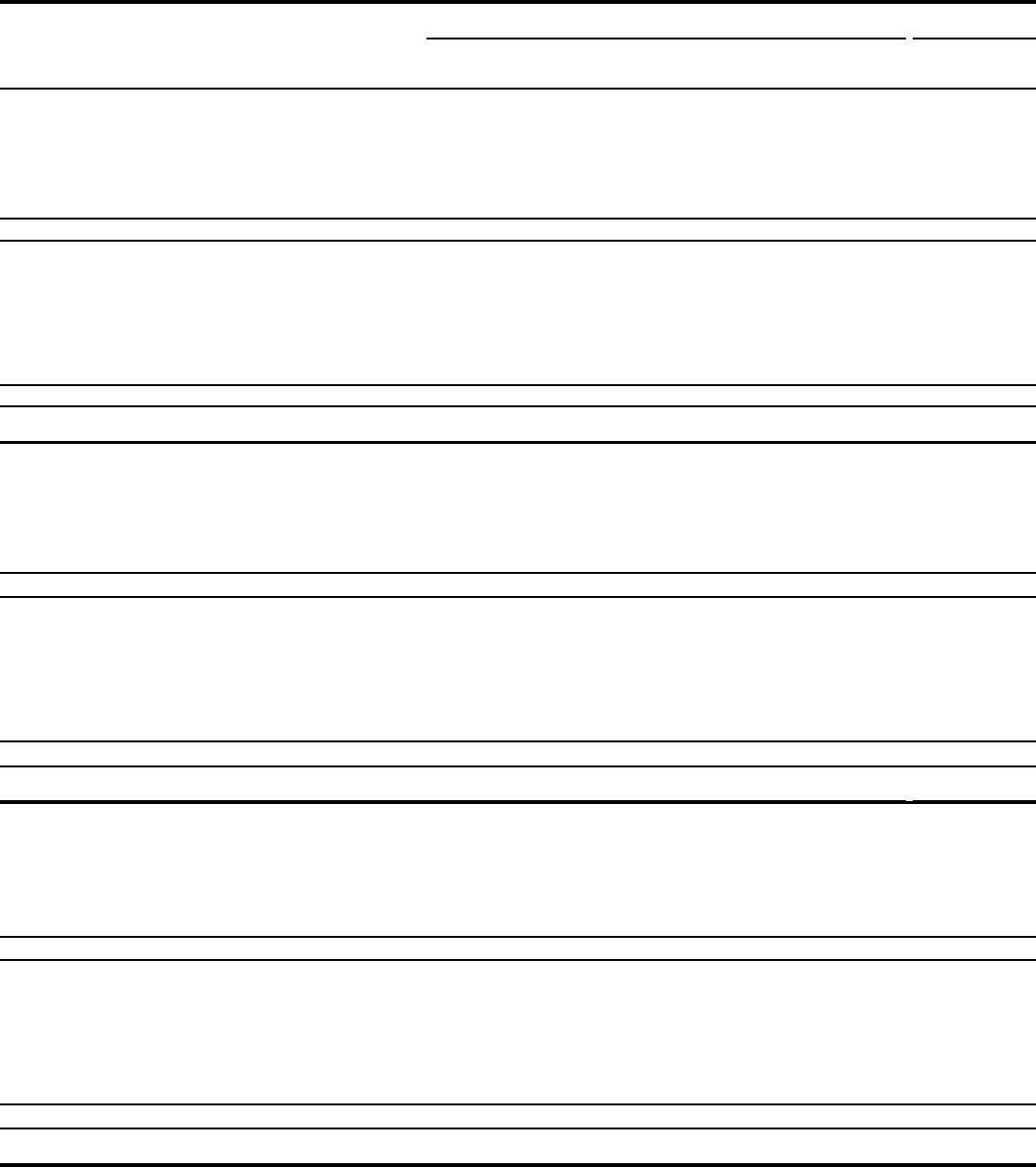
Note 14: Derivatives (continued)
Table 14.6 shows the net gains (losses), recognized by
income statement lines, related to derivatives not designated a s
hedging instruments.
Table 14.6: Gains (Losses) on Derivatives Not Designated as Hedging Instruments
Noninterest income
Noninterest
expense
(in millions)
Mortgage
banking
Net gains from
trading and
securities Other Total Personnel expense
Year Ended December 31, 2022
Net gains (losses) recognized on economic hedges derivatives:
Interest contracts (1) $ (1,040) — (83) (1,123) —
Equity contracts (2) — — 10 10 877
Foreign exchange contracts — — 547 547 —
Credit contracts — — 6 6 —
Subtotal (1,040) — 480 (560) 877
Net gains (losses) recognized on customer accommodation trading
and other derivatives:
Interest contracts (1,079) 9,742 — 8,663 —
Commodity contracts — 390 — 390 —
Equity contracts (2) — 4,652 (286) 4,366 —
Foreign exchange contracts — 1,177 — 1,177 —
Credit contracts — (27) — (27) —
Subtotal (1,079) 15,934 (286) 14,569 —
Net gains (losses) recognized related to derivatives not designated
as hedging instruments $ (2,119) 15,934 194 14,009 877
Year Ended December 31, 2021
Net gains (losses) recognized on economic hedges derivatives:
Interest contracts (1) $ (51) — (11) (62) —
Equity contracts — 495 (1) 494 (611)
Foreign exchange contracts — — 335 335 —
Credit contracts — — (12) (12) —
Subtotal (51) 495 311 755 (611)
Net gains (losses) recognized on customer accommodation trading
and other derivatives:
Interest contracts 62 1,217 — 1,279 —
Commodity contracts — 133 — 133 —
Equity contracts — (4,549) (444) (4,993) —
Foreign exchange contracts — 827 — 827 —
Credit contracts — (93) — (93) —
Subtotal 62 (2,465) (444) (2,847) —
Net gains (losses) recognized related to derivatives not designated as
hedging instruments $ 11 (1,970) (133) (2,092) (611)
Year ended December 31, 2020
Net gains (losses) recognized on economic hedges derivatives:
Interest contracts (1) $ 2,787 — (93) 2,694 —
Equity contracts — (1,167) (25) (1,192) (778)
Foreign exchange contracts — — (455) (455) —
Credit contracts — — 14 14 —
Subtotal 2,787 (1,167) (559) 1,061 (778)
Net gains (losses) recognized on customer accommodation trading
and other derivatives:
Interest contracts 1,964 (1,021) — 943 —
Commodity contracts — 446 — 446 —
Equity contracts — (436) (334) (770) —
Foreign exchange contracts — 89 — 89 —
Credit contracts — (1) — (1) —
Subtotal 1,964 (923) (334) 707 —
Net gains (losses) recognized related to derivatives not designated as
hedging instruments $ 4,751 (2,090) (893) 1,768 (778)
(1) Mortgage banking amounts for the years ended 2022, 2021 and 2020 are comprised of gains (losses) of $(3.5) billion, $(1.2) billion and $4.6 billion, respectively, related to derivatives used as
economic hedges of MSRs measured at fair value offset by gains (losses) of $2.5 billion, $1.2 billion and $(1.8) billion, respectively, related to derivatives used as economic hedges of mortgage loans
held for sale and derivative loan commitments.
(2) In first quarter 2022, we prospectively reclassified certain equity securities and related economic hedge derivatives from “not held for trading activities” to “held for trading activities” to better
reflect the business activity of those financial instruments. For additional information on Trading Activities, see Note 1 (Summary of Significant Accounting Policies).
Wells Fargo & Company 146
Credit Derivatives
Credit derivative contracts are arrangements whose value is
derived from the transfer of credit risk of a reference asset or
entity from one party (the purchaser of credit protection) to
another party (the seller of credit protection). We generally use
credit derivatives to assist customers with their risk
management objectives by purchasing and selling credit
protection on corporate debt obligations through the use of
credit default swaps or through risk participation swaps to help
manage counterparty exposure. We would be required to
perform under the credit derivatives we sold in the event of
default by the referenced obligors. Events of default include
events such as bankruptcy, capital restructuring or lack of
principal and/or interest payment.
Table 14.7 provides details of sold credit derivatives.
Table 14.7: Sold Credit Derivatives
Notional amount
(in millions) Protection sold
Protection sold –
non-investment
grade
December 31, 2022
Credit default swaps $ 12,733 1,860
Risk participation swaps 6,728 6,518
Total credit derivatives $ 19,461 8,378
December 31, 2021
Credit default swaps $ 8,033 1,982
Risk participation swaps 6,756 6,012
Total credit derivatives $ 14,789 7,994
Protection sold represents the estimated maximum
exposure to loss that would be incurred if, upon an event of
default, the value of our interests and any associated collateral
declined to zero, and does not take into consideration any of
recovery value from the referenced obligation or offset from
collateral held or any economic hedges.
The amounts under non-investment grade represent the
notional amounts of those credit derivatives on which we have a
higher risk of being required to perform under the terms of the
credit derivative and are a function of the underlying assets.
We consider the credit risk to be low if the underlying assets
under the credit derivative have an external rating that is
investment grade. If an external rating is not available, we classify
the credit derivative as non-investment grade.
Our maximum exposure to sold credit derivatives is
managed through posted collateral and purchased credit
derivatives with identical or similar reference positions in order
to achieve our desired credit risk profile. The credit risk
management is designed to provide an ability to recover a
significant portion of any amounts that would be paid under sold
credit derivatives.
Credit-Risk Contingent Features
Certain of our derivative contracts contain provisions whereby if
the credit rating of our debt were to be downgraded by certain
major credit rating agencies, the counterparty could demand
additional collateral or require termination or replacement of
derivative instruments in a net liability position. Table 14.8
illustrates our exposure to OTC bilateral derivative contracts with
credit-risk contingent features, collateral we have posted, and
the additional collateral we would be required to post if the credit
rating of our debt was downgraded below investment grade.
Table 14.8: Credit-Risk Contingent Features
(in billions)
Dec 31,
2022
Dec 31,
2021
Net derivative liabilities with credit-risk
contingent features $ 20.7 12.2
Collateral posted 17.4 11.0
Additional collateral to be posted upon a below
investment grade credit rating (1) 3.3 1.2
(1) Any credit rating below investment grade requires us to post the maximum amount of
collateral.
Wells Fargo & Company 147

Note 15: Fair Values of Assets and Liabilities
We use fair value measurements to record fair value adjustments
to certain assets and liabilities and to fulfill fair value disclosure
requirements. Assets and liabilities recorded at fair value on a
recurring basis, such as derivatives, residential MSRs, and trading
or AFS debt securities, are presented in Table 15.1 in this Note.
Additionally, from time to time, we record fair value adjustments
on a nonrecurring basis. These nonrecurring adjustments
typically involve application of lower of cost or fair value
(LOCOM) accounting, write-downs of individual assets or
application of the measurement alternative for nonmarketable
equity securities. Assets recorded at fair value on a nonrecurring
basis are presented in Table 15.4 in this Note. We provide in
Table 15.9 estimates of fair value for financial instruments that
are not recorded at fair value, such as loans and debt liabilities
carried at amortized cost.
FAIR VALUE HIERARCHY We classify our assets and liabilities
recorded at fair value as either Level 1, 2, or 3 in the fair value
hierarchy. The highest priority (Level 1) is assigned to valuations
based on unadjusted quoted prices in active markets and the
lowest priority (Level 3) is assigned to valuations based on
significant unobservable inputs. See Note 1 (Summary of
Significant Accounting Policies) in this Report for a detailed
description of the fair value hierarchy.
In the determination of the classification of financial
instruments in Level 2 or Level 3 of the fair value hierarchy, we
consider all available information, including observable market
data, indications of market liquidity and orderliness, and our
understanding of the valuation techniques and significant inputs
used. This determination is ultimately based upon the specific
facts and circumstances of each instrument or instrument
category and judgments are made regarding the significance of
the unobservable inputs to the instruments’ fair value
measurement in its entirety. If unobservable inputs are
considered significant, the instrument is classified as Level 3.
We do not classify nonmarketable equity securities in the
fair value hierarchy if we use the non-published net asset value
(NAV) per share (or its equivalent) as a practical expedient to
measure fair value. Marketable equity securities with published
NAVs are classified in the fair value hierarchy.
Assets
TRADING DEBT SECURITIES Trading debt securities are recorded
at fair value on a recurring basis. These securities are valued using
internal trader prices that are subject to independent price
verification procedures, which includes comparing internal trader
prices against multiple independent pricing sources, such as
prices obtained from third-party pricing services, observed
trades, and other approved market data. These pricing services
compile prices from various sources and may apply matrix pricing
for similar securities when no price is observable. We review
pricing methodologies provided by pricing services to determine
if observable market information is being used versus
unobservable inputs. When evaluating the appropriateness of an
internal trader price, compared with other independent pricing
sources, considerations include the range and quality of available
information and observability of trade data. These sources are
used to evaluate the reasonableness of a trader price; however,
valuing financial instruments involves judgments acquired from
knowledge of a particular market. Substantially all of our trading
debt securities are recorded using internal trader prices.
AVAILABLE-FOR-SALE DEBT SECURITIES AFS debt securities are
recorded at fair value on a recurring basis. Fair value
measurement for AFS debt securities is based upon various
sources of market pricing. Where available, we use quoted prices
in active markets. When instruments are traded in secondary
markets and quoted prices in active markets do not exist for such
securities, we use prices obtained from third-party pricing
services and, to a lesser extent, may use prices obtained from
independent broker-dealers (brokers), collectively vendor prices.
Substantially all of our AFS debt securities are recorded using
vendor prices. See the “Level 3 Asset and Liability Valuation
Processes – Vendor Developed Valuations” section in this Note
for additional discussion of our processes when using vendor
prices to record fair value of AFS debt securities, which includes
those classified as Level 2 or Level 3 within the fair value
hierarchy.
When vendor prices are deemed inappropriate, they may be
adjusted based on other market data or internal models. We also
use internal models when no vendor prices are available. Internal
models use discounted cash flow techniques or market
comparable pricing techniques.
LOANS HELD FOR SALE (LHFS) LHFS generally includes
commercial and residential mortgage loans originated for sale in
the securitization or whole loan market. A majority of residential
LHFS, and our portfolio of commercial LHFS in our trading
business, are recorded at fair value on a recurring basis. The
remaining LHFS are held at LOCOM which may be written down
to fair value on a nonrecurring basis. Fair value for LHFS that are
not part of our trading business is based on quoted market
prices, where available, or the prices for other mortgage whole
loans with similar characteristics. We may use securitization
prices that are adjusted for typical securitization activities
including servicing value, portfolio composition, market
conditions and liquidity. Fair value for LHFS in our trading
business is based on pending transactions when available. Where
market pricing data or pending transactions are not available, we
use a discounted cash flow model to estimate fair value.
LOANS Although loans are recorded at amortized cost, we record
nonrecurring fair value adjustments to reflect write-downs that
are based on the observable market price of the loan or current
appraised value of the collateral less costs to sell.
MORTGAGE SERVICING RIGHTS (MSRs) Residential MSRs are
carried at fair value on a recurring basis. Commercial MSRs are
carried at LOCOM and may be written down to fair value on a
nonrecurring basis. MSRs do not trade in an active market with
readily observable prices. We determine the fair value of MSRs
using a valuation model that estimates the present value of
expected future net servicing income. The model incorporates
assumptions that market participants may use in estimating
future net servicing income cash flows, including estimates of
prepayment speeds (including housing price volatility for
residential MSRs), discount rates, default rates, cost to service
(including delinquency and foreclosure costs), escrow account
earnings, contractual servicing fee income, ancillary income and
late fees.
DERIVATIVES Derivatives are recorded at fair value on a recurring
basis. The fair value of exchange-traded derivatives that are
actively traded and valued using quoted market prices are
Wells Fargo & Company 148
classified as Level 1 of the fair value hierarchy. The fair val ue of
other derivatives, which predominantly relate to derivatives
traded in over-the-counter (OTC) markets, are measured using
internal valuation techniques, as quoted market prices are not
readily available. These instruments are classified as Level 2 or
Level 3 of the fair value hierarchy, depending on the significa nce
of unobservable inputs in the valuation. Valuation techniques a nd
inputs to internal models depend on the type of derivative and
nature of the underlying rate, price or index upon which the va lue
of the derivative is based. Key inputs can include yield curves ,
credit curves, foreign exchange rates, prepayment rates,
volatility measurements and correlation of certain of these
inputs.
EQUITY SECURITIES Marketable equity securities and certain
nonmarketable equity securities that we have elected to account
for at fair value are recorded at fair value on a recurring basis. Our
remaining nonmarketable equity securities are accounted for
using the equity method, cost method or measurement
alternative and can be subject to nonrecurring fair value
adjustments to record impairment. Additionally, the carrying
value of equity securities accounted for under the measurement
alternative is also remeasured to fair value upon the occurrence
of orderly observable transactions of the same or similar
securities of the same issuer.
We use quoted prices to determine the fair value of
marketable equity securities, as the securities are publicly traded.
Quoted prices are typically not available for nonmarketable
equity securities. We therefore use other methods, generally
market comparable pricing techniques, to determine fair value
for such securities. We use all available information in making this
determination, which includes observable transaction prices for
the same or similar security, prices from third-party pricing
services, broker quotes, trading multiples of comparable public
companies, and discounted cash flow models. Where
appropriate, we make adjustments to observed market data to
reflect the comparative differences between the market data
and the attributes of our equity security, such as differences with
public companies and other investment-specific considerations
like liquidity, marketability or differences in terms of the
instruments.
OTHER ASSETS Although other assets are generally recorded at
amortized cost, we record nonrecurring fair value adjustments to
reflect impairments or the impact of certain lease modifications.
Other assets subject to nonrecurring fair value measurements
include operating lease ROU assets, foreclosed assets and
physical commodities. Fair value is generally based upon
independent market prices or appraised values less costs to sell,
or the use of a discounted cash flow model.
Liabilities
SHORT-SALE TRADING LIABILITIES Short-sale trading liabilities in
our trading business are recorded at fair value on a recurring
basis and are measured using quoted prices in active markets,
where available. When quoted prices for the same instruments
are not available or markets are not active, fair values are
estimated using recent trades of similar securities.
LONG-TERM DEBT Although long-term debt is generally recorded
at amortized cost, we have elected the fair value option for
certain structured notes issued by our trading business. Fair
values for these instruments are estimated using a discounted
cash flow model that includes both the embedded derivative and
debt portions of the notes. The discount rate used in these
discounted cash flow models also incorporates the impact of our
credit spread, which is based on observable spreads in the
secondary bond market.
Level 3 Asset and Liability Valuation Processes
We generally determine fair value of our Level 3 assets and
liabilities by using internal models and, to a lesser extent, prices
obtained from vendors. Our valuation processes vary depending
on which approach is utilized.
INTERNAL MODEL VALUATIONS Certain Level 3 fair value
estimates are based on internal models, such as discounted cash
flow or market comparable pricing techniques. Some of the
inputs used in these valuations are unobservable. Unobservable
inputs are generally derived from or can be correlated to historic
performance of similar portfolios or previous market trades in
similar instruments where particular unobservable inputs may be
implied. We attempt to correlate each unobservable input to
historical experience and other third-party data where available.
Internal models are subject to review prescribed within our
model risk management policies and procedures, which include
model validation. Model validation helps ensure our models are
appropriate for their intended use and appropriate controls exist
to help mitigate risk of invalid valuations. Model validation
assesses the adequacy and appropriateness of our models,
including reviewing its key components, such as inputs,
processing components, logic or theory, output results and
supporting model documentation. Validation also includes
ensuring significant unobservable model inputs are appropriate
given observable market transactions or other market data
within the same or similar asset classes. We also have ongoing
monitoring procedures in place for our Level 3 assets and
liabilities that use internal valuation models. These procedures,
which are designed to provide reasonable assurance that models
continue to perform as expected, include:
• ongoing analysis and benchmarking to market transactions
and other independent market data (including pricing
vendors, if available);
• back-testing of modeled fair values to actual realized
transactions; and
• review of modeled valuation results against expectations,
including review of significant or unusual fluctuations in
value.
We update model inputs and methodologies periodically to
reflect these monitoring procedures. Additionally, existing
models are subject to periodic reviews and we perform full model
revalidations as necessary.
Internal valuation models are subject to ongoing review by
the appropriate principal line of business or enterprise function
and monitoring oversight by Independent Risk Management.
Independent Risk Management, through its Model Risk function,
provides independent oversight of model risk management, and
its responsibilities include governance, validation, periodic review,
and monitoring of model risk across the Company and providing
periodic reports to management and the Board’s Risk
Committee.
VENDOR-DEVELOPED VALUATIONS We routinely obtain pricing
from third-party vendors to value our assets or liabilities. In
certain limited circumstances, this includes assets and liabilities
that we classify as Level 3. We have processes in place to approve
and periodically review third-party vendors to assess whether
information obtained and valuation techniques used are
appropriate. This review may consist of, among other things,
Wells Fargo & Company 149
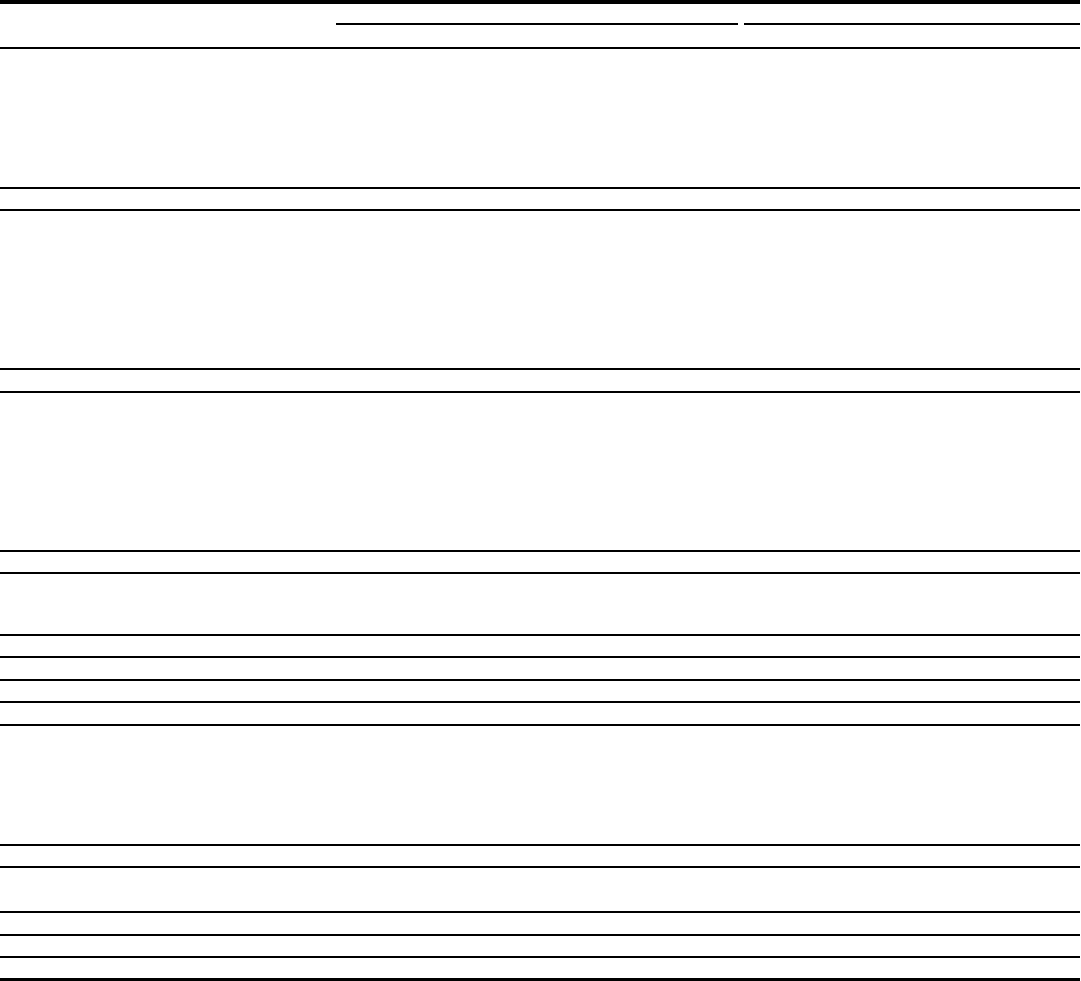
Note 15: Fair Values of Assets and Liabilities (continued)
obtaining and evaluating control reports issued and pricing
methodology materials distributed. We monitor and review
vendor prices on an ongoing basis to evaluate whether the fair
values are reasonable and in line with market experience in
similar asset classes. While the inputs used to determine fair
value are not provided by the pricing vendors, and therefore
unavailable for our review, we perform one or more of the
following procedures to validate the pricing information and
determine appropriate classification within the fair value
hierarchy:
• comparison to other pricing vendors (if available);
• variance analysis of prices;
• corroboration of pricing by reference to other independent
market data, such as market transactions and relevant
benchmark indices;
• review of pricing by Company personnel familiar with market
liquidity and other market-related conditions; and
• investigation of prices on a specific instrument-by -
instrument basis.
Assets and Liabilities Recorded at Fair Value on a
Recurring Basis
Table 15.1 presents the balances of assets and liabilities recorded
at fair value on a recurring basis.
Table 15.1: Fair Va lue o n a Recurring Ba sis
December 31, 2022 December 31, 2021
(in millions) Level 1 Level 2 Level 3 Total Level 1 Level 2 Level 3 Total
Trading debt securities:
Securities of U.S. Treasury and federal agencies $ 28,844 4,530 — 33,374 27,607 2,249 — 29,856
Collateralized loan obligations — 540 150 690 — 655 211 866
Corporate debt securities — 10,344 23 10,367 — 9,987 18 10,005
Federal agency mortgage-backed securities — 34,447 — 34,447 — 40,350 — 40,350
Non-agency mortgage-backed securities — 1,243 12 1,255 — 1,531 11 1,542
Other debt securities — 6,022 — 6,022 — 5,645 1 5,646
Total trading debt securities 28,844 57,126 185 86,155 27,607 60,417 241 88,265
Available-for-sale debt securities:
Securities of U.S. Treasury and federal agencies 45,285 — — 45,285 39,661 — — 39,661
Non-U.S. government securities — 162 — 162 — 71 — 71
Securities of U.S. states and political subdivisions — 10,332 113 10,445 — 16,832 85 16,917
Federal agency mortgage-backed securities — 48,137 — 48,137 — 105,886 — 105,886
Non-agency mortgage-backed securities — 3,284 — 3,284 — 4,522 10 4,532
Collateralized loan obligations — 3,981 — 3,981 — 5,708 — 5,708
Other debt securities — 2,137 163 2,300 — 4,378 91 4,469
Total available-for-sale debt securities 45,285 68,033 276 113,594 39,661 137,397 186 177,244
Loans held for sale — 3,427 793 4,220 — 14,862 1,033 15,895
Mortgage servicing rights (residential) — — 9,310 9,310 — — 6,920 6,920
Derivative assets (gross):
Interest rate contracts 262 40,503 321 41,086 52 22,296 190 22,538
Commodity contracts — 5,866 134 6,000 — 5,902 63 5,965
Equity contracts (1) 112 9,051 410 9,573 6,402 9,350 2,019 17,771
Foreign exchange contracts 27 22,175 11 22,213 8 6,573 7 6,588
Credit contracts — 44 22 66 — 32 14 46
Total derivative assets (gross) 401 77,639 898 78,938 6,462 44,153 2,293 52,908
Equity securities:
Marketable 18,527 86 3 18,616 29,968 82 4 30,054
Nonmarketable (2) — 9,750 17 9,767 — 57 8,906 8,963
Total equity securities 18,527 9,836 20 28,383 29,968 139 8,910 39,017
Total assets prior to derivative netting $ 93,057 216,061 11,482 320,600 103,698 256,968 19,583 380,249
Derivative netting (3) (56,164) (31,430)
Total assets after derivative netting $ 264,436 348,819
Derivative liabilities (gross):
Interest rate contracts $ (193) (40,377) (2,903) (43,473) (28) (17,712) (63) (17,803)
Commodity contracts — (3,325) (120) (3,445) — (2,351) (66) (2,417)
Equity contracts (1) (118) (6,502) (1,652) (8,272) (5,820) (10,753) (2,448) (19,021)
Foreign exchange contracts (29) (26,622) (35) (26,686) (8) (6,654) (10) (6,672)
Credit contracts — (33) (3) (36) — (40) (3) (43)
Total derivative liabilities (gross) (340) (76,859) (4,713) (81,912) (5,856) (37,510) (2,590) (45,956)
Short-sale and other trading liabilities (14,791) (5,513) — (20,304) (15,436) (5,249) — (20,685)
Long-term debt — (1,346) — (1,346) — — — —
Total liabilities prior to derivative netting $ (15,131) $ (83,718) (4,713) (103,562) (21,292) (42,759) (2,590) (66,641)
Derivative netting (3) 61,827 36,532
Total liabilities after derivative netting $ (41,735) (30,109)
(1) During fourth quarter 2022, we changed the technique used to value certain exchanged-traded equity contracts from prices received from exchanges to an internal model. As a result of this change,
these instruments are now classified as Level 2.
(2) Excludes $81 million of nonmarketable equity securities as of December 31, 2021, that are measured at fair value using non-published NAV per share (or its equivalent) as a practical expedient that
are not classified in the fair value hierarchy.
(3) Represents balance sheet netting of derivative asset and liability balances, related cash collateral and portfolio level counterparty valuation adjustments. See Note 14 (Derivatives) for additional
information.
Wells Fargo & Company 150
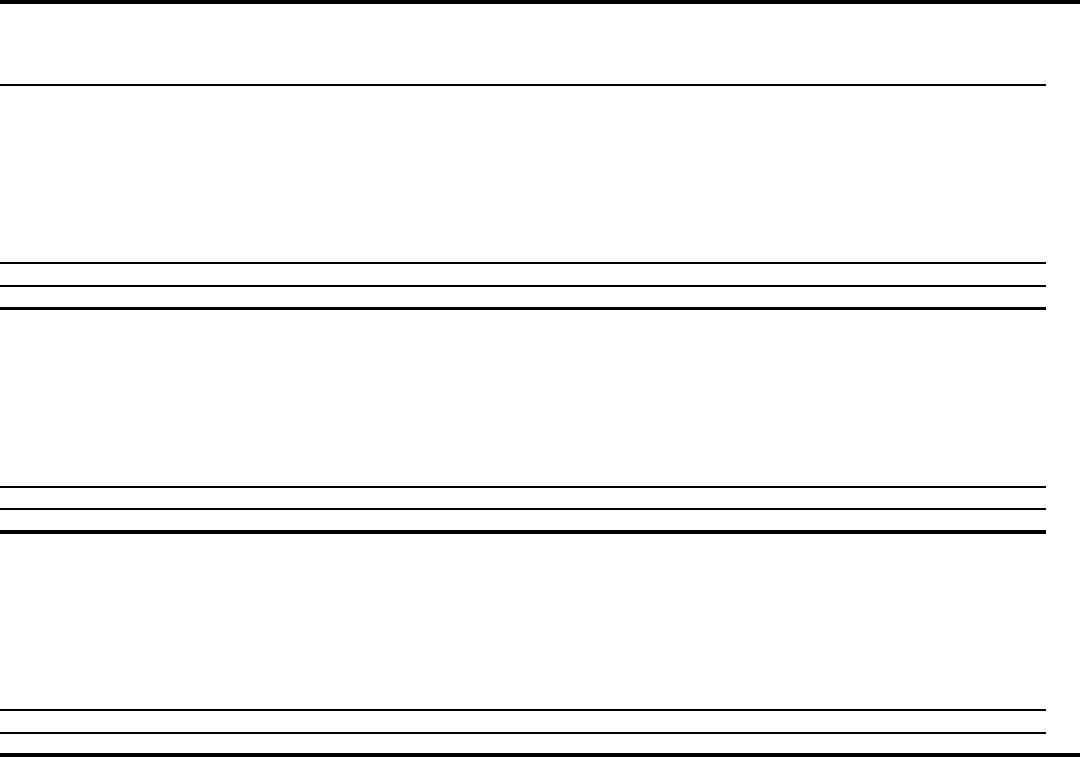
Level 3 Assets and Liabilities Recorded at Fair Value
on a Recurring Basis
Table 15.2 presents the changes in Level 3 assets and
liabilities measured at fair value on a recurring basis.
Table 15.2: Changes in Level 3 Fa ir Va lue Assets a nd Liabilities o n a Recurring Ba sis
(in millions)
Balance,
beginning
of period
Net gains/
(losses) (1) Purchases (2) Sales Settlements
Transfers
into
Level 3 (3)
Transfers
out of
Level 3 (4)
Balance,
end of
period
Net unrealized
gains (losses)
related to
assets and
liabilities held
at period end (5)
Year ended December 31, 2022
Trading debt securities
$ 241 (72) 218 (186) (6) 22 (32) 185 (73) (6)
Available-for-sale debt securities 186 (36) 327 (26) (25) 460 (610) 276 (10) (6)
Loans held for sale 1,033 (252) 389 (391) (207) 237 (16) 793 (170) (7)
Mortgage servicing rights (residential) (8) 6,920 2,001 1,003 (614) — — — 9,310 3,254 (7)
Net derivative assets and liabilities:
Interest rate contracts 127 (3,280) — — 994 (435) 12 (2,582) (2,073)
Equity contracts (429) 28 — (9) 721 (584) (969) (1,242) 271
Other derivative contracts 5 (68) 19 (9) 118 (16) (40) 9 (16)
Total derivative contracts (297) (3,320) 19 (18) 1,833 (1,035) (997) (3,815) (1,818) (9)
Equity securities 8,910 4 1 (2) — 3 (8,896) 20 (2) (6)
Year ended December 31, 2021
Trading debt securities
$ 173 7 518 (448) (12) 34 (31) 241 (8) (6)
Available-for-sale d ebt securities 2,994 21 809 (112) (278) 353 (3,601) 186 (4) (6)
Loans h eld for sale 1,234 (25) 477 (534) (377) 394 (136) 1,033 (26) (7)
Mortgage ser vicing rights (r esidential) (8) 6,125 (842) 1,645 (8) — — — 6,920 1,170 (7)
Net derivative a ssets a nd liabilities:
Interest rate cont racts 446 27 — — (340) (5) (1) 127 (75)
Equity contracts (314) (468) — — 379 (228) 202 (429) (266)
Other derivative cont racts 39 (114) 3 (3) 77 — 3 5 (36)
Total d erivative cont racts 171 (555) 3 (3) 116 (233) 204 (297) (377) (9)
Equity securities 9,233 (267) 1 (68) — 11 — 8,910 (316) (6)
Year ended December 31, 2020
Trading debt securities
$ 223 (53) 600 (589) (12) 115 (111) 173 (36) (6)
Available-for-sale d ebt securities 1,565 (34) 43 (68) (263) 2,255 (504) 2,994 1 (6)
Loans h eld for sale 1,214 (96) 1,312 (586) (323) 1,927 (2,214) 1,234 (38) (7)
Mortgage ser vicing rights (r esidential) (8) 11,517 (7,068) 1,707 (32) 1 — — 6,125 (4,693) (7)
Net derivative a ssets a nd liabilities:
Interest rate cont racts 214 2,074 — — (1,842) — — 446 334
Equity contracts (269) (316) — — 298 (22) (5) (314) (19)
Other derivative cont racts (5) (63) 8 3 73 22 1 39 11
Total d erivative cont racts (60) 1,695 8 3 (1,471) — (4) 171 326 (9)
Equity securities 7,850 1,369 2 — — 23 (11) 9,233 1,370 (6)
(1) Includes net gains (losses) included in both net income and other comprehensive income. All amounts represent net gains (losses) included in net income except for $(37) million, $41 million and
$0 million included in other comprehensive income from AFS debt securities for the years ended December 31, 2022, 2021 and 2020, respectively.
(2) Includes originations of mortgage servicing rights and loans held for sale.
(3) All assets and liabilities transferred into Level 3 were previously classified within Level 2.
(4) All assets and liabilities transferred out of Level 3 are classified as Level 2. During first quarter 2022, we transferred $8.9 billion of non-marketable equity securities and $1.4 billion of related
economic hedging derivative assets (equity contracts) out of Level 3 due to our election to measure fair value of these instruments as a portfolio. Under this election, the unit of valuation is the
portfolio-level, rather than each individual instrument. The unobservable inputs previously significant to the valuation of the instruments individually are no longer significant, as those unobservable
inputs offset under the portfolio election.
(5) Includes net unrealized gains (losses) related to assets and liabilities held at period end included in both net income and other comprehensive income. All amounts represent net unrealized gains
(losses) included in net income except for $(9) million, $(1) million and $57 million included in other comprehensive income from AFS debt securities for the years ended December 31, 2022, 2021
and 2020, respectively.
(6) Included in net gains from trading and securities on our consolidated statement of income.
(7) Included in mortgage banking income on our consolidated statement of income.
(8) For additional information on the changes in mortgage servicing rights, see Note 6 (Mortgage Banking Activities).
(9) Included in mortgage banking income, net gains from trading and securities, and other noninterest income on our consolidated statement of income.
Wells Fargo & Company 151
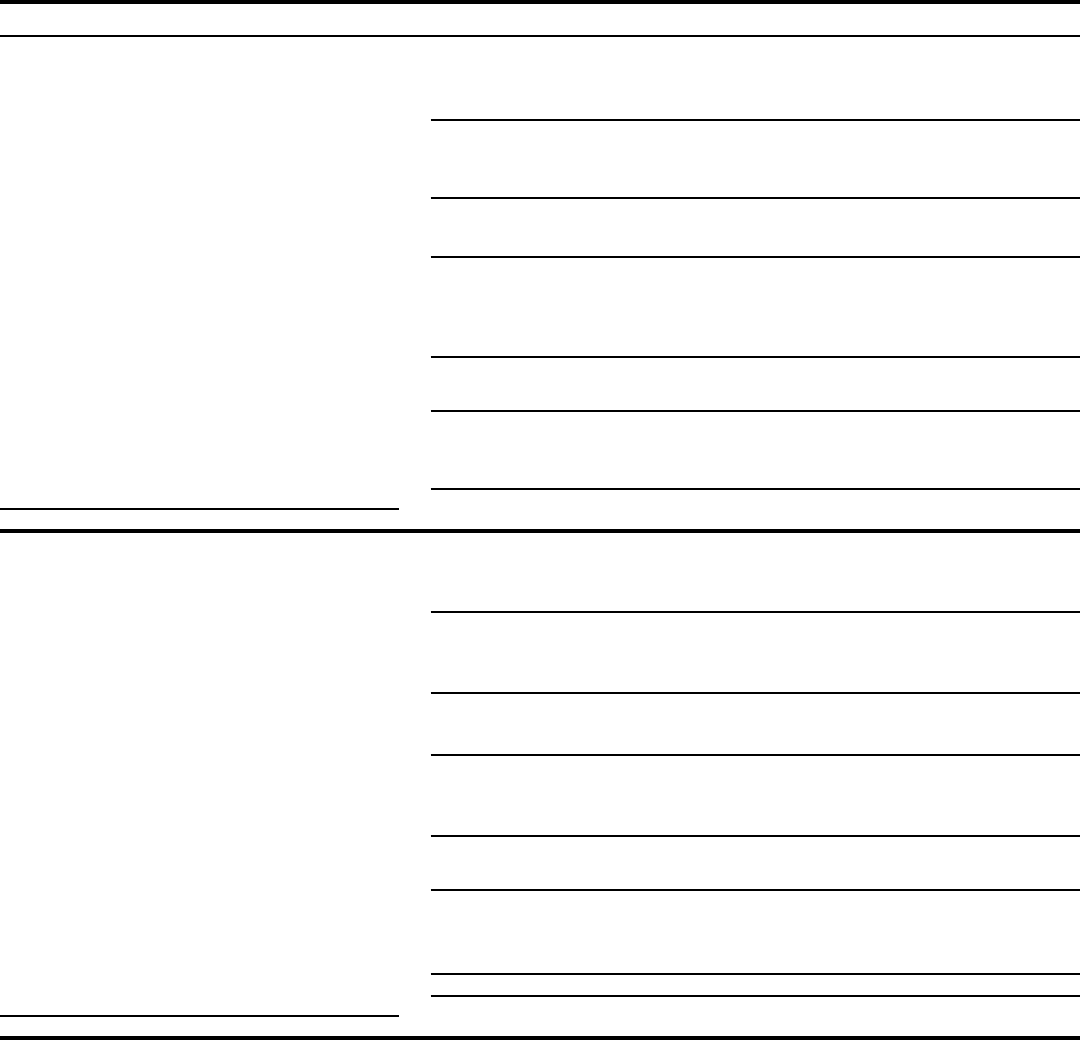
Note 15: Fair Values of Assets and Liabilities (continued)
Table 15.3 provides quantitative information about the
valuation techniques and significant unobservable inputs used in
the valuation of our Level 3 assets and liabilities measured at fair
value on a recurring basis.
The significant unobservable inputs for Level 3 assets
inherent in the fair values obtained from third-party vendors are
not included in the table, as the specific inputs applied are not
provided by the vendor (see discussion in the “Level 3 Asset and
Liability Valuation Processes” section within this Note regarding
vendor-developed valuations).
Weighted averages of inputs are calculated using
outstanding unpaid principal balance for cash instruments, such
as loans and securities, and notional amounts for derivative
instruments.
Table 15.3: Valuation Techniques – Recurring Ba sis
($ in millions, except cost to service amounts)
Fair Value
Level 3 Valuation Technique
Significant
Unobservable Input Range of Inputs
Weighted
Average
December 31, 2022
Trading and available-for-sale debt securities $ 157 Discounted cash flow Discount rate 2.7 - 12.5 % 6.4
185 Market comparable pricing Comparability adjustment (33.6) - 14.1 (4.8)
119 Market comparable pricing Multiples 1.1x - 7.4x 4.0x
Loans held for sale 793 Discounted cash flow Default rate 0.0 - 25.0 % 0.7
Discount rate 2.9 - 13.4 9.5
Loss severity 0.0 - 53.6 15.7
Prepayment rate 3.5 - 14.2 10.7
Mortgage servicing rights (residential) 9,310 Discounted cash flow Cost to service per loan (1) $ 52 - 550 102
Discount rate 8.7 - 14.1 % 9.1
Prepayment rate (2) 8.1 - 21.9 9.4
Net derivative assets and (liabilities):
Interest rate contracts (2,411) Discounted cash flow Discount rate 3.2 - 4.9 4.2
(63) Discounted cash flow Default rate 0.4 - 5.0 2.3
Loss severity 50.0 - 50.0 50.0
Prepayment rate 2.8 - 22.0 18.7
Interest rate contracts: derivative loan
commitments (108) Discounted cash flow Fall-out factor 1.0 - 99.0 41.0
Initial-value servicing (9.3) - 141.0 bps 11.5
Equity contracts (1,000) Discounted cash flow Conversion factor (12.2) - 0.0 % (9.9)
Weighted average life 0.5 - 1.5 yrs 0.8
(242) Option model Correlation factor (77.0) - 99.0 % 49.5
Volatility factor 6.5 - 96.5 37.3
Insignificant Level 3 assets, net of liabilities 29
Total Level 3 assets, net of liabilities $ 6,769 (3)
December 31, 2021
Trading and available-for-sale debt securities $ 136 Discounted cash flow Discount rate 0.4 - 12.5 % 5.5
11 Vendor priced
280 Market comparable pricing Comparability adjustment (30.2) - 19. 2 (4.6)
Loans held for sale 1,033 Discounted cash flow Default rate 0.0 - 29.2 % 1.2
Discount rate 1.6 - 11.9 5.1
Loss severity 0.0 - 46.9 15.4
Prepayment rate 7. 5 - 18. 2 13.1
Mortgage servicing rights (residential) 6,920 Discounted cash flow Cost to service per loan (1) $ 54 - 585 106
Discount rate 5. 8 - 8. 8 % 6.4
Prepayment rate (2) 12. 5 - 21. 1 14.7
Net derivative assets and (liabilities):
Interest rate contracts 87 Discounted cash flow Default rate 0. 0 - 5. 0 2.1
Loss severity 50. 0 - 50. 0 50.0
Prepayment rate 2. 8 - 22. 0 18.7
Interest rate contracts: derivative loan
commitments 40 Discounted cash flow Fall-out factor 1. 0 - 99. 0 16.8
Initial-value servicing (74.8) - 146.0 bps 50.9
Equity contracts 253 Discounted cash flow Conversion factor (10. 2) - 0. 0 % (9.7)
Weighted average life 0.5 - 2.0 yrs 1.1
(682) Option model Correlation factor (77. 0) - 99. 0 % 23.2
Volatility factor 6. 5 - 72. 0 29.1
Nonmarketable equity securities 8,906 Market comparable pricing Comparability adjustment (21. 6) - (7. 7) (15.5)
Insignificant Level 3 assets, net of liabilities 9
Total Level 3 assets, net of liabilities $ 16,993 (3)
(1) The high end of the range of inputs is for servicing modified loans. For non-modified loans the range is $52 - $178 at December 31, 2022, and $54 - $199 at December 31, 2021.
(2) Includes a blend of prepayment speeds and expected defaults. Prepayment speeds are influenced by mortgage interest rates as well as our estimation of drivers of borrower behavior.
(3) Consists of total Level 3 assets of $11.5 billion and $19.6 billion and total Level 3 liabilities of $4.7 billion and $2.6 billion, before netting of derivative balances, at December 31, 2022 and 2021,
respectively.
Wells Fargo & Company 152
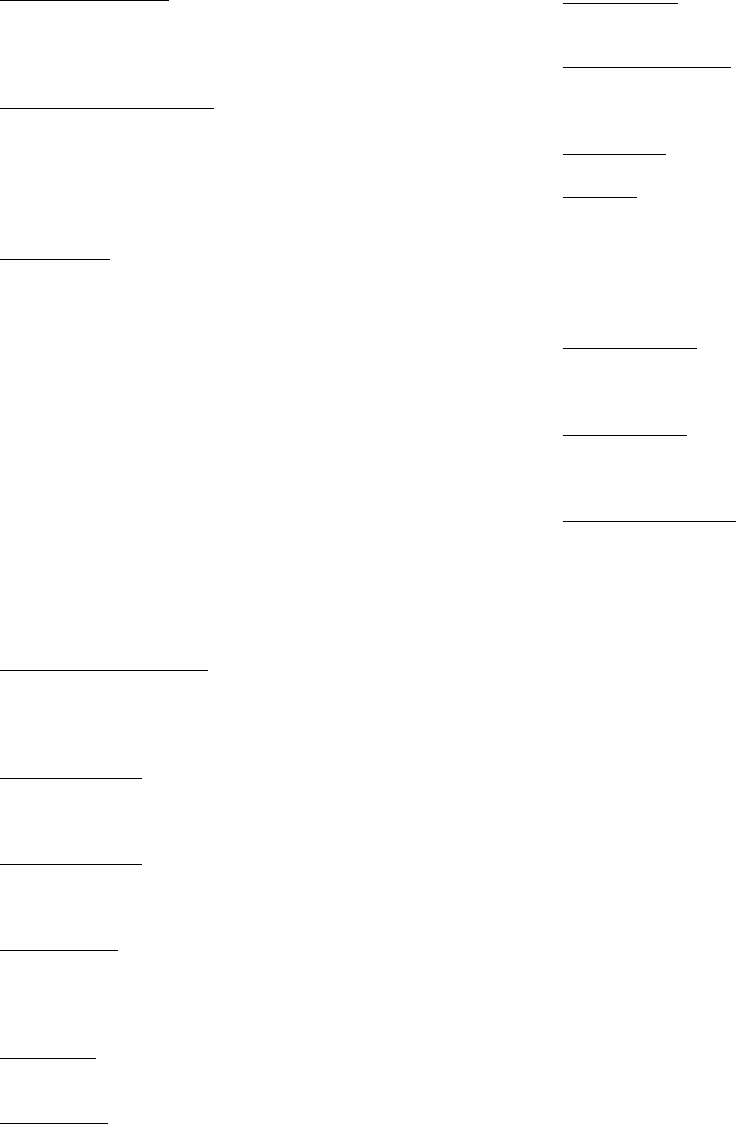
The internal valuation techniques used for our Level 3 assets
and liabilities, as presented in Table 15.3, are described as
follows:
• Discounted cash flow – Discounted cash flow valuation
techniques generally consist of developing an estimate of
future cash flows that are expected to occur over the life of
an instrument and then discounting those cash flows at a
rate of return that results in the fair value amount.
• Market comparable pricing – Market comparable pricing
valuation techniques are used to determine the fair value of
certain instruments by incorporating known inputs, such as
recent transaction prices, pending transactions, financial
metrics of comparable companies, or prices of other similar
investments that require significant adjustment to reflect
differences in instrument characteristics.
• Option model – Option model valuation techniques are
generally used for instruments in which the holder has a
contingent right or obligation based on the occurrence of a
future event, such as the price of a referenced asset going
above or below a predetermined strike price. Option models
estimate the likelihood of the specified event occurring by
incorporating assumptions such as volatility estimates, price
of the underlying instrument and expected rate of return.
The unobservable inputs presented in the previous tables are
those we consider significant to the fair value of the Level 3 asset
or liability. We consider unobservable inputs to be significant if
by their exclusion the fair value of the Level 3 asset or liability
would be impacted by a predetermined percentage change. We
also consider qualitative factors, such as nature of the
instrument, type of valuation technique used, and the
significance of the unobservable inputs relative to other inputs
used within the valuation. Following is a description of the
significant unobservable inputs provided in the table.
• Comparability adjustment – is an adjustment made to
observed market data, such as a transaction price to reflect
dissimilarities in underlying collateral, issuer, rating, or ot her
factors used within a market valuation approach, expressed
as a percentage of an observed price.
• Conversion factor – is the risk-adjusted rate in which a
particular instrument may be exchanged for another
instrument upon settlement, expressed as a percentage
change from a specified rate.
• Correlation factor – is the likelihood of one instrument
changing in price relative to another based on an established
relationship expressed as a percentage of relative change in
price over a period over time.
• Cost to service – is the expected cost per loan of servicing a
portfolio of loans, which includes estimates for
unreimbursed expenses (including delinquency and
foreclosure costs) that may occur as a result of servicing
such loan portfolios.
• Default rate – is an estimate of the likelihood of not
collecting contractual amounts owed expressed as a
constant default rate (CDR).
• Discount rate – is a rate of return used to calculate the
present value of the future expected cash flow to arrive at
the fair value of an instrument. The discount rate consists
of a benchmark rate component and a risk premium
component. The benchmark rate component, for example,
OIS, London Interbank Offered Rate (LIBOR), Secured
Overnight Financing Rate (SOFR) or U.S. Treasury rates, is
generally observable within the market and is necessary to
appropriately reflect the time value of money. The risk
premium component reflects the amount
of compensation market participants require due to the
uncertainty inherent in the instruments’ cash flows resulting
from risks such as credit and liquidity.
• Fall-out factor – is the expected percentage of loans
associated with our interest rate lock commitment portfolio
that are likely of not funding.
• Initial-value servicing – is the estimated value of the
underlying loan, including the value attributable to the
embedded servicing right, expressed in basis points of
outstanding unpaid principal balance.
• Loss severity – is the estimated percentage of contractual
cash flows lost in the event of a default.
• Multiples – are financial ratios of comparable public
companies, such as ratios of enterprise value or market value
of equity to earnings before interest, depreciation, and
amortization (EBITDA), revenue, net income or book value,
adjusted to reflect dissimilarities in operational, financial, or
marketability to the comparable public company used in a
market valuation approach.
• Prepayment rate – is the estimated rate at which forecasted
prepayments of principal of the related loan or debt
instrument are expected to occur, expressed as a constant
prepayment rate (CPR).
• Volatility factor – is the extent of change in price an item is
estimated to fluctuate over a specified period of time
expressed as a percentage of relative change in price over a
period over time.
• Weighted average life – is the weighted average number of
years an investment is expected to remain outstanding
based on its expected cash flows reflecting the estimated
date the issuer will call or extend the maturity of the
instrument or otherwise reflecting an estimate of the timing
of an instrument’s cash flows whose timing is not
contractually fixed.
Interrelationships and Uncertainty of Inputs Used in
Recurring Level 3 Fair Value Measurements
Usage of the valuation techniques presented in Table 15.3
requires determination of relevant inputs and assumptions, some
of which represent significant unobservable inputs. Accordingly,
changes in these unobservable inputs may have a significant
impact on fair value.
Certain of these unobservable inputs will (in isolation) have a
directionally consistent impact on the fair value of the
instrument for a given change in that input. Alternatively, the fair
value of the instrument may move in an opposite direction for a
given change in another input. Where multiple inputs are used
within the valuation technique of an asset or liability, a change in
one input in a certain direction may be offset by an opposite
change in another input having a potentially muted impact to the
overall fair value of that particular instrument. Additionally, a
change in one unobservable input may result in a change to
another unobservable input (that is, changes in certain inputs are
interrelated to one another), which may counteract or magnify
the fair value impact.
DEBT SECURITIES AND LOANS HELD FOR SALE The internal models
used to determine fair value for these Level 3 instruments use
certain significant unobservable inputs within a discounted cash
flow or market comparable pricing valuation technique. Such
inputs include discount rate, prepayment rate, default rate, loss
severity, multiples, and comparability adjustment.
These Level 3 assets would decrease (increase) in value
based upon an increase (decrease) in discount rate, default rate
or loss severity inputs and would generally decrease (increase) in
Wells Fargo & Company 153
Note 15: Fair Values of Assets and Liabilities (continued)
value based upon an increase (decrease) in prepayment rate.
Conversely, these Level 3 assets would increase (decrease) in
value based upon an increase (decrease) in multiples. The
comparability adjustment input may have a positive or negative
impact on fair value depending on the change in fair value of the
item the comparability adjustment references.
Generally, a change in the assumption used for the default
rate is accompanied by a directionally similar change in the risk
premium component of the discount rate (specifically, the
portion related to credit risk) and a directionally opposite change
in the assumption used for prepayment rates. Unobservable
inputs for comparability adjustment, multiples, and loss severity
do not increase or decrease based on movements in the other
significant unobservable inputs for these Level 3 assets.
MORTGAGE SERVICING RIGHTS The discounted cash flow models
used to determine fair value of Level 3 MSRs utilize certain
significant unobservable inputs including prepayment rate,
discount rate and costs to service. An increase in any of these
unobservable inputs will reduce the fair value of the MSRs and
alternatively, a decrease in any one of these inputs would result in
the MSRs increasing in value. Generally, a decrease in discount
rates increases the value of MSRs, unless accompanied by a
related update to our prepayment rates. The cost to service
assumption generally does not increase or decrease based on
movements in the discount rate or the prepayment rate. The
sensitivity of our residential MSRs is discussed further in Note 6
(Mortgage Banking Activities).
DERIVATIVE INSTRUMENTS Level 3 derivative instruments are
valued using market comparable pricing, option pricing and
discounted cash flow valuation techniques which use certain
unobservable inputs to determine fair value. Such inputs consist
of prepayment rate, default rate, loss severity, initial-value
servicing, fall-out factor, volatility factor, weighted average life,
conversion factor, and correlation factor.
Level 3 derivative assets (liabilities) where we are long the
underlying would decrease (increase) in value upon an increase
(decrease) in default rate, fall-out factor, conversion factor, or
loss severity inputs. Conversely, Level 3 derivative assets
(liabilities) would generally increase (decrease) in value upon an
increase (decrease) in prepayment rate, initial-value servicing,
weighted average life or volatility factor inputs. The inverse of
the above relationships would occur for instruments when we are
short the underlying. The correlation factor input may have a
positive or negative impact on the fair value of derivative
instruments depending on the change in fair value of the item
the correlation factor references.
Generally, for derivative instruments for which we are
subject to changes in the value of the underlying referenced
instrument, a change in the assumption used for default rate is
accompanied by directionally similar change in the risk premium
component of the discount rate (specifically, the portion related
to credit risk) and a directionally opposite change in the
assumption used for prepayment rates. Unobservable inputs for
loss severity, initial-value servicing, fall-out factor, volatility
factor, weighted average life, conversion factor, and correlation
factor do not increase or decrease based on movements in other
significant unobservable inputs for these Level 3 instruments.
NONMARKETABLE EQUITY SECURITIES Level 3 nonmarketable
equity securities are valued using a market comparable pricing
valuation technique, with a comparability adjustment as the
single significant unobservable input. The comparability
adjustment input may have a positive or negative impact on fair
value depending on the change in fair value of the item the
comparability adjustment references.
Assets and Liabilities Recorded at Fair Value on a
Nonrecurring Basis
We may be required, from time to time, to measure certain
assets at fair value on a nonrecurring basis in accordance with
GAAP. These adjustments to fair value usually result from
application of LOCOM accounting, write-downs of individual
assets, or application of the measurement alternative for certain
nonmarketable equity securities.
Table 15.4 provides the fair value hierarchy and fair value at
the date of the nonrecurring fair value adjustment for all assets
that were still held as of December 31, 2022 and 2021, and for
which a nonrecurring fair value adjustment was recorded during
the years then ended.
Table 15.4: Fair Va lue o n a Nonrecurring Ba sis
December 31, 2022
December 31, 2021
(in millions) Level 2
Level 3
Total
Level 2
Level 3
Total
Loans held for sale (1) $ 838
554
1,392
3,911
1,407
5,318
Loans:
Commercial 285 — 285 476 — 476
Consumer 512 — 512 380 — 380
Total loans 797 — 797 856 — 856
Mortgage servicing rights (commercial)
—
75
75
—
567
567
Nonmarketable equity securities
1,926
2,818
4,744
6,262
765
7,027
Other assets
1,862
296
2,158
1,373
175
1,548
Total assets at fair value on a nonrecurring basis $
5,423
3,743
9,166
12,402
2,914
15,316
(1) Predominantly consists of commercial mortgages and residential mortgage – first lien loans.
Table 15.5 presents the gains (losses) on certain assets held
at the end of the reporting periods presented for which a
nonrecurring fair value adjustment was recognized in earnings
during the respective periods.
Wells Fargo & Company 154
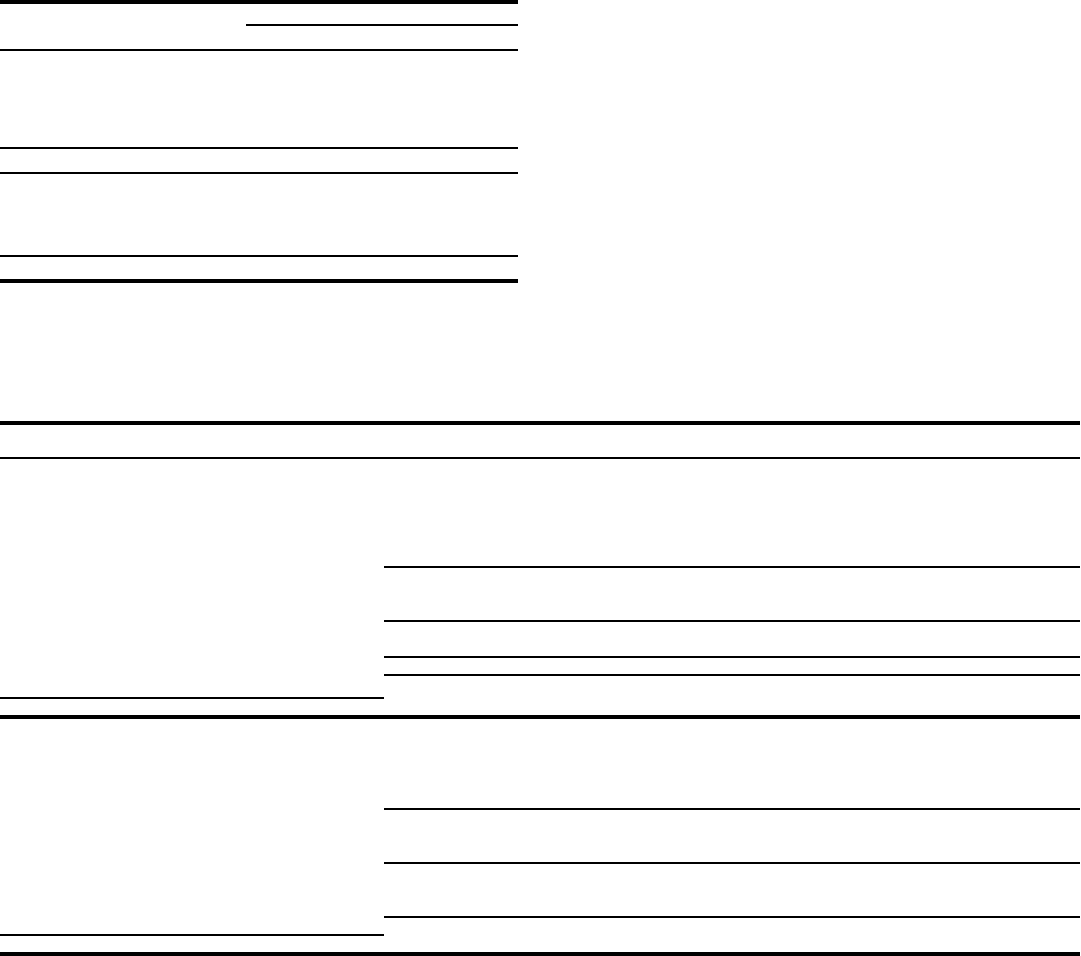
Table 15.5: Gains (Losses) on Assets with Nonrecurring Fair Value
Adjustment
Year ended December 31,
(in millions) 2022 2021 2020
Loans held for sale $ (120) 33 12
Loans:
Commercial (96) (230) (754)
Consumer (739) (564) (260)
Total loans (835) (794) (1,014)
Mortgage servicing rights
(commercial) 4 33 (37)
Nonmarketable equity securities (1) (1,191) 4,407 435
Other assets (2) (275) (388) (469)
Total $ (2,417) 3,291 (1,073)
(1) Includes impairment of nonmarketable equity securities and observable price changes
related to nonmarketable equity securities accounted for under the measurement
alternative.
(2) Includes impairment of operating lease ROU assets, valuation of physical commodities,
valuation losses on foreclosed real estate and other collateral owned, and impairment of
private equity and venture capital investments in consolidated portfolio companies.
Table 15.6 provides quantitative information about the
valuation techniques and significant unobservable inputs used in
the valuation of our Level 3 assets that are measured at fair value
on a nonrecurring basis and determined using an internal model.
The table is limited to financial instruments that had
nonrecurring fair value adjustments during the periods
presented. Weighted averages of inputs are calculated using
outstanding unpaid principal balance for cash instruments, such
as loans, and carrying value prior to the nonrecurring fair value
measurement for nonmarketable equity securities and private
equity and venture capital investments in consolidated portfolio
companies.
Table 15.6: Valuation Techniques – Nonrecurring Basis
($ in millions)
Fair Value
Level 3
Valuation
Technique (1)
Significant
Unobservable Input (1)
Range of Inputs
Positive (Negative)
Weighted
Average
December 31, 2022
Loans held for sale (2) $ 143 Discounted cash flow Default rate (3) 0.1 - 86.1 % 13.8
Discount rate 3.8 - 13.8 9.0
Loss severity 8.1 - 43.8 18.6
Prepayment rate (4) 2.3 - 23.4 18.6
411 Market comparable pricing Comparability adjustment (8.2) - (0.9) (4.3)
Mortgage servicing rights (commercial) 75 Discounted cash flow Cost to service per loan $ 3,775 - 3,775 3,775
Discount rate 5.2 - 5.2 % 5.2
Prepayment rate 0.0 - 20.6 6.7
Nonmarketable equity securities 1,461 Market comparable pricing Comparability adjustment (100.0) - (4.0) (30.1)
1,352 Market comparable pricing Multiples 0.8x - 18.7x 9.9x
Other assets (5) 234 Market comparable pricing Multiples 6.4 - 8.0 7.1
Insignificant Level 3 assets 67
Total $ 3,743
December 31, 2021
Loans h eld for sale (2) $ 1,407 Discounted cash flow Default rate (3) 0.2 - 78. 3 % 25.6
Discount rate 0.6 - 12.0 3.3
Loss sev erity 0. 4 - 45.6 4.8
Prepayment rate (4) 5. 4 - 100. 0 38. 9
Mortgage ser vicing rights (com mercial) 567 Discounted cash flow Cost to ser vice p er loan $ 150 - 3,381 2,771
Discount rate 4. 0 - 4. 5 % 4. 0
Prepayment rate 0. 0 - 20. 6 5. 5
Nonmarketable eq uity securities 745 Market comparable p ricing Comparability adjustment (100. 0) - (33. 0) (59. 0)
15 Market comparable p ricing Multiples 2.0x - 3.3x 2.8x
5 Discounted cash flow Discount rate 10. 5 - 10. 5 % 10. 5
Other assets 175 Discounted cash flow Discount rate 0. 2 - 4. 4 2. 9
Total $ 2,914
(1) Refer to the narrative following Table 15.3 for a definition of the valuation technique(s) and significant unobservable inputs used in the valuation of loans held for sale, mortgage servicing rights,
certain nonmarketable equity securities, and other assets.
(2) Consists of approximately $400 million and $1.2 billion of government insured/guaranteed loans purchased from GNMA-guaranteed mortgage securitizations at December 31, 2022 and 2021,
respectively, and approximately $150 million and $200 million of other mortgage loans that are not government insured/guaranteed at December 31, 2022 and 2021, respectively.
(3) Applies only to non-government insured/guaranteed loans.
(4) Includes the impact on prepayment rate of expected defaults for government insured/guaranteed loans, which impact the frequency and timing of early resolution of loans.
(5) Represents private equity and venture capital investments in consolidated portfolio companies.
Wells Fargo & Company 155
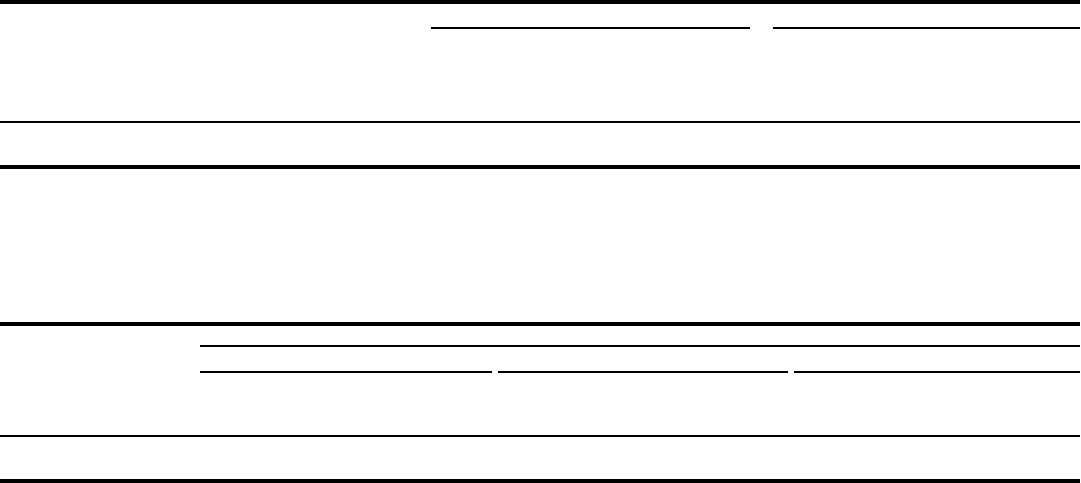
Note 15: Fair Values of Assets and Liabilities (continued)
Fair Value Option
The fair value option is an irrevocable election, generally only
permitted upon initial recognition of financial assets or liabilities,
to measure eligible financial instruments at fair value with
changes in fair value reflected in earnings. We may elect the fair
value option to align the measurement model with how the
financial assets or liabilities are managed or to reduce complexity
or accounting asymmetry. Following is a discussion of the
portfolios for which we elected the fair value option.
LOANS HELD FOR SALE (LHFS) LHFS measured at fair value include
residential mortgage loan originations for which an active
secondary market and readily available market prices exist to
reliably support our valuations. Loan origination fees on these
loans are recorded when earned, and related direct loan
origination costs are recognized when incurred. We believe fair
value measurement for LHFS reduces certain timing differences
and better matches changes in the value of these assets with
changes in the value of derivatives used as economic hedges for
these assets.
Additionally we purchase loans for market-making purposes
to support the buying and selling demands of our customers in
our trading business. These loans are generally held for a short
period of time and managed within parameters of internally
approved market risk limits. Fair value measurement best aligns
with our risk management practices. Fair value for these loans is
generally determined using readily available market data based
on recent transaction prices for similar loans.
LONG-TERM DEBT We have elected to account for certain
structured debt liabilities under the fair value option. These
exposures relate to our trading activities and fair value
accounting better aligns with our risk management practices and
reduces complexity.
For long-term debt carried at fair value, the change in fair
value attributable to instrument-specific credit risk is recorded in
OCI and all other changes in fair value are recorded in earnings.
Table 15.7 reflects differences between the fair value
carrying amount of the assets and liabilities for which we have
elected the fair value option and the contractual aggregate
unpaid principal amount at maturity.
Table 15.7: Fair Value Option
December 31, 2022 December 31, 2021
(in millions)
Fair valu e
carrying
amount
Aggregate
unpaid
principal
Fair valu e
carrying
amount less
aggregate
unpaid
principal
Fair value
carrying
amount
Aggregate
unpaid
principal
Fair value
carrying
amount less
aggregate
unpaid
principal
Loans held for sale (1) $ 4,220 4,614 (394) 15,895 15,750 145
Long-term debt (1,346) (1,775) 429 — — —
(1) Nonaccrual loans and loans 90 days or more past due and still accruing included in LHFS for which we have elected the fair value option were insignificant at December 31, 2022 and 2021.
Table 15.8 reflects amounts included in earnings related to
initial measurement and subsequent changes in fair value, by
income statement line item, for assets and liabilities for whic h
the fair value option was elected . Amounts recorded in net
interest income are excluded from the table below.
Table 15.8: Gains (Lo sses) o n C hanges in Fa ir Va lue Includ ed in Ea rnings
Year ended December 31,
2022 2021 2020
(in millions)
Mortgage
banking
noninterest
income
Net gains
from trading
and
securities
Other
noninterest
income
Mortgage
banking
noninterest
income
Net gains
from trading
and
securities
Other
noninterest
income
Mortgage
banking
noninterest
income
Net gains
from trading
and
securities
Other
noninterest
income
Loans held for sale $
(681)
6
—
1,972
54
2
2,719
28
1
Long-term debt
—
52
—
—
—
—
—
—
—
For performing loans, instrument-specific credit risk gains or
losses are derived principally by determining the change in fair
value of the loans due to changes in the observable or implied
credit spread. Credit spread is the market yield on the loans less
the relevant risk-free benchmark interest rate. For
nonperforming loans, we attribute all changes in fair value to
instrument-specific credit risk. For LHFS accounted for under the
fair value option, instrument-specific credit gains or losses for
the years ended December 31, 2022, 2021 and 2020 were
insignificant.
For long-term debt, instrument-specific credit risk gains or
losses represent the impact of changes in fair value due to
changes in our credit spread and are derived using observable
secondary bond market information. These impacts are recorded
in OCI. See amounts relating to debit valuation adjustments
(DVA) within Note 24 (Other Comprehensive Income) for
additional information.
Wells Fargo & Company 156
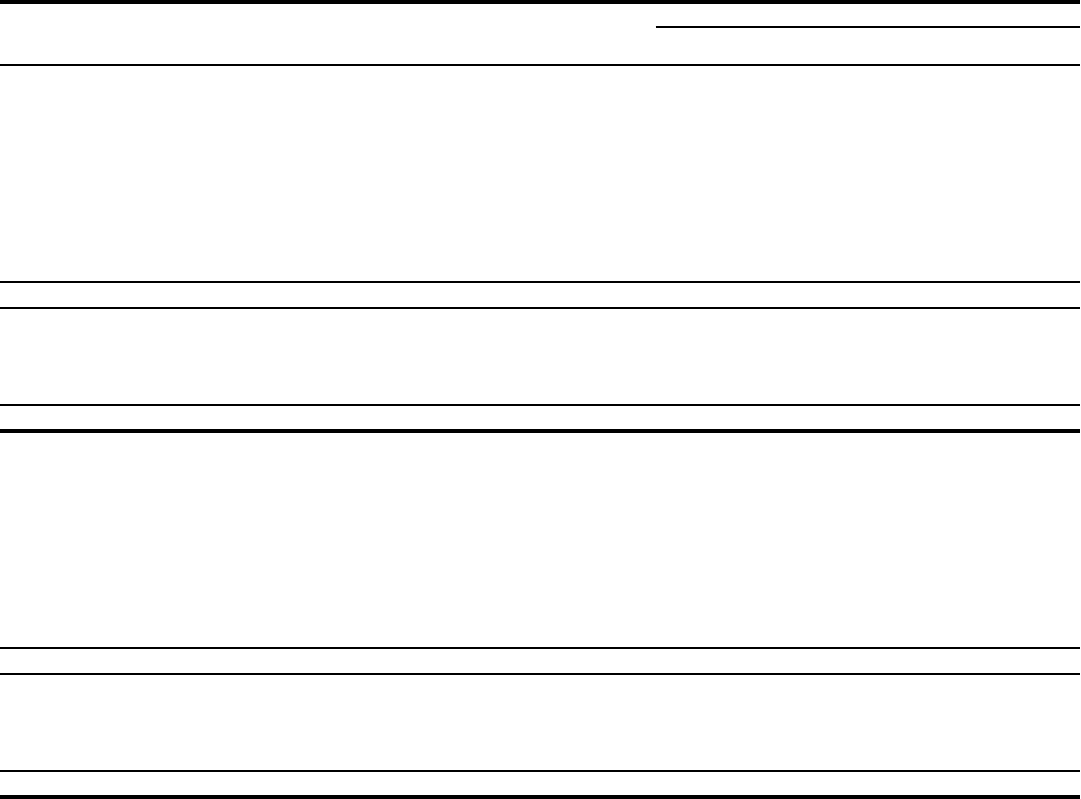
Disclosures about Fair Value of Financial Instruments
Table 15.9 presents a summary of fair value estimates for
financial instruments that are not carried at fair value on a
recurring basis. Some financial instruments are excluded from
the scope of this table, such as certain insurance contracts,
certain nonmarketable equity securities, and leases. This table
also excludes assets and liabilities that are not financial
instruments such as the value of the long-term relationships with
our deposit, credit card and trust customers, MSRs, premises and
equipment, goodwill and deferred taxes.
Loan commitments, standby letters of credit and
commercial and similar letters of credit are not included in
Table 15.9. A reasonable estimate of the fair value of these
instruments is the carrying value of deferred fees plus the
allowance for unfunded credit commitments, which totaled
$737 million and $1.4 billion at December 31, 2022 and 2021,
respectively.
The total of the fair value calculations presented does not
represent, and should not be construed to represent, the
underlying fair value of the Company.
Table 15.9: Fair Value Estimates for Financial Instruments
Estimated fair value
(in millions)
Carrying
amount Level 1 Level 2 Level 3 Total
December 31, 2022
Financial assets
Cash and due from banks (1) $ 34,596 34,596 — — 34,596
Interest-earning deposits with banks (1) 124,561 124,338 223 — 124,561
Federal funds sold and securities purchased under resale agreements (1) 68,036 — 68,036 — 68,036
Held-to-maturity debt securities 297,059 14,285 238,552 2,684 255,521
Loans held for sale 2,884 — 2,208 719 2,927
Loans, net (2) 928,049 — 57,532 836,831 894,363
Nonmarketable equity securities (cost method) 4,900 — — 4,961 4,961
Total financial assets $ 1,460,085 173,219 366,551 845,195 1,384,965
Financial liabilities
Deposits (3) $ 66,887 — 46,745 18,719 65,464
Short-term borrowings 50,964 — 50,970 — 50,970
Long-term debt (4) 173,502 — 172,783 999 173,782
Total financial liabilities $ 291,353 — 270,498 19,718 290,216
December 31, 2021
Financial assets
Cash and due from banks (1) $ 24,616 24,616 — — 24,616
Interest-earning deposits with banks (1) 209,614 209,452 162 — 209,614
Federal funds sold and securities purchased under resale agreements (1) 66,223 — 66,223 — 66,223
Held-to-maturity debt securities 272,022 16,825 252,717 2,844 272,386
Loans held for sale 7,722 — 6,300 1,629 7,929
Loans, net (2) 868,278 — 63,404 820,559 883,963
Nonmarketable equity securities (cost method) 3,584 — — 3,646 3,646
Total financial assets $ 1,452,059 250,893
388,806 828,678 1,468,377
Financial liabilities
Deposits (3) $ 30,012 — 14,401 15,601 30,002
Short-term borrowings 34,409 — 34,409 — 34,409
Long-term debt (4) 160,660 — 166,682 1,402 168,084
Total financial liabilities $ 225,081 — 215,492 17,003 232,495
(1) Amounts consist of financial instruments for which carrying value approximates fair value.
(2) Excludes lease financing with a carrying amount of $14.7 billion and $14.5 billion at December 31, 2022 and 2021, respectively.
(3) Excludes deposit liabilities with no defined or contractual maturity of $1.3 trillion and $1.5 trillion at December 31, 2022 and 2021, respectively.
(4) Excludes obligations under finance leases of $22 million and $26 million at December 31, 2022 and 2021, respectively.
Wells Fargo & Company 157

Note 16: Securitizations and Variable Interest Entities
Involvement with Variable Interest Entities (VIEs)
In the normal course of business, we enter into various types of
on- and off-balance sheet transactions with special purpose
entities (SPEs), which are corporations, trusts, limited liability
companies or partnerships that are established for a limited
purpose. SPEs are often formed in connection with securitization
transactions whereby financial assets are transferred to an SPE.
SPEs formed in connection with securitization transactions are
generally considered variable interest entities (VIEs). The VIE
may alter the risk profile of the asset by entering into derivative
transactions or obtaining credit support, and issues various
forms of interests in those assets to investors. When we transfer
financial assets from our consolidated balance sheet to a VIE in
connection with a securitization, we typically receive cash and
sometimes other interests in the VIE as proceeds for the assets
we transfer. In certain transactions with VIEs, we may retain the
right to service the transferred assets and repurchase the
transferred assets if the outstanding balance of the assets falls
below the level at which the cost to service the assets exceed the
benefits. In addition, we may purchase the right to service loans
transferred to a VIE by a third party.
In connection with our securitization or other VIE activities,
we have various forms of ongoing involvement with VIEs, which
may include:
• underwriting securities issued by VIEs and subsequently
making markets in those securities;
• providing credit enhancement on securities issued by VIEs
through the use of letters of credit or financial guarantees;
• entering into other derivative contracts with VIEs;
• holding senior or subordinated interests in VIEs;
• acting as servicer or investment manager for VIEs;
• providing administrative or trustee services to VIEs; and
• providing seller financing to VIEs.
Loan Sales and Securitization Activity
We periodically transfer consumer and commercial loans and
other types of financial assets in securitization and whole loan
sale transactions.
MORTGAGE LOANS SOLD TO U.S. GOVERNMENT SPONSORED
ENTITIES AND TRANSACTIONS WITH GINNIE MAE In the normal
course of business we sell originated and purchased residential
and commercial mortgage loans to government-sponsored
entities (GSEs). These loans are generally transferred into
securitizations sponsored by the GSEs, which provide certain
credit guarantees to investors and servicers. We also transfer
mortgage loans into securitization pools pursuant to
Government National Mortgage Association (GNMA) guidelines
which are insured by the Federal Housing Administration (FHA)
or guaranteed by the Department of Veterans Affairs (VA).
Mortgage loans eligible for securitization with the GSEs or
GNMA are considered conforming loans. The GSEs or GNMA
design the structure of these securitizations, sponsor the
involved VIEs, and have power over the activities most significant
to the VIE.
We account for loans transferred in conforming mortgage
loan securitization transactions as sales and do not consolidate
the VIEs as we are not the primary beneficiary. In exchange for
the transfer of loans, we typically receive securities issued by the
VIEs which we sell to third parties for cash or hold for investment
purposes as HTM or AFS securities. We also retain servicing
rights on the transferred loans. As a servicer, we retain the option
to repurchase loans from GNMA loan securitization pools, which
becomes exercisable when three scheduled loan payments
remain unpaid by the borrower. During the years ended
December 31, 2022, 2021 and 2020, we repurchased loans of
$2.2 billion, $4.6 billion, and $30.3 billion, respectively, which
predominantly represented repurchases of government insured
loans. We recorded assets and related liabilities of $743 million
and $107 million at December 31, 2022 and 2021, respectively,
where we did not exercise our option to repurchase eligible loans.
Upon transfers of loans, we also provide indemnification for
losses incurred due to material breaches of contractual
representations and warranties as well as other recourse
arrangements. At December 31, 2022 and 2021, our liability for
these repurchase and recourse arrangements was $167 million
and $173 million, respectively, and the maximum exposure to
loss was $13.8 billion and $13.3 billion at December 31, 2022 and
2021, respectively.
Substantially all residential servicing activity is related to
assets transferred to GSE and GNMA securitizations. See Note 6
(Mortgage Banking Activities) for additional information about
residential and commercial servicing rights, advances and
servicing fees.
NONCONFORMING MORTGAGE LOAN SECURITIZATIONS In the
normal course of business, we sell nonconforming residential and
commercial mortgage loans in securitization transactions that
we design and sponsor. Nonconforming mortgage loan
securitizations do not involve a government credit guarantee,
and accordingly, beneficial interest holders are subject to credit
risk of the underlying assets held by the securitization VIE. We
typically originate the transferred loans, account for the transfers
as sales and do not consolidate the VIE. We also typically retain
the right to service the loans and may hold other beneficial
interests issued by the VIEs, such as debt securities held for
investment purposes. Our servicing role related to
nonconforming commercial mortgage loan securitizations is
limited to primary or master servicer and the most significant
decisions impacting the performance of the VIE are generally
made by the special servicer or the controlling class security
holder. For our residential nonconforming mortgage loan
securitizations accounted for as sales, we either do not hold
variable interests that we consider potentially significant or are
not the primary servicer for a majority of the VIE assets.
WHOLE LOAN SALE TRANSACTIONS We also sell whole loans to
VIEs where we have continuing involvement in the form of
financing. We account for these transfers as sales, and do not
consolidate the VIEs as we do not have the power to direct the
most significant activities of the VIEs.
Table 16.1 presents information about transfers of assets during
the periods presented for which we recorded the transfers as
sales and have continuing involvement with the transferred
assets. In connection with these transfers, we received proceeds
and recorded servicing assets, securities, and loans. Each of these
interests are initially measured at fair value. Servicing rights are
classified as Level 3 measurements, and generally securities are
classified as Level 2. Substantially all transfers were related to
residential mortgage securitizations with the GSEs or GNMA and
resulted in no gain or loss because the loans are measured at fair
value on a recurring basis. Additionally, we may transfer certain
government insured loans that we previously repurchased. These
Wells Fargo & Company 158
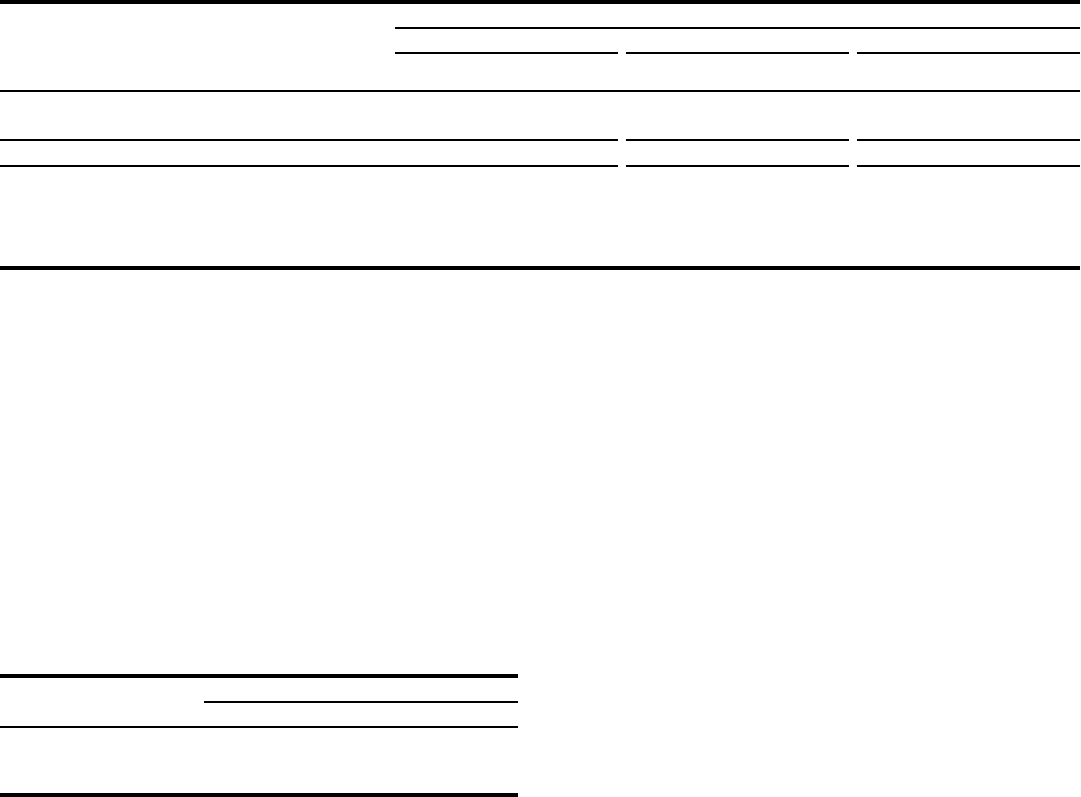
loans are carried at the lower of cost or market, and we recognize
gains on such transfers when the market value is greater than the
carrying value of the loan when it is sold.
Table 16.1: Transfers with Continuing Involvement
Year ended December 31,
2022 2021 2020
(in millions)
Residential
mortgages
Commercial
mortgages
Residential
mortgages
Commercial
mortgages
Residential
mortgages
Commercial
mortgages
Assets sold $ 75,582 13,735 157,063 18,247 177,441 11,744
Proceeds from transfer (1) 75,634 13,963 157,852 18,563 177,478 12,034
Net gains (losses) on sale 52 228 789 316 37
290
Continuing involvement (2):
Servicing rights recognized $ 966 128 1,636 166 1,808 161
Securities recognized (3) 2,062 189 23,188 173 31,567 112
Loans recognized — — 926 — — —
(1) Represents cash proceeds and the fair value of non-cash beneficial interests recognized at securitization settlement.
(2) Represents assets or liabilities recognized at securitization settlement date related to our continuing involvement in the transferred assets.
(3) Represents d ebt securities ob tained at securitization set tlement held for investment purposes t hat are cla ssified as a vailable-for-sale or held-to-maturity, which predominantly relate t o a gency
securities. Excludes t rading debt securities h eld temporarily for market-marking purposes, which are sold to t hird parties a t or shortly after securitization set tlement, of $19.0 b illion, $40.7 b illion,
and $37.6 b illion, during the y ears end ed December 31, 2022, 2021 a nd 2020, respectively.
In the normal course of business, we purchase certain
non-agency securities at initial securitization or subsequently in
the secondary market, which we hold for investment. We also
provide seller financing in the form of loans. During the years
ended December 31, 2022, 2021 and 2020, we received
cash flows of $456 million, $686 million, and $198 million,
respectively, related to principal and interest payments on these
securities and loans, which exclude cash flows related to trading
activities and to the sale of our student loan portfolio.
Table 16.2 presents the key weighted-average assumptions
we used to initially measure residential MSRs recognized during
the periods presented.
Table 16.2: Residential MSRs – Assumptions at Securitization Date
Year ended December 31,
2022 2021 2020
Prepayment rate
(1) 12.4 % 13.7 15.4
Discount rate 8.0 5.9 6.5
Cost to service ($ per loan) $ 110 91 96
(1) Includes a blend of prepayment speeds and expected defaults. Prepayment speeds are
influenced by mortgage interest rates as well as our estimation of drivers of borrower
behavior.
See Note 15 (Fair Values of Assets and Liabilities) and
Note 6 (Mortgage Banking Activities) for additional information
on key assumptions for residential MSRs.
SALE OF STUDENT LOAN PORTFOLIO In the year ended
December 31, 2021, we sold $9.5 billion of student loans,
servicing-released. For the same period, we received $9.9 billion
in proceeds from the sales and recognized $355 million of gains,
which are included in other noninterest income on our
consolidated statement of income. In connection with the sales,
we provided $3.8 billion of collateralized loan financing to a third-
party sponsored VIE, and received cash flows of $3.8 billion which
fully repaid these loans. We do not consolidate the VIE as we do
not have power over the significant activities of the entity.
RESECURITIZATION ACTIVITIES We enter into resecuritization
transactions as part of our trading activities to accommodate the
investment and risk management activities of our customers. In
resecuritization transactions, we transfer trading debt securities
to VIEs in exchange for new beneficial interests that are sold to
third parties at or shortly after securitization settlement. This
activity is performed for customers seeking a specific return or
risk profile. Substantially all of our transactions involve the
resecuritization of conforming mortgage-backed securities
issued by the GSEs or guaranteed by GNMA. We do not
consolidate the resecuritization VIEs as we share in the decision-
making power with third parties and do not hold significant
economic interests in the VIEs other than for market-making
activities. We transferred $17.0 billion, $39.6 billion, and
$77.2 billion of securities to resecuritization VIEs during the
years ended December 31, 2022, 2021 and 2020, respectively.
These amounts are not included in Table 16.1. Related total VIE
assets were $112.0 billion and $117.7 billion at December 31,
2022 and 2021, respectively. As of December 31, 2022 and
2021, we held $793 million and $817 million of securities,
respectively, of which $428 million and $607 million related to
resecuritizations transacted during the years ended
December 31, 2022 and 2021, respectively.
Wells Fargo & Company 159
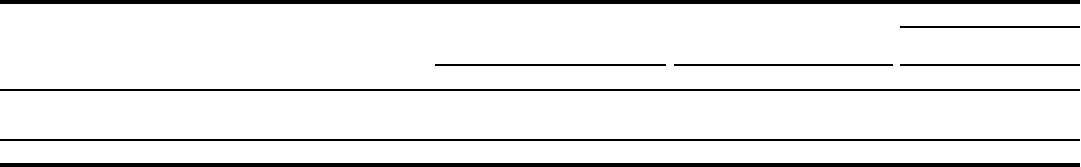
Note 16: Securitizations and Variable Interest Entities (continued)
Sold or Securitized Loans Serviced for Others
Table 16.3 presents information about loans that we sold or
securitized in which we have ongoing involvement as servicer.
Delinquent loans include loans 90 days or more past due and
loans in bankruptcy, regardless of delinquency status. For loans
sold or securitized where servicing is our only form of continuing
involvement, we generally experience a loss only if we were
required to repurchase a delinquent loan or foreclosed asset due
to a breach in representations and warranties associated with our
loan sale or servicing contracts. Table 16.3 excludes mortgage
loans in GSE or GNMA securitizations of $704.5 billion and
$736.8 billion at December 31, 2022 and 2021, respectively.
Delinquent loans and foreclosed assets related to GSEs and
GNMA were $4.6 billion and $10.3 billion at December 31, 2022
and 2021, respectively.
Table 16.3: Sold or Securitized Loans Serviced for Others
Net charge-offs
Total loans
Delinquent loans
and foreclosed assets (1) Year ended December 31,
(in millions) Dec 31, 2022 Dec 31, 2021 Dec 31, 2022 Dec 31, 2021 2022 2021
Commercial $ 67,029 65,655 912 1,617 49 143
Residential 9,201 9,288 501 764 14 22
Total off-balance sheet sold or securitized loans $ 76,230 74,943 1,413 2,381 63 165
(1) Includes $274 million and $403 million of commercial foreclosed assets and $25 million and $29 million of residential foreclosed assets at December 31, 2022 and 2021, respectively.
Transactions with Unconsolidated VIEs
MORTGAGE LOAN SECURITIZATIONS Table 16.4 includes
nonconforming mortgage loan securitizations where we
originate and transfer the loans to the unconsolidated
securitization VIEs that we sponsor. For additional information
about these VIEs, see the “Loan Sales and Securitization Activity”
section within this Note. Nonconforming mortgage loan
securitizations also include commercial mortgage loan
securitizations sponsored by third parties where we did not
originate or transfer the loans but serve as master servicer and
invest in securities that could be potentially significant to the
VIE.
Conforming loan securitization and resecuritization
transactions involving the GSEs and GNMA are excluded from
Table 16.4 because we are not the sponsor or we do not have
power over the activities most significant to the VIEs.
Additionally, due to the nature of the guarantees provided by the
GSEs and the FHA and VA, our credit risk associated with these
VIEs is limited. For additional information about conforming
mortgage loan securitizations and resecuritizations, see the
“Loan Sales and Securitization Activity” and “Resecuritization
Activities” sections within this Note.
COMMERCIAL REAL ESTATE LOANS We may transfer purchased
industrial development bonds and GSE credit enhancements to
VIEs in exchange for beneficial interests. We may also acquire
such beneficial interests in transactions where we do not act as a
transferor. We own all of the beneficial interests and may also
service the underlying mortgages that serve as collateral to the
bonds. The GSEs have the power to direct the servicing and
workout activities of the VIE in the event of a default, therefore
we do not have control over the key decisions of the VIEs.
OTHER VIE STRUCTURES We engage in various forms of
structured finance arrangements with other VIEs, including
asset-backed finance structures and other securitizations
collateralized by asset classes other than mortgages. Collateral
may include rental properties, asset-backed securities, student
loans and mortgage loans. We may participate in structuring or
marketing the arrangements as well as provide financing, service
one or more of the underlying assets, or enter into derivatives
with the VIEs. We may also receive fees for those services. We
are not the primary beneficiary of these structures because we
do not have power to direct the most significant activities of the
VIEs.
Table 16.4 provides a summary of our exposure to the
unconsolidated VIEs described above, which includes
investments in securities, loans, guarantees, liquidity
agreements, commitments and certain derivatives. We exclude
certain transactions with unconsolidated VIEs when our
continuing involvement is temporary or administrative in nature
or insignificant in size.
In Table 16.4, “Total VIE assets” represents the remaining
principal balance of assets held by unconsolidated VIEs using the
most current information available. “Carrying value” is the
amount in our consolidated balance sheet related to our
involvement with the unconsolidated VIEs. “Maximum exposure
to loss” is determined as the carrying value of our investment in
the VIEs excluding the unconditional repurchase options that
have not been exercised, plus the remaining undrawn liquidity
and lending commitments, the notional amount of net written
derivative contracts, and generally the notional amount of, or
stressed loss estimate for, other commitments and guarantees.
Debt, guarantees and other commitments include amounts
related to lending arrangements, liquidity agreements, and
certain loss sharing obligations associated with loans originated,
sold, and serviced under certain GSE programs.
“Maximum exposure to loss” represents estimated loss that
would be incurred under severe, hypothetical circumstances, for
which we believe the possibility is extremely remote, such as
where the value of our interests and any associated collateral
declines to zero, without any consideration of recovery or offset
from any economic hedges. Accordingly, this disclosure is not an
indication of expected loss.
Wells Fargo & Company 160
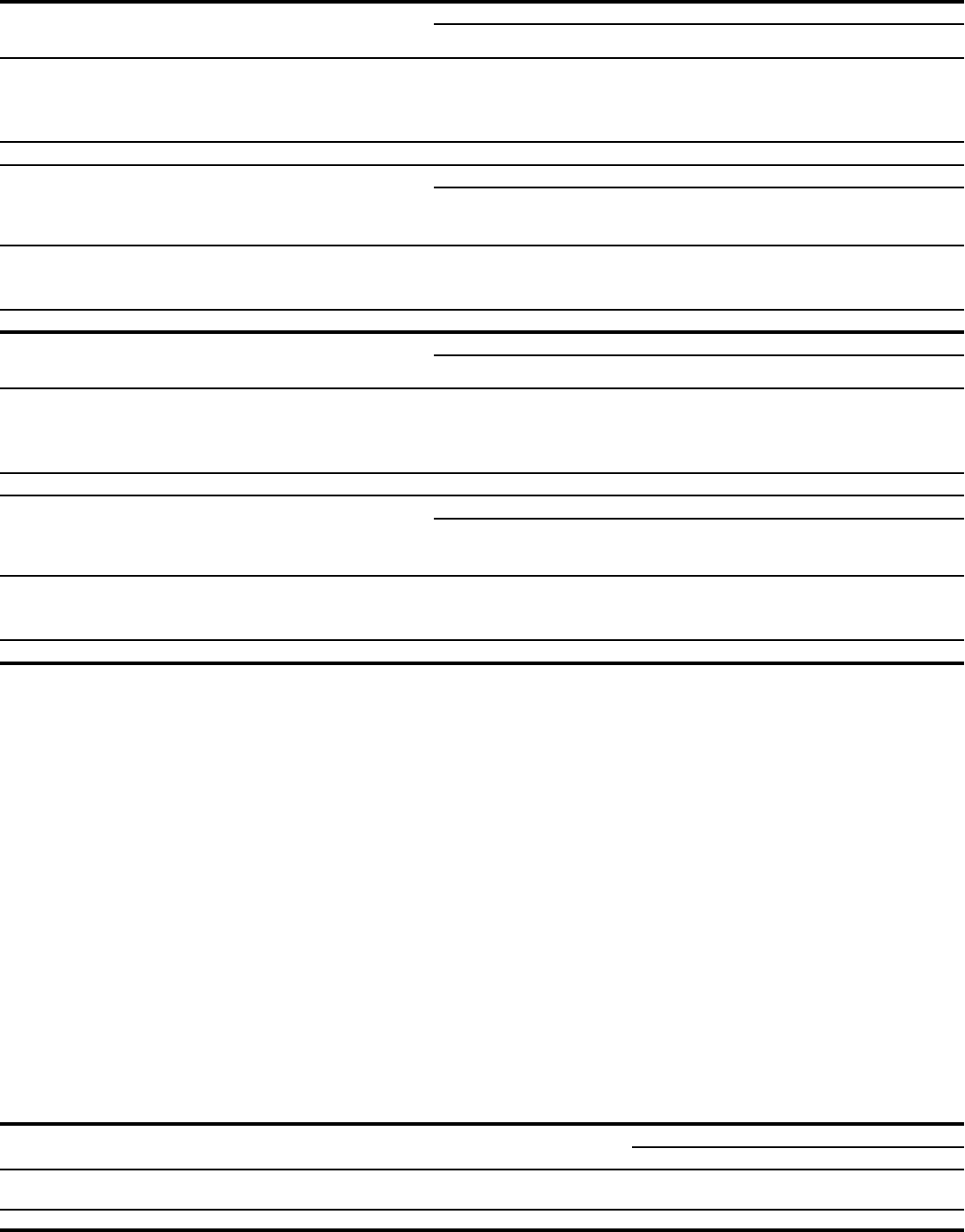
Table 16.4: Unconsolidated VIEs
Carrying value – asset (liability)
(in millions)
Total
VIE assets Loans
Debt
securities (1)
Equity
securities
All other
assets (2)
Debt and other
liabilities Net assets
December 31, 2022
Nonconforming mortgage loan securitizations
$ 154,464 — 2,420 — 617 (13) 3,024
Commercial real estate loans 5,627 5,611 — — 16 — 5,627
Other 2,174 292 1 43 21 — 357
Total $ 162,265 5,903 2,421 43 654 (13) 9,008
Maximum exposure to loss
Loans
Debt
securities (1)
Equity
securities
All other
assets (2)
Debt,
guarantees,
and other
commitments
Total
exposure
Nonconforming mortgage loan securitizations
$ — 2,420 — 617 13 3,050
Commercial real estate loans 5,611 — — 16 705 6,332
Other 292 1 43 21 228 585
Total $ 5,903 2,421 43 654 946 9,967
Carrying value – asset (liability)
(in millions)
Total
VIE assets Loans
Debt
securities (1)
Equity
securities
All other
assets (2)
Debt and other
liabilities Net assets
December 31, 2021
Nonconforming mortgage loan securitizations $ 146,482 — 2,620 — 694 — 3,314
Commercial real estate loans 5,489 5,481 — — 8 — 5,489
Other 3,196 531 3 62 49 (1) 644
Total $ 155,167 6,012 2,623 62 751 (1) 9,447
Maximum exposure to loss
Loans
Debt
securities (1)
Equity
securities
All other
assets (2)
Debt,
guarantees,
and other
commitments
Total
exposure
Nonconforming mortgage loan securitizations $ — 2,620
— 694 27 3,341
Commercial real estate loans 5,481 — — 8 710 6,199
Other 531 3 62 49 229 874
T
otal $ 6,012 2,623 62 751 966 10,414
(1) Includes $172 million and $352 million of securities classified as trading at December 31, 2022 and 2021, respectively.
(2) All other assets includes mortgage servicing rights, derivative assets, and other assets (predominantly servicing advances).
INVOLVEMENT WITH TAX CREDIT VIES In addition to the
unconsolidated VIEs in Table 16.4, we may invest in or provide
funding to affordable housing, renewable energy or similar
projects that are designed to generate a return primarily through
the realization of federal tax credits and other tax benefits. The
projects are typically managed by third-party sponsors who have
the power over the VIE’s assets, therefore, we do not consolidate
the VIEs. The carrying value of our equity investments in tax
credit VIEs was $18.7 billion and $17.0 billion at December 31,
2022 and 2021, respectively. We also had loans to tax credit VIEs
with a carrying value of $2.0 billion and $1.9 billion at
December 31, 2022 and 2021, respectively.
Our maximum exposure to loss for tax credit VIEs at
December 31, 2022 and 2021, was $28.0 billion and $24.7 billion,
respectively. Our maximum exposure to loss included total
unfunded equity and lending commitments of $7.3 billion and
$5.6 billion at December 31, 2022 and 2021, respectively. See
Note 17 (Guarantees and Other Commitments) for additional
information about unfunded capital commitments.
Our affordable housing equity investments qualify for the
low-income housing tax credit (LIHTC). For these investments
we are periodically required to provide additional financial
support during the investment period, or at the discretion of
project sponsors. A liability is recognized for unfunded
commitments that are both legally binding and probable of
funding. These commitments are predominantly funded within
three years of initial investment. Our liability for affordable
housing equity investment unfunded commitments was
$4.8 billion at December 31, 2022, and $4.9 billion at
December 31, 2021, and was included in long-term debt on our
consolidated balance sheet.
Table 16.5 summarizes the amortization of our LIHTC
investments and the related tax credits and other tax benefits
that are recognized in income tax expense/(benefit) on our
consolidated statement of income.
Table 16.5: LIHTC Investments
Year
ended
December
31,
(in millions) 2022
2021 2020
Proportional
amortization of investments $ 1,549
1,545
1,407
Tax credits and other tax benefits (1,834)
(1,783) (1,639)
Net expense/(benefit) recognized within income tax expense $ (285)
(238) (232)
Wells Fargo & Company 161
Note 16: Securitizations and Variable Interest Entities (continued)
Consolidated VIEs
We consolidate VIEs where we are the primary beneficiary. We
are the primary beneficiary of the following structure types:
COMMERCIAL AND INDUSTRIAL LOANS AND LEASES We may
securitize dealer floor plan loans in a revolving master trust
entity. As servicer and residual interest holder, we control the key
decisions of the trust and consolidate the entity. The total VIE
assets held by the master trust represent a majority of the total
VIE assets presented for this category in Table 16.6. In a separate
transaction structure, we may provide the majority of debt and
equity financing to an SPE that engages in lending and leasing to
specific vendors and service the underlying collateral.
OTHER VIE STRUCTURES Other VIEs are predominantly related to
municipal tender option bond (MTOB) transactions. MTOBs are
vehicles to finance the purchase of municipal bonds through the
issuance of short-term debt to investors. Our involvement with
MTOBs includes serving as the residual interest holder, which
provides control over the key decisions of the VIE, as well as the
remarketing agent or liquidity provider related to the debt issued
to investors. We may also securitize nonconforming mortgage
loans, in which our involvement includes servicer of the
underlying assets and holder of subordinate or senior securitie
s
issued by the VIE. During second quarter 2022, we purchased the
outstanding mortgage loans from the VIEs and extinguished the
related debt associated with such securitizations.
Table 16.6 presents a summary of financial assets and liabilities
of our consolidated VIEs. The carrying value represents assets
and liabilities recorded on our consolidated balance sheet. “Total
VIE assets” includes affiliate balances that are eliminated upon
consolidation, and therefore in some instances will differ from
the carrying value of assets.
On our consolidated balance sheet, we separately disclose
(1) the consolidated assets of certain VIEs that can only be used
to settle the liabilities of those VIEs, and (2) the consolidated
liabilities of certain VIEs for which the VIE creditors do not have
recourse to Wells Fargo.
Table 16.6: Transactions with Consolidated VIEs
Carrying value – asset (liability)
(in millions)
Total
VIE assets Loans
Debt
securities
All other
assets (1)
Long-term
debt
All other
liabilities (2)
December 31, 2022
Commercial and industrial loans and leases $ 7,148 4,802 — 190 — (129)
Other 72 — 71 1 — (72)
Total consolidated VIEs $ 7,220 4,802 71 191 — (201)
December 31, 2021
Commercial and industrial loans and leases $ 7,013 4,099 — 231 — (188)
Other 516 377 71 3 (149) (71)
Total consolidated VIEs $ 7,529 4,476 71 234 (149) (259)
(1) All other assets includes cash and due from banks, and other assets.
(2) All other liabilities includes short-term borrowings, and accrued expenses and other liabilities.
Other Transactions
In addition to the transactions included in the previous tables, we
have used wholly-owned trust preferred security VIEs to issue
debt securities or preferred equity exclusively to third-party
investors. As the sole assets of the VIEs are receivables from us,
we do not consolidate the VIEs even though we own all of the
voting equity shares of the VIEs, have fully guaranteed the
obligations of the VIEs, and may have the right to redeem the
third-party securities under certain circumstances. On our
consolidated balance sheet, we reported the debt securities
issued to the VIEs as long-term junior subordinated debt. See
Note 10 (Long-Term Debt) for additional information about the
trust preferred securities.
Wells Fargo & Company 162
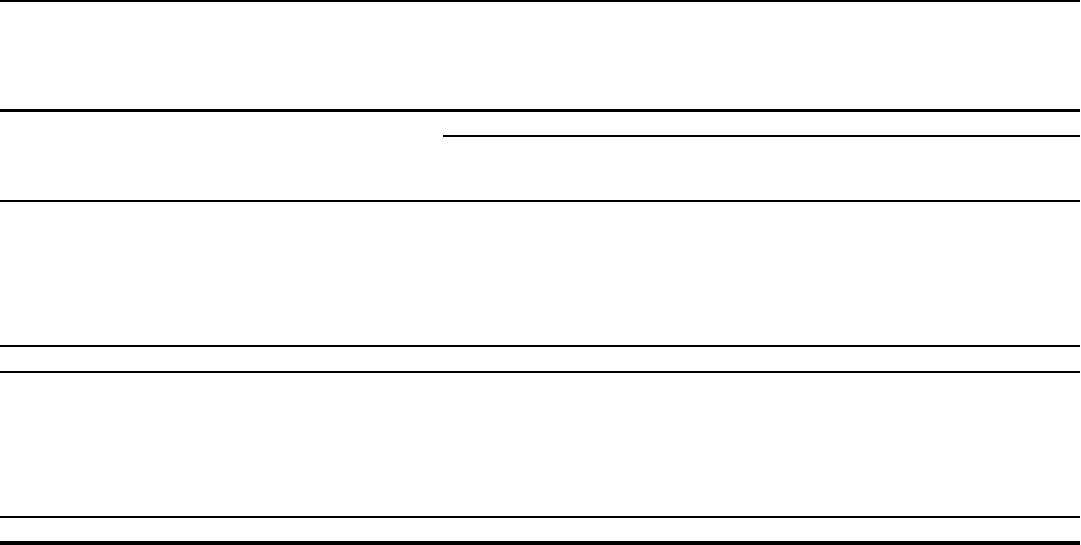
Note 17: Guarantees and Other Commitments
Guarantees are contracts that contingently require us to make
payments to a guaranteed party based on an event or a change i n
an underlying asset, liability, rate or index. Table 17.1 shows
carrying value and maximum exposure to loss on our guarantees.
Table 17.1: Guarantees – C arrying Va lue a nd Maximum Expo sure to Loss
Maximum exposure to loss
(in millions)
Carrying
value of
obligation
Expires in one
year or less
Expires after
one year
through three
years
Expires after
three years
through five
years
Expires after
five years Total
Non-
investment
grade
December 31, 2022
Standby letters of credit (1) $ 112 14,014 4,694 3,058 53 21,819 7,071
Direct pay letters of credit (1) 13 1,593 2,734 465 5 4,797 1,283
Loans and LHFS sold with recourse (2) 16 322 1,078 3,408 8,906 13,714 11,399
Exchange and clearing house guarantees (3) — 4,623 — — — 4,623 —
Other guarantees and indemnifications (4) — 548 1 10 201 760 515
Total guarantees $ 141 21,100 8,507 6,941 9,165 45,713 20,268
December 31, 2021
Standby letters of credit (1) $ 119 13,816 5,260 1,572 460 21,108 6,939
Direct pay letters of credit (1) 6 1,597 2,137 1,283 4 5,021 1,373
Loans and LHFS sold with recourse (2) 20 71 943 3,610 8,650 13,274 11,268
Exchange and clearing house guarantees (3) — — — — 8,100 8,100 —
Other guarantees and indemnifications (4) — 797 2 12 263 1,074 756
Total guarantees $ 145 16,281 8,342 6,477 17,477 48,577 20,336
(1) Standby and direct pay letters of credit are reported net of syndications and participations.
(2) Represents recourse provided, predominantly to the GSEs, on loans sold under various programs and arrangements.
(3) In 2022, we changed our presentation for maximum exposure to loss for these guarantees. As the agreements that include these guarantees automatically renew annually, we believe presentation of
these amounts within the expires in one year or less category better aligns with the committed term.
(4) Includes indemnifications provided to certain third-party clearing agents. Estimated maximum exposure to loss was $157 million and $216 million with related collateral of $1.3 billion and $2.3 billion
as of December 31, 2022 and 2021, respectively.
Maximum exposure to loss represents the estimated loss
that would be incurred under an assumed hypothetical
circumstance, despite what we believe is a remote possibility,
where the value of our interests and any associated collateral
declines to zero. Maximum exposure to loss estimates in
Table 17.1 do not reflect economic hedges or collateral we could
use to offset or recover losses we may incur under our guarantee
agreements. Accordingly, these amounts are not an indication of
expected loss. We believe the carrying value is more
representative of our current exposure to loss than maximum
exposure to loss. The carrying value represents the fair value of
the guarantee, if any, and also includes an ACL for guarantees, if
applicable. In determining the ACL for guarantees, we consider
the credit risk of the related contingent obligation.
For our guarantees in Table 17.1, non-investment grade
represents those guarantees on which we have a higher risk of
performance under the terms of the guarantee, which is
determined based on an external rating or an internal credit
grade that is below investment grade.
STANDBY LETTERS OF CREDIT We issue standby letters of credit,
which include performance and financial guarantees, for
customers in connection with contracts between our customers
and third parties. Standby letters of credit are conditional lending
commitments where we are obligated to make payment to a
third party on behalf of a customer if the customer fails to meet
their contractual obligations. Total maximum exposure to loss
includes the portion of multipurpose lending facilities for which
we have issued standby letters of credit under the commitments.
DIRECT PAY LETTERS OF CREDIT We issue direct pay letters of
credit to serve as credit enhancements for certain bond
issuances. Beneficiaries (bond trustees) may draw upon these
instruments to make scheduled principal and interest payments,
redeem all outstanding bonds because a default event has
occurred, or for other reasons as permitted by the agreement.
WRITTEN OPTIONS We enter into written foreign currency
options and over-the-counter written equity put options that are
derivative contracts that have the characteristics of a guarantee.
Written put options give the counterparty the right to sell to us
an underlying instrument held by the counterparty at a specified
price by a specified date. While these derivative transactions
expose us to risk if the option is exercised, we manage this risk by
entering into offsetting trades or by taking short positions in the
underlying instrument. We offset market risk related to options
written to customers with cash securities or other offsetting
derivative transactions. Additionally, for certain of these
contracts, we require the counterparty to pledge the underlying
instrument as collateral for the transaction. Our ultimate
obligation under written options is based on future market
conditions and is only quantifiable at settlement. The fair value of
written options represents our view of the probability that we
will be required to perform under the contract. The fair value of
these written options was a liability of $15 million, and an asset
of $280 million at December 31, 2022 and 2021, respectively.
The fair value may be an asset as a result of deferred premiums
on certain option trades. The maximum exposure to loss
represents the notional value of these derivative contracts. At
December 31, 2022, the maximum exposure to loss was
$23.4 billion, with $21.3 billion expiring in three years or less
compared with $17.2 billion and $16.7 billion, respectively, at
December 31, 2021. See Note 14 (Derivatives) for additional
information regarding written derivative contracts.
Wells Fargo & Company 163
Note 17: Guarantees and Other Commitments (continued)
LOANS AND LHFS SOLD WITH RECOURSE In certain sales and
securitizations of loans, including mortgage loans, we provide
recourse to the buyer whereby we are required to indemnify the
buyer for any loss on the loan up to par value plus accrued
interest. We provide recourse, predominantly to GSEs, on loans
sold under various programs and arrangements. Substantially all
of these programs and arrangements require that we share in the
loans’ credit exposure for their remaining life by providing
recourse to the GSE, up to 33.33% of actual losses incurred on a
pro-rata basis in the event of borrower default. Under the
remaining recourse programs and arrangements, if certain
events occur within a specified period of time from transfer date,
we have to provide limited recourse to the buyer to indemnify
them for losses incurred for the remaining life of the loans. The
maximum exposure to loss reported in Table 17.1 represents the
outstanding principal balance of the loans sold or securitized that
are subject to recourse provisions or the maximum losses per the
contractual agreements. However, we believe the likelihood of
loss of the entire balance due to these recourse agreements is
remote, and amounts paid can be recovered in whole or in part
from the sale of collateral. We also provide representation and
warranty guarantees on loans sold under the various recourse
programs and arrangements. Our loss exposure relative to these
guarantees is separately considered and provided for, as
necessary, in determination of our liability for loan repurchases
due to breaches of representation and warranties.
EXCHANGE AND CLEARING HOUSE GUARANTEES We are members
of several securities and derivatives exchanges and clearing
houses, both in the U.S. and in countries outside the U.S., that we
use to clear our trades and those of our customers. It is common
that all members in these organizations are required to
collectively guarantee the performance of other members and of
the organization. Our obligations under the guarantees are
generally a pro-rata share based on either a fixed amount or a
multiple of the guarantee fund we are required to maintain with
these organizations. Some membership rules require members
to assume a pro-rata share of losses resulting from another
member’s default or from non-member default losses after
applying the guarantee fund. We have not recorded a liability for
these arrangements as of the dates presented in Table 17.1
because we believe the likelihood of loss is remote.
OTHER GUARANTEES AND INDEMNIFICATIONS We have
contingent performance arrangements related to various
customer relationships and lease transactions. We are required
to pay the counterparties to these agreements if third parties
default on certain obligations.
Under certain factoring arrangements, we may be required
to purchase trade receivables from third parties, if receivable
debtors default on their payment obligations.
We use certain third-party clearing agents to clear and settle
transactions on behalf of some of our institutional brokerage
customers. We indemnify the clearing agents against loss that
could occur for non-performance by our customers on
transactions that are not sufficiently collateralized. Transactions
subject to the indemnifications may include customer obligations
related to the settlement of margin accounts and short
positions, such as written call options and securities borrowing
transactions.
We enter into other types of indemnification agreements in
the ordinary course of business under which we agree to
indemnify third parties against any damages, losses and
expenses incurred in connection with legal and other proceedings
arising from relationships or transactions with us. These
relationships or transactions include those arising from service as
a director or officer of the Company, underwriting agreements
relating to our securities, acquisition agreements and various
other business transactions or arrangements. Because the extent
of our obligations under these agreements depends entirely
upon the occurrence of future events, we are unable to
determine our potential future liability under these agreements.
We do, however, record a liability for residential mortgage loans
that we expect to repurchase pursuant to various
representations and warranties.
MERCHANT PROCESSING SERVICES We provide debit and credit
card transaction processing services through payment networks
directly for merchants and as a sponsor for merchant processing
servicers, including our joint venture with a third party that is
accounted for as an equity method investment. In our role as the
merchant acquiring bank, we have a potential obligation in
connection with payment and delivery disputes between the
merchant and the cardholder that are resolved in favor of the
cardholder, referred to as a charge-back transaction. If we are
unable to collect the amounts from the merchant, we incur a loss
for the refund to the cardholder. We are secondarily obligated to
make a refund for transactions involving sponsored merchant
processing servicers. We generally have a low likelihood of loss in
connection with our merchant processing services because most
products and services are delivered when purchased and
amounts are generally refunded when items are returned to the
merchant. In addition, we may reduce our risk in connection with
these transactions by withholding future payments and requiring
cash or other collateral. We estimate our potential maximum
exposure to be the total merchant transaction volume processed
in the preceding four months, which is generally the lifecycle for a
charge-back transaction. As of December 31, 2022, our potential
maximum exposure was approximately $759.6 billion, and
related losses, including those from our joint venture entity, were
insignificant.
GUARANTEES OF SUBSIDIARIES In the normal course of business,
the Parent may provide counterparties with guarantees related
to its subsidiaries’ obligations. These obligations are included in
the Company’s consolidated balance sheet or are reflected as
off-balance sheet commitments, and therefore, the Parent has
not recognized a separate liability for these guarantees. The
Parent fully and unconditionally guarantees the payment of
principal, interest, and any other amounts that may be due on
securities that its 100% owned finance subsidiary, Wells Fargo
Finance LLC, may issue. These securities are not guaranteed by
any other subsidiary of the Parent. The guaranteed liabilities
were $948 million and $1.2 billion at December 31, 2022 and
2021, respectively. These guarantees rank on parity with all of
the Parent’s other unsecured and unsubordinated indebtedness.
The assets of the Parent consist primarily of equity in its
subsidiaries, and the Parent is a separate and distinct legal entity
from its subsidiaries. As a result, the Parent’s ability to address
claims of holders of these debt securities against the Parent
under the guarantee depends on the Parent’s receipt of
dividends, loan payments and other funds from its subsidiaries. If
any of the Parent’s subsidiaries becomes insolvent, the direct
creditors of that subsidiary will have a prior claim on that
subsidiary’s assets. The rights of the Parent and the rights of the
Parent’s creditors will be subject to that prior claim unless the
Parent is also a direct creditor of that subsidiary. For additional
information regarding other restrictions on the Parent’s ability to
receive dividends, loan payments and other funds from its
Wells Fargo & Company 164
subsidiaries, see Note 25 (Regulatory Capital Requirements and
Other Restrictions.
OTHER COMMITMENTS To meet the financing needs of our
customers, we may enter into commitments to purchase debt
and equity securities to provide capital for their funding, liquidity
or other future needs. As of December 31, 2022 and 2021, we
had commitments to purchase debt securities of $100 million
and $18 million and commitments to purchase equity securities
of $3.8 billion and $2.4 billion, respectively.
As part of maintaining our memberships in certain clearing
organizations, we are required to stand ready to provide liquidity
to sustain market clearing activity in the event unforeseen
events occur or are deemed likely to occur. Certain of these
obligations are guarantees of other members’ performance and
accordingly are included in Table 17.1 in Other guarantees and
indemnifications.
We have commitments to enter into resale and securities
borrowing agreements as well as repurchase and securities
lending agreements with certain counterparties, including central
clearing organizations. The amount of our unfunded contractual
commitments for resale and securities borrowing agreements
was $19.9 billion and $11.0 billion as of December 31, 2022 and
2021, respectively. The amount of our unfunded contractual
commitments for repurchase and securities lending agreements
was $1.6 billion and $1.3 billion as of December 31, 2022 and
2021, respectively.
Given the nature of these commitments, they are excluded
from Table 5.4 (Unfunded Credit Commitments) in Note 5
(Loans and Related Allowance for Credit Losses).
Wells Fargo & Company 165
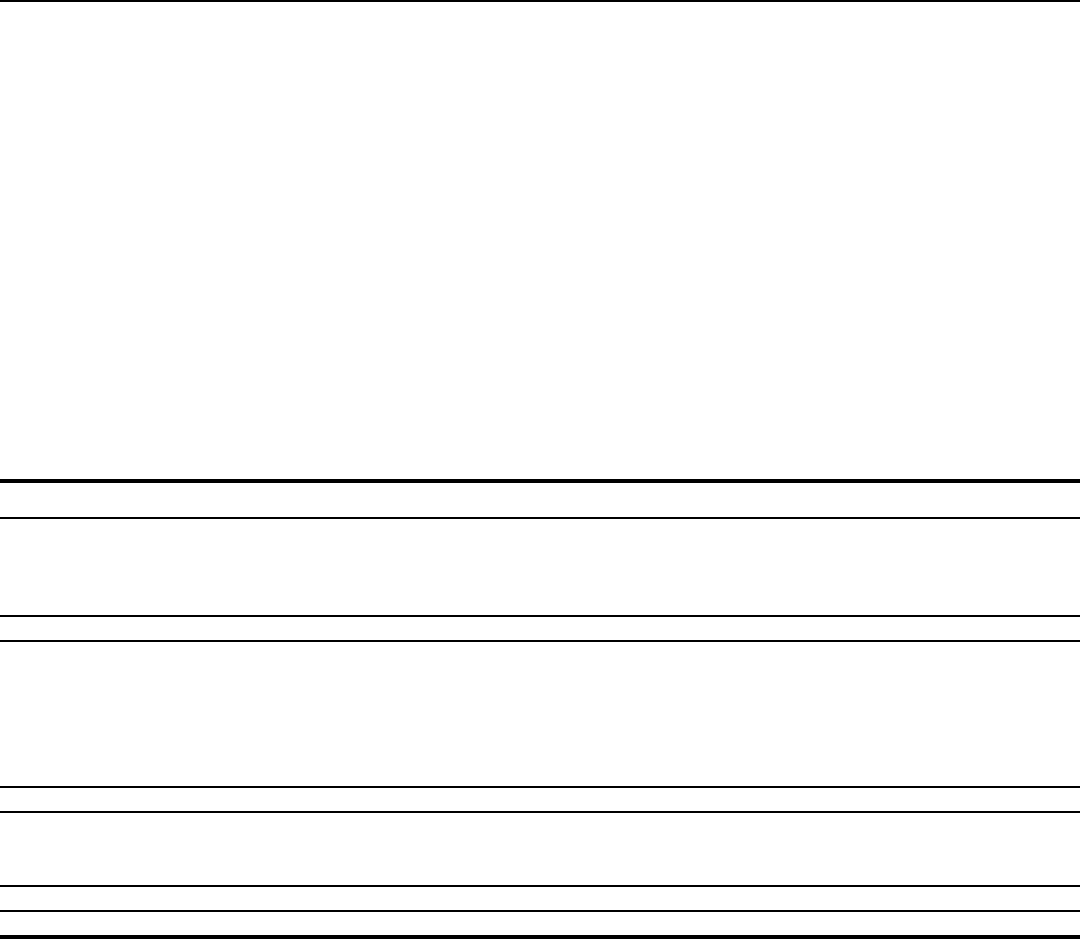
Note 18: Pledged Assets and Collateral
Pledged Assets
Table 18.1 provides the carrying amount of on-balance sheet
pledged assets as well as the fair value of other pledged collateral
not recognized on our consolidated balance sheet, which we have
received from third parties, have the right to repledge and have
repledged. These amounts include assets pledged in transactions
accounted for as secured borrowings, which are presented
parenthetically on our consolidated balance sheet.
TRADING RELATED ACTIVITY Our trading businesses may pledge
debt and equity securities in connection with securities sold
under agreements to repurchase (repurchase agreements) and
securities lending arrangements. The collateral that we pledge
related to our trading activities may include our own collateral as
well as collateral that we have received from third parties and
have the right to repledge. All of the collateral we pledge related
to trading activity is eligible to be repledged or sold by the
secured party.
NON-TRADING RELATED ACTIVITY As part of our liquidity
management strategy, we may pledge loans, debt securities, and
other financial assets to secure trust and public deposits,
borrowings and letters of credit from Federal Home Loan Banks
(FHLBs) and the Board of Governors of the Federal Reserve
System (FRB) and for other purposes as required or permitted by
law or insurance statutory requirements. Substantially all of the
non-trading activity pledged collateral is not eligible to be
repledged or sold by the secured party.
VIE RELATED We pledge assets in connection with various types
of transactions entered into with VIEs. These pledged assets can
only be used to settle the liabilities of those entities.
We also have loans recorded on our consolidated balance
sheet which represent certain delinquent loans that are eligible
for repurchase from GNMA loan securitizations. See Note 16
(Securitizations and Variable Interest Entities) for additional
information on consolidated VIE assets.
Table 18.1: Pledged Assets
(in millions)
Dec 31,
2022
Dec 31,
2021
Related to trading activities:
Off-balance sheet repledged third-party owned debt and equity securities $ 38,191 31,087
Trading debt securities and other 28,284 14,216
Equity securities 1,477 984
Total pledged assets related to trading activities 67,952 46,287
Related to non-trading activities:
Loans 344,000 288,698
Debt securities:
Available-for-sale 50,538 65,198
Held-to-maturity 17,477 13,843
Equity securities 141 1,600
Total pledged assets related to non-trading activities 412,156 369,339
Related to VIEs:
Consolidated VIE assets 5,064 4,781
Loans eligible for repurchase from GNMA securitizations 749 109
Total pledged assets related to VIEs 5,813 4,890
Total pledged assets $ 485,921 420,516
Securities and Other Collateralized Financing Activities
We enter into resale and repurchase agreements and securities
borrowing and lending agreements (collectively, “securities
financing activities”) typically to finance trading positions
(including securities and derivatives), acquire securities to c over
short trading positions, accommodate customers’ financing
needs, and settle other securities obligations. These activitie s are
conducted through our broker-dealer subsidiaries and, to a less er
extent, through other bank entities. Our securities financing
activities primarily involve high-quality, liquid securities such as
U.S. Treasury securities and government agency securities and,
to a lesser extent, less liquid securities, including equity
securities, corporate bonds and asset-backed securities. We
account for these transactions as collateralized financings in
which we typically receive or pledge securities as collateral. We
believe these financing transactions generally do not have
material credit risk given the collateral provided and the rela ted
monitoring processes. We also enter into resale agreements
involving collateral other than securities, such as loans, as part of
our commercial lending business activities.
OFFSETTING OF SECURITIES AND OTHER COLLATERALIZED
FINANCING ACTIVITIES Table 18.2 presents resale and repurchase
agreements subject to master repurchase agreements (MRA)
and securities borrowing and lending agreements subject to
master securities lending agreements (MSLA). Where legally
enforceable, these master netting arrangements give the ability,
in the event of default by the counterparty, to liquidate securities
held as collateral and to offset receivables and payables with the
same counterparty. Collateralized financings, and those with a
single counterparty, are presented net on our consolidated
balance sheet, provided certain criteria are met that permit
balance sheet netting. The majority of transactions subject to
these agreements do not meet those criteria and thus are not
eligible for balance sheet netting.
Collateral we pledged consists of non-cash instruments,
such as securities or loans, and is not netted on our consolidated
Wells Fargo & Company 166
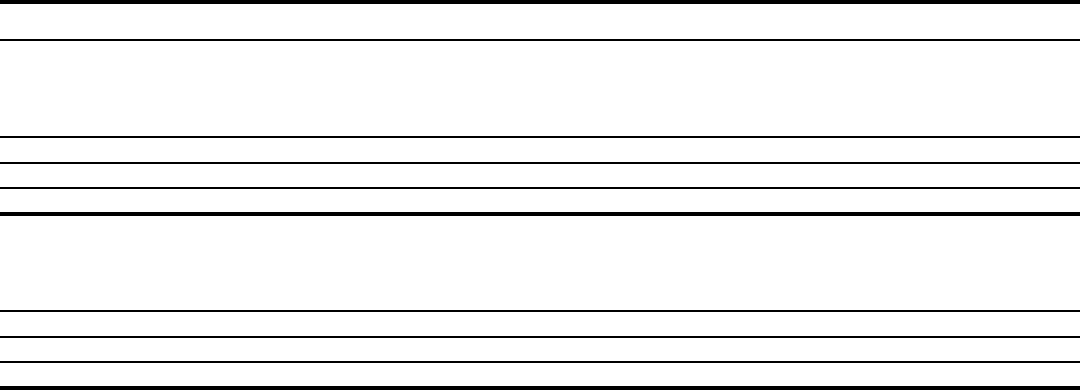
balance sheet against the related liability. Collateral we rece ived
includes securities or loans and is not recognized on our
consolidated balance sheet. Collateral pledged or received may
be increased or decreased over time to maintain certain
contractual thresholds, as the assets underlying each
arrangement fluctuate in value. Generally, these agreements
require collateral to exceed the asset or liability recognized on
the balance sheet. The following table includes the amount of
collateral pledged or received related to exposures subject to
enforceable MRAs or MSLAs. While these agreements are
typically over-collateralized, U.S. GAAP requires disclosure i n this
table to limit the reported amount of such collateral to the
amount of the related recognized asset or liability for each
counterparty.
In addition to the amounts included in Table 18.2 , we also
have balance sheet netting related to derivatives that is discl osed
in Note 14 (Derivatives).
Table 18.2: Offsetting – Securities and Other Collateralized Financing Activities
(in millions)
Dec 31,
2022
Dec 31,
2021
Assets:
Resale and securities borrowing agreements
Gross amounts recognized $
114,729
103,140
Gross amounts offset in consolidated balance sheet (1) (24,464) (14,074)
Net amounts in consolidated balance sheet (2) 90,265 89,066
Collateral not recognized in consolidated balance sheet
(3) (89,592) (88,330)
Net amount (4) $
673
736
Liabilities:
Repurchase and securities lending agreements
Gross amounts recognized $
55,054
35,043
Gross amounts offset in consolidated balance sheet
(1) (24,464) (14,074)
Net amounts in consolidated balance sheet
(5) 30,590 20,969
Collateral pledged but not netted in consolidated balance sheet (6) (30,383) (20,820)
Net amount (4) $
207
149
(1) Represents recognized amount of resale and repurchase agreements with counterparties subject to enforceable MRAs that have been offset in our consolidated balance sheet.
(2) Includes $68.0 billion and $66.2 billion classified on our consolidated balance sheet in federal funds sold and securities purchased under resale agreements at December 31, 2022 and 2021,
respectively. Also includes $22.3 billion and $22.9 billion classified on our consolidated balance sheet in loans at December 31, 2022 and 2021, respectively.
(3) Represents the fair value of collateral we have received under enforceable MRAs or MSLAs, limited in the table above to the amount of the recognized asset due from each counterparty. At
December 31, 2022 and 2021, we have received total collateral with a fair value of $136.6 billion and $124.4 billion, respectively, all of which we have the right to sell or repledge. These amounts
include securities we have sold or repledged to others with a fair value of $59.1 billion and $28.8 billion at December 31, 2022 and 2021, respectively.
(4) Represents the amount of our exposure (assets) or obligation (liabilities) that is not collateralized and/or is not subject to an enforceable MRA or MSLA.
(5) Amount is classified in short-term borrowings on our consolidated balance sheet.
(6) Represents the fair value of collateral we have pledged, related to enforceable MRAs or MSLAs, limited in the table above to the amount of the recognized liability owed to each counterparty. At
December 31, 2022 and 2021, we have pledged total collateral with a fair value of $56.3 billion and $35.9 billion, respectively, substantially all of which may be sold or repledged by the counterparty.
REPURCHASE AND S ECURITIES LENDING AGREEMENTS Securities
sold under repurchase agreements and securities lending
arrangements are effectively short-term collateralized
borrowings. In these transactions, we receive cash in exchange
for transferring securities as collateral and recognize an
obligation to reacquire the securities for cash at the transact ion’s
maturity. These types of transactions create risks, including
(1) the counterparty may fail to return the securities at maturity ,
(2) the fair value of the securities transferred may decline below
the amount of our obligation to reacquire the securities, and
therefore create an obligation for us to pledge additional
amounts, and (3) the counterparty may accelerate the maturity
on demand, requiring us to reacquire the security prior to
contractual maturity. We attempt to mitigate these risks in
various ways. Our collateral primarily consists of highly liquid
securities. In addition, we underwrite and monitor the financia l
strength of our counterparties, monitor the fair value of
collateral pledged relative to contractually required repurchas e
amounts, and monitor that our collateral is properly returned
through the clearing and settlement process in advance of our
cash repayment. Table 18.3 provides the gross amounts
recognized on our consolidated balance sheet (before the effect s
of offsetting) of our liabilities for repurchase and securitie s
lending agreements disaggregated by underlying collateral type .
Wells Fargo & Company 167
Note 18: Pledged Assets and Collateral (continued)
Table 18.3: Gross Obligations by Underlying Collateral Type
(in millions)
Dec 31,
2022
Dec 31,
2021
Repurchase agreements:
Securities of U.S. Treasury and federal agencies $ 27,857 14,956
Securities of U.S. States and political subdivisions 83 1
Federal agency mortgage-backed securities 8,386 3,432
Non-agency mortgage-backed securities 682 809
Corporate debt securities 6,541 8,899
Asset-backed securities 1,529 358
Equity securities 711 919
Other 300 409
Total repurchases 46,089 29,783
Securities lending arrangements:
Securities of U.S. Treasury and federal agencies 278 33
Federal agency mortgage-backed securities 58 17
Corporate debt securities 206 80
Equity securities (1) 8,356 5,050
Other 67 80
Total securities lending 8,965 5,260
Total repurchases and securities lending $ 55,054 35,043
(1) Equity securities are generally exchange traded and represent collateral received from third parties that has been repledged. We received the collateral through either margin lending agreements or
contemporaneous securities borrowing transactions with other counterparties.
Table 18.4 provides the contractual maturities of our gross
obligations under repurchase and securities lending agreements.
Table 18.4: Contractual Maturities of Gross Obligations
(in millions)
Overnight/
continuous Up to 30 days 30-90 days >90 days
Total gross
obligation
December 31, 2022
Repurchase agreements $ 36,251 734 2,884 6,220 46,089
Securities lending arrangements 8,965 — — — 8,965
Total repu rchases and secu rities lending (1) $ 45,216 734 2,884 6,220 55,054
December 31, 2021
Repurchase agreements $ 16,452 3,570 4,276 5,485 29,783
Securities lending arrangements 4,810 — — 450 5,260
Total repurchases and securities lending (1) $ 21,262 3,570 4,276 5,935 35,043
(1) Securities lending is executed under agreements that allow either party to terminate the transaction without notice, while repurchase agreements have a term structure to them that technically
matures at a point in time. The overnight/continuous repurchase agreements require election of both parties to roll the trade rather than the election to terminate the arrangement as in securities
lending.
Wells Fargo & Company 168

Note 19: Operating Segments
Our management reporting is organized into four reportable
operating segments: Consumer Banking and Lending;
Commercial Banking; Corporate and Investment Banking; and
Wealth and Investment Management. All other business
activities that are not included in the reportable operating
segments have been included in Corporate. We define our
reportable operating segments by type of product and customer
segment, and their results are based on our management
reporting process. The management reporting process measures
the performance of the reportable operating segments based on
the Company’s management structure, and the results are
regularly reviewed with our Chief Executive Officer and relevant
senior management. The management reporting process is
based on U.S. GAAP and includes specific adjustments, such as
funds transfer pricing for asset/liability management, shared
revenue and expenses, and taxable-equivalent adjustments to
consistently reflect income from taxable and tax-exempt
sources, which allows management to assess performance
consistently across the operating segments.
Consumer Banking and Lending offers diversified financial
products and services for consumers and small businesses with
annual sales generally up to $10 million. These financial products
and services include checking and savings accounts, credit and
debit cards as well as home, auto, personal, and small business
lending.
Commercial Banking provides financial solutions to private,
family owned and certain public companies. Products and
services include banking and credit products across multiple
industry sectors and municipalities, secured lending and lease
products, and treasury management.
Corporate and Investment Banking delivers a suite of capital
markets, banking, and financial products and services to
corporate, commercial real estate, government and institutional
clients globally. Products and services include corporate banking,
investment banking, treasury management, commercial real
estate lending and servicing, equity and fixed income solutions as
well as sales, trading, and research capabilities.
Wealth and Investment Management provides personalized
wealth management, brokerage, financial planning, lending,
private banking, trust and fiduciary products and services to
affluent, high-net worth and ultra-high-net worth clients. We
operate through financial advisors in our brokerage and wealth
offices, consumer bank branches, independent offices, and
digitally through WellsTrade® and Intuitive Investor®.
Corporate includes corporate treasury and enterprise functions,
net of allocations (including funds transfer pricing, capital,
liquidity and certain expenses), in support of the reportable
operating segments as well as our investment portfolio and
affiliated venture capital and private equity businesses. In
addition, Corporate includes all restructuring charges related to
our efficiency initiatives. See Note 20 (Revenue and Expenses)
for additional information on restructuring charges. Corporate
also includes certain lines of business that management has
determined are no longer consistent with the long-term
strategic goals of the Company as well as results for previously
divested businesses.
Basis of Presentation
FUNDS TRANSFER PRICING Corporate treasury manages a funds
transfer pricing methodology that considers interest rate risk,
liquidity risk, and other product characteristics. Operating
segments pay a funding charge for their assets and receive a
funding credit for their deposits, both of which are included in
net interest income. The net impact of the funding charges or
credits is recognized in corporate treasury.
REVENUE AND EXPENSE SHARING When lines of business jointly
serve customers, the line of business that is responsible for
providing the product or service recognizes revenue or expense
with a referral fee paid or an allocation of cost to the other line of
business based on established internal revenue-sharing
agreements.
When a line of business uses a service provided by another
line of business or enterprise function (included in Corporate),
expense is generally allocated based on the cost and use of the
service provided.
TAXABLE-EQUIVALENT ADJUSTMENTS Taxable-equivalent
adjustments related to tax-exempt income on certain loans and
debt securities are included in net interest income, while taxable-
equivalent adjustments related to income tax credits for low-
income housing and renewable energy investments are included
in noninterest income, in each case with corresponding impacts
to income tax expense (benefit). Adjustments are included in
Corporate, Commercial Banking, and Corporate and Investment
Banking and are eliminated to reconcile to the Company’s
consolidated financial results.
Wells Fargo & Company 169
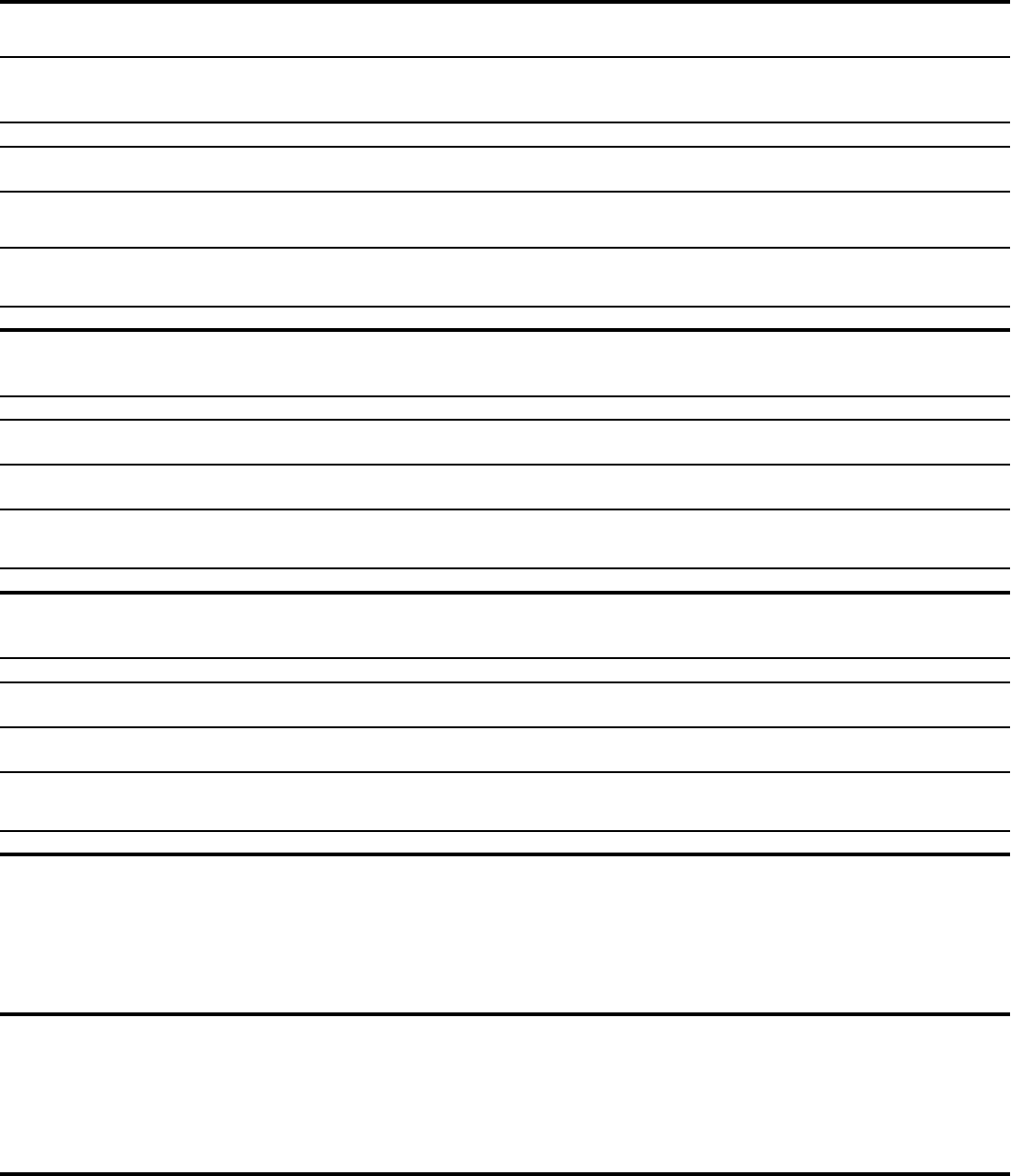
Note 19: Operating Segments (continued)
Table 19.1 presents our results by operating segment.
Table 19.1: Operating Segments
(in millions)
Consumer
Banking and
Lending
Commercial
Banking
Corporate and
Investment
Banking
Wealth and
Investment
Management Corporate
Reconciling
Items (1)
Consolidated
Company
Year ended December 31, 2022
Net interest income (2) $ 27,044 7,289 8,733 3,927 (1,607) (436) 44,950
Noninterest income 8,766 3,631 6,509 10,895 609 (1,575) 28,835
Total revenue 35,810 10,920 15,242 14,822 (998) (2,011) 73,785
Provision for credit losses 2,276 (534) (185) (25) 2 — 1,534
Noninterest expense 26,277 6,058 7,560 11,613 5,774 — 57,282
Income (loss) before income tax expense
(benefit) 7,257 5,396 7,867 3,234 (6,774) (2,011) 14,969
Income tax expense (benefit) 1,816 1,366 1,989 812 (1,885) (2,011) 2,087
Net income (loss) before noncontrolling interests 5,441 4,030 5,878 2,422 (4,889) — 12,882
Less: Net income (loss) from noncontrolling
interests — 12 — — (312) — (300)
Net income (loss) $ 5,441 4,018 5,878 2,422 (4,577) — 13,182
Year ended December 31, 2021
Net interest income (2) $ 22,807 4,960 7,410 2,570 (1,541) (427) 35,779
Noninterest income 12,070 3,589 6,429 11,776 10,036 (1,187) 42,713
Total revenue 34,877 8,549 13,839 14,346 8,495 (1,614) 78,492
Provision for credit losses (1,178) (1,500) (1,439) (95) 57 — (4,155)
Noninterest expense 24,648 5,862 7,200 11,734 4,387 — 53,831
Income (loss) before income tax expense (benefit)
11,407 4,187 8,078 2,707 4,051 (1,614) 28,816
Income tax expense (benefit) 2,852 1,045 2,019 680 596 (1,614) 5,578
Net income before noncontrolling interests 8,555 3,142 6,059 2,027 3,455 — 23,238
Less: Net income (loss) from noncontrolling
interests — 8 (3) — 1,685 — 1,690
Net income $ 8,555 3,134 6,062 2,027 1,770 — 21,548
Year ended December 31, 2020
Net interest income
(2) $ 23,378 6,134 7,509 2,988 441 (494) 39,956
Noninterest income 10,638 3,041 6,419 10,225 4,916 (931) 34,308
Total revenue 34,016 9,175 13,928 13,213 5,357 (1,425) 74,264
Provision for credit losses 5,662 3,744 4,946 249 (472) — 14,129
Noninterest expense 26,976 6,323 7,703 10,912 5,716 — 57,630
Income (loss) before income tax expense (benefit) 1,378 (892) 1,279 2,052 113 (1,425) 2,505
Income tax expense (benefit) 302 (208) 330 514 (670) (1,425) (1,157)
Net income (loss) before noncontrolling interests 1,076 (684) 949 1,538 783 — 3,662
Less: Net income (loss) from noncontrolling
interests — 5 (1) — 281 — 285
Net income (loss) $ 1,076 (689) 950 1,538 502 — 3,377
Year ended December 31, 2022
Loans (average) $ 332,433 206,032 296,984 85,228 9,143 — 929,820
Assets (average) 379,213 227,935 557,396 91,748
638,017 — 1,894,309
Deposits (average) 883,130 186,079 161,720 164,883 28,457 — 1,424,269
Loans (period-end) 340,529 223,529 298,377 84,273 9,163 — 955,871
Assets (period-end) 387,710 250,198 550,177 91,717 601,214 — 1,881,016
Deposits (period-end) 859,695 173,942 157,217 138,760 54,371 — 1,383,985
Year ended December 31, 2021
Loans (average) $ 333,885 181,237 257,036 82,364 9,766 — 864,288
Assets (average) 388,208 198,761 523,344 88,503 743,089 — 1,941,905
Deposits (average) 834,739 197,269 189,176 176,562 40,066 — 1,437,812
Loans (period-end) 326,574 190,348 284,374 84,101 9,997 — 895,394
Assets (period-end) 378,620 210,810 546,549 90,754 721,335 — 1,948,068
Deposits (period-end) 883,674 205,428 168,609 192,548 32,220 — 1,482,479
(1) Taxable-equivalent adjustments related to tax-exempt income on certain loans and debt securities are included in net interest income, while taxable-equivalent adjustments related to income tax
credits for low-income housing and renewable energy investments are included in noninterest income, in each case with corresponding impacts to income tax expense (benefit). Adjustments are
included in Corporate, Commercial Banking, and Corporate and Investment Banking and are eliminated to reconcile to the Company’s consolidated financial results.
(2) Net interest income is interest earned on assets minus the interest paid on liabilities to fund those assets. Segment interest earned includes actual interest income on segment assets as well as a
funding credit for their deposits. Segment interest paid on liabilities includes actual interest expense on segment liabilities as well as a funding charge for their assets.
Wells Fargo & Company 170
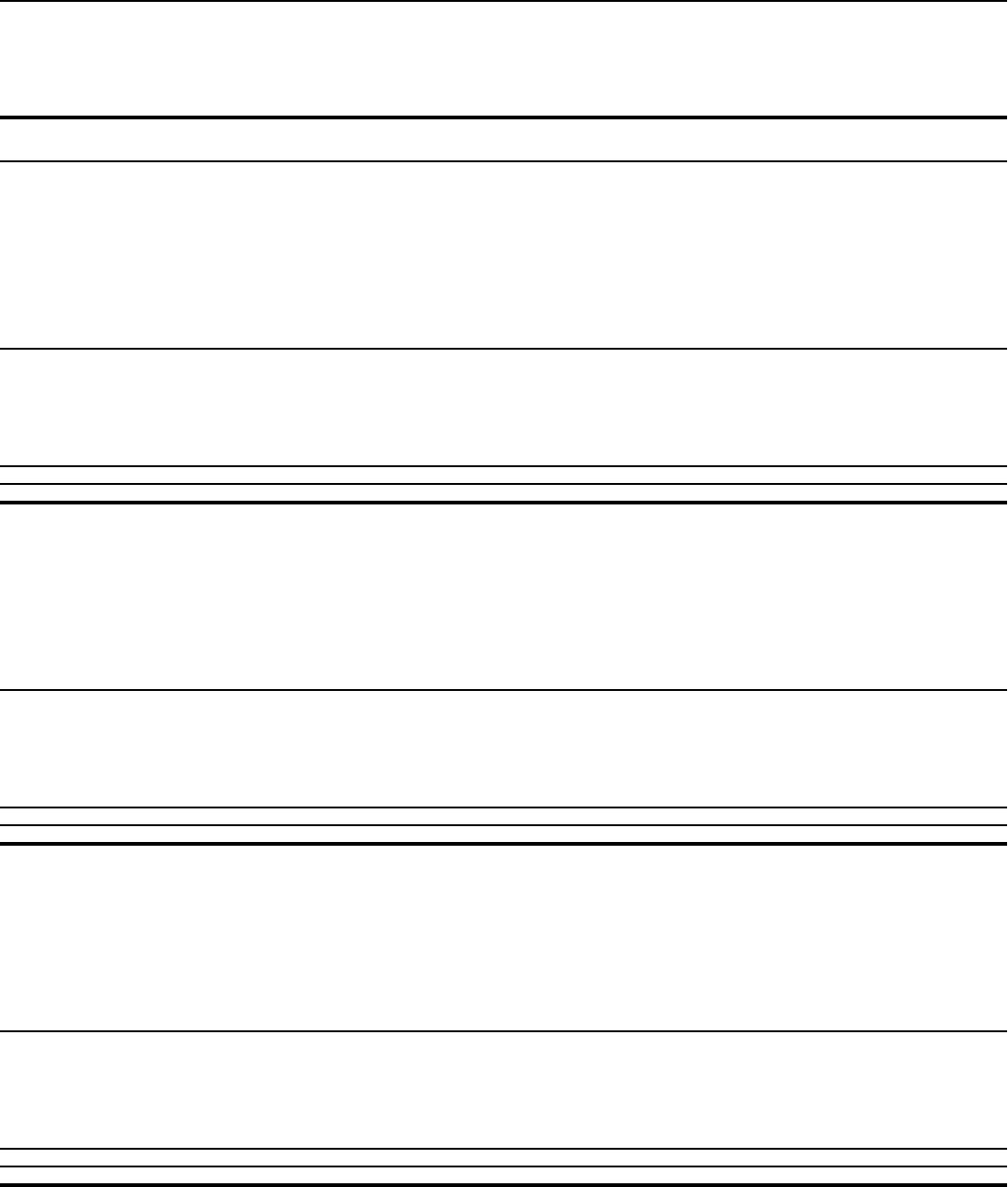
Note 20: Revenue and Expenses
Revenue
Our revenue includes net interest income on financial
instruments and noninterest income. Table 20.1 presents our
revenue by operating segment. For additional description of ou r
operating segments, including additional financial information
and the underlying management accounting process, see
Note 19 (Operating Segments ).
Table 20.1: Revenue by Opera ting S egment
(in millions)
Consumer
Banking and
Lending
Commercial
Banking
Corporate and
Investment
Banking
Wealth and
Investment
Management Corporate
Reconciling
Items (1)
Consolidated
Company
Year ended December 31, 2022
Net interest income (2) $ 27,044 7,289 8,733 3,927 (1,607) (436) 44,950
Noninterest income:
Deposit-related fees 3,093 1,131 1,068 24 — — 5,316
Lending-related fees (2) 129 491 769 8 — — 1,397
Investment advisory and other asset-based fees (3) — 42 107 8,847 8 — 9,004
Commissions and brokerage services fees — — 311 1,931 — — 2,242
Investment banking fees (3) 60 1,492 — (110) — 1,439
Card fees:
Card interchange and network revenue (4) 3,590 224 60 4 — — 3,878
Other card fees (2) 477 — — — — — 477
Total card fees 4,067 224 60 4 — — 4,355
Mortgage banking (2) 1,100 — 296 (12) (1) — 1,383
Net gains (losses) from trading activities (2) — (6) 1,886 58 178 — 2,116
Net gains from debt securities (2) — 5 — — 146 — 151
Net gains (losses) from equity securities (2) (5) 64 (5) (2) (858) — (806)
Lease income (2) — 710 15 — 544 — 1,269
Other (2) 385 910 510 37 702 (1,575) 969
Total noninterest income 8,766 3,631 6,509 10,895 609 (1,575) 28,835
Total revenue $ 35,810 10,920 15,242 14,822 (998) (2,011) 73,785
Year ended December 31, 2021
Net interest income (2) $ 22,807 4,960 7,410 2,570 (1,541) (427) 35,779
Noninterest income:
Deposit-related fees 3,045 1,285 1,112 28 5 — 5,475
Lending-related fees (2) 145 532 761 8 (1) — 1,445
Investment advisory and other asset-based fees (3) — 10 52 9,574 1,375 — 11,011
Commissions and brokerage services fees — — 290 2,010 (1) — 2,299
Investment banking fees (11) 53 2,405 1 (94) — 2,354
Card fees:
Card interchange and network revenue (4) 3,426 196 45 4 — — 3,671
Other card fees (2) 504 — — — — — 504
Total card fees 3,930 196 45 4 — — 4,175
Mortgage banking (2) 4,490 — 480 (12) (2) — 4,956
Net gains (losses) from trading activities (2) — — 272 21 (9) — 284
Net gains from debt securities (2) — 44 — — 509 — 553
Net gains (losses) from equity securities (2) (2) 132 289 79 5,929 — 6,427
Lease income (2) — 682 33 — 281 — 996
Other (2) 473 655 690 63 2,044 (1,187) 2,738
Total noninterest income 12,070 3,589 6,429 11,776 10,036 (1,187) 42,713
Total revenue $ 34,877 8,549 13,839 14,346 8,495 (1,614) 78,492
Year ended December 31, 2020
Net interest income (2) $ 23,378 6,134 7,509 2,988 441 (494) 39,956
Noninterest income:
Deposit-related fees 2,904 1,219 1,062 27 9 — 5,221
Lending-related fees (2) 158 531 684 9 (1) — 1,381
Investment advisory and other asset-based fees (3) — 32 95 8,085 1,651 — 9,863
Commissions and brokerage services fees — — 315 2,078 (9) — 2,384
Investment banking fees (8) 76 1,952 14 (169) — 1,865
Card fees:
Card interchange and network revenue (4) 2,805 170 51 3 1 — 3,030
Other card fees (2) 513 — — — 1 — 514
Total card fees 3,318 170 51 3 2 — 3,544
Mortgage banking (2) 3,224 — 282 (13) — — 3,493
Net gains (losses) from trading activities (2) 1 (4) 1,190 25 (40) — 1,172
Net gains from debt securities (2) 6 — — — 867 — 873
Net gains (losses) from equity securities (2) 10 (147) 212 (101) 691 — 665
Lease income (2) — 646 20 — 579 — 1,245
Other (2) 1,025 518 556 98 1,336 (931) 2,602
Total noninterest income 10,638 3,041 6,419 10,225 4,916 (931) 34,308
Total revenue $ 34,016 9,175 13,928 13,213 5,357 (1,425) 74,264
(1) Taxable-equivalent adjustments related to tax-exempt income on certain loans and debt securities are included in net interest income, while taxable-equivalent adjustments related to income tax
credits for low-income housing and renewable energy investments are included in noninterest income, in each case with corresponding impacts to income tax expense (benefit). Adjustments are
included in Corporate, Commercial Banking, and Corporate and Investment Banking and are eliminated to reconcile to the Company’s consolidated financial results.
(2) These revenue types are related to financial assets and liabilities, including loans, leases, securities and derivatives, with additional details included in other footnotes to our financial statements.
(3) We earned trailing commissions of $989 million, $1.2 billion, and $1.1 billion for the years ended December 31, 2022, 2021 and 2020, respectively.
(4) The cost of credit card rewards and rebates of $2.2 billion, $1.6 billion and $1.3 billion for the years ended December 31, 2022, 2021 and 2020, respectively, are presented net against the related
revenue.
Wells Fargo & Company 171
Note 20: Revenue and Expenses (continued)
We provide services to customers which have related
performance obligations that we complete to recognize revenue.
Our revenue is generally recognized either immediately upon the
completion of our service or over time as we perform services.
Any services performed over time generally require that we
render services each period and therefore we measure our
progress in completing these services based upon the passage of
time.
DEPOSIT-RELATED FEES are earned in connection with depository
accounts for commercial and consumer customers and include
fees for account charges, overdraft services, cash network fees,
wire transfer and other remittance fees, and safe deposit box
fees. Account charges include fees for periodic account
maintenance activities and event-driven services such as stop
payment fees. Our obligation for event-driven services is
satisfied at the time of the event when the service is delivered,
while our obligation for maintenance services is satisfied over the
course of each month. Our obligation for overdraft services is
satisfied at the time of the overdraft. Cash network fees are
earned for processing ATM transactions, and our obligation is
completed upon settlement of ATM transactions. Wire transfer
and other remittance fees consist of fees earned for providing
funds transfer services and issuing cashier’s checks and money
orders. Our obligation is satisfied at the time of the performance
of the funds transfer service or upon issuance of the cashier’s
check or money order. Safe deposit box fees are generally
recognized over time as we provide the services.
INVESTMENT ADVISORY AND OTHER ASSET-BASED FEES are earned
for providing brokerage advisory, asset management and trust
services. These fees were impacted by the sales of our Corporate
Trust Services business and Wells Fargo Asset Management,
which closed in fourth quarter 2021.
Fees from advisory account relationships with brokerage
customers are charged based on a percentage of the market
value of the client’s assets. Services and obligations related to
providing investment advice, active management of client assets,
and assistance with selecting and engaging a third-party advisory
manager are generally satisfied over a month or quarter. Trailing
commissions are earned for selling shares to investors and our
obligation is satisfied at the time shares are sold. However, these
fees are received and recognized over time during the period the
customer owns the shares and we remain the broker of record.
The amount of trailing commissions is variable based on the
length of time the customer holds the shares and on changes in
the value of the underlying assets.
Asset management services include managing and
administering assets, including mutual funds, and institutional
separate accounts. Fees for these services are generally
determined based on a tiered scale relative to the market value
of assets under management (AUM). In addition to AUM, we
have client assets under administration (AUA) that earn various
administrative fees which are generally based on the extent of
the services provided to administer the account. Services with
AUM and AUA-based fees are generally satisfied over time.
Trust services include acting as a trustee or agent for
personal trust and agency assets. Obligations for trust services
are generally satisfied over time; however, obligations for
activities that are transitional in nature are satisfied at the time
of the transaction.
COMMISSIONS AND BROKERAGE SERVICES FEES are earned for
providing brokerage services.
Commissions from transactional accounts with brokerage
customers are earned for executing transactions at the client’s
direction. Our obligation is generally satisfied upon the execution
of the transaction and the fees are based on the size and number
of transactions executed.
Fees earned from other brokerage services include securities
clearance, omnibus and networking fees received from mutual
fund companies in return for providing record keeping and other
administrative services, and annual account maintenance fees
charged to customers. Our obligation is satisfied at the time we
provide the service which is generally at the time of the
transaction.
INVESTMENT BANKING FEES are earned for underwriting debt and
equity securities, arranging syndicated loan transactions and
performing other advisory services. Our obligation for these
services is generally satisfied at closing of the transaction.
CARD FEES include credit and debit card interchange and network
revenue and various card-related fees. Credit and debit card
interchange and network revenue is earned on credit and debit
card transactions conducted through payment networks such as
Visa, MasterCard, and American Express. Our obligation is
satisfied concurrently with the delivery of services on a daily
basis. Other card fees represent late fees, cash advance fees,
balance transfer fees, and annual fees.
Expenses
OPERATING LOSSES We may incur expenses related to various
loss contingencies, such as customer remediation activities. We
establish an accrued liability when a loss event is probable and
the amount of the loss can be reasonably estimated. Our
operating losses of $7.0 billion, $1.6 billion, and $3.5 billion in
2022, 2021 and 2020, respectively, included expenses primarily
related to a variety of historical matters, including litigation,
regulatory, and customer remediation matters. See Note 13
(Legal Actions) for additional information on accruals for legal
actions.
RESTRUCTURING CHARGES The Company began pursuing various
initiatives to reduce expenses and create a more efficient and
streamlined organization in third quarter 2020. Actions from
these initiatives included (i) reorganizing and simplifying business
processes and structures to improve internal operations and the
customer experience, (ii) reducing headcount, (iii) optimizing
third-party spending, including for our technology infrastructure,
and (iv) rationalizing our branch and administrative locations,
which may include consolidations and closures. Substantially all
of the restructuring charges were personnel expenses related to
severance costs associated with headcount reductions with
payments made over time in accordance with our severance plan
as well as payments for other employee benefit costs such as
incentive compensation.
Restructuring charges are recorded as a component of
noninterest expense on our consolidated statement of income.
Changes in estimates represent adjustments to noninterest
expense based on refinements to previously estimated amounts,
which may reflect trends such as higher voluntary employee
attrition as well as changes in business activities.
Table 20.2 provides details on our restructuring charges.
Wells Fargo & Company 172
Table 20.2: Accruals for Restructuring Charges
Year ended December 31,
(in millions) 2022 2021 2020
Balance, beginning of period $ 565 1,214 —
Restructuring charges — 726 1,595
Changes in estimates 5 (650) (96)
Payments and utilization (404) (725) (285)
Balance, end of period $ 166 565 1,214
OTHER EXPENSES Regulatory Charges and Assessments expense,
which is included in other noninterest expense, was $860 million,
$842 million, and $834 million in 2022, 2021 and 2020,
respectively, and primarily consisted of Federal Deposit
Insurance Corporation (FDIC) deposit assessment expense.
Wells Fargo & Company 173
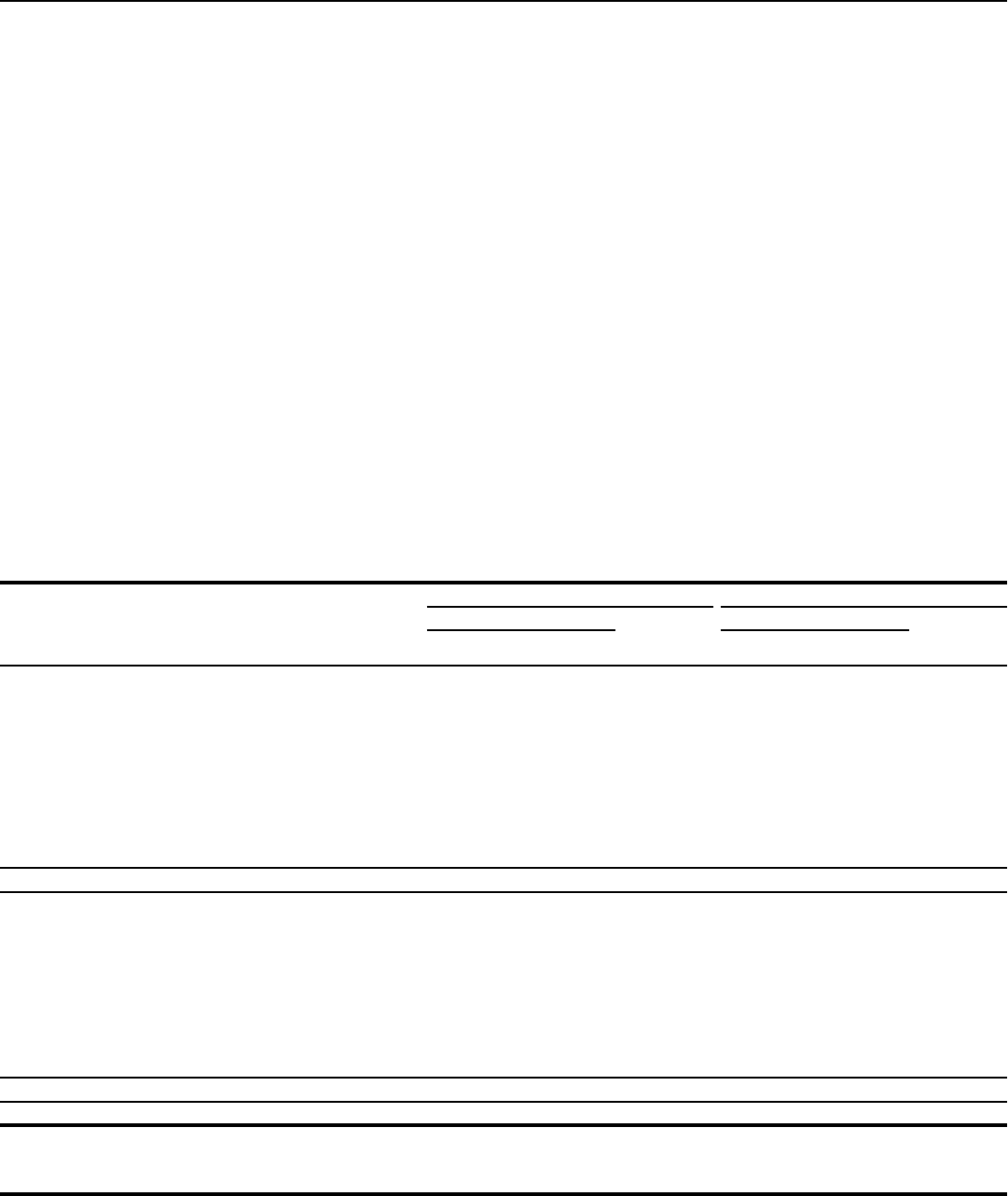
Note 21: Employee Benefits
Pension and Postretirement Plans
We sponsor a frozen noncontributory qualified defined benefit
retirement plan, the Wells Fargo & Company Cash Balance Plan
(Cash Balance Plan), which covers eligible employees of
Wells Fargo. The Cash Balance Plan was frozen on July 1, 2009,
and no new benefits accrue after that date.
Prior to July 1, 2009, eligible employees’ Cash Balance Plan
accounts were allocated a compensation credit based on a
percentage of their certified compensation; the freeze
discontinued the allocation of compensation credits after
June 30, 2009. Investment credits continue to be allocated to
participants’ accounts based on their accumulated balances.
We did not make a contribution to our Cash Balance Plan in
2022. We do not expect that we will be required to make a
contribution to the Cash Balance Plan in 2023. For the
nonqualified pension plans and postretirement benefit plans,
there is no minimum required contribution beyond the amount
needed to fund benefit payments.
We recognize settlement losses for our Cash Balance Plan
based on an assessment of whether lump sum benefit payments
will, in aggregate for the year, exceed the sum of its annual
service and interest cost (threshold). Settlement losses of $221
million and $133 million were recognized during 2022 and 2021,
respectively, representing the pro rata portion of the net loss in
accumulated other comprehensive income (AOCI) based on the
percentage reduction in the Cash Balance Plan’s projected
benefit obligation attributable to 2022 and 2021 lump sum
payments (included in the “Benefits paid” line in Table 21.1).
Additionally, we sponsored the Wells Fargo Canada
Corporation Pension Plan to employees in Canada (Canada
Pension Plan),
a defined benefit retirement plan. In June 2022, an
annuity contract was entered into that effected a full settlement
of this Canada Pension Plan, resulting in a plan settlement of
$29 million and a settlement loss of $5 million.
Our nonqualified defined benefit plans are unfunded and
provide supplemental defined benefit pension benefits to certain
eligible employees. The benefits under these plans were frozen in
prior years.
Other benefits include health care and life insurance benefits
provided to certain retired employees. We reserve the right to
amend, modify or terminate any of these benefits at any time.
The information set forth in the following tables is based on
current actuarial reports using the measurement date of
December 31 for our pension and postretirement benefit plans.
Table 21.1 presents the changes in the benefit obligation
and the fair value of plan assets, the funded status, and the
amounts recognized on our consolidated balance sheet. Changes
in the benefit obligation for the qualified plans were driven by the
amounts of benefits paid and changes in the actuarial loss (gain)
amounts, which are driven by changes in the discount rates at
December 31, 2022 and 2021, respectively.
Table 21.1: Changes in Benefit Obligation and Fair Value of Plan Assets
December 31, 2022 December 31, 2021
Pension benefits Pension benefits
(in millions)
Qualified
Non-
qualified
Other
benefits
Qualified
Non-
qualified
Other
benefits
Change in benefit obligation:
Benefit obligation at beginning of period $ 11,032 501 439 11,956 556 491
Service cost 19 — — 17 — —
Interest cost 348 12 9 296 12 11
Plan participants’ contributions
—
—
39
—
—
40
Actuarial loss (gain)
(2,256)
(76)
(103)
(414)
(18)
(34)
Benefits paid
(966)
(46)
(75)
(818)
(49)
(69)
Settlements, Curtailments, and Amendments
(29)
—
—
(2)
—
—
Foreign exchange impact
(7)
—
—
(3)
—
—
Benefit obligation at end of period
8,141
391
309
11,032
501
439
Change in plan assets:
Fair value of plan assets at beginning of period
11,581
—
550
12,061
—
549
Actual return on plan assets
(1,998)
—
(45)
324
—
25
Employer contribution
16
46
7
15
49
5
Plan participants’ contributions
—
—
39
—
—
40
Benefits paid
(966)
(46)
(75)
(818)
(49)
(69)
Settlement
(29)
—
—
—
—
—
Foreign exchange impact
(4)
—
—
(1)
—
—
Fair value of plan assets at end of period
8,600
—
476
11,581
—
550
Funded status at end of period
$
459
(391)
167
549
(501)
111
Amounts recognized on the consolidated balance sheet at end of period:
Assets $
522
—
181
620
—
133
Liabilities
(63)
(391) (14)
(71)
(501)
(22)
Wells Fargo & Company 174
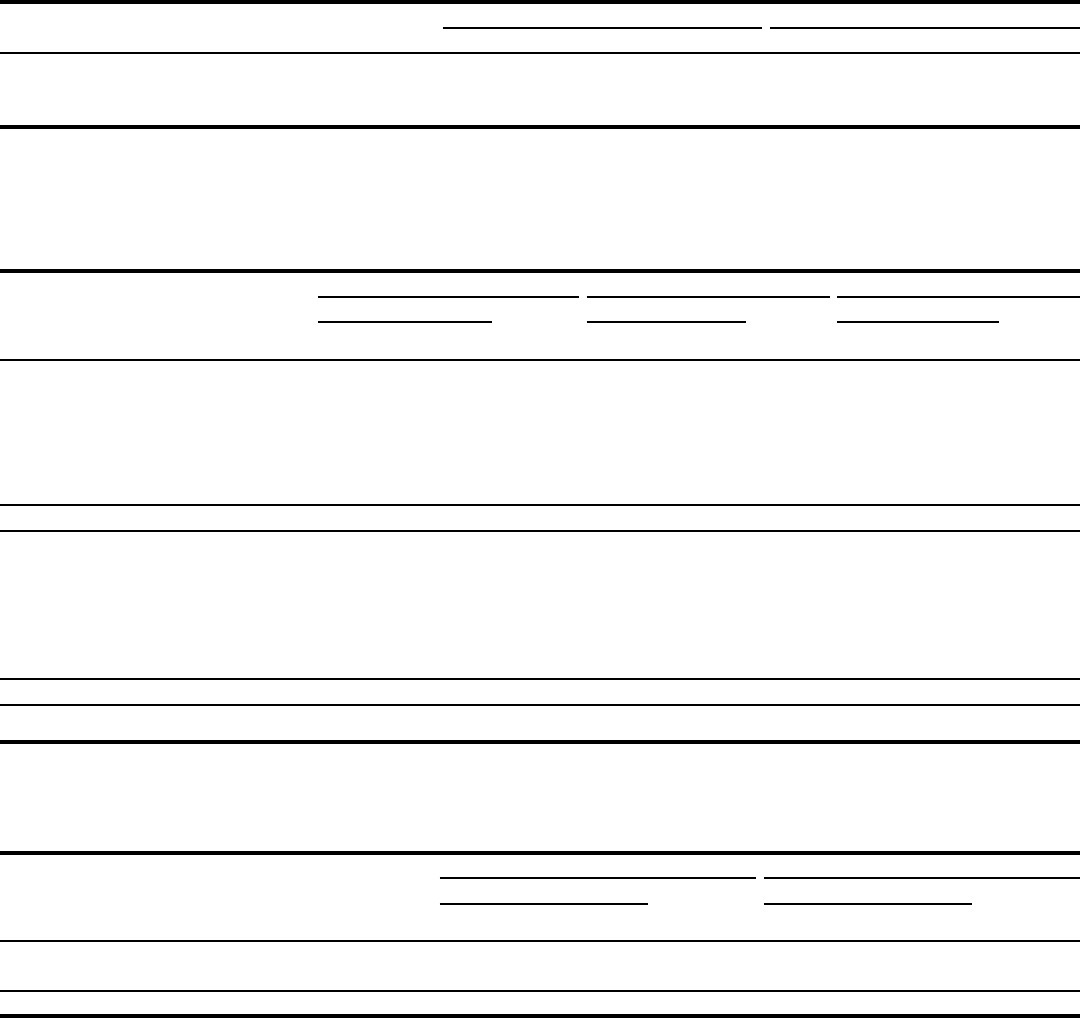
Table 21.2 provides information for pension and
postretirement plans with benefit obligations in excess of plan
assets.
Table 21.2: Plans with Benefit Obligations in Excess of Plan Assets
December 31, 2022 December 31, 2021
(in millions) Pension Benefits Other Benefits Pension Benefits Other Benefits
Projected benefit obligation $ 539 N/A 664 N/A
Accumulated benefit obligation 509 14 631 22
Fair value of plan assets 86 — 91 —
Table 21.3 presents the components of net periodic benefit
cost and OCI. Service cost is reported in personnel expense an d
all other components of net periodic benefit cost are reported in
other noninterest expense on our consolidated statement of
income.
Table 21.3: Net Perio dic Benefit C ost a nd Other C omprehensive Inco me
December 31, 2022 December 31, 2021 December 31, 2020
Pension benefits Pension benefits Pension benefits
(in millions) Qualified
Non-
qualified
Other
benefits Qualified
Non-
qualified
Other
benefits Qualified
Non-
qualified
Other
benefits
Service cost $ 19 — — 17 — — 14 — —
Interest cost 348 12 9 296 12 11 325 16 16
Expected return on plan assets (511) — (22) (598) — (19) (603) — (21)
Amortization of net actuarial loss (gain) 136 11 (22) 140 15 (20) 157 14 (19)
Amortization of prior service cost (credit) 1 — (10) — — (10) — — (10)
Settlement loss 226 1 — 134 2 — 121 3 —
Net periodic benefit cost 219 24 (45) (11) 29 (38) 14 33 (34)
Other changes in plan assets and benefit
obligations recognized in other comprehensive
income:
Net actuarial loss (gain) 253 (76) (36) (142) (18) (40) 517 25 (32)
Amortization of net actuarial gain (loss) (136) (11) 22 (140) (15) 20 (157) (14) 19
Amortization of prior service credit (cost) (1) — 10 — — 10 — — 10
Settlement (loss) (226) (1) — (134) (2) — (121) (3) —
Total recognized in other comprehensive income (110) (88) (4) (416) (35) (10) 239 8 (3)
Total recognized in net periodic benefit cost and
other comprehensive income $ 109 (64) (49) (427) (6) (48) 253 41 (37)
Table 21.4 provides the a mounts recognized in AOCI
(pre-tax).
Table 21.4: Benefits Reco gnized in Accumula ted OCI
December 31, 2022 December 31, 2021
Pension benefits Pension benefits
(in millions)
Qualified
Non-
qualified
Other
benefits
Qualified
Non-
qualified
Other
benefits
Net actuarial loss (gain)
$
2,940
71
(404)
3,049
159
(390)
Net prior service cost (credit)
—
—
(116)
1
—
(126)
Total $
2,940
71
(520)
3,050
159
(516)
Wells Fargo & Company 175
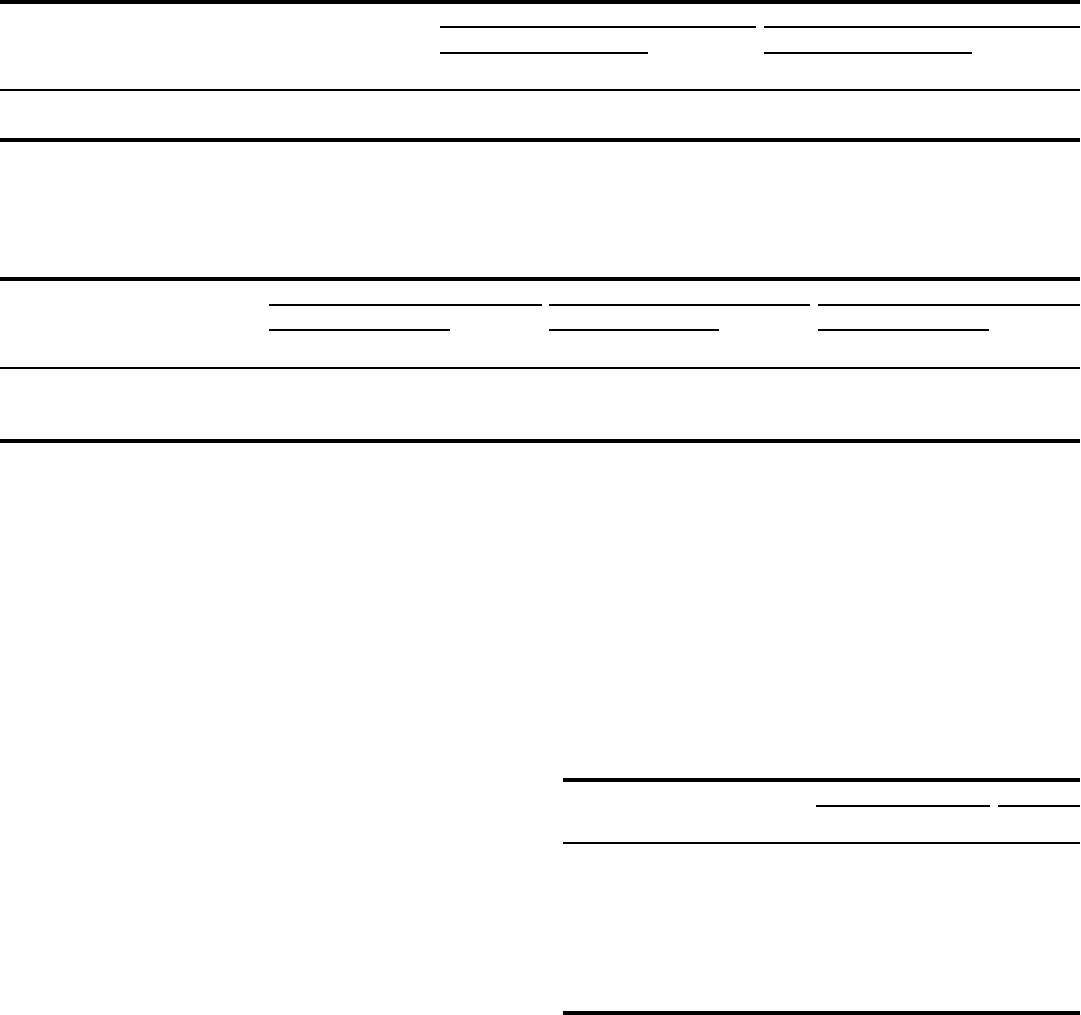
Note 21: Employee Benefits (continued)
Plan Assumptions
For additional information on our pension accounting
assumptions, see Note 1 (Summary of Significant Accounting
Policies). Table 21.5 presents the weighted-average assumptions
used to estimate the projected benefit obligation.
Table 21.5: Weighted-Average Assumptio ns Used to Estimate Pro jected Benefit Ob ligation
December 31, 2022 December 31, 2021
Pension benefits Pension benefits
Qualified
Non-
qualified
Other
benefits Qualified
Non-
qualified
Other
benefits
Discount
rate
5.18
%
5.08
5.12
2.85
2.60
2.71
Interest crediting rate
4.10 3.58 N/A 2.69 1.25 N/A
Table 21.6 presents the weighted-average assumptions
used to determine the net periodic benefit cost, including the
impact of interim re-measurements as applicable.
Table 21.6: Weighted-Average Assumptions Used to Determine Net Periodic Benefit Cost
December 31, 2022 December 31, 2021 December 31, 2020
Pension benefits Pension benefits Pension benefits
Qualified
Non-
qualified
Other
benefits Qualified
Non-
qualified
Other
benefits Qualified
Non-
qualified
Other
benefits
Discount rate 3.93 % 2.34 2.11 2.63 2.32 2.31 2.95 3.12 3.10
Interest crediting rate 3.37 1.51 N/A 2.68 1.08 N/A 2.68 1.46 N/A
Expected return on plan assets 5.35 N/A 4.00 5.17 N/A 3.50 5.74 N/A 4.00
To account for postretirement health care plans, we used
health care cost trend rates to recognize the effect of expecte d
changes in future health care costs due to medical inflation,
utilization changes, new technology, regulatory requirements
and Medicare cost shifting. In determining the end of year
benefit obligation, we assumed an average annual increase of
approximately 13.90% for health care costs in 2023. This rate is
assumed to trend down 0.60%-1.50% per year until the trend
rate reaches an ultimate rate of 4.50% in 2032. The 2022
periodic benefit cost was determined using an initial annual tr end
rate of 7.50%. This rate was assumed to decrease 0.30%-0.40%
per year until the trend rate reached an ultimate rate of 4.50% in
2030.
Investment Strategy and Asset Allocation
We seek to achieve the expected long-term rate of return with a
prudent level of risk, given the benefit obligations of the pension
plans and their funded status. Our overall investment strategy is
designed to provide our Cash Balance Plan with a moderate
amount of long-term growth opportunities while ensuring that
risk is mitigated through diversification across numerous asset
classes and various investment strategies, coupled with an
investment strategy for the fixed income assets that is generally
designed to approximate the interest rate sensitivity of the Cash
Balance Plan’s benefit obligations. The Cash Balance Plan
currently has a target asset allocation mix comprised of the
following ranges: 75%-85% fixed income, 10%-20% equities, and
0%-10% in real estate, private equity and other investments. The
Employee Benefit Review Committee (EBRC), which includes
several members of senior management, formally reviews the
investment risk and performance of our Cash Balance Plan on a
quarterly basis. Annual Plan liability analysis and periodic asset/
liability evaluations are also conducted.
Other benefit plan assets include (1) assets held in a 401(h)
trust, which are invested with a target mix of 50%-60% equities
and 40%-50% fixed income, and (2) assets held in the Retiree
Medical Plan Voluntary Employees’ Beneficiary Association
(VEBA) trust, which are predominantly invested in fixed income
securities and cash. Members of the EBRC formally review the
investment risk and performance of these assets on a quarterly
basis.
Projected Benefit Payments
Future benefits that we expect to pay under the pension and
other benefit plans are presented in Table 21.7.
Table 21.7: Projected Benefit Payments
Pension benefits
(in millions) Qualified
Non-
qualified
Other
benefits
Period ended December 31,
2023 $ 690 43 31
2024 654 42 30
2025 646 40 30
2026 643 38 28
2027 640 37 27
2028-2032 3,052 155 119
Wells Fargo & Company 176
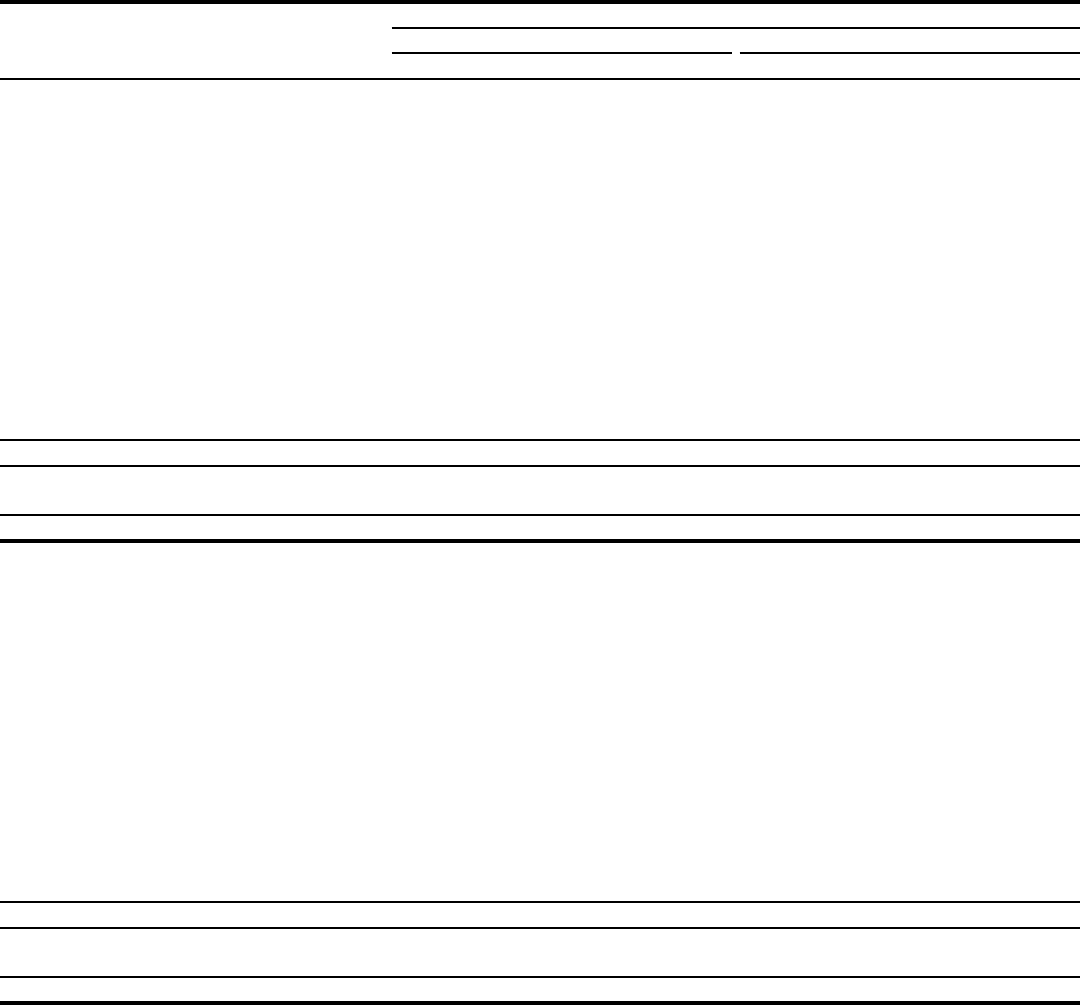
Fair Value of Plan Assets
Table 21.8 presents the classification of the fair value of the
pension plan and other benefit plan assets in the fair value
hierarchy. See Note 15 (Fair Values of Assets and Liabilities) for a
description of the fair value hierarchy.
Table 21.8: Pension and Other Benefit Plan Assets
Carrying value at year end
Pension plan assets Other benefits plan assets
(in millions) Level 1 Level 2 Level 3 Total Level 1 Level 2 Level 3 Total
December 31, 2022
Cash and cash equ ivalents $ 214 4 — 218 41 135 — 176
Long du ration fixed income (1) 1,398 4,919 — 6,317 — — — —
Intermediate (core) fixed income — 227 — 227 — 154 — 154
High-yield fixed income — 91 — 91 — — — —
International fixed income — 84 — 84 — — — —
Domestic large-cap stock s 232 35 — 267 — 60 — 60
Domestic mid-cap stock s 74 40 — 114 — 16 — 16
Domestic small-cap stock s 64 4 — 68 — 9 — 9
Global stocks — 152 — 152 — — — —
International stock s 105 141 — 246 9 19 — 28
Emerging mark et stock s 29 57 — 86 — — — —
Real estate 46 — — 46 — — — —
Hedge fu nds/absolute retu rn — 42 — 42 — — — —
Other 90 23 10 123 6 — 24 30
Plan investments – exclu ding investments at NAV $ 2,252 5,819 10 8,081 56 393 24 473
Investments at NAV (2) 415 —
Net receivables 104
3
Total plan assets $ 8,600 476
December 31, 2021
Cash and cash equivalents $ 2 242 — 244 40 143 — 183
Long duration fixed income (1) 1,562 6,827 1 8,390 — — — —
Intermediate (core) fixed income — 429 — 429 — 193 — 193
High-yield fixed income — 134 — 134 — — — —
International fixed income — 83 — 83 — — — —
Domestic large-cap stocks 378 57 — 435 11 67 — 78
Domestic mid-cap stocks 104 60 — 164 — 20 — 20
Domestic small-cap stocks 94 6 — 100 — 11 — 11
Global stocks — 204 — 204 — — — —
International stocks 139 216 — 355 11 24 — 35
Emerging market stocks 30 96 — 126 — — — —
Real estate 87 28 1 116 — — — —
Hedge funds/absolute return — 54 — 54 — — — —
Other 111 45 9 165 6 — 24 30
Plan investments – excluding investments at NAV $ 2,507 8,481 11 10,999 68 458 24 550
Investments at NAV (2) 533 —
Net receivables 49 —
Total plan assets $ 11,581 550
(1) This category includes a diversified mix of assets, which are being managed in accordance with a duration target of approximately 9 years and 11 years for December 31, 2022 and 2021, respectively,
and an emphasis on corporate credit bonds combined with investments in U.S. Treasury securities and other U.S. agency and non-agency bonds.
(2) Consists of certain investments that are measured at fair value using NAV per share (or its equivalent) as a practical expedient and are excluded from the fair value hierarchy.
Wells Fargo & Company 177
Note 21: Employee Benefits (continued)
Table 21.9 presents the changes in Level 3 pension plan and
other benefit plan assets measured at fair value.
Table 21.9: Fair Value Level 3 Pension and Other Benefit Plan Assets
(in millions)
Balance
beginning
of year
Gains
(losses) (1)
Purchases,
sales and
settlements
(net)
Transfer into/
(out of) Level 3
Balance
end of
year
Period ended December 31, 2022
Pension plan assets $ 11 — — (1) 10
Other benefits plan assets 24 — — — 24
Period ended December 31, 2021
Pension plan assets $ 12 6 (8) 1 11
Other benefits plan assets 24 — — — 24
(1) Represents unrealized and realized gains (losses).
VALUATION METHODOLOGIES Following is a description of the
valuation methodologies used for assets measured at fair value.
Cash and Cash Equivalents – includes investments in
collective investment funds valued at fair value based upon the
fund’s NAV per share held at year-end. The NAV per share is
quoted on a private market that is not active; however, the NAV
per share is based on underlying investments traded on an active
market. This group of assets also includes investments in
registered investment companies valued at the NAV per share
held at year-end and in interest-bearing bank accounts.
Long Duration, Intermediate (Core), High-Yield, and
International Fixed Income – includes investments traded on the
secondary markets; prices are measured by using quoted market
prices for similar securities, pricing models, and discounted cash
flow analyses using significant inputs observable in the market
where available, or a combination of multiple valuation
techniques. This group of assets also includes highly liquid
government securities such as U.S. Treasuries, limited
partnerships valued at the NAV, registered investment
companies, and collective investment funds described above.
Domestic, Global, International and Emerging Market Stocks –
investments in exchange-traded equity securities are valued at
quoted market values. This group of assets also includes
investments in registered investment companies and collective
investment funds described above.
Real Estate –includes investments in exchange-traded equity
securities, registered investment companies, and collective
investment funds described above.
Hedge Funds / Absolute Return – includes investments in
collective investment funds as described above.
Other – insurance contracts that are stated at cash surrender
value. This group of assets also includes investments in
registered investment companies and collective investment
funds described above.
The methods described above may produce a fair value
calculation that may not be indicative of net realizable value or
reflective of future fair values. While we believe our valuation
methods are appropriate and consistent with other market
participants, the use of different methodologies or assumptions
to determine the fair value of certain financial instruments could
result in a different fair value measurement at the reporting date.
Defined Contribution Retirement Plans
We sponsor a qualified defined contribution retirement plan, the
Wells Fargo & Company 401(k) Plan (401(k) Plan). Under the
401(k) Plan, after 1 month of service, eligible employees may
contribute up to 50% of their certified compensation, subject to
statutory limits.
Effective January 2021, we implemented the following
changes to the 401(k) Plan employer contributions: (1) with
some exceptions, employees with one year of service must be
employed in a benefit-eligible position on December 15; (2)
added a new non-discretionary base contribution of 1% of
certified compensation for employees with annual compensation
of less than $75,000; (3) replaced the discretionary profit sha ring
contribution with a discretionary contribution for eligible
employees with annual compensation of less than $150,000; and
(4) revised the matching contribution vesting and timing. Eligible
employees are 100% vested in their base and discretionary
contributions after three years of service. A three-year service
vesting requirement for matching contributions applies to
employees hired after December 31, 2020. Base and matching
contributions are made annually at year-end, and the
discretionary contribution, if awarded, is made no later than t he
due date for the Company’s federal income tax return (includin g
extensions) for the plan year. Additionally, we added installme nt
payment options to the existing lump sum and partial lump sum
distribution options and added optional advisory services.
Prior to January 2021, eligible employees who completed
one year of service were eligible to receive the matching
contributions quarterly, which are dollar for dollar up to 6% of
certified compensation, and a discretionary profit sharing
contribution up to 4% of certified compensation, if awarded, paid
following the plan year. Matching contributions were 100%
vested, and the discretionary profit sharing contributions
required three years of vesting service (no change).
Total defined contribution retirement plan expenses were
$1.0 billion in 2022, and $1.1 billion in both 2021 and 2020.
Wells Fargo & Company 178
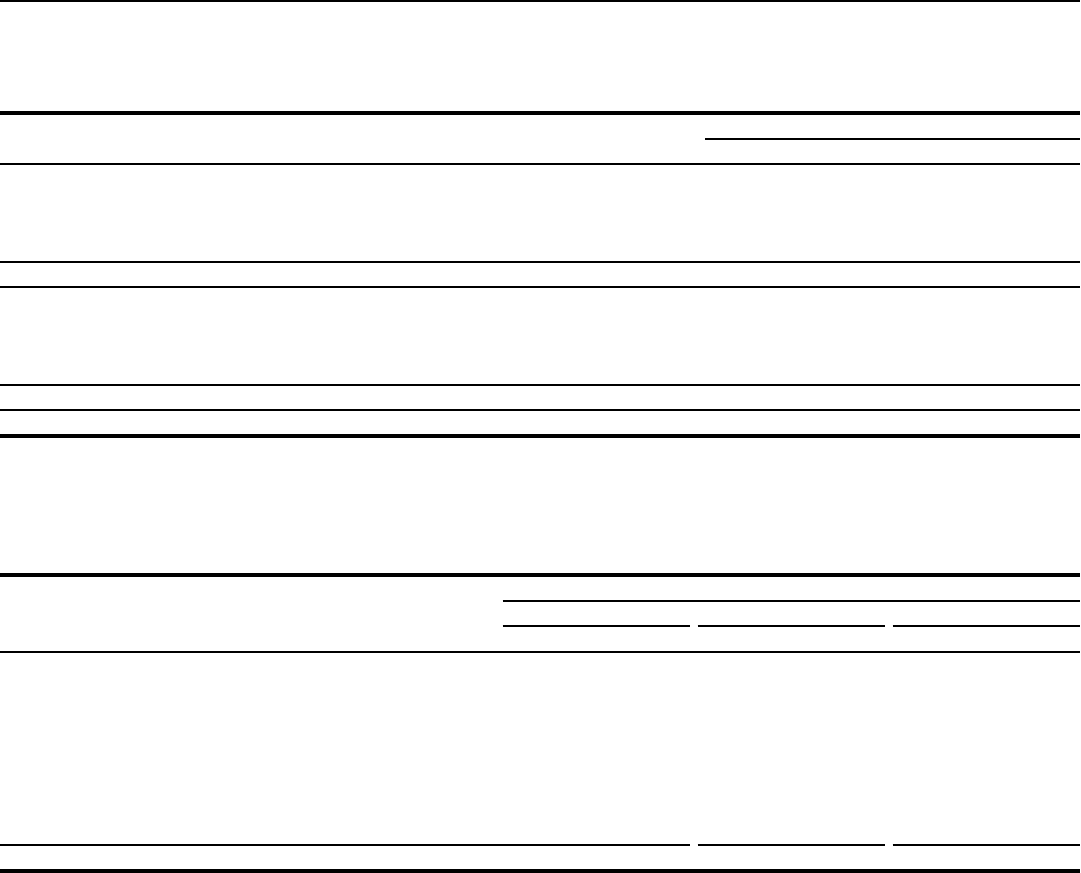
Wells Fargo & Company
Note 22: Income Taxes
Table 22.1 presents the components of income tax expense
(benefit).
Table 22.1: Income Tax Expense (Benefit)
Year ended December 31,
(in millions) 2022 2021 2020
Current:
U.S.
Federal $
888
5,850
2,231
U.S.
State
and
local (45)
849
(310)
Non-U.S. 169
171
211
Total
current 1,012
6,870
2,132
Deferred:
U.S.
Federal 636
(1,446)
(2,440)
U.S.
State
and
local 448
200
(789)
Non-U.S. (9)
(46)
(60)
Total
deferred 1,075
(1,292)
(3,289)
Total $
2,087
5,578
(1,157)
Table 22.2 reconciles the statutory federal income tax rate
to the effective income tax rate. Our effective tax rate is
calculated by dividing income tax expense (benefit) by income
before income tax expense (benefit) less the net income from
noncontrolling interests.
Table 22.2: Effective Income Tax Expense (Benefit) and Rate
December 31,
2022 2021
2020
(in
millions) Amount
Rate
Amount
Rate
Amount
Rate
Statutory
federal
income
tax
expense
and
rate $
3,206
21.0
% $
5,697
21.0
% $
466
21.0
%
Change
in
tax
rate
resulting
from:
State
and
local
taxes
on
income,
net
of
federal
income
tax
benefit 556
3.7
1,046
3.9
65
2.8
Tax-exempt
interest (321)
(2.1)
(316)
(1.2)
(358)
(16.1)
Tax
credits,
net
of
amortization
(1) (1,264)
(8.3)
(1,001)
(3.7)
(626)
(28.2)
Nondeductible
expenses
(2) 560
3.7
368
1.4
199
9.0
Changes
in
prior
year
unrecognized
tax
benefits,
inclusive
of
interest (503)
(3.3)
(122)
(0.4)
(938)
(42.2)
Other (147)
(1.0)
(94)
(0.4)
35
1.6
Effective
income
tax
expense
(benefit)
and
rate $
2,087
13.7
% $
5,578
20.6
% $
(1,157)
(52.1)%
(1) Includes LIHTC proportional amortization expense, net of tax of $1.2 billion at both 2022 and 2021, and $1.1 billion in 2020.
(2) Includes amounts related to nondeductible litigation and regulatory accruals in all years presented as well as a nondeductible goodwill impairment in 2021.
179

Note 22: Income Taxes(continued)
The tax effects of our temporary differences that gave rise
to significant portions of our deferred tax assets and liabilities
are presented in Table 22.3.
Table 22.3: Net Deferred Taxes
(in millions)
Dec 31,
2022
Dec 31,
2021
Deferred tax assets
Net operating loss and tax credit carry
forwards $ 5,513 382
Allowance for credit losses 3,393 3,415
Net unrealized losses on debt securities 3,193 —
Deferred compensation and employee
benefits 2,799 3,124
Accrued expenses 1,843 1,300
Lease liabilities 1,132 1,142
Other 2,044 1,048
Total deferred tax assets 19,917 10,411
Deferred tax assets valuation allowance (232) (267)
Deferred tax liabilities
Mark to market, net (11,081) (3,631)
Leasing and fixed assets (2,792) (3,523)
Mortgage servicing rights (2,153) (2,414)
Basis difference in investments (1,095) (496)
Right-of-use assets (935) (948)
Intangible assets (753) (559)
Net unrealized gains from debt securities — (278)
Other (1,006) (1,082)
Total deferred tax liabilities (19,815) (12,931)
Net deferred tax liability (1) $ (130) (2,787)
(1) The net deferred tax liability is included in accrued expenses and other liabilities.
Deferred taxes related to net unrealized gains (losses) on
debt securities, net unrealized gains (losses) on derivatives,
foreign currency translation, and employee benefit plan
adjustments are recorded in accumulated OCI. See Note 24
(Other Comprehensive Income) for additional information.
We have determined that a valuation allowance is required
for 2022 in the amount of $232 million, attributable to deferred
tax assets in various state and non-U.S. jurisdictions where we
believe it is more likely than not that these deferred tax assets
will not be realized due to lack of sources of taxable income,
limitations on carry back of losses or credits and the inability to
implement tax planning to realize these deferred tax assets. We
have concluded that it is more likely than not that the remaining
deferred tax assets will be realized based on our history of
earnings, sources of taxable income in carry back periods, and our
ability to implement tax planning strategies.
Table 22.4 presents the components of the deferred tax
assets related to net operating loss (NOL) and tax credit carry
forwards at December31, 2022.
Table 22.4: Deferred Tax Assets Related To Net Operating Loss and
Tax Credit Carry Forwards (1)
(in millions)
Dec 31,
2022
U.S. Federal NOLs $ 3,244
U.S. Federal tax credits 1,221
U.S. State NOLs and credits 974
Non-U.S. NOLs and credits 74
Total net operating loss and tax credit carryforwards $ 5,513
(1) U.S. Federal NOLs have no expiration date. The remaining balances, if not utilized, mostly
expire in varying amounts through December31, 2042.
We do not intend to distribute earnings of certain non-U.S.
subsidiaries in a taxable manner, and therefore intend to limit
distributions to non-U.S. earnings previously taxed in the U.S.,
that would qualify for the 100% dividends received deduction,
and that would not result in any significant state or non-U.S.
taxes. All other undistributed non-U.S. earnings will continue to
be permanently reinvested outside the U.S. and the related tax
liability on these earnings is insignificant.
Table 22.5 presents the change in unrecognized tax benefits.
Table 22.5: Change in Unrecognized Tax Benefits
Year ended
December 31,
(in millions) 2022 2021
Balance, beginning of period $ 5,218 4,826
Additions:
For tax positions related to the current year 695 441
For tax positions related to prior years 358 259
Reductions:
For tax positions related to prior years (514) (124)
Lapse of statute of limitations (13) (164)
Settlements with tax authorities (307) (20)
Balance, end of period $ 5,437 5,218
Of the $5.4 billion of unrecognized tax benefits at
December31, 2022, approximately $3.6 billion would, if
recognized, affect the effective tax rate. The remaining
$1.8billion of unrecognized tax benefits relates to income tax
positions on temporary differences.
We account for interest and penalties related to income tax
liabilities as a component of income tax expense. As of
December31, 2022 and 2021, we have accrued expenses of
approximately $436 million and $914 million, respectively, for
interest and penalties. In 2022 and 2021, we recognized income
tax benefit, net of tax, of $385million and $33 million,
respectively, related to interest and penalties.
We are subject to U.S. federal income tax as well as income
tax in numerous state and non-U.S. jurisdictions. We are routinely
examined by tax authorities in these various jurisdictions. With
few exceptions, Wells Fargo and its subsidiaries are not subject to
federal, state, local and non-U.S. income tax examinations for
taxable years prior to 2011. It is reasonably possible that one or
more of the examinations or appeals may be resolved within the
next twelve months resulting in a decrease of up to $1.4 billion of
our gross unrecognized tax benefits. Table 22.6 summarizes our
major tax jurisdiction examination status as of December31,
2022.
Table 22.6: Tax Examination Status
Jurisdiction Tax Year(s) Status
United States 2011-2014 Administrative appeals
United States 2015-2020 Field examination
California 2015-2016 Field examination
New York 2015-2019 Field examination
Wells Fargo & Company 180
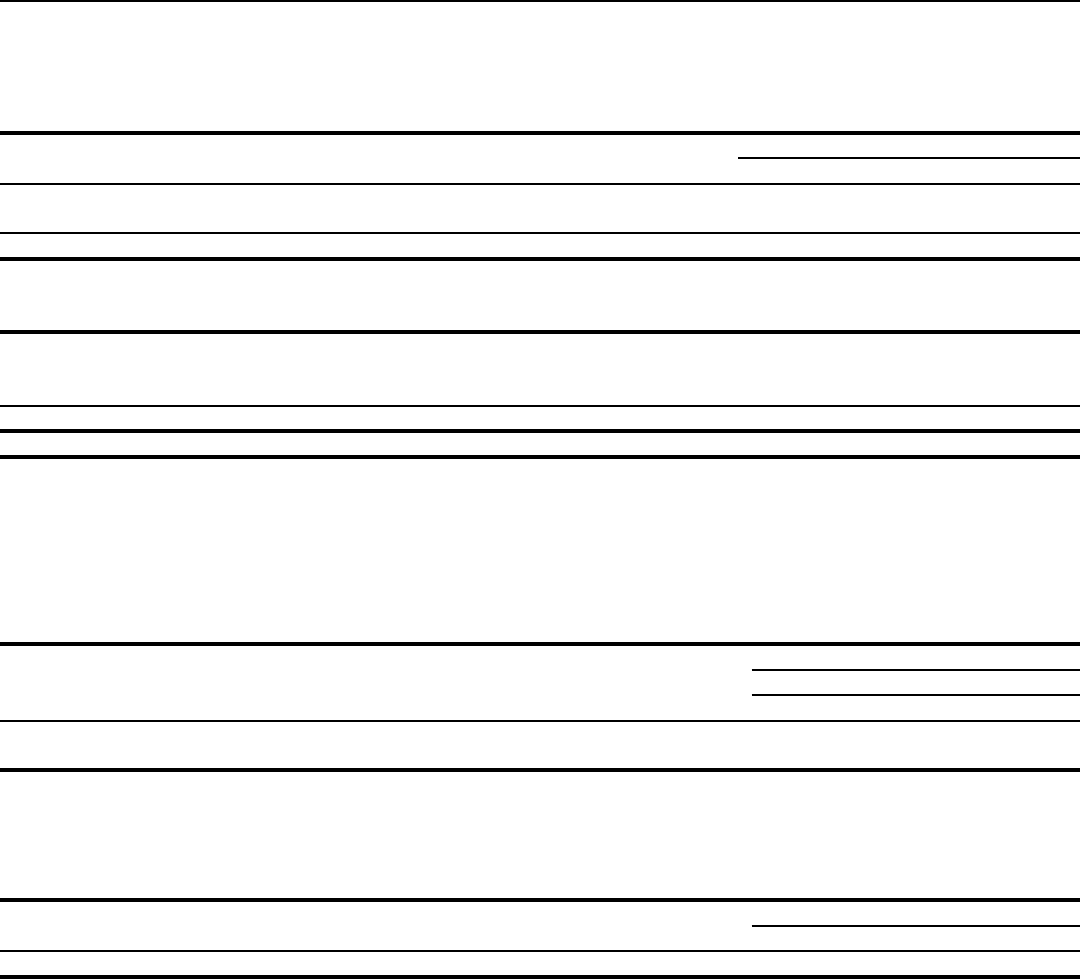
Note 23: Earnings and Dividends Per Common Share
Table 23.1 shows earnings per common share and diluted
earnings per common share and reconciles the numerator and
denominator of both earnings per common share calculations.
See the Consolidated Statement of Changes in Equity and Note
12 (Common Stock and Stock Plans) for information about stock
and options activity.
Table 23.1: Earnings Per Common Share Calculations
Year ended December 31,
(in millions, except per share amounts) 2022 2021 2020
Wells Fargo net income $ 13,182 21,548 3,377
Less: Preferred stock dividends and other (1) 1,115 1,292 1,591
Wells Fargo net income applicable to common stock (numerator) $ 12,067 20,256 1,786
Earnings per common share
Average common shares outstanding (denominator) 3,805.2 4,061.9 4,118.0
Per share $ 3.17 4.99 0.43
Diluted earnings per common share
Average common shares outstanding 3,805.2 4,061.9 4,118.0
Add: Restricted share rights (2) 31.8 34.3 16.2
Diluted average common shares outstanding (denominator) 3,837.0 4,096.2 4,134.2
Per share $ 3.14 4.95 0.43
(1) The balance for the years ended December 31, 2022, 2021 and 2020 includes $0 million, $87 million and $301 million, respectively, from the elimination of discounts or issuance costs associated
with redemptions of preferred stock.
(2) Calculated using the treasury stock method.
Table 23.2 presents the outstanding securities that were
anti-dilutive and therefore not included in the calculation of
diluted earnings per common share.
Table 23.2: Outstanding Anti-Dilutive Securities
Weighted-average shares
Year ended Dec ember 31,
(in millions) 2022
2021 2020
Convertible Preferred Stock, Series L (1) 25.3 25.3 25.3
Restricted share rights (2) 0.2 0.2 1.1
(1) Calculated using the if-converted method.
(2) Calculated using the treasury stock method.
Table 23.3 presents dividends declared per common share.
Table 23.3: Dividends Declared Per Common Share
Year ended December 31,
2022 2021 2020
Per common share $
1.10 0.60 1.22
Wells Fargo & Company 181
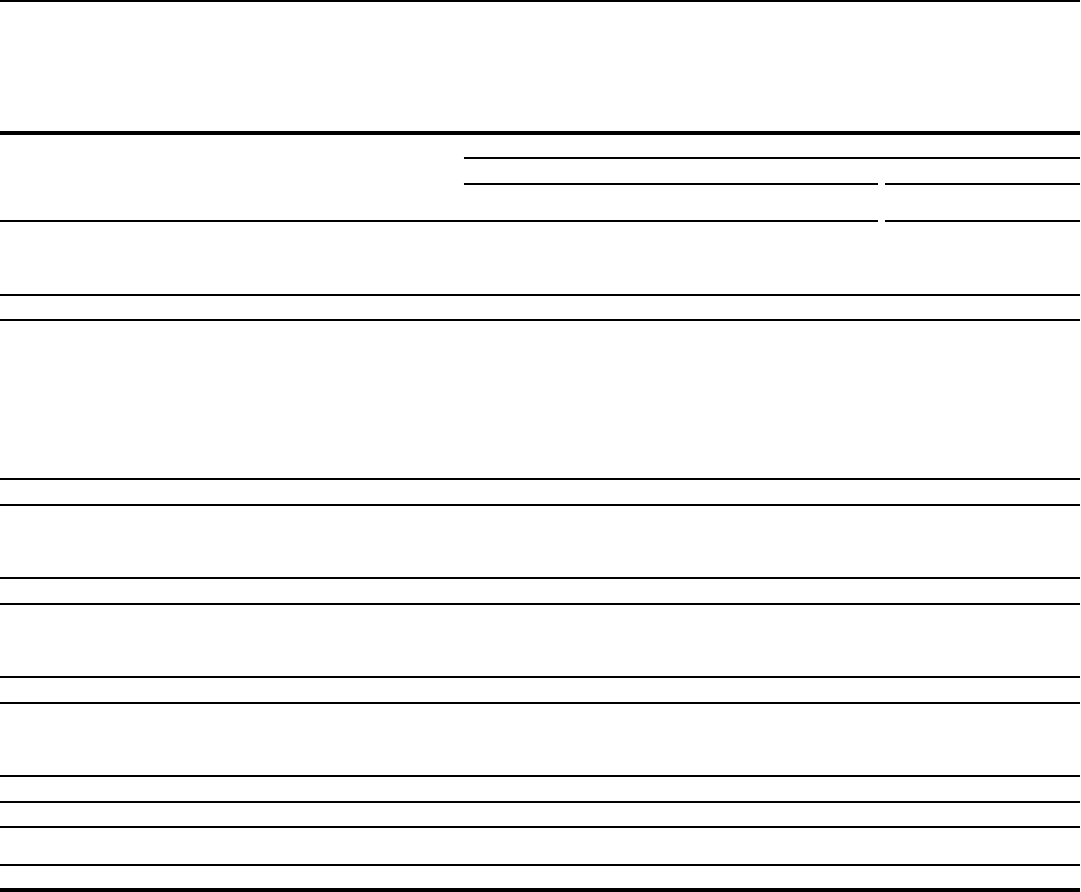
Note 24: Other Comprehensive Income
Table 24.1 provides the components of other comprehensive
income (OCI), reclassifications to net income by income
statement line item, and the related tax effects.
Table 24.1: Summary of Other Comprehensive Income
Twelve months ended December 31,
2022 2021 2020
(in millions)
Before
tax
Tax
effect
Net of
tax
Before
tax
Tax
effect
Net of
tax
Before
tax
Tax
effect
Net of
tax
Debt securities:
Net unrealized gains (losses) arising during the period $(14,320) 3,526 (10,794) (3,070) 759 (2,311) 2,317 (570) 1,747
Reclassification of net (gains) losses to net income 391 (97) 294 (82) 18 (64) (341) 81 (260)
Net change (13,929) 3,429 (10,500) (3,152) 777 (2,375) 1,976 (489) 1,487
Derivatives and hedging activities:
Fair Value Hedges:
Change in fair value of excluded components on fair value hedges (1) 87 (21) 66 81 (20) 61 (31) 7 (24)
Cash Flow Hedges:
Net unrealized gains (losses) arising during the period on cash flow
hedges (1,541) 381 (1,160) (12) 3 (9) 10 (2) 8
Reclassification of net (gains) losses to net income 6 (2) 4 143 (36) 107 219 (54) 165
Net change (1,448) 358 (1,090) 212 (53) 159 198 (49) 149
Defined benefit plans adjustments:
Net actuarial and prior service gains (losses) arising during the period (141) 35 (106) 200 (50) 150 (510) 126 (384)
Reclassification of amounts to noninterest expense (2) 343 (83) 260 261 (62) 199 266 (63) 203
Net change 202 (48) 154 461 (112) 349 (244) 63 (181)
Debit valuation adjustments (DVA):
Net unrealized gains (losses) arising during the period (8) 2 (6) — — — — — —
Reclassification of net (gains) losses to net income — — — — — — — — —
Net change (8) 2 (6) — — — — — —
Foreign currency translation adjustments:
Net unrealized gains (losses) arising during the period (232) (3) (235) (30) 1 (29) 52 (2) 50
Reclassification of net (gains) losses to net income — — — (1) — (1) — — —
Net
change
(232)
(3)
(235) (31) 1 (30) 52 (2) 50
Other
comprehensive
income
(loss)
$(15,415) 3,738
(11,677) (2,510) 613 (1,897) 1,982 (477) 1,505
Less:
Other
comprehensive
income
(loss)
from
noncontrolling
interests,
net
of
tax 2
(1) —
Wells
Fargo
other
comprehensive
income
(loss),
net
of
tax
$(11,679) (1,896) 1,505
(1) Represents changes in fair value of cross-currency swaps attributable to changes in cross-currency basis spreads, which are excluded from the assessment of hedge effectiveness and recorded in
other comprehensive income.
(2) These items are included in the computation of net periodic benefit cost (see Note 21 (Employee Benefits) for additional information).
Wells Fargo & Company 182
Table 24.2 provides the accumulated OCI (AOCI) balance
activity on an after-tax basis.
Table 24.2: Accumulated OCI Balances
(in millions)
Debt
securities
Fair value
hedges (1)
Cash flow
hedges (2)
Defined
benefit
plans
adjustments
Debit
valuation
adjustments
(DVA)
Foreign
currency
translation
adjustments
Accumulated
other
comprehensive
income (loss)
Balance, December 31, 2019 $ 1,552 (180) (298) (2,223) — (162) (1,311)
Net unrealized gains (losses) arising during the period 1,747 (24) 8 (384) — 50 1,397
Amounts reclassified from accumulated other
comprehensive income (260) — 165 203 — — 108
Net change 1,487 (24) 173 (181) — 50 1,505
Less: Other comprehensive income from noncontrolling
interests — — — — — — —
Balance, December 31, 2020 3,039 (204) (125) (2,404) — (112) 194
Net unrealized gains (losses) arising during the period (2,311) 61 (9) 150 — (29) (2,138)
Amounts reclassified from accumulated other
comprehensive income (64) — 107 199 — (1) 241
Net change (2,375) 61 98 349 — (30) (1,897)
Less: Other comprehensive loss from noncontrolling
interests (1) — — — — — (1)
Balance, December 31, 2021 (3) 665 (143) (27) (2,055) — (142) (1,702)
Net u nrealized gains (losses) arising du ring the period (10,794) 66 (1,160) (106) (6) (235) (12,235)
Amounts reclassified from accu mulated other
comprehensive income 294 — 4 260 — — 558
Net change (10,500) 66 (1,156) 154 (6) (235) (11,677)
Less: Other comprehensive income from
noncontrolling interests — — — — — 2 2
Balance, December 31, 2022 (3) $ (9,835) (77) (1,183) (1,901) (6) (379) (13,381)
(1) Substantially all of the amounts for fair value hedges are foreign exchange contracts.
(2) Substantially all of the amounts for cash flow hedges are interest rate contracts.
(3) AOCI related to debt securities includes after-tax unrealized gains or losses associated with the transfer of securities from AFS to HTM of $3.7 billion and $680 million at December 31, 2022 and
2021, respectively. These amounts are subsequently amortized from AOCI into earnings over the same period as the related unamortized premiums and discounts.
Wells Fargo & Company 183
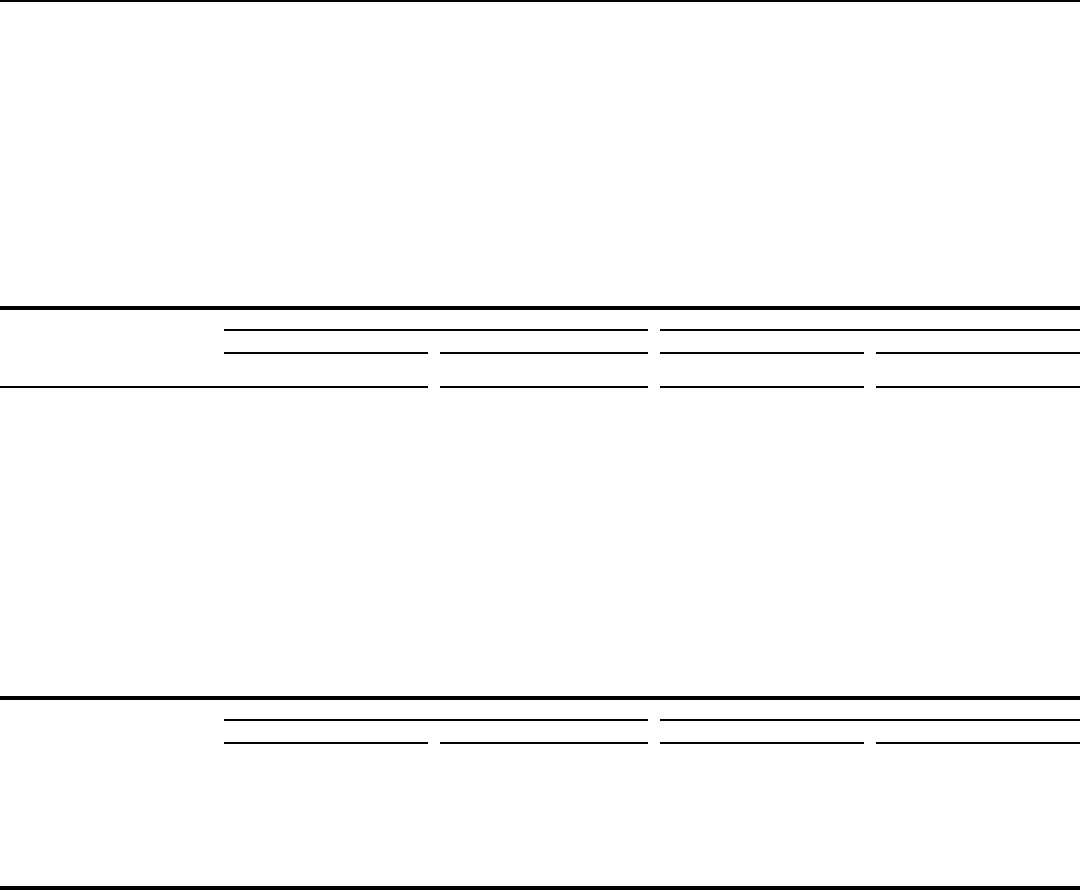
Note 25: Regulatory Capital Requirements and Other Restrictions
Regulatory Capital Requirements
The Company and each of its subsidiary banks are subject to
regulatory capital adequacy requirements promulgated by
federal banking regulators. The FRB establishes capital
requirements for the consolidated financial holding company,
and the Office of the Comptroller of the Currency (OCC) has
similar requirements for the Company’s national banks, including
Wells Fargo Bank, N.A. (the Bank).
Table 25.1 presents regulatory capital information for the
Company and the Bank in accordance with Basel III capital
requirements. We must calculate our risk-based capital ratios
Table 25.1: Regulatory Capital Information
under both the Standardized and Advanced Approaches. The
Standardized Approach applies assigned risk weights to broad
risk categories, while the calculation of risk-weighted assets
(RWAs) under the Advanced Approach differs by requiring
applicable banks to utilize a risk-sensitive methodology, which
relies upon the use of internal credit models, and includes an
operational risk component.
At December 31, 2022, the Bank and our other insured
depository institutions were considered well-capitalized under
the requirements of the Federal Deposit Insurance Act.
Wells Fargo & Company Wells Fargo Bank, N.A.
Standardized Approach Advanced Approach Standardized Approach Advanced Approach
(in millions, except ratios)
December 31,
2022
December 31,
2021
December 31,
2022
December 31,
2021
December 31,
2022
December 31,
2021
December 31,
2022
December 31,
2021
Regulatory capital:
Common Equity Tier 1 $ 133,527 140,643 133,527 140,643 140,644 149,318 140,644 149,318
Tier 1 152,567 159,671 152,567 159,671 140,644 149,318 140,644 149,318
Total 186,747 196,308 177,258 186,580 163,885 173,044 154,292 163,213
Assets:
Risk-weighted assets 1,259,889 1,239,026 1,112,307 1,116,068 1,177,300 1,137,839 977,713 965,511
Adjusted average assets 1,846,954 1,915,585 1,846,954 1,915,585 1,685,401 1,758,479 1,685,401 1,758,479
Regulatory capital ratios:
Common Equity Tier 1 capital 10.60 % * 11.35 12.00 12.60 11.95 * 13.12 14.39 15.47
Tier 1 capital 12.11 * 12.89 13.72 14.31 11.95 * 13.12 14.39 15.47
Total capital 14.82 * 15.84 15.94 16.72 13.92 * 15.21 15.78 16.90
Required minimum capital ratios:
Common Equity Tier 1 capital 9.20 9.60 8.50 9.00 7.00 7.00 7.00 7.00
Tier 1 capital 10.70 11.10 10.00 10.50 8.50 8.50 8.50 8.50
Total capital 12.70 13.10 12.00 12.50 10.50 10.50 10.50 10.50
Wells Fargo & Company Wells Fargo Bank, N.A
December 31, 2022 December 31, 2021 December 31, 2022 December 31, 2021
Regulatory leverage:
Total leverage exposure (1) $ 2,224,789 2,316,079 2,058,568 2,133,798
Supplementary leverage ratio (SLR) (1) 6.86 % 6.89 6.83 7.00
Tier 1 leverage ratio (2) 8.26 8.34 8.34 8.49
Required minimum leverage:
Supplementary leverage ratio 5.00 5.00 6.00 6.00
Tier 1 leverage ratio 4.00 4.00 4.00 4.00
.
* Denotes the binding ratio under the Standardized and Advanced Approaches at December 31, 2022.
(1) The SLR consists of Tier 1 capital divided by total leverage exposure. Total leverage exposure consists of total average assets, less goodwill and other permitted Tier 1 capital deductions (net of
deferred tax liabilities), plus certain off-balance sheet exposures.
(2) The Tier 1 leverage ratio consists of Tier 1 capital divided by total average assets, excluding goodwill and certain other items as determined under the rule.
At December 31, 2022, the Common Equity Tier 1 (CET1),
Tier 1 and total capital ratio requirements for the Company
included a global systemically important bank (G-SIB) surcharge
of 1.50%. The G-SIB surcharge is not applicable to the Bank. In
addition, the CET1, Tier 1 and total capital ratio requirements for
the Company included a stress capital buffer of 3.20% under the
Standardized Approach and a capital conservation buffer of
2.50% under the Advanced Approach. The capital ratio
requirements for the Bank included a capital conservation buffer
of 2.50% under both the Standardized and Advanced
Approaches. The Company is required to maintain these risk-
based capital ratios and to maintain an SLR of at least 5.00%
(composed of a 3.00% minimum requirement plus a
supplementary leverage buffer of 2.00%) to avoid restrictions on
capital distributions and discretionary bonus payments. The Bank
is required to maintain an SLR of at least 6.00% to be considered
well-capitalized under applicable regulatory capital adequacy
rules.
Capital Planning Requirements
The FRB’s capital plan rule establishes capital planning and other
requirements that govern capital distributions, including
dividends and share repurchases, by certain large bank holding
companies (BHCs), including Wells Fargo. The FRB conducts an
annual Comprehensive Capital Analysis and Review exercise and
has also published guidance regarding its supervisory
expectations for capital planning, including capital policies
regarding the process relating to common stock dividend and
repurchase decisions in the FRB’s SR Letter 15-18. The Parent’s
ability to make certain capital distributions is subject to the
requirements of the capital plan rule and is also subject to the
Parent meeting or exceeding certain regulatory capital
minimums.
Wells Fargo & Company 184

Loan and Dividend Restrictions
Federal law restricts the amount and the terms of both credit
and non-credit transactions between a bank and its nonbank
affiliates. These covered transactions may not exceed 10% of
the bank’s capital and surplus (which for this purpose
represents Tier 1 and Tier 2 capital, as calculated under the risk-
based capital rules, plus the balance of the ACL excluded from
Tier 2 capital) with any single nonbank affiliate and 20% of the
bank’s capital and surplus with all its nonbank affiliates.
Covered transactions that are extensions of credit may require
collateral to be pledged to provide added security to the bank.
Additionally, federal laws and regulations limit the
dividends that a national bank may pay. Dividends that may be
paid by a national bank without the express approval of the
OCC are generally limited to that bank’s retained net income
for the preceding two calendar years plus net income up to the
date of any dividend declaration in the current calendar year.
Retained net income, as defined by the OCC, consists of net
income less dividends declared during the period. Our national
bank subsidiaries could have declared additional dividends of
$6.4 billion at December 31, 2022, without obtaining prior
regulatory approval. We have elected to retain higher capital at
our national bank subsidiaries to meet internal capital targets,
which are set above regulatory requirements.
Our nonbank subsidiaries are also limited by certain federal
and state statutory provisions and regulations covering the
amount of dividends that may be paid in any given year. In
addition, under a Support Agreement dated June 28, 2017, as
amended and restated on June 26, 2019, among Wells Fargo &
Company, the parent holding company (Parent), WFC Holdings,
LLC, an intermediate holding company and subsidiary of the
Parent (IHC), the Bank, Wells Fargo Securities, LLC, Wells Fargo
Clearing Services, LLC, and certain other subsidiaries of the
Parent designated from time to time as material entities for
resolution planning purposes or identified from time to time as
related support entities in our resolution plan, the IHC may be
restricted from making dividend payments to the Parent if
certain liquidity and/or capital metrics fall below defined triggers
or if the Parent’s board of directors authorizes it to file a case
under the U.S. Bankruptcy Code. Based on retained earnings at
December 31, 2022, our nonbank subsidiaries could have
declared additional dividends of $26.9 billion at December 31,
2022, without obtaining prior regulatory approval.
Cash Restrictions
Cash and cash equivalents may be restricted as to usage or
withdrawal. Table 25.2 provides a summary of restrictions on
cash and cash equivalents.
Table 25.2: Nature of Restrictions on Cash and Cash Equivalents
(in millions)
Dec 31,
2022
Dec 31,
2021
Reserve balance for non-U.S. central banks $ 238 382
Segregated for benefit of brokerage customers
under federal and other brokerage regulations 898 830
Wells Fargo & Company 185
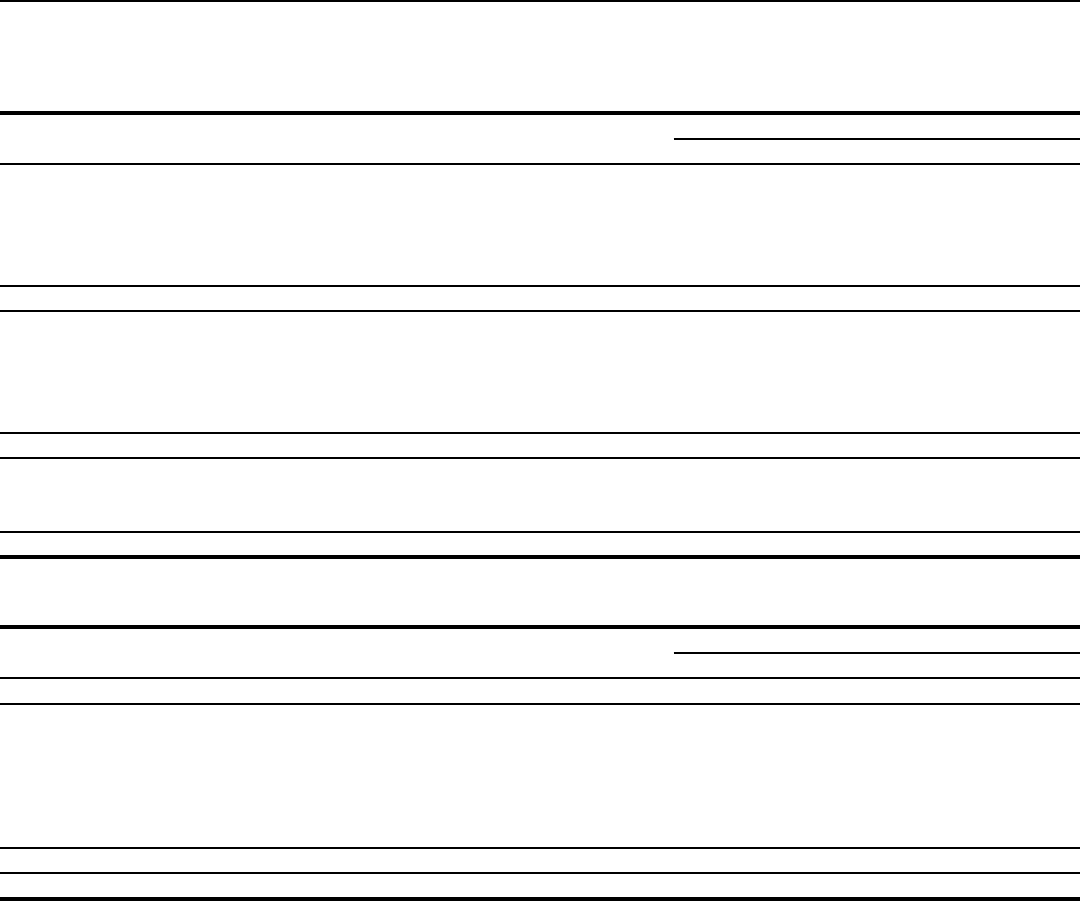
Note 26: Parent-Only Financial Statements
The following tables present Parent-only condensed financial
statements.
Table 26.1: Parent-Only Statement of Income
Year ended December 31,
(in millions) 2022 2021 2020
Income
Dividends from subsidiaries
(1) $ 14,590 17,895 42,578
Interest income from subsidiaries 4,759 3,934 1,295
Other interest income 2 1 3
Other income (53) (418) (231)
Total income 19,298 21,412 43,645
Expense
Interest expense:
Indebtedness to nonbank subsidiaries 1,124 89 155
Long-term debt 4,994 2,823 3,591
Noninterest expense 2,043 309 794
Total expense 8,161 3,221 4,540
Income before income tax benefit and equity in undistributed income of subsidiaries 11,137 18,191 39,105
Income tax benefit (1,503) (819) (1,694)
Equity in undistributed income of subsidiaries 542 2,538 (37,422)
Net income $ 13,182 21,548 3,377
(1) Includes dividends paid from indirect bank subsidiaries of $14.5 billion, $15.2 billion and $1.8 billion in 2022, 2021 and 2020, respectively.
Table 26.2: Parent-Only Statement of Comprehensive Income
Year ended December 31,
(in millions) 2022 2021 2020
Net income $ 13,182 21,548 3,377
Other comprehensive income (loss), after tax:
Debt securities 34 5 (10)
Derivatives and hedging activities 57 49 (2)
Defined benefit plans adjustments 145 347 (178)
Debit valuation adjustments (DVA) (6) — —
Equity in other comprehensive income (loss) of subsidiaries (11,909) (2,297) 1,695
Other comprehensive income (loss), after tax: (11,679) (1,896) 1,505
Total comprehensive income $ 1,503 19,652 4,882
Wells Fargo & Company 186
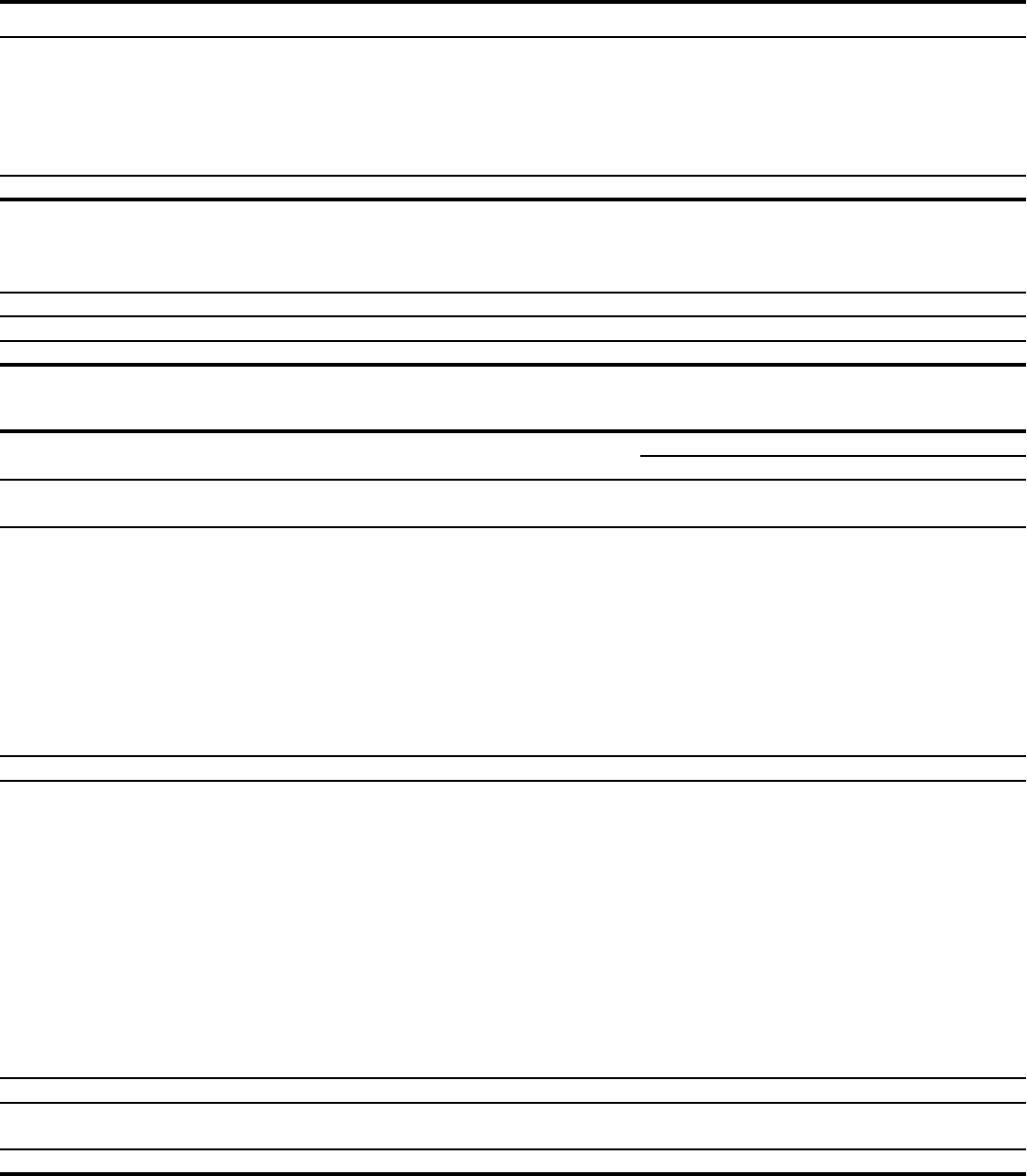
Table 26.3: Parent-Only Balance Sheet
(in millions)
Dec 31,
2022
Dec 31,
2021
Assets
Cash, cash equivalents, and restricted cash due from subsidiary banks $ 16,171 15,134
Loans to nonbank subsidiaries 182,656 185,050
Investments in subsidiaries
(1) 161,627 172,926
Equity securities 143 140
Other assets 9,408 7,341
Total assets $ 370,005 380,591
Liabilities and equity
Accrued expenses and other liabilities $ 8,258 7,333
Long-term debt 134,159 146,082
Indebtedness to nonbank subsidiaries 47,699 39,570
Total liabilities 190,116 192,985
Stockholders’ equity 179,889 187,606
Total liabilities and equity $ 370,005 380,591
(1) The years ended December 31, 2022 and 2021, include indirect ownership of bank subsidiaries with equity of $163.9 billion and $173.7 billion, respectively.
Table 26.4: Parent-Only Statement of Cash Flows
Year ended December 31,
(in millions) 2022 2021 2020
Cash flows from operating activities:
Net cash provided (used) by operating activities $ (4,575) 11,938 50,193
Cash flow s from investing activities:
Equity securities, not held for trading:
Proceeds from sales and capital returns 3 11 2,333
Purchases (8) (18) (1,479)
Loans:
Net
repayments
from
subsidiaries —
—
10
Capital
notes
and
term
loans
made
to
subsidiaries (3,567)
(3,500)
(38,547)
Principal
collected
on
notes/loans
made
to
subsidiaries 4,062
2,618
558
Net
decrease
in
investment
in
subsidiaries —
—
425
Other,
net (263)
14
16
Net
cash
provided
(used)
by
investing
activities 227
(875)
(36,684)
Cash flow
s from financing activities:
Net
increase
(decrease)
in
short-term
borrowings
and
indebtedness
to
subsidiaries 8,153
35,958
(22,613)
Long-term
debt:
Proceeds
from
issuance 26,520
1,001
34,918
Repayment (17,618)
(28,331)
(15,803)
Preferred
stock:
Proceeds
from
issuance —
5,756
3,116
Redeemed —
(6,675)
(3,602)
Cash
dividends
paid (1,115)
(1,205)
(1,290)
Common
stock:
Repurchased (6,033)
(14,464)
(3,415)
Cash
dividends
paid (4,178)
(2,422)
(4,852)
Other,
net (344)
(364)
(100)
Net
cash
provided
(used)
by
financing
activities 5,385
(10,746)
(13,641)
Net change in cash, cash equ
ivalents, and restricted cash
1,037
317
(132)
Cash,
cash
equivalents,
and
restricted
cash
at
beginning
of
period 15,134
14,817
14,949
Cash, cash equ
ivalents, and restricted cash at end of period
$
16,171
15,134
14,817
Wells Fargo & Company 187

Report of Independent Registered Public Accounting Firm
To the Stockholders and Board of Directors
Wells Fargo & Company:
Opinion on the Consolidated Financial Statements
We have audited the accompanying consolidated balance sheet of Wells Fargo & Company and subsidiaries (the Company) as of
December 31, 2022 and 2021, the related consolidated statement of income, comprehensive income, changes in equity, and cash flows
for each of the years in the three-year period ended December 31, 2022, and the related notes (collectively, the consolidated financial
statements). In our opinion, the consolidated financial statements present fairly, in all material respects, the financial position of the
Company as of December 31, 2022 and 2021, and the results of its operations and its cash flows for each of the years in the three-year
period ended December 31, 2022, in conformity with U.S. generally accepted accounting principles.
We also have audited, in accordance with the standards of the Public Company Accounting Oversight Board (United States) (PCAOB),
the Company’s internal control over financial reporting as of December 31, 2022, based on criteria established in Internal Control –
Integrated Framework (2013) issued by the Committee of Sponsoring Organizations of the Treadway Commission, and our report dated
February 21, 2023 expressed an unqualified opinion on the effectiveness of the Company’s internal control over financial reporting.
Basis for Opinion
These consolidated financial statements are the responsibility of the Company’s management. Our responsibility is to express an
opinion on these consolidated financial statements based on our audits. We are a public accounting firm registered with the PCAOB and
are required to be independent with respect to the Company in accordance with the U.S. federal securities laws and the applicable rules
and regulations of the Securities and Exchange Commission and the PCAOB.
We conducted our audits in accordance with the standards of the PCAOB. Those standards require that we plan and perform the audit to
obtain reasonable assurance about whether the consolidated financial statements are free of material misstatement, whether due to
error or fraud. Our audits included performing procedures to assess the risks of material misstatement of the consolidated financial
statements, whether due to error or fraud, and performing procedures that respond to those risks. Such procedures included examining,
on a test basis, evidence regarding the amounts and disclosures in the consolidated financial statements. Our audits also included
evaluating the accounting principles used and significant estimates made by management, as well as evaluating the overall presentation
of the consolidated financial statements. We believe that our audits provide a reasonable basis for our opinion.
Critical Audit Matters
The critical audit matters communicated below are matters arising from the current period audit of the consolidated financial
statements that were communicated or required to be communicated to the audit committee and that: (1) relate to accounts or
disclosures that are material to the consolidated financial statements and (2) involved our especially challenging, subjective, or complex
judgments. The communication of critical audit matters does not alter in any way our opinion on the consolidated financial statements,
taken as a whole, and we are not, by communicating the critical audit matters below, providing separate opinions on the critical audit
matters or on the accounts or disclosures to which they relate.
Assessment of the allowance for credit losses for loans (ACL)
As discussed in Notes 1 and 5 to the consolidated financial statements, the Company’s ACL as of December 31, 2022 was
$13.6 billion. The ACL includes the measurement of expected credit losses on a collective basis for those loans that share similar risk
characteristics utilizing multiple credit loss models. The Company estimated the ACL for commercial loans by applying probability of
default and severity of loss estimates to an expected exposure at default. The probability of default and severity of loss estimates
are statistically derived through historical observations of default and losses after default for each credit risk rating. The Company
estimated the ACL for consumer loans utilizing credit loss models which estimate expected credit losses in the portfolio based on
individual risk characteristics of the loans and historical experience of probability of default and severity of loss estimates. The
Company’s credit loss models utilize economic variables, including economic assumptions forecast over a reasonable and
supportable forecast period. The Company forecasts multiple economic scenarios and applies weighting to the scenarios that are
used to estimate expected credit losses. After the reasonable and supportable forecast period, the Company reverts over the
reversion period to the long-term average for the forecasted economic variables based on historical observations over multiple
economic cycles. A portion of the ACL is comprised of adjustments for qualitative factors which may not be adequately captured in
the loss models.
We identified the assessment of the ACL as a critical audit matter. A high degree of audit effort, including specialized skills and
knowledge, and subjective and complex auditor judgment was involved in the assessment of the ACL. Specifically, the assessment
encompassed the evaluation of the ACL methodology for collectively evaluated loans, including the methods and models used to
estimate (1) probability of default and severity of loss estimates, significant economic assumptions, the reasonable and supportable
forecast period, the historical observation period, and credit risk ratings for commercial loans, and (2) the adjustments for
qualitative factors that may not be adequately captured in the loss models. The assessment also included an evaluation of the
conceptual soundness and performance of certain credit loss models. In addition, auditor judgment was required to evaluate the
sufficiency of audit evidence obtained.
Wells Fargo & Company 188
The following are the primary procedures we performed to address this critical audit matter.
We evaluated the design and tested the operating effectiveness of certain internal controls related to the measurement of the ACL
estimate, including controls over the:
• development of certain credit loss and economic forecasting models
• continued use and appropriateness of changes made to certain credit loss and economic forecasting models
• performance monitoring of certain credit loss and economic forecasting models
• identification and determination of the significant assumptions used in certain credit loss and economic forecasting models
• development of the qualitative factors, including significant assumptions used in the measurement of certain qualitative
factors
• analysis of the ACL results, trends, and ratios.
We evaluated the Company’s process to develop the estimate by testing certain sources of data and assumptions that the Company
used and considered the relevance and reliability of such data and assumptions. In addition, we involved credit risk professionals
with specialized skills and knowledge, who assisted in:
• evaluating the Company’s ACL methodology for compliance with U.S. generally accepted accounting principles
• evaluating judgments made by the Company relative to the development, assessment and performance testing of certain
credit loss models by comparing them to relevant Company-specific metrics and trends and the applicable industry and
regulatory practices
• assessing the conceptual soundness of the credit loss models, including the selection of certain assumptions, by inspecting the
model documentation to determine whether the models are suitable for their intended use
• evaluating the methodology used to develop the forecasted economic scenarios, the selection of underlying assumptions and
the weighting of scenarios by comparing it to the Company’s business environment
• assessing the forecasted economic scenarios through comparison to publicly available forecasts
• testing the historical observation period and reasonable and supportable forecast periods to evaluate the length of each period
• testing individual credit risk ratings for a selection of commercial loans by evaluating the financial performance of the borrower,
sources of repayment, and any relevant guarantees or underlying collateral
• evaluating the methods and assumptions used to develop certain qualitative factors and the effect of those factors on the ACL
compared with relevant credit risk factors and consistency with credit trends and identified limitations of the underlying
quantitative models.
We also assessed the sufficiency of the audit evidence obtained related to the ACL estimates by evaluating the:
• cumulative results of the audit procedures
• qualitative aspects of the Company’s accounting practices
• potential bias in the accounting estimates.
Assessment of the residential mortgage servicing rights (MSRs)
As discussed in Notes 1, 6, 15, and 16 to the consolidated financial statements, the Company’s residential MSR asset as of
December 31, 2022 was $9.3 billion on an underlying loan servicing portfolio of $681 billion. The Company recognizes MSRs when it
retains servicing rights in connection with the sale or securitization of loans it originated or purchases servicing rights from third
parties and has elected to carry its residential MSRs at fair value with periodic changes reflected in earnings. The Company uses a
valuation model for determining fair value that calculates the present value of estimated future net servicing income cash flows,
which incorporates assumptions that market participants use in estimating future net servicing income cash flows. These
assumptions include estimates of prepayment rates (including estimated borrower defaults), discount rates, cost to service
(including delinquency and foreclosure costs), escrow account earnings, contractual servicing fee income, ancillary income and late
fees. The estimated fair value of MSRs is periodically benchmarked to independent appraisals.
We identified the assessment of the valuation of residential MSRs as a critical audit matter. A high degree of audit effort, including
specialized skills and knowledge, and subjective and complex auditor judgment was involved in the assessment of the MSRs.
Specifically, there was a high degree of subjectivity used to evaluate the following assumptions because they are unobservable and
the sensitivity of changes to those assumptions had a significant effect on the valuation (1) prepayment rates, (2) discount rates,
and (3) cost to service. There was also a high degree of subjectivity and potential for management bias related to updates made to
significant assumptions due to changes in market conditions, mortgage interest rates, or servicing standards.
The following are the primary procedures we performed to address this critical audit matter. We evaluated the design and tested
the operating effectiveness of certain internal controls related to the assessment of residential MSRs, including controls over the:
• assessment of the valuation model
• evaluation of the significant assumptions (prepayment rates, discount rates, and cost to service) used in determining the MSR
fair value
• comparison of the MSR fair value to independent appraisals.
Wells Fargo & Company 189

We
e
v
alua
t
ed
the
C
ompany
’s
p
r
oce
ss
to
d
eve
l
o
p
the
MS
R
fa
i
r
value
by
t
estin
g
ce
r
ta
in
sou
r
ces
of
data
a
n
d
assum
p
tion
s
tha
t
the
C
omp
a
n
y
use
d
an
d
cons
i
d
ere
d
the
re
l
evanc
e
an
d
re
l
ia
b
i
l
it
y
o
f
s
u
c
h
d
at
a
a
n
d
assumpt
i
ons
.
I
na
dd
itio
n
,
w
e
i
nvo
l
ve
d
v
a
l
uatio
n
p
ro
f
essional
s
wi
t
hs
p
ecia
l
i
z
e
d
sk
ill
s
a
n
d
kn
owled
g
e
,
w
ho
ass
i
sted
i
n
:
•
eva
l
uatin
g
the
desi
gn
of
the
v
aluat
i
on
model
u
s
ed
to
est
im
ate
the
M
SR
f
a
i
r
value
i
n
acco
r
da
n
ce
w
i
th
r
ele
v
a
n
t
U.
S
.
ge
nera
lly
accepte
d
account
i
ng
p
rincip
l
e
s
•
e
v
a
l
uat
in
g
s
i
g
ni
f
ica
n
t
assu
mpt
i
o
n
s
based
o
n
a
n analysi
s
of
bac
k
test
i
n
g
resu
l
ts
a
n
d
a
c
omparison
of
s
ign
i
f
i
ca
n
t
assump
t
io
n
s
to
avai
l
a
ble
d
at
a
f
o
r
compara
bl
e
ent
i
t
i
e
s
an
d
i
n
d
epen
d
e
n
t
appraisa
l
s
•
assessin
g
signi
f
i
ca
n
t
assu
m
p
t
i
o
nu
p
date
s
m
ade
d
uring
t
h
e
year
b
y
co
n
s
i
de
ri
n
g
b
acktestin
g
r
es
ults
,
e
x
te
rn
al
m
a
r
k
et
even
t
s
,
i
n
d
epen
d
ent appraisa
l
s
,
a
n
d
ot
h
e
r
c
i
rcumstance
s
th
a
t
a
mar
k
e
t
p
art
i
c
i
pant
wou
ld
h
ave
e
xpecte
d
t
o
be
incorporate
d
i
n
the
v
a
l
uat
i
on
t
h
at
we
r
e
n
ot
i
ncor
p
orated.
Assess
m
e
n
t
o
f
goo
dw
i
ll
i
m
p
ai
r
me
n
t
As
d
i
scus
sed
in
Notes
1
a
n
d
7
to
t
h
e
co
n
so
li
dat
ed
f
i
n
a
n
c
i
a
l
s
t
a
t
emen
t
s
,
t
h
e
C
ompa
n
y
’
s
g
oodwill
ba
l
a
n
ce
as
of
D
ecem
be
r
3
1
,
2
022
w
as
$
25.
2
b
illi
o
n
.
Th
e
C
ompan
y
tests
goodw
i
ll
f
or
i
mpa
i
rment
annu
all
y
i
n
t
h
e
f
ou
r
th
quar
t
e
r
,
o
r
mo
r
e
f
requentl
y
if
ev
e
n
ts
o
r
c
ir
c
u
m
sta
n
ces
in
d
i
cate
t
h
at
t
h
e
carr
y
i
n
g
v
a
l
u
e
of
go
odw
ill
ma
y
be
i
m
p
aired, b
y
com
p
arin
g
t
h
e
f
a
i
r
v
a
l
u
e
of
t
h
e
reportin
g
u
ni
t
w
i
t
h
its
carryin
g
amoun
t,
i
n
c
l
udi
n
g
g
oodwill
.
M
ana
ge
m
e
n
t
est
im
ates
t
h
e
f
a
ir
va
l
ue
of
its
re
p
orti
n
g
u
ni
ts
u
sin
g
an
in
co
m
e
a
pp
r
o
a
ch
a
n
d
a
ma
rk
et
approach
.
Th
e
i
n
co
m
e
approac
h
is
a
d
i
scou
n
ted
cash
f
low
(
DCF
)
an
a
lysi
s
t
h
at
i
ncorporates assumpt
i
o
n
s
includin
g
f
in
a
n
c
i
al
f
o
r
ecas
ts
,
a
te
rmi
n
a
l
va
l
u
e
based
o
n
a
n
assu
m
e
d
lon
g
-ter
m
g
row
t
h
rate
,
a
n
d
a
d
i
scoun
t
rate
.Th
e
fin
a
n
c
i
al
f
o
r
ecasts
i
n
c
l
ude
f
ut
u
r
e
ex
p
ectation
s
of
eco
n
o
mi
c
co
n
di
ti
o
n
s
a
n
d
ba
l
a
n
ce
s
h
eet
c
h
an
g
e
s
,
a
n
d
co
n
s
i
de
r
at
i
o
n
s
r
e
l
ated
to
f
utu
r
e
bus
in
es
s
act
ivi
t
i
es.
T
he
fo
r
ecas
ted
cas
h
f
l
o
w
s
a
r
e
d
i
scou
n
te
d
u
sin
g
a
r
ate
de
riv
ed
f
r
om
a
c
apita
l
asset
pricin
g
m
odel
w
hi
c
h produce
s
a
n
est
im
ated
co
st
of
equ
i
t
y
to
the
report
i
n
g
u
n
it
.
T
he
m
a
r
ket
a
pproac
h
ut
i
l
iz
es
obse
rv
able
m
a
r
ket
data
f
r
om
compara
ble
p
u
bl
ic
ly
t
r
aded
compa
n
ies
a
n
d
incor
p
orate
s
as
s
um
p
tions includin
g
t
h
e
se
l
ecti
o
n
of
com
p
arabl
e
com
p
anies
a
n
d
a
co
n
t
r
o
l
p
remium re
p
rese
n
tat
iv
e
of
m
a
n
a
g
em
e
n
t
’
s
e
xpectatio
n
of
a
hy
p
o
t
het
i
ca
l
a
cqu
i
si
ti
on
of
t
h
e
reporti
n
g
u
ni
t
.
We
i
de
n
t
ifi
ed
t
h
e
assess
m
e
nt
of
t
h
e
g
oodw
i
l
l
i
m
p
airment f
or
t
h
e
C
o
n
s
u
m
e
r
Le
n
d
in
g
re
p
orti
n
g
u
nit
,
w
hi
ch
h
ad
$
7.
1
b
i
lli
o
n
of
a
ll
ocated
g
oodwil
l
as
of
D
ece
m
ber
3
1
,
2022
,
a
s
a
c
r
i
t
ic
a
l
a
u
d
i
t
m
a
t
t
e
r
.
A
h
i
g
h
de
gr
e
e
of
a
u
d
i
t
e
ff
o
r
t
,
in
c
lu
din
g
spe
c
i
a
liz
e
d
s
kill
s
a
nd
k
nowledge
,
a
n
d
subject
i
ve
a
n
d
comple
x
aud
i
tor
j
udgment
was
i
nv
o
lv
ed
i
n
t
h
e
assess
m
e
n
t.
S
peci
f
ically,
t
h
e
assess
m
e
n
t
e
ncom
p
asse
d
t
h
e
e
v
a
l
u
at
i
o
n
of
ce
r
tai
n
assum
p
t
i
o
n
s
u
sed
in
t
h
e
DCF
a
n
a
l
y
si
s
to
es
t
im
ate
t
h
e
f
a
i
r
v
a
l
u
e
of
t
h
e
reportin
g
unit
,
includin
g
(
1
)
t
h
e
f
u
tu
r
e
ex
pe
ctat
i
o
n
s
of
ba
l
a
n
ce
s
h
eet
c
h
a
n
g
e
s
a
n
d
bu
s
i
n
ess
act
ivi
t
i
es
u
sed
i
n
t
h
e
fin
a
n
c
i
al
f
o
r
ecas
t
a
n
d
(2
)
t
h
e
d
i
sc
ou
n
t
rate.
Th
e
followin
g
ar
e
t
h
e
primar
y
p
rocedu
res
we
p
erf
o
rm
ed
to
add
r
ess
t
hi
s
c
ri
t
i
cal
au
d
i
t
m
atte
r.
We
e
v
a
l
uated
t
h
e
desi
gn
a
n
d
test
ed
t
h
e
operatin
g
effect
i
v
e
n
e
ss
of
ce
r
ta
in
i
n
te
rn
a
l
co
n
t
r
o
l
s
r
e
l
ated
to
t
h
e
C
ompan
y’
s
dete
rmin
at
i
on
of
t
h
e
est
im
ated
fa
i
r
v
a
lue
of
t
h
e
C
onsume
r
Lending report
i
ng
u
n
i
t, in
c
l
udi
n
g
co
n
t
r
o
l
s
r
e
l
ated
to
t
h
e
:
•
e
v
alua
t
io
n
of
the
f
utu
r
e
expectat
i
on
s
of
bala
n
ce
sheet
cha
n
ges
a
n
d
bus
in
ess
acti
v
ities
u
sed
i
n
the
f
in
a
n
c
i
al
fo
r
ec
ast
a
ssumpt
i
on
a
n
d
•
e
v
aluat
i
on
of
t
he
d
i
scou
n
t
r
ate
assu
mpti
o
n.
We
e
v
a
l
uated
t
h
e
r
easo
n
ab
l
e
n
ess
of
t
h
e
fin
a
n
c
i
al
f
o
r
ecas
t
a
ssum
p
tio
n
f
or
t
h
e
re
p
orti
n
g
u
ni
t
by
e
v
a
l
uat
in
g
h
i
sto
ri
ca
l
pe
rf
o
rm
a
n
ce
a
n
d
eco
n
o
mi
c
t
r
e
n
ds.
We
a
l
so
e
v
a
l
uate
d
t
h
e
co
n
si
ste
nc
y
of
t
h
e
f
i
n
a
n
c
i
al
fo
r
ecast
as
sum
p
tio
n
by
com
p
arin
g
t
h
e
f
o
r
ecast
to
ot
h
er
ana
l
ys
es
used
b
y
the
C
om
p
any
a
n
d
i
nqu
i
ri
e
s
per
f
o
r
m
ed
of
sen
i
or
managemen
t
regar
d
in
g
the
strategi
c
pl
ans
for
the
re
p
o
r
ting
u
ni
t
,
includin
g
f
utu
r
e
ex
p
ectat
i
o
n
s
of
ba
l
a
n
ce
s
h
e
et
c
h
a
n
g
e
s
a
n
d
bu
s
i
n
ess
act
ivi
t
i
es.
We
com
p
are
d
h
i
sto
ri
ca
lf
i
n
an
c
i
al
f
o
r
ecasts
to
actua
l
r
esu
l
ts
to
as
sess
t
h
e
Compan
y
’
s
a
bilit
y
to
accu
r
atel
y
f
o
r
ecas
t
.
In
add
i
t
i
o
n
,
we
inv
o
lv
ed
a
va
l
uat
i
o
n
p
rof
ess
i
o
n
a
l
w
i
th
sp
ecialized
s
kill
s
a
n
d
knowledge
,
w
h
o
ass
i
sted
i
n
:
•
e
v
a
l
ua
t
in
g
t
h
e
reaso
n
ab
l
e
n
e
ss
of
t
h
e
f
in
a
n
c
i
al
f
o
r
ecas
t
as
s
umption
for
t
h
e
reporti
n
g
u
ni
t
b
y comparin
g
ce
r
ta
i
n
g
r
o
w
th
t
r
e
n
ds
for
the
report
i
n
g
u
n
it
to
p
u
bli
c
ly
a
v
a
i
labl
e
data
f
or
compara
ble
e
n
tities
•
e
v
a
l
uat
in
g
t
h
e
d
i
scou
n
t
r
ate
assu
mpt
i
o
n
use
d
i
n
t
h
e
f
a
i
r
va
l
ue
dete
rmin
at
i
on
by
comparin
g
t
h
e
i
nputs
to
t
h
e
d
i
s
co
u
n
t
rate
to
pu
bl
ic
ly
a
v
a
i
la
ble
data
f
or
compara
bl
e
e
n
tities
a
n
d
asses
sin
g
the
r
esu
l
tin
g
d
i
scou
n
t
r
ate
an
d
•
e
v
a
l
ua
tin
g
t
h
e
reaso
n
ab
l
e
n
e
ss
of
t
h
e
tota
l
f
a
i
r
v
a
l
ue
t
hr
ou
g
h
com
p
ariso
n
to
t
h
e
C
om
p
an
y’
s
m
a
rk
et
ca
p
italizatio
n
a
n
d
a
n
a
lysi
s
of
the
resu
l
tin
g
prem
i
u
m
to
app
l
ica
ble
m
a
r
ket
t
r
an
s
actio
n
s.
W
e
ha
v
e
se
rv
ed
as
t
h
e
C
ompany
’s
aud
i
tor
s
in
ce
1
93
1
.
C
harlotte
,
N
o
r
th
C
aro
l
i
n
a
Februar
y
2
1
,
2023
W
ell
s
Far
g
o
&
C
om
p
any
190
Quarterly Financial Data
Condensed Consolidated Statement o f Inco me – Qua rterly (Una udited)
2022
Quarter ended
2021
Quarter ended
(in millions, except per share amounts) Dec 31, Sep 30, Jun 30, Mar 31, Dec 31, Sep 30, Jun 30, Mar 31,
Interest income $ 17,793 14,494 11,556 10,181 10,121 9,834 9,693 10,046
Interest expense 4,360 2,396 1,358 960 859 925 893 1,238
Net interest income 13,433 12,098 10,198 9,221 9,262 8,909 8,800 8,808
Noninterest income
Deposit and lending-related fees 1,522 1,647 1,729 1,815 1,819 1,781 1,704 1,616
Investment advisory and other asset-based fees 2,049 2,111 2,346 2,498 2,579 2,882 2,794 2,756
Commissions and brokerage services fees 601 562 542 537 558 525 580 636
Investment banking fees 331 375 286 447 669 547 570 568
Card fees 1,095 1,119 1,112 1,029 1,071 1,078 1,077 949
Mortgage banking 79 324 287 693 1,035 1,259 1,336 1,326
Net gains (losses) from trading and securities (181) 872 (26) 796 2,412 1,244 2,717 891
Other 731 397 554 556 1,451 609 692 982
Total noninterest income 6,227 7,407 6,830 8,371 11,594 9,925 11,470 9,724
Total revenue 19,660 19,505 17,028 17,592 20,856 18,834 20,270 18,532
Provision for credit losses 957 784
580 (787) (452) (1,395) (1,260) (1,048)
Noninterest expense
Personnel 8,415 8,212 8,442 9,271 8,475 8,690 8,818 9,558
Technology, telecommunications and equipment 902 798 799 876 827 741 815 844
Occupancy 722 732 705 722 725 738 735 770
Operating losses 3,517 2,218 576 673 512 540 303 213
Professional and outside services 1,357 1,235 1,310 1,286 1,468 1,417 1,450 1,388
Advertising and promotion 178 126 102 99 225 153 132 90
Restructuring charges — — — 5 66 1 (4) 13
Other 1,111 1,006 949 938 900 1,023 1,092 1,113
Total noninterest expense 16,202 14,327 12,883 13,870 13,198 13,303 13,341 13,989
Income before income tax expense (benefit) 2,501 4,394 3,565 4,509 8,110 6,926 8,189 5,591
Income tax expense (benefit) (127) 894 613 707 1,711 1,521 1,445 901
Net income before noncontrolling interests 2,628 3,500 2,952 3,802 6,399 5,405 6,744 4,690
Less: Net income (loss) from noncontrolling interests (236) (28) (167) 131 649 283 704 54
Wells Fargo net income $
2,864
3,528 3,119 3,671 5,750
5,122 6,040 4,636
Less: Preferred stock dividends and other
279 278 280 278 280 335 297 380
Wells Fargo net income applicable to common stock $
2,585
3,250 2,839 3,393 5,470 4,787 5,743 4,256
Per share information
Earnings per common share $
0.68
0.86 0.75 0.89 1.39 1.18 1.39 1.03
Diluted earnings per common share 0.67 0.85 0.74 0.88 1.38 1.17 1.38 1.02
Average common shares outstanding 3,799.9 3,796.5 3,793.8 3,831.1 3,927.6 4,056.3 4,124.6 4,141.3
Diluted average common shares outstanding 3,832.7 3,825.1 3,819.6 3,868.9 3,964.7 4,090.4 4,156.1 4,171.0
Wells Fargo & Company 191

Glossary of Acronyms
ACL Allowance for credit losses
AFS Available-for-sale
AOCI Accumulated ot her comprehensive income
ARM Adjustable-rate mort gage
ASC Accounting S tandards C odification
ASU Accounting S tandards Upda te
AVM Automated va luation model
BCBS Basel C ommittee on Ba nking S upervision
BHC Bank holding compa ny
CCAR Comprehensive C apital Ana lysis a nd Review
CD Certificate of deposit
CECL Current expected credit loss
CET1 Common Equit y Tier 1
CFPB Consumer F inancial Prot ection Burea u
CLO Collateralized loa n obliga tion
CLTV Combined loa n-to-value
CPI Collateral prot ection insura nce
CRE Commercial rea l est ate
DPD Days pa st due
ESOP Employee S tock Ownership Pla n
FASB Financial Account ing S tandards Boa rd
FDIC Federal Deposit Insurance C orporation
FHA Federal Housing Administ ration
FHLB Federal Home Loa n Ba nk
FHLMC Federal Home Loa n Mort gage C orporation
FICO Fair Isa ac C orporation (credit rating)
FNMA Federal Na tional Mort gage Associa tion
FRB Board of Governors of t he F ederal Reserve S ystem
GAAP Generally a ccepted a ccounting principles
GNMA Government National Mort gage Associa tion
GSE Government-sponsored ent ity
G-SIB Global syst emically import ant bank
HQLA High-quality liquid a ssets
HTM
Held-to-maturity
LCR
Liquidity covera
ge ra
tio
LHFS
Loans held for sa
le
LIBOR
London Int
erbank
Offered Ra
te
LIHTC
Low-income housing t
ax credit
LOCOM
Lower of cost
or fa
ir va
lue
LTV
Loan-to-value
MBS
Mortgage-backed securit
ies
MSR
Mortgage servicing right
NAV
Net
asset
value
NPA
Nonperforming a
sset
NSFR
Net
stable funding ra
tio
OCC
Office of t
he C
omptroller of t
he C
urrency
OCI
Other comprehensive income
OTC
Over-the-counter
PCD
Purchased credit
-deteriorated
PTPP
Pre-tax pre-provision profit
RMBS
Residential mort
gage-backed securit
ies
ROA
Return on a
verage a
ssets
ROE
Return on a
verage equit
y
ROTCE
Return on a
verage t
angible common equit
y
RWAs
Risk-weighted a
ssets
SEC
Securities a
nd Excha
nge C
ommission
S&P
Standard & Poor’
s Globa
l Ra
tings
SLR
Supplementary levera
ge ra
tio
SOFR
Secured Overnight
Financing Ra
te
SPE
Special purpose ent
ity
TDR
Troubled debt
restructuring
TLAC
Total Loss Absorbing C
apacity
VA
Department
of Vet
erans Affa
irs
VaR
Value-at-Risk
VIE
Variable int
erest
entity
WIM
Wealth a
nd Invest
ment
Management
Wells Fargo & Company 192
Operating Committee
William M. Daley
Vice Chair of Public Affairs
Kristy Fercho
Senior EVP
Head of Diverse Segments,
Representation and Inclusion
Derek A. Flowers
Senior EVP
Chief Risk Officer
Kyle G. Hranicky
Senior EVP
CEO of Commercial Banking
Bei Ling
Senior EVP
Head of Human Resources
Mary T. Mack
Senior EVP
CEO of Consumer & Small
Business Banking
Lester J. Owens
Senior EVP
Head of Operations
Ellen R. Patterson
Senior EVP
General Counsel
Scott E. Powell
Senior EVP
Chief Operating Officer
Paul Ricci
Senior EVP
Chief Auditor
Michael P. Santomassimo
Senior EVP
Chief Financial Officer
Kleber R. Santos
Senior EVP
CEO of Consumer Lending
Charles W. Scharf
Chief Executive Officer
and President
Barry Sommers
Senior EVP
CEO of Wealth &
Investment Management
Saul Van Beurden
Senior EVP
Head of Technology
Jonathan G. Weiss
Senior EVP
CEO of Corporate
&
Investment Banking
Ather Williams III
Senior EVP
Head of Strategy, Digital,
and Innovation
As of February 24, 2023
Except for Paul Ricci, all members of the
Operating Committee are executive officers
according to Securities and Exchange
Commission rules. Muneera S. Carr, EVP, Chief
Accounting Officer and Controller, also is an
executive officer.
Board of Directors
Steven D. Black (Chair)
Former Co-CEO
Bregal Investments, Inc., an international
private equity firm
Mark A. Chancy
Former Vice Chair and Co-COO
SunTrust Banks, Inc., a bank holding
company
Celeste A. Clark
Principal, Abraham Clark
Consulting, LLC,
a health and regulatory policy
consulting firm
Theodore F. Craver, Jr.
Former Chair,
President and CEO
Edison International, an electric utility
holding company
Richard K. Davis
Former President and CEO
Make-A-Wish America, a non-profit
organization
Wayne M. Hewett
Senior Advisor
Permira, a global private equity firm
CeCelia “CeCe” G. Morken
Former CEO
Headspace, an online wellness company
Maria R. Morris
Former EVP and Head,
Global Employee Benefits business
MetLife, a global financial services
company
Felicia F. Norwood
EVP and President,
Government Business Division
Elevance Health, Inc.,
a health company
Richard B. Payne, Jr.
Former Vice Chair
Wholesale Banking
U.S. Bancorp, a U.S. bank holding
company
Juan A. Pujadas*
Former Vice Chair
Global Advisory Services,
PwC
, a global professional
services firm
Ronald L. Sargent
Former CEO and Chair
Staples, Inc., a workplace products
retailer
Charles W. Scharf
Chief Executive Officer and
President
Wells Fargo & Company
Suzanne M. Vautrinot
President
Kilovolt Consulting, Inc.,
a cybersecurity strategy and
technology consulting firm
As of February 24, 2023
*Juan A. Pujadas is not standing for re-election
and will retire as a director at the 2023 annual
meeting.
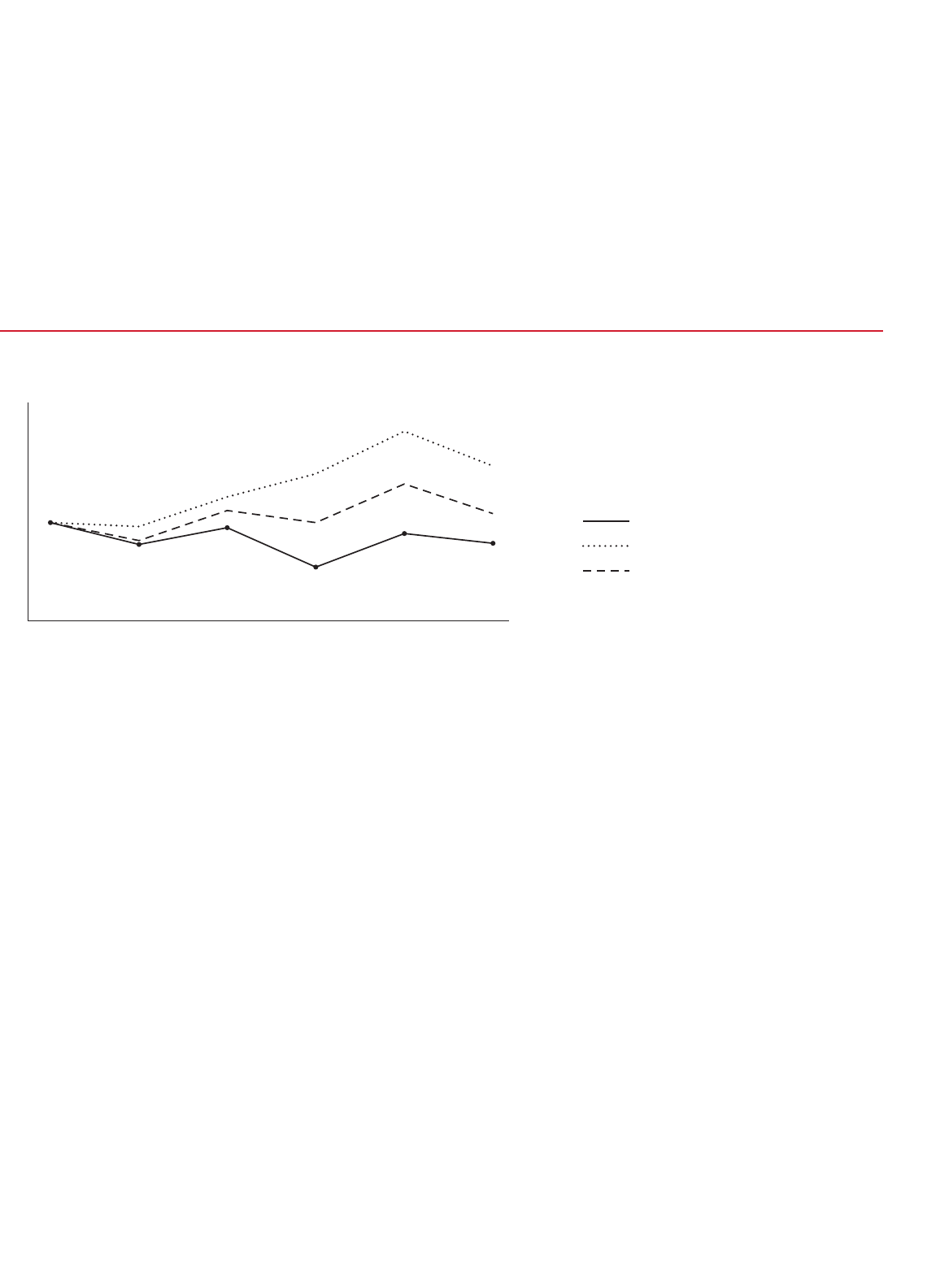
Stock Performance
This graph compares the cumulative total stockholder return and total compound annual growth rate (CAGR) for our common
stock (NYSE: WFC) for the five-year period ended December 31, 2022, with the cumulative total stockholder return for the same
period for the Keefe, Bruyette and Woods (KBW) Total Return Bank Index (KBW Nasdaq Bank Index (BKX)) and the S&P 500
Index.
The cumulative total stockholder returns (including reinvested dividends) in the graph assume the investment of $100 in Wells
Fargo’s common stock, the KBW Nasdaq Bank Index, and the S&P 500 Index.
FIVE YEAR PERFORMANCE GRAPH
$220
$200
$180
$160
$140
$120
$100
$ 80
$ 60
$ 40
$ 20
Wells Fargo
(WFC)
S&P 500
KBW Nasdaq
Bank Index
2017
2018
2019
2020
2021
2022
5-year
CAGR
$100
$78
$95
$55
$89
$79
-5%
Wells Fa
rgo
100
96
126
149
192
157
9%
S&P 500
100
82
112
100
139
109
2%
KBW Nasdaq
Bank Index

General Information
Common Stock
Wells Fargo & Company is listed and trades on the New York
Stock Exchange: WFC. At February 10, 2023, there were
231,886 holders of record of the Company’s common stock and
the closing price reported on the New York Stock Exchange for
the common stock was $47.51 per share.
3,833,804,452 common shares outstanding (12/31/22)
Stock Purchase and Dividend Reinvestment
You can buy Wells Fargo stock directly from Wells Fargo, even if
you’re not a Wells Fargo shareholder, through optional cash
payments or automatic monthly deductions from a bank
account. You can also have your dividends reinvested
automatically. It’s a convenient, economical way to increase your
Wells Fargo investment.
Call 1-877-840-0492 for an enrollment kit, which includes a
plan prospectus.
Form 10-K
We will send Wells Fargo’s 2022 Annual Report on Form 10-K
(including the financial statements filed with the U.S.
Securities and Exchange Commission) free to any shareholder
who asks for a copy in writing.
Shareholders also can ask for copies of any exhibit to the Form
10-K. We will charge a fee to cover expenses to prepare and
send any exhibits.
Please send requests to: Corporate Secretary, Wells Fargo &
Company, MAC J0193-610, 30 Hudson Yards, New York, NY
10001-2170
SEC Filings
Our annual reports on Form 10-K, quarterly reports on Form
10-Q, current reports on Form 8-K, and amendments to those
reports are available free of charge on our website
(www.wellsfargo.com) as soon as practical after they are
electronically filed with or furnished to the SEC. Those reports
and amendments are also available free of charge on the SEC’s
website at www.sec.gov¹.
Forward-Looking Statements
This Annual Report contains forward-looking statements about
our future financial performance and business. Because forward-
looking statements are based on our current expectations and
assumptions regarding the future, they are subject to inherent
risks and uncertainties. Do not unduly rely on forward-looking
statements, as actual results could differ materially from
expectations. Forward-looking statements speak only as of the
date made, and we do not undertake to update them to reflect
changes or events that occur after that date. For information
about factors that could cause actual results to differ materially
from our expectations, refer to the discussion under “Forward-
Looking Statements” and “Risk Factors” in the Financial Review
portion of this Annual Report.
Investor Relations
1-415-371-2921
Shareowner Services
and Transfer Agent
EQ Shareowner Services
P.O. Box 64874
St. Paul, Minnesota
55164-0874
1-877-840-0492
www.shareowneronline.com¹
Annual Shareholders’ Meeting
10:00 a.m. Eastern Daylight Time
Tuesday, April 25, 2023
See Wells Fargo’s 2023 Proxy Statement
for more information about the annual
shareholders’ meeting.
1. We do not control this website. Wells Fargo has provided this link for your convenience, but does not endorse and is not responsible for the content, links, privacy policy, or security policy of this website.
Wells Fargo & Company
420 Montgomery Street
San Francisco, CA 94104
wellsfargo.com
©2023 Wells Fargo & Company.
CCM7565 (Rev 00, 1/each)
